Security Target
Page 5
All Rights Reserved. Page 5 of 80 7.1.2.3 Password Feedback Area Protection 67 7.1.2.4 Password Registration...67 7.1.3 SF.DOC_ACC Document Data Access Control Function 68 7.1.3.1 General User Operations on Document Data 68 7.1.3.2 File Administrator Operations on Document Data 69 7.1.4 SF.... for Intrusion via Telephone Line 74 7.1.9 SF.GENUINE MFP Control Software Verification Function 74 8 Appendix ...76 8.1 Definitions of Terminology 76 8.2 References ...80 Copyright (c) 2009,2010 RICOH COMPANY, LTD.
All Rights Reserved. Page 5 of 80 7.1.2.3 Password Feedback Area Protection 67 7.1.2.4 Password Registration...67 7.1.3 SF.DOC_ACC Document Data Access Control Function 68 7.1.3.1 General User Operations on Document Data 68 7.1.3.2 File Administrator Operations on Document Data 69 7.1.4 SF.... for Intrusion via Telephone Line 74 7.1.9 SF.GENUINE MFP Control Software Verification Function 74 8 Appendix ...76 8.1 Definitions of Terminology 76 8.2 References ...80 Copyright (c) 2009,2010 RICOH COMPANY, LTD.
Security Target
Page 15
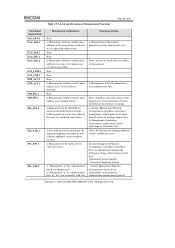
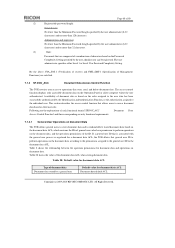
...Explanation about duties involved Managing general users. When the TOE is registered on the document data. Copyright (c) 2009,2010 RICOH COMPANY, LTD. The responsible manager of selecting the TOE administrators and TOE supervisor. Table 1: List of the following ...and/or file administration. 1.4.3.2 Administrator An "administrator" is a user who is being installed, the administrators who manages administrator passwords and changes them. The person selected to four administrators and one or more administrators. When selecting administrators, the responsible manager assigns...
...Explanation about duties involved Managing general users. When the TOE is registered on the document data. Copyright (c) 2009,2010 RICOH COMPANY, LTD. The responsible manager of selecting the TOE administrators and TOE supervisor. Table 1: List of the following ...and/or file administration. 1.4.3.2 Administrator An "administrator" is a user who is being installed, the administrators who manages administrator passwords and changes them. The person selected to four administrators and one or more administrators. When selecting administrators, the responsible manager assigns...
Security Target
Page 19
... delete the recorded audit logs. For editing permission, the same operation on the document data. It prompts the users to register passwords that are outside the TOE. Copyright (c) 2009,2010 RICOH COMPANY, LTD. The Identification and Authentication Function includes the following: - Each of these operations is permitted as follows: Reading document data...
... delete the recorded audit logs. For editing permission, the same operation on the document data. It prompts the users to register passwords that are outside the TOE. Copyright (c) 2009,2010 RICOH COMPANY, LTD. The Identification and Authentication Function includes the following: - Each of these operations is permitted as follows: Reading document data...
Security Target
Page 21
... machine administrator to add and delete administrator roles, and change , and delete general user information. - Copyright (c) 2009,2010 RICOH COMPANY, LTD. All Rights Reserved. Management of administrator information Allows specified users to register and delete administrators, to perform maintenance...users with full control permissions can change the document file owners. Management of supervisor information Superv isor can change administrator passwords. Only file administrators can change their user IDs. 4. Only administrators are required to them in document data. ...
... machine administrator to add and delete administrator roles, and change , and delete general user information. - Copyright (c) 2009,2010 RICOH COMPANY, LTD. All Rights Reserved. Management of administrator information Allows specified users to register and delete administrators, to perform maintenance...users with full control permissions can change the document file owners. Management of supervisor information Superv isor can change administrator passwords. Only file administrators can change their user IDs. 4. Only administrators are required to them in document data. ...
Security Target
Page 43
...Timing of identification. All Rights Reserved. FIA_SOS.1 Verification of secrets Hierarchical to the user while the Copyright (c) 2009,2010 RICOH COMPANY, LTD. For administrators and a supervisor No fewer than 128 characters. The user administrator specifies either Level 1 ...letter of authentication. FIA_UAU.7.1 The TSF shall provide only [assignment: displaying a dummy letter (*: asterisks, or : bullets) for Password Complexity Setting. FIA_UAU.7 Protected authentication feedback Hierarchical to be registered. FIA_SOS.1.1 The TSF shall provide a mechanism to verify that ...
...Timing of identification. All Rights Reserved. FIA_SOS.1 Verification of secrets Hierarchical to the user while the Copyright (c) 2009,2010 RICOH COMPANY, LTD. For administrators and a supervisor No fewer than 128 characters. The user administrator specifies either Level 1 ...letter of authentication. FIA_UAU.7.1 The TSF shall provide only [assignment: displaying a dummy letter (*: asterisks, or : bullets) for Password Complexity Setting. FIA_UAU.7 Protected authentication feedback Hierarchical to be registered. FIA_SOS.1.1 The TSF shall provide a mechanism to verify that ...
Security Target
Page 47
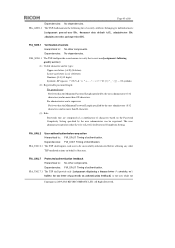
...the following Management Functions: [assignment: list of specifications of Management Function Hierarchical to: No other components. second) TSF data Operations Que ry Minimum Password Length Password Complexity Setting HDD cryptographic key Audit logs Service mode lock setting Query, modify Query, modify Query, newly create Query, delete entirely Query, modify... of S/MIME user information General users User administrator, General users FMT_SMF.1 Specification of Management Functions described in Table19 Copyright (c) 2009,2010 RICOH COMPANY, LTD. Dependencies: No dependencies.
...the following Management Functions: [assignment: list of specifications of Management Function Hierarchical to: No other components. second) TSF data Operations Que ry Minimum Password Length Password Complexity Setting HDD cryptographic key Audit logs Service mode lock setting Query, modify Query, modify Query, newly create Query, delete entirely Query, modify... of S/MIME user information General users User administrator, General users FMT_SMF.1 Specification of Management Functions described in Table19 Copyright (c) 2009,2010 RICOH COMPANY, LTD. Dependencies: No dependencies.
Security Target
Page 48
... from administrator roles. None: No functions for defining additional security attributes for users. Password Complexity Setting - All Rights Reserved. a) Management of the authentication data by an administrator, b) Management of general Copyright (c) ...2009,2010 RICOH COMPANY, LTD. a) Management of the threshold for unsuccessful authentication attempts. Minimum Password Length - a) Management of the file administrator from administrator roles. b) Management of users with this...
... from administrator roles. None: No functions for defining additional security attributes for users. Password Complexity Setting - All Rights Reserved. a) Management of the authentication data by an administrator, b) Management of general Copyright (c) ...2009,2010 RICOH COMPANY, LTD. a) Management of the threshold for unsuccessful authentication attempts. Minimum Password Length - a) Management of the file administrator from administrator roles. b) Management of users with this...
Security Target
Page 56
...functional requirements corresponding to O.I&A in Table 22, and these requirements are included to fulfil the O.DOC_ACC specification. To fulfil O.I &A, passwords for user authentication shall beprotected from the Operation Panel, the Web browser of a client computer, or a client computer when printing... specified by displaying masking characters (*: asterisks or : bullets) in place of each password character entered in the document data ACL of a document, Copyright (c) 2009,2010 RICOH COMPANY, LTD. For this , FIA_ATD.1 and FIA_USB.1 bind successfully identified and authenticated...
...functional requirements corresponding to O.I&A in Table 22, and these requirements are included to fulfil the O.DOC_ACC specification. To fulfil O.I &A, passwords for user authentication shall beprotected from the Operation Panel, the Web browser of a client computer, or a client computer when printing... specified by displaying masking characters (*: asterisks or : bullets) in place of each password character entered in the document data ACL of a document, Copyright (c) 2009,2010 RICOH COMPANY, LTD. For this , FIA_ATD.1 and FIA_USB.1 bind successfully identified and authenticated...
Security Target
Page 57
...To fulfil O.MANAGE, access to TSF data shall be limited to specified users only, and a default value shall be Copyright (c) 2009,2010 RICOH COMPANY, LTD. the machine administrator to query the date and time of the system clock and the service mode lock setting; - and -... change supervisor ID; - the user administrator and general users with full control operation permission for the document data to query and specify the Minimum Password Length, complexity setting, anda Lockout Flag for the document data to query, newly create, and change S/MIME user information; - a ) Management...
...To fulfil O.MANAGE, access to TSF data shall be limited to specified users only, and a default value shall be Copyright (c) 2009,2010 RICOH COMPANY, LTD. the machine administrator to query the date and time of the system clock and the service mode lock setting; - and -... change supervisor ID; - the user administrator and general users with full control operation permission for the document data to query and specify the Minimum Password Length, complexity setting, anda Lockout Flag for the document data to query, newly create, and change S/MIME user information; - a ) Management...
Security Target
Page 64
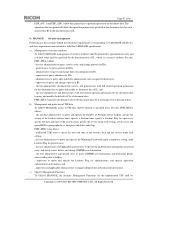
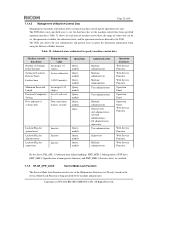
... audit log Audit logs Basic audit information - Communication IP address - -: No applicable expanded audit information Copyright (c) 2009,2010 RICOH COMPANY, LTD. Table 25 shows the audit information for the generation of auditable event occurs. ID of object document data ID...generation Successful storage of document data Successful reading of document data (*3) Successful deletion of document data Receiving fax Changing user password (including new creation and deletion) Deletion of administrator role Addition of administrator role Changing document data ACL Changing date and ...
... audit log Audit logs Basic audit information - Communication IP address - -: No applicable expanded audit information Copyright (c) 2009,2010 RICOH COMPANY, LTD. Table 25 shows the audit information for the generation of auditable event occurs. ID of object document data ID...generation Successful storage of document data Successful reading of document data (*3) Successful deletion of document data Receiving fax Changing user password (including new creation and deletion) Deletion of administrator role Addition of administrator role Changing document data ACL Changing date and ...
Security Target
Page 66
...methods for printing or transmitting faxes. Copyright (c) 2009,2010 RICOH COMPANY, LTD. Authentication methods vary according to their ID and password, and then identifies and authenticates the user based on the user ID and password sent from the client computer when the TOE receives a ... and maintains those bindings and associations. The TOE also identifies and authenticates the user based on the entered user IDs and passwords. Page 66 of failed identification and authentication attempts made under each ID, as described in "7.1.2.1 User Identification and Authentication". Check...
...methods for printing or transmitting faxes. Copyright (c) 2009,2010 RICOH COMPANY, LTD. Authentication methods vary according to their ID and password, and then identifies and authenticates the user based on the user ID and password sent from the client computer when the TOE receives a ... and maintains those bindings and associations. The TOE also identifies and authenticates the user based on the entered user IDs and passwords. Page 66 of failed identification and authentication attempts made under each ID, as described in "7.1.2.1 User Identification and Authentication". Check...
Security Target
Page 67
... to initiate lockout, and the lockout time has elapsed, then lockout will be registered or changed meets conditions (2) and (3). If it does not, the password is satisfied. 7.1.2.4 Password Registration The TOE provides a function for each letter of attempts specified to indefinite, lockout release will be performed by manual lockout release. (2) Manual Lockout... characters and its types: Upper-case letters: [A -Z] (26 letters) Lower-case letters: [a -z] (26 letters) Numbers: [0-9] (10 digits) Symbols: SP (space 33 symbols) Copyright (c) 2009,2010 RICOH COMPANY, LTD.
... to initiate lockout, and the lockout time has elapsed, then lockout will be registered or changed meets conditions (2) and (3). If it does not, the password is satisfied. 7.1.2.4 Password Registration The TOE provides a function for each letter of attempts specified to indefinite, lockout release will be performed by manual lockout release. (2) Manual Lockout... characters and its types: Upper-case letters: [A -Z] (26 letters) Lower-case letters: [a -z] (26 letters) Numbers: [0-9] (10 digits) Symbols: SP (space 33 symbols) Copyright (c) 2009,2010 RICOH COMPANY, LTD.
Security Target
Page 68
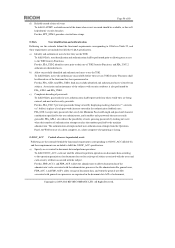
The user administrator specifies either Level 1 or Level 2 for document data ACL Document data default ACL Copyright (c) 2009,2010 RICOH COMPANY, LTD. This section describes the access control function that allows users to access document data based on document data. Table 2...data ACL, which contains the IDs of the document data ACL when storing document data. Administrators and supervisor No fewer than the Minimum Password Length specified by the user administrator (8-32 characters) and no more than 128 characters. Availability of document data is registered for document data...
The user administrator specifies either Level 1 or Level 2 for document data ACL Document data default ACL Copyright (c) 2009,2010 RICOH COMPANY, LTD. This section describes the access control function that allows users to access document data based on document data. Table 2...data ACL, which contains the IDs of the document data ACL when storing document data. Administrators and supervisor No fewer than the Minimum Password Length specified by the user administrator (8-32 characters) and no more than 128 characters. Availability of document data is registered for document data...
Security Target
Page 72
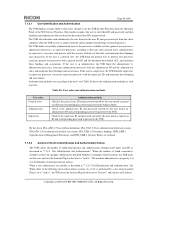
...to specify machine control data Machine control data items Number of Attempts before Lockout Setting for Lockout Release Timer Lockout time Minimum Password Length Password Complexity Setting Date and time of system clock Range of setting value An integer 1-5 (times) Active or Inactive 1-9999...allowed by specified users only. All Rights Reserved. The TOE allows only specified users to Folder function. Copyright (c) 2009,2010 RICOH COMPANY, LTD. Table 32 shows for supervisor Inactive Inactive Inactive Query, modify Query, modify Query, modify Authorised setter Machine administrators...
...to specify machine control data Machine control data items Number of Attempts before Lockout Setting for Lockout Release Timer Lockout time Minimum Password Length Password Complexity Setting Date and time of system clock Range of setting value An integer 1-5 (times) Active or Inactive 1-9999...allowed by specified users only. All Rights Reserved. The TOE allows only specified users to Folder function. Copyright (c) 2009,2010 RICOH COMPANY, LTD. Table 32 shows for supervisor Inactive Inactive Inactive Query, modify Query, modify Query, modify Authorised setter Machine administrators...
Security Target
Page 77
... Fax Unit with network management responsibility. A function that data at a later time. There are Level 1 and Level 2 Password Complexity Settings. The user administrator is a person who is a person with instructions for sending e-mail using Simple Mail Transfer Protocol...assigning responsibility for management of the TOE's network connections. The control software on the Controller Board. Copyright (c) 2009,2010 RICOH COMPANY, LTD. The network administrator is employed by E-mail Memory Transmission User administration Definitions A server for fax communication....
... Fax Unit with network management responsibility. A function that data at a later time. There are Level 1 and Level 2 Password Complexity Settings. The user administrator is a person who is a person with instructions for sending e-mail using Simple Mail Transfer Protocol...assigning responsibility for management of the TOE's network connections. The control software on the Controller Board. Copyright (c) 2009,2010 RICOH COMPANY, LTD. The network administrator is employed by E-mail Memory Transmission User administration Definitions A server for fax communication....
Security Target
Page 78
...item of general user information and an identification code for identification and authentication of an administrator. Copyright (c) 2009,2010 RICOH COMPANY, LTD. All Rights Reserved. When this setting is inactive, Lockout can be updated by an administrator. Print... Definitions The number of consecutive failed authentication attempts that are given administrator roles and perform administrative operations accordingly. A password for identification and authentication of general users. Administrators and supervisor who prints the document data. A setting that enables...
...item of general user information and an identification code for identification and authentication of an administrator. Copyright (c) 2009,2010 RICOH COMPANY, LTD. All Rights Reserved. When this setting is inactive, Lockout can be updated by an administrator. Print... Definitions The number of consecutive failed authentication attempts that are given administrator roles and perform administrative operations accordingly. A password for identification and authentication of general users. Administrators and supervisor who prints the document data. A setting that enables...