Security Target
Page 5
All rights reserved. Page 4 of 93 7.3 Document Access Control Function 84 7.4 Use-of-Feature Restriction Function 86 7.5 Network Protection Function 87 7.6 Residual Data Overwrite Function 87 7.7 Stored Data Protection Function 88 7.8 Security Management Function 88 7.9 Software Verification Function 93 7.10 Fax Line Separation Function 93 Copyright (c) 2011 RICOH COMPANY, LTD.
All rights reserved. Page 4 of 93 7.3 Document Access Control Function 84 7.4 Use-of-Feature Restriction Function 86 7.5 Network Protection Function 87 7.6 Residual Data Overwrite Function 87 7.7 Stored Data Protection Function 88 7.8 Security Management Function 88 7.9 Software Verification Function 93 7.10 Fax Line Separation Function 93 Copyright (c) 2011 RICOH COMPANY, LTD.
Security Target
Page 8
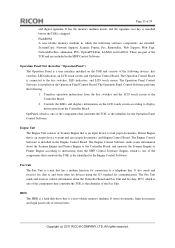
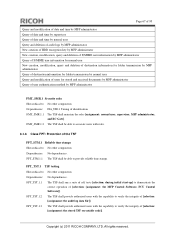
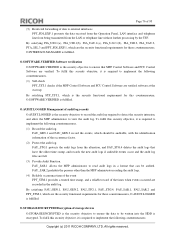
... versions consist of the TOE. Table 1 : Identification Information of TOE Names Ricoh Aficio MP C3001, Ricoh Aficio MP C3501, Ricoh Aficio MP C3001G, Ricoh Aficio MP C3501G, Gestetner MP C3001, Gestetner MP C3501, Lanier MP C3001, Lanier MP C3501, Lanier LD630C, Lanier LD635C, Lanier LD630CG, Lanier LD635CG, nashuatec MP C3001, nashuatec MP C3501, Rex-Rotary MP C3001, Rex-Rotary MP C3501, MFPs Versions Software System/Copy Network Support Scanner Printer Fax RemoteFax Web Support Web Uapl...
... versions consist of the TOE. Table 1 : Identification Information of TOE Names Ricoh Aficio MP C3001, Ricoh Aficio MP C3501, Ricoh Aficio MP C3001G, Ricoh Aficio MP C3501G, Gestetner MP C3001, Gestetner MP C3501, Lanier MP C3001, Lanier MP C3501, Lanier LD630C, Lanier LD635C, Lanier LD630CG, Lanier LD635CG, nashuatec MP C3001, nashuatec MP C3501, Rex-Rotary MP C3001, Rex-Rotary MP C3501, MFPs Versions Software System/Copy Network Support Scanner Printer Fax RemoteFax Web Support Web Uapl...
Security Target
Page 10
... following operations from the Operation Panel of TOE Environment The TOE is the TOE itself, and hardware and software other than the TOE. Copy, fax, storage, and network transmission of paper documents, - Copyright (c) 2011 RICOH COMPANY, LTD. LAN Network used by connecting to the office LAN, and users can store it as...
... following operations from the Operation Panel of TOE Environment The TOE is the TOE itself, and hardware and software other than the TOE. Copy, fax, storage, and network transmission of paper documents, - Copyright (c) 2011 RICOH COMPANY, LTD. LAN Network used by connecting to the office LAN, and users can store it as...
Security Target
Page 12
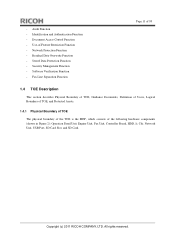
Network Protection Function - Software Verification Function - Use-of the following hardware components (shown in Figure 2): Operation Panel Unit, Engine Unit, Fax Unit, Controller Board, HDD, Ic Ctlr, Network Unit, USB Port, SD Card Slot, and SD Card. Security Management Function - Document Access Control Function - Copyright (c) 2011 RICOH COMPANY, LTD. Residual Data Overwrite Function...
Network Protection Function - Software Verification Function - Use-of the following hardware components (shown in Figure 2): Operation Panel Unit, Engine Unit, Fax Unit, Controller Board, HDD, Ic Ctlr, Network Unit, USB Port, SD Card Slot, and SD Card. Security Management Function - Document Access Control Function - Copyright (c) 2011 RICOH COMPANY, LTD. Residual Data Overwrite Function...
Security Target
Page 13
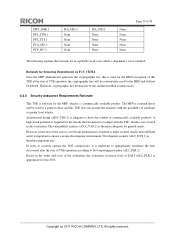
... is used as compressing/decompressing the image data. All rights reserved. The following describes the components of random number generation, cryptographic key generation Copyright (c) 2011 RICOH COMPANY, LTD. NVRAM A non-volatile memory medium in which is stored. - It can also be used to control the MFP is a device that performs basic... to control the MFP. Page 12 of 93 Figure 2 : Hardware Configuration of the TOE Controller Board The Controller Board is processed by the MFP Control Software on the Controller Board.
... is used as compressing/decompressing the image data. All rights reserved. The following describes the components of random number generation, cryptographic key generation Copyright (c) 2011 RICOH COMPANY, LTD. NVRAM A non-volatile memory medium in which is stored. - It can also be used to control the MFP is a device that performs basic... to control the MFP. Page 12 of 93 Figure 2 : Hardware Configuration of the TOE Controller Board The Controller Board is processed by the MFP Control Software on the Controller Board.
Security Target
Page 14
...to print and eject paper documents, and Engine Control Board. Engine, which the following : 1. Copyright (c) 2011 RICOH COMPANY, LTD. The Engine Control Software sends status information about the Controller Board and Fax Unit and fax data. Page 13 of the following devices: ...the Controller Board, and operates the Scanner Engine or Printer Engine according to and from the MFP Control Software. The Operation Panel Control Software performs the following software components are part of normal users. These are installed: System/Copy, Network Support, Scanner, Printer, Fax...
...to print and eject paper documents, and Engine Control Board. Engine, which the following : 1. Copyright (c) 2011 RICOH COMPANY, LTD. The Engine Control Software sends status information about the Controller Board and Fax Unit and fax data. Page 13 of the following devices: ...the Controller Board, and operates the Scanner Engine or Printer Engine according to and from the MFP Control Software. The Operation Panel Control Software performs the following software components are part of normal users. These are installed: System/Copy, Network Support, Scanner, Printer, Fax...
Security Target
Page 15
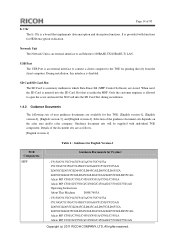
.../C9155A C9130G/C9135G/C9145G/C9145AG/C9155G/C9155AG LD630C/LD635C/LD645C/LD645CA/LD655C/LD655CA LD630CG/LD635CG/LD645CG/LD645CAG/LD655CG/LD655CAG Aficio MP C3001/C3501/C4501/C4501A/C5501/C5501A Aficio MP C3001G/C3501G/C4501G/C4501AG/C5501G/C5501AG Copyright (c) 2011 RICOH COMPANY, LTD. Only the customer engineer is allowed to open the cover and insert the SD Card into...-1], [English version-2], [English version-3], and [English version-4]. Network Unit The Network Unit is a board that is a memory medium in which Data Erase Std (MFP Control Software) are stored.
.../C9155A C9130G/C9135G/C9145G/C9145AG/C9155G/C9155AG LD630C/LD635C/LD645C/LD645CA/LD655C/LD655CA LD630CG/LD635CG/LD645CG/LD645CAG/LD655CG/LD655CAG Aficio MP C3001/C3501/C4501/C4501A/C5501/C5501A Aficio MP C3001G/C3501G/C4501G/C4501AG/C5501G/C5501AG Copyright (c) 2011 RICOH COMPANY, LTD. Only the customer engineer is allowed to open the cover and insert the SD Card into...-1], [English version-2], [English version-3], and [English version-4]. Network Unit The Network Unit is a board that is a memory medium in which Data Erase Std (MFP Control Software) are stored.
Security Target
Page 27
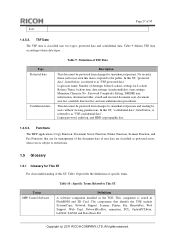
...this function can be used to be protected by the TOE are user data, TSF data, and functions. 1.4.5.1. Copyright (c) 2011 RICOH COMPANY, LTD. Fax Line Separation Function The Fax Line Separation Function is to restrict input information from the telephone lines to specify... through encrypted communication with RC Gate, encrypted communication is used. Software Verification Function The Software Verification Function is to verify the integrity of the executable codes of the MFP Control Software and FCU Control Software and to overwrite specific patterns on the HDD. Table 8 :...
...this function can be used to be protected by the TOE are user data, TSF data, and functions. 1.4.5.1. Copyright (c) 2011 RICOH COMPANY, LTD. Fax Line Separation Function The Fax Line Separation Function is to restrict input information from the telephone lines to specify... through encrypted communication with RC Gate, encrypted communication is used. Software Verification Function The Software Verification Function is to verify the integrity of the executable codes of the MFP Control Software and FCU Control Software and to overwrite specific patterns on the HDD. Table 8 :...
Security Target
Page 28
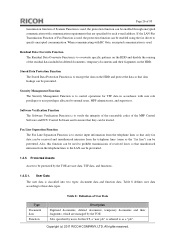
...even this data is classified into two types: protected data and confidential data. Login password, audit log, and HDD cryptographic key. 1.4.5.3. Copyright (c) 2011 RICOH COMPANY, LTD. TSF Data The TSF data is exposed to the public. Table 9 defines TSF data according to as "TSF confidential data". Login user... management of the document data of user data are classified as protected assets, whose use is referred to This ST Definitions A software component installed in FlashROM and SD Card. Type Protected data Confidential data Table 9 : Definition of specific terms. Terms MFP Control...
...even this data is classified into two types: protected data and confidential data. Login password, audit log, and HDD cryptographic key. 1.4.5.3. Copyright (c) 2011 RICOH COMPANY, LTD. TSF Data The TSF data is exposed to the public. Table 9 defines TSF data according to as "TSF confidential data". Login user... management of the document data of user data are classified as protected assets, whose use is referred to This ST Definitions A software component installed in FlashROM and SD Card. Type Protected data Confidential data Table 9 : Definition of specific terms. Terms MFP Control...
Security Target
Page 38
P.SOFTWARE.VERIFICATION Software verification Procedures shall exist to self-verify executable code in a restricted or monitored area that provides protection from unauthorised disclosure or alteration, and shall be ... and security-relevant events. P.AUDIT.LOGGING Management of audit log records The TOE shall create and maintain a log of TOE use the TOE. Copyright (c) 2011 RICOH COMPANY, LTD. 3.2 Organisational Security Policies The following organisational security policies are taken: Page 37 of 93 P.USER.AUTHORIZATION User identification and authentication Only users with...
P.SOFTWARE.VERIFICATION Software verification Procedures shall exist to self-verify executable code in a restricted or monitored area that provides protection from unauthorised disclosure or alteration, and shall be ... and security-relevant events. P.AUDIT.LOGGING Management of audit log records The TOE shall create and maintain a log of TOE use the TOE. Copyright (c) 2011 RICOH COMPANY, LTD. 3.2 Organisational Security Policies The following organisational security policies are taken: Page 37 of 93 P.USER.AUTHORIZATION User identification and authentication Only users with...
Security Target
Page 41
O.SOFTWARE.VERIFIED Software verification The TOE shall provide procedures to use and security-relevant events in the MFP and prevent its unauthorised disclosure or alteration. OE.AUDIT_ACCESS.AUTHORIZED ... path between itself and RC Gate, and detect any tampering with RC Gate The TOE shall conceal the communication data on the HDD. Copyright (c) 2011 RICOH COMPANY, LTD. O.RCGATE.COMM.PROTECT Protection of communication with those communication data. 4.2 Security Objectives of Operational Environment This section describes the security objectives of the...
O.SOFTWARE.VERIFIED Software verification The TOE shall provide procedures to use and security-relevant events in the MFP and prevent its unauthorised disclosure or alteration. OE.AUDIT_ACCESS.AUTHORIZED ... path between itself and RC Gate, and detect any tampering with RC Gate The TOE shall conceal the communication data on the HDD. Copyright (c) 2011 RICOH COMPANY, LTD. O.RCGATE.COMM.PROTECT Protection of communication with those communication data. 4.2 Security Objectives of Operational Environment This section describes the security objectives of the...
Security Target
Page 43
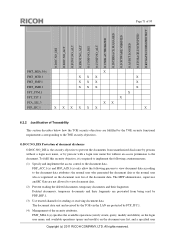
...O.DOC.NO_ALT O.FUNC.NO_ALT O.PROT.NO_ALT O.CONF.NO_DIS O.CONF.NO_ALT O.USER.AUTHORIZED OE.USER.AUTHORIZED O.SOFTWARE.VERIFIED O.AUDIT.LOGGED OE.AUDIT_STORAGE.PROTCTED OE.AUDIT_ACCESS_AUTHORIZED OE.AUDIT.REVIEWED O.INTERFACE.MANAGED OE.PHYSICAL.MANAGED OE.... X X X T.FUNC.ALT X X X T.PROT.ALT X X X T.CONF.DIS X X X T.CONF.ALT X X X P.USER.AUTHORIZATION X X P.SOFTWARE.VERIFICATION X P.AUDIT.LOGGING X XXX P.INTERFACE.MANAGEMENT X X P.STORAGE.ENCRYPTION X P.RCGATE.COMM.PROTECT X A.ACCESS.MANAGED X A.ADMIN.TRAINING X A.ADMIN.TRUST X A.USER.TRAINING X Copyright (c) ...
...O.DOC.NO_ALT O.FUNC.NO_ALT O.PROT.NO_ALT O.CONF.NO_DIS O.CONF.NO_ALT O.USER.AUTHORIZED OE.USER.AUTHORIZED O.SOFTWARE.VERIFIED O.AUDIT.LOGGED OE.AUDIT_STORAGE.PROTCTED OE.AUDIT_ACCESS_AUTHORIZED OE.AUDIT.REVIEWED O.INTERFACE.MANAGED OE.PHYSICAL.MANAGED OE.... X X X T.FUNC.ALT X X X T.PROT.ALT X X X T.CONF.DIS X X X T.CONF.ALT X X X P.USER.AUTHORIZATION X X P.SOFTWARE.VERIFICATION X P.AUDIT.LOGGING X XXX P.INTERFACE.MANAGEMENT X X P.STORAGE.ENCRYPTION X P.RCGATE.COMM.PROTECT X A.ACCESS.MANAGED X A.ADMIN.TRAINING X A.ADMIN.TRUST X A.USER.TRAINING X Copyright (c) ...
Security Target
Page 45
... to users who follow the security policies and procedures of their organisation. T.CONF.ALT is enforced by these objectives. Copyright (c) 2011 RICOH COMPANY, LTD. By OE.USER.AUTHORIZED, the responsible manager of MFP gives the authority to use the TOE to users who follow... is countered by O.CONF.NO_ALT, O.USER.AUTHORIZED and OE.USER.AUTHORIZED. T.CONF.DIS T.CONF.DIS is enforced by O.SOFTWARE.VERIFIED. SOFTWARE.VERIFICATION P.SOFTWARE.VERIFICATION is countered by O.CONF.NO_DIS, O.USER.AUTHORIZED and OE.USER.AUTHORIZED. All rights reserved. P.USER.AUTHORIZATION is countered by ...
... to users who follow the security policies and procedures of their organisation. T.CONF.ALT is enforced by these objectives. Copyright (c) 2011 RICOH COMPANY, LTD. By OE.USER.AUTHORIZED, the responsible manager of MFP gives the authority to use the TOE to users who follow... is countered by O.CONF.NO_ALT, O.USER.AUTHORIZED and OE.USER.AUTHORIZED. T.CONF.DIS T.CONF.DIS is enforced by O.SOFTWARE.VERIFIED. SOFTWARE.VERIFICATION P.SOFTWARE.VERIFICATION is countered by O.CONF.NO_DIS, O.USER.AUTHORIZED and OE.USER.AUTHORIZED. All rights reserved. P.USER.AUTHORIZATION is countered by ...
Security Target
Page 68
Dependencies: FIA_UID.1 Timing of [selection: [assignment: the MFP Control Software, FCU Control Software]]. FPT_TST.1 TSF testing Hierarchical to : No other components. Dependencies: No dependencies. FPT_TST.1.1 The TSF shall run a suite of self tests [selection: during ... FPT_STM.1 Reliable time stamps Hierarchical to : No other components. FPT_STM.1.1 The TSF shall be able to provide reliable time stamps. Copyright (c) 2011 RICOH COMPANY, LTD. Page 67 of 93 Query and modification of date and time by MFP administrator Query of date and time by supervisor Query of...
Dependencies: FIA_UID.1 Timing of [selection: [assignment: the MFP Control Software, FCU Control Software]]. FPT_TST.1 TSF testing Hierarchical to : No other components. Dependencies: No dependencies. FPT_TST.1.1 The TSF shall run a suite of self tests [selection: during ... FPT_STM.1 Reliable time stamps Hierarchical to : No other components. FPT_STM.1.1 The TSF shall be able to provide reliable time stamps. Copyright (c) 2011 RICOH COMPANY, LTD. Page 67 of 93 Query and modification of date and time by MFP administrator Query of date and time by supervisor Query of...
Security Target
Page 71
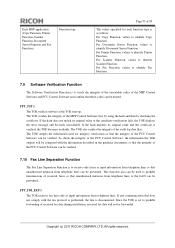
... Table 32 : Relationship between Security Objectives and Functional Requirements O.DOC.NO_DI S O.DOC.NO_ALT O.FUNC.NO_ALT O.PROT.NO_ALT O.CONF.NO_DI S O.CONF.NO_ALT O.USER.AUTHORIZED O.INTERFACE.MANAGED O.SOFTWARE.VERIFIED O.AUDIT.LOGGED O.STORAGE.ENCRYPTED O.RCGATE.COMM.PROTECT FAU_GEN.1 FAU_GEN.2 FAU_STG.1 FAU_STG.4 FAU_SAR.1 FAU_SAR.2 FCS_CKM.1 FCS_COP.1 FDP_ACC.1(a) X X X FDP_ACC.1(b) FDP_ACF.1(a) X X X FDP_ACF.1(b) FDP_RIP.1 X X FIA_AFL.1 FIA_ATD.1 FIA_SOS.1 FIA_UAU...
... Table 32 : Relationship between Security Objectives and Functional Requirements O.DOC.NO_DI S O.DOC.NO_ALT O.FUNC.NO_ALT O.PROT.NO_ALT O.CONF.NO_DI S O.CONF.NO_ALT O.USER.AUTHORIZED O.INTERFACE.MANAGED O.SOFTWARE.VERIFIED O.AUDIT.LOGGED O.STORAGE.ENCRYPTED O.RCGATE.COMM.PROTECT FAU_GEN.1 FAU_GEN.2 FAU_STG.1 FAU_STG.4 FAU_SAR.1 FAU_SAR.2 FCS_CKM.1 FCS_COP.1 FDP_ACC.1(a) X X X FDP_ACC.1(b) FDP_ACF.1(a) X X X FDP_ACF.1(b) FDP_RIP.1 X X FIA_AFL.1 FIA_ATD.1 FIA_SOS.1 FIA_UAU...
Security Target
Page 72
... security objective, it is registered on the document user list, and a specified user Copyright (c) 2011 RICOH COMPANY, LTD. The document data sent and received by the TOE via the LAN are protected by ... document data. All rights reserved. Page 71 of 93 O.DOC.NO_DI S O.DOC.NO_ALT O.FUNC.NO_ALT O.PROT.NO_ALT O.CONF.NO_DI S O.CONF.NO_ALT O.USER.AUTHORIZED O.INTERFACE.MANAGED O.SOFTWARE.VERIFIED O.AUDIT.LOGGED O.STORAGE.ENCRYPTED O.RCGATE.COMM.PROTECT FMT_MSA.3(b) FMT_MTD.1 FMT_SMF.1 FMT_SMR.1 FPT_STM.1 FPT_TST.1 FTA_SSL.3 FTP_ITC.1 X X X X X X X X X X X X X X X X X X X X X X X ...
... security objective, it is registered on the document user list, and a specified user Copyright (c) 2011 RICOH COMPANY, LTD. The document data sent and received by the TOE via the LAN are protected by ... document data. All rights reserved. Page 71 of 93 O.DOC.NO_DI S O.DOC.NO_ALT O.FUNC.NO_ALT O.PROT.NO_ALT O.CONF.NO_DI S O.CONF.NO_ALT O.USER.AUTHORIZED O.INTERFACE.MANAGED O.SOFTWARE.VERIFIED O.AUDIT.LOGGED O.STORAGE.ENCRYPTED O.RCGATE.COMM.PROTECT FMT_MSA.3(b) FMT_MTD.1 FMT_SMF.1 FMT_SMR.1 FPT_STM.1 FPT_TST.1 FTA_SSL.3 FTP_ITC.1 X X X X X X X X X X X X X X X X X X X X X X X ...
Security Target
Page 77
...FAU_GEN.2, FAU_STG.1, FAU_STG.4, FAU_SAR.1, FAU_SAR.2 and FPT_STM.1, which should be written into the HDD is fulfilled. Copyright (c) 2011 RICOH COMPANY, LTD. FAU_GEN.1 and FAU_GEN.2 record the events, which are the security functional requirements for these countermeasures, O.AUDIT....log files are the security functional requirements for these countermeasures, O.INTERFACE.MANAGED is encrypted. To fulfil this countermeasure, O.SOFTWARE.VERIFIED is required to implement the following countermeasures. O.AUDIT.LOGGED Management of data to external interfaces. Page 76 of...
...FAU_GEN.2, FAU_STG.1, FAU_STG.4, FAU_SAR.1, FAU_SAR.2 and FPT_STM.1, which should be written into the HDD is fulfilled. Copyright (c) 2011 RICOH COMPANY, LTD. FAU_GEN.1 and FAU_GEN.2 record the events, which are the security functional requirements for these countermeasures, O.AUDIT....log files are the security functional requirements for these countermeasures, O.INTERFACE.MANAGED is encrypted. To fulfil this countermeasure, O.SOFTWARE.VERIFIED is required to implement the following countermeasures. O.AUDIT.LOGGED Management of data to external interfaces. Page 76 of...
Security Target
Page 80
Copyright (c) 2011 RICOH COMPANY, LTD. A high attack potential is required for the attacks that circumvent or tamper with the possibility of moderate or greater level attacks. The MFP ... discovered after the start of TOE operation, the cryptographic key will be continuously used for the HDD and will be deleted. Development security (ALC_DVS.1) is software for general needs. Based on FCS_CKM.4 Once the MFP administrator generates the cryptographic key that is used for the HDD encryption of this TOE. Therefore...
Copyright (c) 2011 RICOH COMPANY, LTD. A high attack potential is required for the attacks that circumvent or tamper with the possibility of moderate or greater level attacks. The MFP ... discovered after the start of TOE operation, the cryptographic key will be continuously used for the HDD and will be deleted. Development security (ALC_DVS.1) is software for general needs. Based on FCS_CKM.4 Once the MFP administrator generates the cryptographic key that is used for the HDD encryption of this TOE. Therefore...
Security Target
Page 94
..., values to identify Scanner Function. FPT_TST.1 The TOE verifies software at the TOE start-up. The TOE also verifies the ... lines to prohibit transmissions of the MFP Control Software and FCU Control Software and confirm that the integrity of received fax ... Function. The TOE verifies the integrity of the FCU Control Software can be verified. If the hash does not match its original...so that the integrity of the MFP Control Software first by using the hash and then by ...the integrity of the FCU Control Software, the information the TOE outputs will not be trusted. Since the...
..., values to identify Scanner Function. FPT_TST.1 The TOE verifies software at the TOE start-up. The TOE also verifies the ... lines to prohibit transmissions of the MFP Control Software and FCU Control Software and confirm that the integrity of received fax ... Function. The TOE verifies the integrity of the FCU Control Software can be verified. If the hash does not match its original...so that the integrity of the MFP Control Software first by using the hash and then by ...the integrity of the FCU Control Software, the information the TOE outputs will not be trusted. Since the...