Design Guide
Page 3
... 42 1-9-5 Captured Documents and Log Data 42 1-10 Additional Methods for Each Individual User 45 2-1-7 Job/Access Log Data Collection 45 2-1-8 Print Backup ...45 2-2 Printer ...47 2-2-1 Overview of Printer Operations 47 2-2-2 Data Flow...47 2-2-3 Data Security Considerations 51 2-3 Scanner (MFP Models Only 54 2-3-1 Overview of Scanner Operations 54 2-3-2 Data Flow Security Considerations...
... 42 1-9-5 Captured Documents and Log Data 42 1-10 Additional Methods for Each Individual User 45 2-1-7 Job/Access Log Data Collection 45 2-1-8 Print Backup ...45 2-2 Printer ...47 2-2-1 Overview of Printer Operations 47 2-2-2 Data Flow...47 2-2-3 Data Security Considerations 51 2-3 Scanner (MFP Models Only 54 2-3-1 Overview of Scanner Operations 54 2-3-2 Data Flow Security Considerations...
Design Guide
Page 5
Print Controller Design Guide for Information Security (MFP models only) ...80 4-2-2 FAX Functions (MFP models only 80 4-2-3 Network Functions 81 4-2-4 Printer Functions 81 4-2-5 Machine Administrative Functions (MFP models only 81 4-2-6 Authentication Functions 81 4-3 Data Security Considerations 83 4-3-1 Preventing the Installation of Illegal Applications 83 4-3-2 Authentication of ...
Print Controller Design Guide for Information Security (MFP models only) ...80 4-2-2 FAX Functions (MFP models only 80 4-2-3 Network Functions 81 4-2-4 Printer Functions 81 4-2-5 Machine Administrative Functions (MFP models only 81 4-2-6 Authentication Functions 81 4-3 Data Security Considerations 83 4-3-1 Preventing the Installation of Illegal Applications 83 4-3-2 Authentication of ...
Design Guide
Page 6
... LD360sp LD370 LD370sp LD380 LD380sp LD390 LD390sp LP37N RICOH SP C820DN SP C821DN Pro 907EX Pro 1107EX Pro 1357EX Pro 907 Pro 1107 Pro 1357 AFICIO MP 6001 MP 6001 SP MP 7001 MP 7001 SP MP 8001 MP 8001 SP MP 9001 MP 9001 SP AFICIO SP4210N SAVIN CLP340D CLP350D Pro 907EX Pro 1107EX ...as the information security of image data and other information handled internally by Ricoh MFP/LPs. Page 6 of 86 For these details, please refer to the Operating Instructions for the multi-functional products and laser printers listed below (herein referred to the following MFPs/LPs designed and developed by...
... LD360sp LD370 LD370sp LD380 LD380sp LD390 LD390sp LP37N RICOH SP C820DN SP C821DN Pro 907EX Pro 1107EX Pro 1357EX Pro 907 Pro 1107 Pro 1357 AFICIO MP 6001 MP 6001 SP MP 7001 MP 7001 SP MP 8001 MP 8001 SP MP 9001 MP 9001 SP AFICIO SP4210N SAVIN CLP340D CLP350D Pro 907EX Pro 1107EX ...as the information security of image data and other information handled internally by Ricoh MFP/LPs. Page 6 of 86 For these details, please refer to the Operating Instructions for the multi-functional products and laser printers listed below (herein referred to the following MFPs/LPs designed and developed by...
Design Guide
Page 11
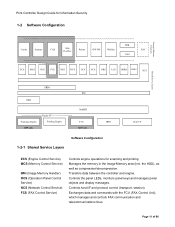
... Panel Control Service) NCS (Network Control Service) FCS (FAX Control Service) Controls engine operations for Information Security 1-2 Software Configuration SDK Copier Scanner FAX Web DocBox Printer GW WS WebSys EAC VAS ECS MCS OCS FCS NCS DCS UCS CCS NRS LCS MIRS DESS SCS S Shared Service Layers SRM libc IMH Engine...
... Panel Control Service) NCS (Network Control Service) FCS (FAX Control Service) Controls engine operations for Information Security 1-2 Software Configuration SDK Copier Scanner FAX Web DocBox Printer GW WS WebSys EAC VAS ECS MCS OCS FCS NCS DCS UCS CCS NRS LCS MIRS DESS SCS S Shared Service Layers SRM libc IMH Engine...
Design Guide
Page 12
...) DESS (Data Encryption Security Service) Manages the status of all non-FAX transmission/reception of e-mail as the operational link between SP settings and machine operations. Controls remote correspondence with RC Gate (e.g. Controls the sending of 86 Controls the encryption and decryption functions. ... between the principal machine function and external charge device during the image creation process. Secondary data, such as that converts the printer language into image data, which then sends the data to the controller. Secondary data is handled via the host I /F. counters...
...) DESS (Data Encryption Security Service) Manages the status of all non-FAX transmission/reception of e-mail as the operational link between SP settings and machine operations. Controls remote correspondence with RC Gate (e.g. Controls the sending of 86 Controls the encryption and decryption functions. ... between the principal machine function and external charge device during the image creation process. Secondary data, such as that converts the printer language into image data, which then sends the data to the controller. Secondary data is handled via the host I /F. counters...
Design Guide
Page 13
... view and make changes to user information and machine configuration settings, as well as to the MFP HDD. GWWS also acts as store Printer documents to print out or perform other operations on documents stored on Document Server documents stored in the MFP (viewing, downloading, printing, ...API that allows machine configuration settings to specific log data collection utilities A Web application that standardizes the meanings of simplified commands used by Ricoh. The EAC allows the external controller to initiate MFP operations such as print jobs and scan jobs, as well as a client ...
... view and make changes to user information and machine configuration settings, as well as to the MFP HDD. GWWS also acts as store Printer documents to print out or perform other operations on documents stored on Document Server documents stored in the MFP (viewing, downloading, printing, ...API that allows machine configuration settings to specific log data collection utilities A Web application that standardizes the meanings of simplified commands used by Ricoh. The EAC allows the external controller to initiate MFP operations such as print jobs and scan jobs, as well as a client ...
Design Guide
Page 17
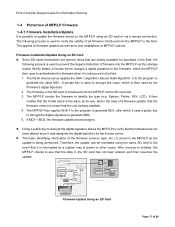
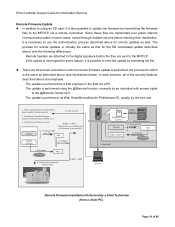
...signa ture 5. Briefly stated, a license server assigns a digital signature to the firmware, which it is introduced in the field. 1. The Ricoh license server applies the SHA-1 algorithm (Secure Hash Algorithm 1) to the program to authenticate the firmware when it uses a public key to decrypt...type (e.g. This applies to firmware updates as well as the update is being performed. Verification of model and target machine functions (Copier, Printer, etc .) 2. Generate MD1 ins ta lled Program using SHA-1 MD 2. Firmware is overwritten with new files Firmware Update Using an ...
...signa ture 5. Briefly stated, a license server assigns a digital signature to the firmware, which it is introduced in the field. 1. The Ricoh license server applies the SHA-1 algorithm (Secure Hash Algorithm 1) to the program to authenticate the firmware when it uses a public key to decrypt...type (e.g. This applies to firmware updates as well as the update is being performed. Verification of model and target machine functions (Copier, Printer, etc .) 2. Generate MD1 ins ta lled Program using SHA-1 MD 2. Firmware is overwritten with new files Firmware Update Using an ...
Design Guide
Page 18
... the firmware files to the MFP/LP via a remote connection. In each scenario, all of model and target machine functions (Copier, Printer, etc.) 3. Files are transmitted over public Internet communication paths in which is not installed MD1 Digital signature 7. Compare MD and...update is interrupted for the SD card-based update described above, with new files If MD1 = MD2 Digital signature Ricoh distribution server Program + digital signature Program Ricoh license server 1. Decryption Public key MD2 8. The update is possible to retry the update by the end...
... the firmware files to the MFP/LP via a remote connection. In each scenario, all of model and target machine functions (Copier, Printer, etc.) 3. Files are transmitted over public Internet communication paths in which is not installed MD1 Digital signature 7. Compare MD and...update is interrupted for the SD card-based update described above, with new files If MD1 = MD2 Digital signature Ricoh distribution server Program + digital signature Program Ricoh license server 1. Decryption Public key MD2 8. The update is possible to retry the update by the end...
Design Guide
Page 22
... LDAP connection with the MFP/LP HDD or one or more of the following types of characters, while Level 2 requires that do this, however, the Printer/Scanner option must be encrypted using an encryption key specified by that user exceeds the predetermined limit (access is denied and further usage of the...
... LDAP connection with the MFP/LP HDD or one or more of the following types of characters, while Level 2 requires that do this, however, the Printer/Scanner option must be encrypted using an encryption key specified by that user exceeds the predetermined limit (access is denied and further usage of the...
Design Guide
Page 32
... Administrators are not able to prohibit all users registered in the ACL from the Address Book ACL, it is stored if the Printer/Scanner option is possible to view the contents of Address Book entries. The data in the Address Book is possible to assign ...separate from programming new destinations in the HDD or SD card. Name E-mail address*1 FAX No. *1 ... Password*1, *2 Protection Code 00001 Taroh Ricoh taroh@ricoh.co.jp 1234-5678 Taroh ********** **** General Users Groups Owner of 86 Print Controller Design Guide for Information Security 1-7-3 Protection of Address Book Data ...
... Administrators are not able to prohibit all users registered in the ACL from the Address Book ACL, it is stored if the Printer/Scanner option is possible to view the contents of Address Book entries. The data in the Address Book is possible to assign ...separate from programming new destinations in the HDD or SD card. Name E-mail address*1 FAX No. *1 ... Password*1, *2 Protection Code 00001 Taroh Ricoh taroh@ricoh.co.jp 1234-5678 Taroh ********** **** General Users Groups Owner of 86 Print Controller Design Guide for Information Security 1-7-3 Protection of Address Book Data ...
Design Guide
Page 40
... SAF memory LAN FAX transmission Storage of LAN FAX file to the MFP HDD. Normal Print, Locked Print, Sample Print) Storage of Printer file to HDD Printing out of Printer file stored in HDD File printed out with Remote Print Scanner Desk Top Editor For Production Forwarding Forwarding + storage to HDD Storage... stored file Restoring a previously downloaded file from Desk Top Editor For Production to HDD for later transmission Transmission of LAN FAX file stored in HDD Printer Printing out of 86
... SAF memory LAN FAX transmission Storage of LAN FAX file to the MFP HDD. Normal Print, Locked Print, Sample Print) Storage of Printer file to HDD Printing out of Printer file stored in HDD File printed out with Remote Print Scanner Desk Top Editor For Production Forwarding Forwarding + storage to HDD Storage... stored file Restoring a previously downloaded file from Desk Top Editor For Production to HDD for later transmission Transmission of LAN FAX file stored in HDD Printer Printing out of 86
Design Guide
Page 47
.... 2-2-2 Data Flow Printing Unencrypted Image Data • As stated above, the printer language-encoded data sent from the host computer is interpreted by the language processing subsystem, after which it is compressed in Ricoh original compression format, and stored in WebImageMonitor, or "Spooling Job" list on... to the HDD. Page 47 of the pages may differ depending on the MFP/LP operation panel. The former is performed by the printer language processing subsystem, while the latter is performed by page. simplex, usage of Booklet or Stapling features, etc.). • When Image...
.... 2-2-2 Data Flow Printing Unencrypted Image Data • As stated above, the printer language-encoded data sent from the host computer is interpreted by the language processing subsystem, after which it is compressed in Ricoh original compression format, and stored in WebImageMonitor, or "Spooling Job" list on... to the HDD. Page 47 of the pages may differ depending on the MFP/LP operation panel. The former is performed by the printer language processing subsystem, while the latter is performed by page. simplex, usage of Booklet or Stapling features, etc.). • When Image...
Design Guide
Page 48
...stored in the HDD. When Store and Print is selected as the page size, paper type and number of the job, together with some printer languages (see below). • With Normal Print, the page location data for the image data stored in the HDD is stored in ... is erased at the conclusion of sets. In addition, the documents remain stored in Ricoh original format. The bibliographic information is part of 86 The necessary bibliographic information for Information Security • From the printer driver, it is possible to select the following printing methods: Normal Print, Sample Print...
...stored in the HDD. When Store and Print is selected as the page size, paper type and number of the job, together with some printer languages (see below). • With Normal Print, the page location data for the image data stored in the HDD is stored in ... is erased at the conclusion of sets. In addition, the documents remain stored in Ricoh original format. The bibliographic information is part of 86 The necessary bibliographic information for Information Security • From the printer driver, it is possible to select the following printing methods: Normal Print, Sample Print...
Design Guide
Page 49
... be decrypted correctly. Printing Encrypted Image Data • With PDF Direct Print, it is also possible to be registered in the printer driver UI, which retrieves the information via WebImageMonitor or the MFP/LP operation panel, or is stored in volatile memory and is therefore... information such as the "page location data" for the document is set in the Printer function via a Ricoh-original MIB over an SNMP connection. *1: The "print management data" is managed and maintained by the Printer function itself will be accessed from one another. Once a user ID is registered,...
... be decrypted correctly. Printing Encrypted Image Data • With PDF Direct Print, it is also possible to be registered in the printer driver UI, which retrieves the information via WebImageMonitor or the MFP/LP operation panel, or is stored in volatile memory and is therefore... information such as the "page location data" for the document is set in the Printer function via a Ricoh-original MIB over an SNMP connection. *1: The "print management data" is managed and maintained by the Printer function itself will be accessed from one another. Once a user ID is registered,...
Design Guide
Page 51
... sends the print data and authentication information to the MFP/LP, the authentication password is destroyed, preventing the introduction of illegal data. When the Printer's authentication mode is set to Simple Authentication, the MFP/LP does not perform authentication on data sent from users that does not contain this information ...
... sends the print data and authentication information to the MFP/LP, the authentication password is destroyed, preventing the introduction of illegal data. When the Printer's authentication mode is set to Simple Authentication, the MFP/LP does not perform authentication on data sent from users that does not contain this information ...
Design Guide
Page 52
... all filenames are displayed as asterisks ("****"). Print Controller Design Guide for printing out by any authenticated user by selecting "Share" in the printer driver's Advanced Options settings when the job is sent. If a password has been assigned to the document, the operator will prohibit all...in the HDD for which will encrypt the communication path. • Although any authenticated user can view the "Spool Printing" list (WebImageMonitor), printer job history and error log, it is possible to display other users' information in the in the form of asterisks ("****"). • When...
... all filenames are displayed as asterisks ("****"). Print Controller Design Guide for printing out by any authenticated user by selecting "Share" in the printer driver's Advanced Options settings when the job is sent. If a password has been assigned to the document, the operator will prohibit all...in the HDD for which will encrypt the communication path. • Although any authenticated user can view the "Spool Printing" list (WebImageMonitor), printer job history and error log, it is possible to display other users' information in the in the form of asterisks ("****"). • When...
Design Guide
Page 59
... for transmission as en email file attachment, after which it is then sent to its destination. The incoming document is then forwarded on to the printer engine for printing out. • For Internet FAX transmission, the scanned image data is converted into image data and then forwarded on to the... printer engine for printing out. • It is possible to store transmission files in non-volatile memory, and can be issued from the operation panel or ...
... for transmission as en email file attachment, after which it is then sent to its destination. The incoming document is then forwarded on to the printer engine for printing out. • For Internet FAX transmission, the scanned image data is converted into image data and then forwarded on to the... printer engine for printing out. • It is possible to store transmission files in non-volatile memory, and can be issued from the operation panel or ...
Design Guide
Page 64
... captured, added to, deleted, and changed from inside Web SmartDeviceMonitor Professional IS. Restoring Files Back to the MFP (MFP models only) • When Copier or Printer files that can be changed from the original one of the two DeskTop applications mentioned above operations from inside DeskTopBinder or Desk Top Editor For...
... captured, added to, deleted, and changed from inside Web SmartDeviceMonitor Professional IS. Restoring Files Back to the MFP (MFP models only) • When Copier or Printer files that can be changed from the original one of the two DeskTop applications mentioned above operations from inside DeskTopBinder or Desk Top Editor For...
Design Guide
Page 65
... inside Web SmartDeviceMonitor Professional IS, it is initiated. A sending/forwarding job is initiated from DeskTopBinder on a Scanner Document Server file - A download is initiated from the printer driver. However with an administrator-level User Account in the Netfile job log whenever any changes during the job), while the access log contains data...
... inside Web SmartDeviceMonitor Professional IS, it is initiated. A sending/forwarding job is initiated from DeskTopBinder on a Scanner Document Server file - A download is initiated from the printer driver. However with an administrator-level User Account in the Netfile job log whenever any changes during the job), while the access log contains data...
Design Guide
Page 68
... the PC and MFP/LP (which can only be protected against by eliminating the need to identify each time. As long as a Machine Administrator. The printer driver uses a track ID to send the user's password over the network each individual print job. Deleting, Pausing or Resuming Print Jobs To delete the...
... the PC and MFP/LP (which can only be protected against by eliminating the need to identify each time. As long as a Machine Administrator. The printer driver uses a track ID to send the user's password over the network each individual print job. Deleting, Pausing or Resuming Print Jobs To delete the...