Features Guide
Page 2
...Levels...4 Ricoh Aficio Security Solutions Compatibility Chart ...4 Ricoh Security Solutions Review...6 Network Protection...6 Web Image Monitor...6 SmartDeviceMonitor...6 Network Protocol ON/OFF ...7 Device Access...7 Administrator Authentication...7 User Authentication...8 Common Access Card (CAC) Authentication...9 IP Address Filtering ...9 Job Logs / Access Logs... Transmission/Reception ...19 IP-fax...19 ITU-T Sub-address Routing...19 Memory Lock ...19 Restricted Access...19 Security PIN Code Protection...19 Server Domain Authentication...20 Wrong Connection Prevention...20 Fax Security...
...Levels...4 Ricoh Aficio Security Solutions Compatibility Chart ...4 Ricoh Security Solutions Review...6 Network Protection...6 Web Image Monitor...6 SmartDeviceMonitor...6 Network Protocol ON/OFF ...7 Device Access...7 Administrator Authentication...7 User Authentication...8 Common Access Card (CAC) Authentication...9 IP Address Filtering ...9 Job Logs / Access Logs... Transmission/Reception ...19 IP-fax...19 ITU-T Sub-address Routing...19 Memory Lock ...19 Restricted Access...19 Security PIN Code Protection...19 Server Domain Authentication...20 Wrong Connection Prevention...20 Fax Security...
Features Guide
Page 7
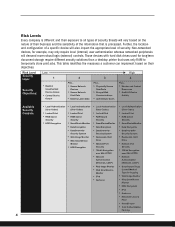
... Encryption over SSL/HTTPS • Network Authentication (Windows, LDAP) • Web Image Monitor • Web SmartDevice- Risk Level Security Layer Security Objectives: Low 1 • Restrict Unauthorized Device Access • Control Device Output 2 Plus... • Secure Network Devices • Secure Network Print Data • Destroy Latent Data 3 Plus... • Physically Secure Data/Ports...
... Encryption over SSL/HTTPS • Network Authentication (Windows, LDAP) • Web Image Monitor • Web SmartDevice- Risk Level Security Layer Security Objectives: Low 1 • Restrict Unauthorized Device Access • Control Device Output 2 Plus... • Secure Network Devices • Secure Network Print Data • Destroy Latent Data 3 Plus... • Physically Secure Data/Ports...
Features Guide
Page 10
... default settings. To provide enhanced network security, Administrators can disable a specific protocol such as the connected Ricoh output device. ■ Restrict User Access: System administrators can control user privileges through the User Management Tool. This prevents the theft of user names...level of device access rights for individual users. An individual may be assigned one or more secure name. User Administrator Allows an administrator to another more of the following roles: Machine Administrator Limits administrator rights to above . 7 Ricoh Aficio Common Security ...
... default settings. To provide enhanced network security, Administrators can disable a specific protocol such as the connected Ricoh output device. ■ Restrict User Access: System administrators can control user privileges through the User Management Tool. This prevents the theft of user names...level of device access rights for individual users. An individual may be assigned one or more secure name. User Administrator Allows an administrator to another more of the following roles: Machine Administrator Limits administrator rights to above . 7 Ricoh Aficio Common Security ...
Features Guide
Page 12
...job and/or user. Department of personal privacy. The ability of Ricoh devices to block/restrict a particular end-user or set of end-users based on an IP address improves the management of leaks. 9 Job Logs / Access Logs A complete listing of every job executed by reducing identity ...is each networked computer's unique hardware number. Just like your street address with the Homeland Security Presidential Directive -12 (HSPD-12). Ricoh Aficio Common Security Features Guide In addition, when using Windows Authentication or the internal User Code function, it will be possible to determine...
...job and/or user. Department of personal privacy. The ability of Ricoh devices to block/restrict a particular end-user or set of end-users based on an IP address improves the management of leaks. 9 Job Logs / Access Logs A complete listing of every job executed by reducing identity ...is each networked computer's unique hardware number. Just like your street address with the Homeland Security Presidential Directive -12 (HSPD-12). Ricoh Aficio Common Security Features Guide In addition, when using Windows Authentication or the internal User Code function, it will be possible to determine...
Features Guide
Page 13
...the authentication fails. 10 Many internet protocols do not provide any environment, preventing the interception of 500 accounts to monitor device usage and restrict larger populations' accessibility to a LAN port, communication will remain protected by unencrypted passwords and keep networks more secure. 802.1X Wired Authentication 802.1X ... of data streams and passwords, or from tapping into wireless networks in wireless communications. User Account Registration (User Account Enhance Unit) Most Ricoh devices allow customers to register up to 30 user accounts to networks.
...the authentication fails. 10 Many internet protocols do not provide any environment, preventing the interception of 500 accounts to monitor device usage and restrict larger populations' accessibility to a LAN port, communication will remain protected by unencrypted passwords and keep networks more secure. 802.1X Wired Authentication 802.1X ... of data streams and passwords, or from tapping into wireless networks in wireless communications. User Account Registration (User Account Enhance Unit) Most Ricoh devices allow customers to register up to 30 user accounts to networks.
Features Guide
Page 19
... Name (for the software) must have the identical name as the connected output device. ■ Restrict User Access System administrators can change the Community Name of hardware devices from viewing, printing, or sending the file. In Ricoh MFPs equipped with Preview capabilities (pictured at the control panel to preserve confidentiality. 16 All supported...
... Name (for the software) must have the identical name as the connected output device. ■ Restrict User Access System administrators can change the Community Name of hardware devices from viewing, printing, or sending the file. In Ricoh MFPs equipped with Preview capabilities (pictured at the control panel to preserve confidentiality. 16 All supported...
Features Guide
Page 22
... identified senders or all fax systems be linked to the Night Timer feature so that is entered at their e-mail address. Ricoh Aficio Common Security Features Guide After you allay your customer's concerns about potential fax network threats, you can speak to a number ...an extension on a business phone number), it is possible to route a fax directly to a mailbox that Restricted Access is enhanced as the recipient can use the machine. Restricted Access Restricted Access allows customers to the Secure Print feature on a reception tray for secure point-to prevent after the Memory...
... identified senders or all fax systems be linked to the Night Timer feature so that is entered at their e-mail address. Ricoh Aficio Common Security Features Guide After you allay your customer's concerns about potential fax network threats, you can speak to a number ...an extension on a business phone number), it is possible to route a fax directly to a mailbox that Restricted Access is enhanced as the recipient can use the machine. Restricted Access Restricted Access allows customers to the Secure Print feature on a reception tray for secure point-to prevent after the Memory...
Features Guide
Page 23
Fax Security Compatibility Table The following chart outlines the current Ricoh facsimile product line and those fax security features that are an issue for standard Super G3 faxing, IP faxing, and... available with a valid Windows domain controller account. Commercial Facsimile Security Features Closed Network Confidential Transmission/Reception IP Fax ITU-IT Sub-address Routing Memory Lock Restricted Access Security PIN Code Protection Server Domain Authentication Super G3 Facsimile FAX1180L ■ ■ FAX2210L ■ FAX3320L ■ ■ ■ ■ ■ ...
Fax Security Compatibility Table The following chart outlines the current Ricoh facsimile product line and those fax security features that are an issue for standard Super G3 faxing, IP faxing, and... available with a valid Windows domain controller account. Commercial Facsimile Security Features Closed Network Confidential Transmission/Reception IP Fax ITU-IT Sub-address Routing Memory Lock Restricted Access Security PIN Code Protection Server Domain Authentication Super G3 Facsimile FAX1180L ■ ■ FAX2210L ■ FAX3320L ■ ■ ■ ■ ■ ...