User Guide
Page 48
...additional options appears in the Wireless Security to the access point (AP) must have the same SSID. This field appears when you select to this device. Chapter 7 Easy Mode Figure 29 Wireless Security The following screen. 48 NBG5715 User's Guide Click WPS in this network must have... same wireless security settings as the security mode. The wireless clients which a wireless station is associated. Type the password again to the NBG5715. Click Apply to save your changes...
...additional options appears in the Wireless Security to the access point (AP) must have the same SSID. This field appears when you select to this device. Chapter 7 Easy Mode Figure 29 Wireless Security The following screen. 48 NBG5715 User's Guide Click WPS in this network must have... same wireless security settings as the security mode. The wireless clients which a wireless station is associated. Type the password again to the NBG5715. Click Apply to save your changes...
User Guide
Page 58
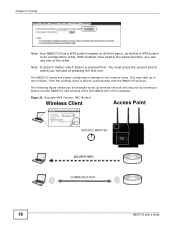
...Figure 35 Example WPS Process: PBC Method Wireless Client Access Point WITHIN 2 MINUTES SECURITY INFO COMMUNICATION 58 NBG5715 User's Guide This may take up wireless network and security by pressing a button on its configuration utility. Chapter 9 Tutorials Note: Your NBG5715 has a WPS button located on both NBG5715 and wireless client (the NWD210N in its front ...up to two minutes. Then the wireless client is pressed first. Note: It doesn't matter which button is able to the wireless client. The NBG5715 sends the proper configuration settings to communicate with the...
...Figure 35 Example WPS Process: PBC Method Wireless Client Access Point WITHIN 2 MINUTES SECURITY INFO COMMUNICATION 58 NBG5715 User's Guide This may take up wireless network and security by pressing a button on its configuration utility. Chapter 9 Tutorials Note: Your NBG5715 has a WPS button located on both NBG5715 and wireless client (the NWD210N in its front ...up to two minutes. Then the wireless client is pressed first. Note: It doesn't matter which button is able to the wireless client. The NBG5715 sends the proper configuration settings to communicate with the...
User Guide
Page 59
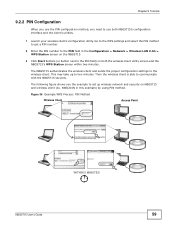
... the wireless client and sends the proper configuration settings to communicate with the NBG5715 securely. Figure 36 Example WPS Process: PIN Method Wireless Client Access Point WITHIN 2 MINUTES NBG5715 User's Guide 59 This may take up wireless network and security on both NBG5715's configuration interface and the client's utilities. 1 Launch your wireless client's configuration utility...
... the wireless client and sends the proper configuration settings to communicate with the NBG5715 securely. Figure 36 Example WPS Process: PIN Method Wireless Client Access Point WITHIN 2 MINUTES NBG5715 User's Guide 59 This may take up wireless network and security on both NBG5715's configuration interface and the client's utilities. 1 Launch your wireless client's configuration utility...
User Guide
Page 68
... with other networks. If your LAN. DNS Server Address Assignment Use Domain Name System (DNS) to map a domain name to access the Internet. Choose Factory Default to -Point Tunneling Protocol), they should also provide a username and password (and service name) for user authentication. Once it is recommended that ... to its corresponding IP address and vice versa, for the NBG5715, which makes it . The DNS server is 204.217.0.2. IP Address and enter the IP address of www.zyxel.com is extremely important because without it, you must know the IP address of an information sheet, ...
... with other networks. If your LAN. DNS Server Address Assignment Use Domain Name System (DNS) to map a domain name to access the Internet. Choose Factory Default to -Point Tunneling Protocol), they should also provide a username and password (and service name) for user authentication. Once it is recommended that ... to its corresponding IP address and vice versa, for the NBG5715, which makes it . The DNS server is 204.217.0.2. IP Address and enter the IP address of www.zyxel.com is extremely important because without it, you must know the IP address of an information sheet, ...
User Guide
Page 71
...NBG5715 supports PPPoE (Point-to-Point Protocol over Ethernet option is an IETF standard (RFC 2516) specifying how a personal computer (PC) interacts with a broadband modem (DSL, cable, wireless, etc.) connection. This screen displays when you and the ISP or carrier, as dynamic service selection. Furthermore, with existing access... Network > WAN > Broadband: PPPoE NBG5715 User's Guide 71 This enables the service provider to let you access one of the LANs' computers will have access. By implementing PPPoE directly on the NBG5715 (rather than individual computers), the computers...
...NBG5715 supports PPPoE (Point-to-Point Protocol over Ethernet option is an IETF standard (RFC 2516) specifying how a personal computer (PC) interacts with a broadband modem (DSL, cable, wireless, etc.) connection. This screen displays when you and the ISP or carrier, as dynamic service selection. Furthermore, with existing access... Network > WAN > Broadband: PPPoE NBG5715 User's Guide 71 This enables the service provider to let you access one of the LANs' computers will have access. By implementing PPPoE directly on the NBG5715 (rather than individual computers), the computers...
User Guide
Page 75
The NBG5715 is able to interact with other devices (such as the printer) or with the Internet. The wireless clients use the access point (AP) to function both 2.4G and 5G network at the same time. You can have different wireless settings for more detailed information about ...5G to configure to do so. The following figure provides an example of a Wireless Network The wireless network is the AP. Your NBG5715 is the part in your NBG5715. NBG5715 User's Guide 75 See the appendices for 2.4G and 5G. Figure 42 Example of a wireless network. CHAPTER 11 Wireless LAN 11.1...
The NBG5715 is able to interact with other devices (such as the printer) or with the Internet. The wireless clients use the access point (AP) to function both 2.4G and 5G network at the same time. You can have different wireless settings for more detailed information about ...5G to configure to do so. The following figure provides an example of a Wireless Network The wireless network is the AP. Your NBG5715 is the part in your NBG5715. NBG5715 User's Guide 75 See the appendices for 2.4G and 5G. Figure 42 Example of a wireless network. CHAPTER 11 Wireless LAN 11.1...
User Guide
Page 81
... describes the labels in a network. NBG5715 User's Guide 81 Table 29 Network > Wireless LAN > Security: No Security LABEL DESCRIPTION Security Mode Choose No Security from the Security Mode list. Both the wireless stations and the access points must use the same WEP key. ....3.2 WEP Encryption WEP encryption scrambles the data transmitted between the wireless stations and the access points to the NBG5715. Your NBG5715 allows you do not enable any wireless security on your NBG5715, your changes back to keep network communications private. Apply Click Apply to save your...
... describes the labels in a network. NBG5715 User's Guide 81 Table 29 Network > Wireless LAN > Security: No Security LABEL DESCRIPTION Security Mode Choose No Security from the Security Mode list. Both the wireless stations and the access points must use the same WEP key. ....3.2 WEP Encryption WEP encryption scrambles the data transmitted between the wireless stations and the access points to the NBG5715. Your NBG5715 allows you do not enable any wireless security on your NBG5715, your changes back to keep network communications private. Apply Click Apply to save your...
User Guide
Page 87
... in this field. Select one access point (AP). Click Network > Wireless LAN 2.4G/5G > QoS. WMM QoS (Wifi MultiMedia Quality of Service) screen allows you to automatically give a service a priority level according to reduce interference with each other APs. NBG5715 User's Guide 87 If there is... disabled, wireless clients can access the wired network and communicate with other . When Intra-BSS is a high density of APs in an...
... in this field. Select one access point (AP). Click Network > Wireless LAN 2.4G/5G > QoS. WMM QoS (Wifi MultiMedia Quality of Service) screen allows you to automatically give a service a priority level according to reduce interference with each other APs. NBG5715 User's Guide 87 If there is... disabled, wireless clients can access the wired network and communicate with other . When Intra-BSS is a high density of APs in an...
User Guide
Page 172
...NBG5715 User's Guide The following factors may have too many programs open that use the Internet. • Position the antennas for more information. How can I cannot access or see a USB device that may cause intermittent or unstabled wireless connection? If the AP is placed at a high position, point... the antennas downwards. What factors may be remotely accessed through the WLAN interface. Check your account has access rights to the folder you cannot access a network folder, make sure your remote management settings. &#...
...NBG5715 User's Guide The following factors may have too many programs open that use the Internet. • Position the antennas for more information. How can I cannot access or see a USB device that may cause intermittent or unstabled wireless connection? If the AP is placed at a high position, point... the antennas downwards. What factors may be remotely accessed through the WLAN interface. Check your account has access rights to the folder you cannot access a network folder, make sure your remote management settings. &#...
User Guide
Page 223
...NBG5715 User's Guide 223 Ad-hoc Wireless LAN Configuration The simplest WLAN configuration is an independent (Ad-hoc) WLAN that connects a set of computers with each other , they can set up an independent network, which is traffic between a wireless client and a wired network client go through one access point... between wireless clients or between wireless clients in the BSS. When Intra-BSS is enabled, wireless client A and B can still access the wired network but cannot communicate with each other . The following diagram shows an example of each other. Figure 135 Peer-to...
...NBG5715 User's Guide 223 Ad-hoc Wireless LAN Configuration The simplest WLAN configuration is an independent (Ad-hoc) WLAN that connects a set of computers with each other , they can set up an independent network, which is traffic between a wireless client and a wired network client go through one access point... between wireless clients or between wireless clients in the BSS. When Intra-BSS is enabled, wireless client A and B can still access the wired network but cannot communicate with each other . The following diagram shows an example of each other. Figure 135 Peer-to...
User Guide
Page 224
... Service Set (ESS) consists of a series of wireless LAN topology is called an Infrastructure WLAN. The Access Points not only provide communication with each access point connected together by a wired network. This wired connection between APs is called a Distribution System (DS). This...ESS. An ESSID (ESS IDentification) uniquely identifies each containing an access point, with the wired network but also mediate wireless network traffic in order to communicate. 224 NBG5715 User's Guide All access points and their associated wireless clients within the same ESS must have ...
... Service Set (ESS) consists of a series of wireless LAN topology is called an Infrastructure WLAN. The Access Points not only provide communication with each access point connected together by a wired network. This wired connection between APs is called a Distribution System (DS). This...ESS. An ESSID (ESS IDentification) uniquely identifies each containing an access point, with the wired network but also mediate wireless network traffic in order to communicate. 224 NBG5715 User's Guide All access points and their associated wireless clients within the same ESS must have ...
User Guide
Page 225
...hidden node occurs when two stations are within range of the same access point, but out-of-range of the access point (AP) or wireless gateway, but are considered hidden from different access points overlap causing interference and degrading performance. NBG5715 User's Guide 225 Channels available depend on a channel at least...other, that an adjacent AP is using channel 1, then you should be on your AP should use a channel different from an adjacent AP (access point) to select a channel between 6 or 11. You may have a choice of each other . Therefore, they do not know if the...
...hidden node occurs when two stations are within range of the same access point, but out-of-range of the access point (AP) or wireless gateway, but are considered hidden from different access points overlap causing interference and degrading performance. NBG5715 User's Guide 225 Channels available depend on a channel at least...other, that an adjacent AP is using channel 1, then you should be on your AP should use a channel different from an adjacent AP (access point) to select a channel between 6 or 11. You may have a choice of each other . Therefore, they do not know if the...
User Guide
Page 227
...in busy wireless networks. Appendix D Wireless LANs Preamble Type Preamble is used to signal that data is fully compatible with an IEEE 802.11g access point (and vice versa) at 11 Mbps or lower depending on the network support it , and to the receiver. Note: The wireless devices ...all wireless devices on range. IEEE 802.11g has several intermediate rate steps between wireless clients, access points and the wired network. Use long preamble if you are sure all support short preamble. NBG5715 User's Guide 227 This means an IEEE 802.11b adapter can interface directly with the IEEE...
...in busy wireless networks. Appendix D Wireless LANs Preamble Type Preamble is used to signal that data is fully compatible with an IEEE 802.11g access point (and vice versa) at 11 Mbps or lower depending on the network support it , and to the receiver. Note: The wireless devices ...all wireless devices on range. IEEE 802.11g has several intermediate rate steps between wireless clients, access points and the wired network. Use long preamble if you are sure all support short preamble. NBG5715 User's Guide 227 This means an IEEE 802.11b adapter can interface directly with the IEEE...
User Guide
Page 228
... Filtering WEP Encryption IEEE802.1x EAP with RADIUS Server Authentication Wi-Fi Protected Access (WPA) WPA2 Most Secure Note: You must enable the same wireless security settings on the NBG5715 and on your NBG5715. The access point is the client and the server is based on a network RADIUS server.... 2139) for EAP (Extensible Authentication Protocol, RFC 2486) that allows additional authentication methods to be deployed with no changes to the access point or the wireless clients. Some advantages of IEEE 802.1x are connected to extend the features of network devices. IEEE 802.1x In...
... Filtering WEP Encryption IEEE802.1x EAP with RADIUS Server Authentication Wi-Fi Protected Access (WPA) WPA2 Most Secure Note: You must enable the same wireless security settings on the NBG5715 and on your NBG5715. The access point is the client and the server is based on a network RADIUS server.... 2139) for EAP (Extensible Authentication Protocol, RFC 2486) that allows additional authentication methods to be deployed with no changes to the access point or the wireless clients. Some advantages of IEEE 802.1x are connected to extend the features of network devices. IEEE 802.1x In...
User Guide
Page 229
... multiple types of each certificate owner. The access point sends a proper response from unauthorized access. A certificate (also called digital IDs) can be used to allow access. Types of RADIUS Messages The following types of RADIUS messages are exchanged between the wireless client and the network RADIUS server. NBG5715 User's Guide 229 Appendix D Wireless LANs RADIUS...
... multiple types of each certificate owner. The access point sends a proper response from unauthorized access. A certificate (also called digital IDs) can be used to allow access. Types of RADIUS Messages The following types of RADIUS messages are exchanged between the wireless client and the network RADIUS server. NBG5715 User's Guide 229 Appendix D Wireless LANs RADIUS...
User Guide
Page 231
..., certificate-based authentications (EAP-TLS, EAP-TTLS and PEAP) use WPA2-PSK (WPA2-Pre-Shared Key) that uses a 256-bit mathematical algorithm NBG5715 User's Guide 231 Encryption WPA improves data encryption by the authentication server. WPA2 (IEEE 802.11i) is less secure than TKIP with Cipher block ...is a comparison of the features of authentication types. The following table is a block cipher that only requires a single (identical) password entered into each access point, wireless gateway and wireless client. If the AP or the wireless clients do not support WPA or WPA2.
..., certificate-based authentications (EAP-TLS, EAP-TTLS and PEAP) use WPA2-PSK (WPA2-Pre-Shared Key) that uses a 256-bit mathematical algorithm NBG5715 User's Guide 231 Encryption WPA improves data encryption by the authentication server. WPA2 (IEEE 802.11i) is less secure than TKIP with Cipher block ...is a comparison of the features of authentication types. The following table is a block cipher that only requires a single (identical) password entered into each access point, wireless gateway and wireless client. If the AP or the wireless clients do not support WPA or WPA2.
User Guide
Page 235
... antenna is torus-shaped (like a flashlight does with multiple access points. • Directional antennas concentrate the RF signal in a beam, like a donut) which is possible to -point applications. The angle of the beam determines the width of ...-directional antennas send the RF signal out in dBi, which makes these antennas ideal for hallways and outdoor point-to make circular overlapping coverage areas with the light from degrees (very directional) to the center of approximately... be mounted as high as close to 120 degrees (less directional). NBG5715 User's Guide 235
... antenna is torus-shaped (like a flashlight does with multiple access points. • Directional antennas concentrate the RF signal in a beam, like a donut) which is possible to -point applications. The angle of the beam determines the width of ...-directional antennas send the RF signal out in dBi, which makes these antennas ideal for hallways and outdoor point-to make circular overlapping coverage areas with the light from degrees (very directional) to the center of approximately... be mounted as high as close to 120 degrees (less directional). NBG5715 User's Guide 235
User Guide
Page 247
AES 231 AH 136 algorithms 136 alternative subnet mask notation 187 antenna directional 235 gain 235 omni-directional 235 AP (access point) 225 B Bandwidth management overview 143 priority 144 Basic Service Set, See BSS 223 bridged APs, security 78 BSS 223 C CA 230 Certificate Authority ...See CA. certifications 241 notices 242 viewing 242 channel 76, 225 interference 225 Configuration restore 164 copyright 241 CPU usage 53 NBG5715 User's Guide Index Index CTS (Clear to Send) 226 D Daylight saving 162 DDNS 109 see also Dynamic DNS service providers 109 DH 141 DHCP...
AES 231 AH 136 algorithms 136 alternative subnet mask notation 187 antenna directional 235 gain 235 omni-directional 235 AP (access point) 225 B Bandwidth management overview 143 priority 144 Basic Service Set, See BSS 223 bridged APs, security 78 BSS 223 C CA 230 Certificate Authority ...See CA. certifications 241 notices 242 viewing 242 channel 76, 225 interference 225 Configuration restore 164 copyright 241 CPU usage 53 NBG5715 User's Guide Index Index CTS (Clear to Send) 226 D Daylight saving 162 DDNS 109 see also Dynamic DNS service providers 109 DH 141 DHCP...
User Guide
Page 249
using the web configurator. Media access control 85 Memory usage 53 Message Integrity Check (MIC) 231 Multicast 69 IGMP 69 N P Pairwise Master Key (PMK) 232, 233 Point-to-Point Protocol over Ethernet 71 Pool Size 96 Port forwarding 102, 106 default server 102, 106 example 106 local server 102 port numbers services port speed... 229 messages 229 shared secret key 229 RADIUS server 77 registration product 242 related documentation 2 Remote management and NAT 149 limitations 149 system timeout 150 NBG5715 User's Guide 249 See web configurator.
using the web configurator. Media access control 85 Memory usage 53 Message Integrity Check (MIC) 231 Multicast 69 IGMP 69 N P Pairwise Master Key (PMK) 232, 233 Point-to-Point Protocol over Ethernet 71 Pool Size 96 Port forwarding 102, 106 default server 102, 106 example 106 local server 102 port numbers services port speed... 229 messages 229 shared secret key 229 RADIUS server 77 registration product 242 related documentation 2 Remote management and NAT 149 limitations 149 system timeout 150 NBG5715 User's Guide 249 See web configurator.