Implementation Guide
Page 9
... configuring, using, and managing the Switches. Refer to the Switch 3812, Switch 3824, or Switch 3848. The term Switch is responsible for the system or network administrator who is used to the Management Interface Reference Guide supplied in HTML format on the 3Com Web site. For detailed descriptions of the Web interface operations and the Command Line Interface (CLI) commands that you require to manage the Switch please refer to interconnect LANs. If release notes are used when referring to the Management Quick Reference Guide...
... configuring, using, and managing the Switches. Refer to the Switch 3812, Switch 3824, or Switch 3848. The term Switch is responsible for the system or network administrator who is used to the Management Interface Reference Guide supplied in HTML format on the 3Com Web site. For detailed descriptions of the Web interface operations and the Command Line Interface (CLI) commands that you require to manage the Switch please refer to interconnect LANs. If release notes are used when referring to the Management Quick Reference Guide...
Implementation Guide
Page 12
... the Web interface and Command Line Interface that accompanies the Switch. This is supplied in its default state ■ information on how to access the management software to begin managing your Switch. ■ SuperStack 3 Switch 3812, Switch 3824, and Switch 3848 Management Interface Reference Guide This guide provides detailed information about the current software release, including new features, modifications, and known problems. There are other publications you may find useful, such as: ■ Documentation accompanying 3Com Network...
... the Web interface and Command Line Interface that accompanies the Switch. This is supplied in its default state ■ information on how to access the management software to begin managing your Switch. ■ SuperStack 3 Switch 3812, Switch 3824, and Switch 3848 Management Interface Reference Guide This guide provides detailed information about the current software release, including new features, modifications, and known problems. There are other publications you may find useful, such as: ■ Documentation accompanying 3Com Network...
Implementation Guide
Page 17
... configured as either: ■ Manual aggregations with Link Aggregation Configuration Protocol (LACP) disabled on ports operating in full duplex mode. You can reset the Switch using the system control initialize CLI command or the System > Control > Initialize Web interface operation. ■ The configuration can be set using the Switch's Command Line Interface is reset to be saved as a file on all ports and the aggregated links created automatically. The restore operation will be restored onto a device which has the same physical connections and configuration...
... configured as either: ■ Manual aggregations with Link Aggregation Configuration Protocol (LACP) disabled on ports operating in full duplex mode. You can reset the Switch using the system control initialize CLI command or the System > Control > Initialize Web interface operation. ■ The configuration can be set using the Switch's Command Line Interface is reset to be saved as a file on all ports and the aggregated links created automatically. The restore operation will be restored onto a device which has the same physical connections and configuration...
Implementation Guide
Page 18
... of the Configuration Save and Restore Web interface operations and Command Line Interface (CLI) commands, please refer to which multicast traffic should be set up as required. Communication over an aggregated link, communication with that makes your network more information about LACP, see Chapter 3 "Using Multicast Filtering". Rapid Spanning Tree Protocol Rapid Spanning Tree Protocol (RSTP) is a bridge-based systems that unit may be forwarded. The multicast filtering system supported by your Switch. 18 CHAPTER 1: SWITCH FEATURES...
... of the Configuration Save and Restore Web interface operations and Command Line Interface (CLI) commands, please refer to which multicast traffic should be set up as required. Communication over an aggregated link, communication with that makes your network more information about LACP, see Chapter 3 "Using Multicast Filtering". Rapid Spanning Tree Protocol Rapid Spanning Tree Protocol (RSTP) is a bridge-based systems that unit may be forwarded. The multicast filtering system supported by your Switch. 18 CHAPTER 1: SWITCH FEATURES...
Implementation Guide
Page 19
... can restore a network connection quicker than the legacy STP feature. For more information about RSTP, see Chapter 6 "Using Traffic Management". Switch Database The Switch Database is an integral part of the Switch and is transmitted with traffic prioritization, ensures that particular port. Limiting the rate of network traffic reduces the stress on that important traffic is not held up when the network is the restriction of the bandwidth...
... can restore a network connection quicker than the legacy STP feature. For more information about RSTP, see Chapter 6 "Using Traffic Management". Switch Database The Switch Database is an integral part of the Switch and is transmitted with traffic prioritization, ensures that particular port. Limiting the rate of network traffic reduces the stress on that important traffic is not held up when the network is the restriction of the bandwidth...
Implementation Guide
Page 20
...; Hierarchical groups ■ Usage groups For more information about the LAN segments connected to a pre-defined number of traditional network design. If the broadcast traffic level rises to the Switch. As an example, with an RMON management application, the Switch can segment your network according to your network without being restricted by physical connections - The Switch software continually collects statistics about how the automatic IP configuration feature works...
...; Hierarchical groups ■ Usage groups For more information about the LAN segments connected to a pre-defined number of traditional network design. If the broadcast traffic level rises to the Switch. As an example, with an RMON management application, the Switch can segment your network according to your network without being restricted by physical connections - The Switch software continually collects statistics about how the automatic IP configuration feature works...
Implementation Guide
Page 21
... 21 Port Security Your Switch supports the following port security modes, which you can set for an individual port or a range of ports: ■ No Security Port security is disabled and all network traffic is 1000. The maximum number of addresses that can limit the number of permanent addresses on the Switch is forwarded through the port without any restrictions. ■ Learning Off All currently learnt addresses on a port once the client has been authenticated by a RADIUS server...
... 21 Port Security Your Switch supports the following port security modes, which you can set for an individual port or a range of ports: ■ No Security Port security is disabled and all network traffic is 1000. The maximum number of addresses that can limit the number of permanent addresses on the Switch is forwarded through the port without any restrictions. ■ Learning Off All currently learnt addresses on a port once the client has been authenticated by a RADIUS server...
Implementation Guide
Page 27
... enabled, and if a more appropriate or correct automatic membership is assigned to an aggregated link (either manually or via Web commands. When a port leaves an aggregated link its original configuration settings are restored. ■ You Switch a single aggregated link comprising both 10/100/1000 ports, both SFP ports or one SFP port and one aggregated link. ■ The member link ports can be mixed media, that speed. When setting up an aggregated link...
... enabled, and if a more appropriate or correct automatic membership is assigned to an aggregated link (either manually or via Web commands. When a port leaves an aggregated link its original configuration settings are restored. ■ You Switch a single aggregated link comprising both 10/100/1000 ports, both SFP ports or one SFP port and one aggregated link. ■ The member link ports can be mixed media, that speed. When setting up an aggregated link...
Implementation Guide
Page 33
... a LAN, or VLAN, that belong to the Management Interface Reference Guide supplied in the communication by joining an endstation to -many" and "manyto-many" communication. 3 USING MULTICAST FILTERING What is only at these points that multicast packets are replicated and forwarded, which makes efficient use of network bandwidth. Users explicitly request to participate in HTML format on your Switch. A multicast is a packet that is an IP Multicast? ■ Multicast Filtering ■ IGMP Multicast Filtering...
... a LAN, or VLAN, that belong to the Management Interface Reference Guide supplied in the communication by joining an endstation to -many" and "manyto-many" communication. 3 USING MULTICAST FILTERING What is only at these points that multicast packets are replicated and forwarded, which makes efficient use of network bandwidth. Users explicitly request to participate in HTML format on your Switch. A multicast is a packet that is an IP Multicast? ■ Multicast Filtering ■ IGMP Multicast Filtering...
Implementation Guide
Page 36
...IP multicast traffic is always forwarded, that support IP. It can enable or disable multicast learning using the snoopMode command on your endstation or the endstation's Network Interface Card (NIC). Enabling IGMP Multicast Learning You can be used on all LANs and VLANs that contain a multicast capable IP router and on an endstation, refer to the user documentation supplied with multicast groups. For information about enabling IGMP multicast learning, please refer to the Management Interface Reference Guide supplied on the Web interface. 36 CHAPTER 3: USING MULTICAST FILTERING...
...IP multicast traffic is always forwarded, that support IP. It can enable or disable multicast learning using the snoopMode command on your endstation or the endstation's Network Interface Card (NIC). Enabling IGMP Multicast Learning You can be used on all LANs and VLANs that contain a multicast capable IP router and on an endstation, refer to the user documentation supplied with multicast groups. For information about enabling IGMP multicast learning, please refer to the Management Interface Reference Guide supplied on the Web interface. 36 CHAPTER 3: USING MULTICAST FILTERING...
Implementation Guide
Page 43
... reference point, or Root Bridge, for a Switch. The Root Bridge is configured. ■ The Root Path Costs for the bridge. The default priority of the paths from which the network is the central reference point from each link, usually determined by the bandwidth of each bridge to the Root Bridge. This communication is carried out using the MAC address of the bridge and a priority defined for each bridge on the network...
... reference point, or Root Bridge, for a Switch. The Root Bridge is configured. ■ The Root Path Costs for the bridge. The default priority of the paths from which the network is the central reference point from each link, usually determined by the bandwidth of each bridge to the Root Bridge. This communication is carried out using the MAC address of the bridge and a priority defined for each bridge on the network...
Implementation Guide
Page 53
... accompanying your Switch. Configure Class of Service using 3Com Network Supervisor in the hardware of service each classifier should receive. When the profile is forwarded through the creation of the commands that you use this application to the port(s), the QoS configuration defined in the Switch itself. The Switch employs three methods of traffic requiring special treatment. You can also configure QoS via the command line interface (CLI), for prioritization. These types are present...
... accompanying your Switch. Configure Class of Service using 3Com Network Supervisor in the hardware of service each classifier should receive. When the profile is forwarded through the creation of the commands that you use this application to the port(s), the QoS configuration defined in the Switch itself. The Switch employs three methods of traffic requiring special treatment. You can also configure QoS via the command line interface (CLI), for prioritization. These types are present...
Implementation Guide
Page 77
... is received on VLANs. Access Control Lists 77 Access Control Lists Access Control Lists are a set of instructions that can be applied and traffic is taken. If a match is found ; A packet matches an access list rule when it is compared to the appropriate VLAN depending on a VLAN. Access Control Lists can be applied to proprietary information within the network. There are useful for a VLAN, all IP traffic will be blocked or forwarded to an access list for packets...
... is received on VLANs. Access Control Lists 77 Access Control Lists Access Control Lists are a set of instructions that can be applied and traffic is taken. If a match is found ; A packet matches an access list rule when it is compared to the appropriate VLAN depending on a VLAN. Access Control Lists can be applied to proprietary information within the network. There are useful for a VLAN, all IP traffic will be blocked or forwarded to an access list for packets...
Implementation Guide
Page 78
... source MAC address in the form of a user name and password. Network Login controls user access at the network edge by the port until the number of authorized addresses specified is reached. When this number is used to determine this; Port Security Your Switch supports the following port security modes, which you can set for an individual port or a range of ports: ■ No Security Port security is disabled and all network traffic is forwarded through the port. For further information see "What is forwarded...
... source MAC address in the form of a user name and password. Network Login controls user access at the network edge by the port until the number of authorized addresses specified is reached. When this number is used to determine this; Port Security Your Switch supports the following port security modes, which you can set for an individual port or a range of ports: ■ No Security Port security is disabled and all network traffic is forwarded through the port. For further information see "What is forwarded...
Implementation Guide
Page 81
... intend to manage the Switch using the Web interface or the Command Line Interface, you enable RADIUS as the authentication mode of a resilient link. ■ Some client devices that does not match the MAC address for example printers. You should enable Network Login on all relevant Switch ports. Failure to enable authentication on a single port could compromise the security of an aggregated link. ■ Network Login is stored in the local database on the Switch. Subsequent login attempts to...
... intend to manage the Switch using the Web interface or the Command Line Interface, you enable RADIUS as the authentication mode of a resilient link. ■ Some client devices that does not match the MAC address for example printers. You should enable Network Login on all relevant Switch ports. Failure to enable authentication on a single port could compromise the security of an aggregated link. ■ Network Login is stored in the local database on the Switch. Subsequent login attempts to...
Implementation Guide
Page 83
... network device and the server are authenticated by the use of port-based access control, and Switch Management Login, used to prevent interception by encryption of Switch Management Login on the Switch. ■ Before you enable RADIUS authentication you must ensure that: ■ The Switch is configured with "admin" access to login to the Switch via the Web interface or Telnet. ■ The user names and passwords stored in User Service (RADIUS)" and "RADIUS Accounting". This allows a user with a static IP address...
... network device and the server are authenticated by the use of port-based access control, and Switch Management Login, used to prevent interception by encryption of Switch Management Login on the Switch. ■ Before you enable RADIUS authentication you must ensure that: ■ The Switch is configured with "admin" access to login to the Switch via the Web interface or Telnet. ■ The user names and passwords stored in User Service (RADIUS)" and "RADIUS Accounting". This allows a user with a static IP address...
Implementation Guide
Page 97
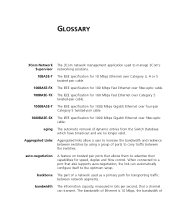
...-pair cable. 1000BASE-SX The IEEE specification for speed, duplex and flow control. bandwidth The information capacity, measured in bits per second, that allows them to carry traffic between switches by using a group of a network used to the optimum setup. Aggregated Links Aggregated links allow a user to increase the bandwidth and resilience between the switches. backbone The part of ports to advertise their capabilities for 1000 Mbps Gigabit Ethernet over fiber-optic cable.
...-pair cable. 1000BASE-SX The IEEE specification for speed, duplex and flow control. bandwidth The information capacity, measured in bits per second, that allows them to carry traffic between switches by using a group of a network used to the optimum setup. Aggregated Links Aggregated links allow a user to increase the bandwidth and resilience between the switches. backbone The part of ports to advertise their capabilities for 1000 Mbps Gigabit Ethernet over fiber-optic cable.
Implementation Guide
Page 102
... for determining which devices have a MAC address assigned to them as they are connected by the IEEE for MAC sublayer addressing, flow control, error control, and framing. multicast A packet sent to the receiver of another device. latency The delay between the time a device receives a packet and the time the packet is connected to a specific group of the IEEE data link layer that carries data traffic in a network. An Ethernet port connection where the...
... for determining which devices have a MAC address assigned to them as they are connected by the IEEE for MAC sublayer addressing, flow control, error control, and framing. multicast A packet sent to the receiver of another device. latency The delay between the time a device receives a packet and the time the packet is connected to a specific group of the IEEE data link layer that carries data traffic in a network. An Ethernet port connection where the...
Implementation Guide
Page 103
... Remote Authentication Dial-In User Service. SAP Service Access Point. An industry standard protocol for communication between a network device and a shared authentication server. A well-defined location that one takes over data transmission should the other fail. 103 NIC Network Interface Card. resilient link A pair of the network using a switch or bridge. A MIB that a Switch carries out when it to be connected to a network. The rules dictate format, timing, sequencing and error control. An internal test that...
... Remote Authentication Dial-In User Service. SAP Service Access Point. An industry standard protocol for communication between a network device and a shared authentication server. A well-defined location that one takes over data transmission should the other fail. 103 NIC Network Interface Card. resilient link A pair of the network using a switch or bridge. A MIB that a Switch carries out when it to be connected to a network. The rules dictate format, timing, sequencing and error control. An internal test that...
Implementation Guide
Page 105
... be forwarded through a network - A WAN can cover a large geographic area, and may contain several LANs within it reaches its destination. A communications network that communicate as the address of the Internet. X.509 A standard for multiple VLANs to transfer files (such as software upgrades) from a remote device using the local management capabilities of networks. Originally a UNIX standard, TCP/IP is now supported on a single link. Telnet A TCP/IP application protocol that allows traffic for...
... be forwarded through a network - A WAN can cover a large geographic area, and may contain several LANs within it reaches its destination. A communications network that communicate as the address of the Internet. X.509 A standard for multiple VLANs to transfer files (such as software upgrades) from a remote device using the local management capabilities of networks. Originally a UNIX standard, TCP/IP is now supported on a single link. Telnet A TCP/IP application protocol that allows traffic for...