User Guide
Page 26
CJQ609 You can check the machine's status and change the system settings, manage jobs, print the job history, and configure the authentication settings. • See Connecting the Machine/ System Settings or Web Image Monitor Help. 24 1. What You Can Do with This Machine You Can Monitor and Set the Machine Using a Computer Using Web Image Monitor, you can check which tray is running out of paper, register information in the Address Book, specify the network settings, configure and change the settings.
CJQ609 You can check the machine's status and change the system settings, manage jobs, print the job history, and configure the authentication settings. • See Connecting the Machine/ System Settings or Web Image Monitor Help. 24 1. What You Can Do with This Machine You Can Monitor and Set the Machine Using a Computer Using Web Image Monitor, you can check which tray is running out of paper, register information in the Address Book, specify the network settings, configure and change the settings.
User Guide
Page 39
... CJS015 1. [Home] key Press to the function keys as a factory default. Display panel Displays keys for each function, operation status, or messages. For details, see "Configuring function keys", Getting Started . 3.
... CJS015 1. [Home] key Press to the function keys as a factory default. Display panel Displays keys for each function, operation status, or messages. For details, see "Configuring function keys", Getting Started . 3.
User Guide
Page 52
Getting Started • Depending on your business details or the type of programs given above are just examples. For details, see "Functions Requiring Optional Configurations", Getting Started . • The names of documents to be scanned, registering a program cannot be registered. 2. You can assign any name to a program according to your objectives. • Depending on the options installed, some functions cannot be recommended. 50
Getting Started • Depending on your business details or the type of programs given above are just examples. For details, see "Functions Requiring Optional Configurations", Getting Started . • The names of documents to be scanned, registering a program cannot be registered. 2. You can assign any name to a program according to your objectives. • Depending on the options installed, some functions cannot be recommended. 50
User Guide
Page 80
... Storing Data in memory and makes one set of this function might not be available. For details about the Document Server, see "Functions Requiring Optional Configurations", Getting Started . 1. Depending on your model and which options are installed on the hard disk of copies.
... Storing Data in memory and makes one set of this function might not be available. For details about the Document Server, see "Functions Requiring Optional Configurations", Getting Started . 1. Depending on your model and which options are installed on the hard disk of copies.
User Guide
Page 82
TX] is not highlighted. 4. Specify a destination. When sending the same original to several destinations (broadcasting), specify the next destination. 80 Place the original into the ADF. 5. You can enter the destination's number or address directly or select from the Address Book by pressing the destination key. If you make a mistake, press the [Clear] key, and then enter again. 8. Configure the transmission settings such as "TX Mode" as scan size and resolution. 6. 4. Make sure [Immed. Fax 3. Make the scan settings such as necessary. 7.
TX] is not highlighted. 4. Specify a destination. When sending the same original to several destinations (broadcasting), specify the next destination. 80 Place the original into the ADF. 5. You can enter the destination's number or address directly or select from the Address Book by pressing the destination key. If you make a mistake, press the [Clear] key, and then enter again. 8. Configure the transmission settings such as "TX Mode" as scan size and resolution. 6. 4. Make sure [Immed. Fax 3. Make the scan settings such as necessary. 7.
User Guide
Page 95
... network environment, and the Standard TCP/IP port will be set to [LPT1]. • Manage Printers permission is displayed in the [Select Printer] dialog box. Configure the user code, default printer, and shared printer as an Administrators group member. 1. 5. For the information not included in the [License Agreement] dialog box. Click...
... network environment, and the Standard TCP/IP port will be set to [LPT1]. • Manage Printers permission is displayed in the [Select Printer] dialog box. Configure the user code, default printer, and shared printer as an Administrators group member. 1. 5. For the information not included in the [License Agreement] dialog box. Click...
User Guide
Page 107
... be accessible by all users. On the [Sharing] tab, select [Advanced Sharing...]. In the [Group or user names:] list, select "Everyone", and then click [Remove]. 7. Configure the access permissions for each group and user. 13. Right-click the folder, and then click [Properties]. Proceed to Folder 5. Specify one or more object...
... be accessible by all users. On the [Sharing] tab, select [Advanced Sharing...]. In the [Group or user names:] list, select "Everyone", and then click [Remove]. 7. Configure the access permissions for each group and user. 13. Right-click the folder, and then click [Properties]. Proceed to Folder 5. Specify one or more object...
User Guide
Page 108
... key for the classification you want to specify access privileges for the created shared folder If you want to grant access to access the folder, configure the folder as follows: 106 Check that [Program / Change] is selected. 4.
... key for the classification you want to specify access privileges for the created shared folder If you want to grant access to access the folder, configure the folder as follows: 106 Check that [Program / Change] is selected. 4.
User Guide
Page 123
.... 3. Select a document to Bottom], [Booklet], [Magazine] For details about each function, see Copy/ Document Server . 1. Up to 30 documents can specify on the Document Server. Configure print settings. 5. Press the [Start] key. 121 The maximum quantity that can be printed. 2. When printing two or more documents at a time, repeat step 1. Enter...
.... 3. Select a document to Bottom], [Booklet], [Magazine] For details about each function, see Copy/ Document Server . 1. Up to 30 documents can specify on the Document Server. Configure print settings. 5. Press the [Start] key. 121 The maximum quantity that can be printed. 2. When printing two or more documents at a time, repeat step 1. Enter...
User Guide
Page 184
... the network, be sure to install a device certificate (PDF with digital signature), see "Parameter Settings", Fax . 182 For details about how to set "Display" by configuring the appropriate User Parameter. • If the paper tray runs out of the machine are any network problems." If you can turn this , see "Parameter...
... the network, be sure to install a device certificate (PDF with digital signature), see "Parameter Settings", Fax . 182 For details about how to set "Display" by configuring the appropriate User Parameter. • If the paper tray runs out of the machine are any network problems." If you can turn this , see "Parameter...
User Guide
Page 192
...; Check that the Document Server can be sent but not stored afterward. 10. "Collate has been cancelled." Reduce the paper size of user information, see "Configuring Classification Codes", Print . If the message appears again, contact your service representative. "Classification Code is full. "Command Error" Causes Solutions Automatic registration of this size...
...; Check that the Document Server can be sent but not stored afterward. 10. "Collate has been cancelled." Reduce the paper size of user information, see "Configuring Classification Codes", Print . If the message appears again, contact your service representative. "Classification Code is full. "Command Error" Causes Solutions Automatic registration of this size...
User Guide
Page 198
...operation has been register programs or cancelled." The specified data is valid. Check the Configuration Page in the Document Server or reduce the number of errors may be printed on the Configuration Page. Job reset is automatically performed if the specified paper type is not correct. ..."You do not have a The logged in user is not supported. The maximum page capacity of pages per file." allowed to print the Configuration Page, see Security Guide . cancelled." change the paper tray settings. For details about how to use this function. For details about the ...
...operation has been register programs or cancelled." The specified data is valid. Check the Configuration Page in the Document Server or reduce the number of errors may be printed on the Configuration Page. Job reset is automatically performed if the specified paper type is not correct. ..."You do not have a The logged in user is not supported. The maximum page capacity of pages per file." allowed to print the Configuration Page, see Security Guide . cancelled." change the paper tray settings. For details about how to use this function. For details about the ...
User Guide
Page 200
... [Start this machine. • If you are using anti-virus software, add the program to your operating system's Help. Check the Scan Profile configuration. 198 Please check the settings." Set Scan Profile. The Scan Profile might be incorrectly configured. The [Take no action] setting has been selected on receipt of scan data.
... [Start this machine. • If you are using anti-virus software, add the program to your operating system's Help. Check the Scan Profile configuration. 198 Please check the settings." Set Scan Profile. The Scan Profile might be incorrectly configured. The [Take no action] setting has been selected on receipt of scan data.
Security Target
Page 6
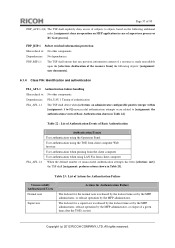
All rights reserved. Page 5 of 93 List of Figures Figure 1 : Example of TOE Environment ...9 Figure 2 : Hardware Configuration of the TOE 12 Figure 3 : Logical Scope of the TOE ...20 List of Tables Table 1 : Identification Information of TOE 7 Table 2 : Guidance for English Version-1 ...14 ... Dependency Analysis of TOE Security Functional Requirements 77 Table 34 : List of Audit Events...80 Table 35 : List of Audit Log Items ...81 Copyright (c) 2012 RICOH COMPANY, LTD.
All rights reserved. Page 5 of 93 List of Figures Figure 1 : Example of TOE Environment ...9 Figure 2 : Hardware Configuration of the TOE 12 Figure 3 : Logical Scope of the TOE ...20 List of Tables Table 1 : Identification Information of TOE 7 Table 2 : Guidance for English Version-1 ...14 ... Dependency Analysis of TOE Security Functional Requirements 77 Table 34 : List of Audit Events...80 Table 35 : List of Audit Log Items ...81 Copyright (c) 2012 RICOH COMPANY, LTD.
Security Target
Page 13
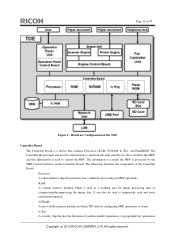
Page 12 of 93 Figure 2 : Hardware Configuration of the Controller Board: - The following describes the components of the TOE Controller Board The Controller Board ... and devices that contains Processors, RAM, NVRAM, Ic Key, and FlashROM. RAM A volatile memory medium which TSF data for configuring MFP operations is processed by the MFP Control Software on the Controller Board. Ic Key A security chip that performs basic arithmetic ... - Processor A semiconductor chip that has the functions of random number generation, cryptographic key generation Copyright (c) 2012 RICOH COMPANY, LTD.
Page 12 of 93 Figure 2 : Hardware Configuration of the Controller Board: - The following describes the components of the TOE Controller Board The Controller Board ... and devices that contains Processors, RAM, NVRAM, Ic Key, and FlashROM. RAM A volatile memory medium which TSF data for configuring MFP operations is processed by the MFP Control Software on the Controller Board. Ic Key A security chip that performs basic arithmetic ... - Processor A semiconductor chip that has the functions of random number generation, cryptographic key generation Copyright (c) 2012 RICOH COMPANY, LTD.
Security Target
Page 19
..., network management, and file management. An IT device connected to manage normal users. Authorised to networks. This privilege allows configuration of device settings and view of Users Normal user Explanation A user who is allowed to use Copy Function, Fax Function,...RC Gate A user who has all management privileges (Table 7). Authorised to manage networks and configure LAN settings. According to modify the login password of MFP Copyright (c) 2012 RICOH COMPANY, LTD. Up to multiple MFP administrators individually. Copy Function, Fax Function, Scanner Function...
..., network management, and file management. An IT device connected to manage normal users. Authorised to networks. This privilege allows configuration of device settings and view of Users Normal user Explanation A user who is allowed to use Copy Function, Fax Function,...RC Gate A user who has all management privileges (Table 7). Authorised to manage networks and configure LAN settings. According to modify the login password of MFP Copyright (c) 2012 RICOH COMPANY, LTD. Up to multiple MFP administrators individually. Copy Function, Fax Function, Scanner Function...
Security Target
Page 38
Copyright (c) 2012 RICOH COMPANY, LTD. A.ADMIN.TRUST Trusted administrator The responsible manager of MFP selects administrators who do not use their organisation, are aware of the security policies and procedures of 93 A.ADMIN.TRAINING Administrator training Administrators are competent to the guidance document. All rights reserved. Page 37 of their privileged access rights for malicious purposes according to correctly configure and operate the TOE in accordance with the guidance document following those policies and procedures.
Copyright (c) 2012 RICOH COMPANY, LTD. A.ADMIN.TRUST Trusted administrator The responsible manager of MFP selects administrators who do not use their organisation, are aware of the security policies and procedures of 93 A.ADMIN.TRAINING Administrator training Administrators are competent to the guidance document. All rights reserved. Page 37 of their privileged access rights for malicious purposes according to correctly configure and operate the TOE in accordance with the guidance document following those policies and procedures.
Security Target
Page 41
... and ensure that audit logs are reviewed at appropriate intervals according to the guidance document for malicious purposes according to the guidance document. and correctly configure and operate the TOE according to follow the guidance document; All rights reserved. OE.AUDIT.REVIEWED Log audit The responsible manager of MFP shall ensure... their organisation and have the training, competence, and time to follow those policies and procedures. have the competence to those policies and procedures. Copyright (c) 2012 RICOH COMPANY, LTD.
... and ensure that audit logs are reviewed at appropriate intervals according to the guidance document for malicious purposes according to the guidance document. and correctly configure and operate the TOE according to follow the guidance document; All rights reserved. OE.AUDIT.REVIEWED Log audit The responsible manager of MFP shall ensure... their organisation and have the training, competence, and time to follow those policies and procedures. have the competence to those policies and procedures. Copyright (c) 2012 RICOH COMPANY, LTD.
Security Target
Page 46
...policies and procedures. A.ADMIN.TRUST A.ADMIN.TRUST is upheld by this objective. A.ADMIN.TRUST is upheld by this objective. Copyright (c) 2012 RICOH COMPANY, LTD. A.USER.TRAINING A.USER.TRAINING is upheld by OE.ADMIN.TRUSTED. By OE.ADMIN.TRUSTED, the responsible manager of MFP ... to make them aware of the security policies and procedures of their organisation, and the users follow the guidance documents, and correctly configure and operate the TOE in accordance with those policies and procedures. A.ADMIN.TRAINING is upheld by OE.USER.TRAINED. All rights reserved...
...policies and procedures. A.ADMIN.TRUST A.ADMIN.TRUST is upheld by this objective. A.ADMIN.TRUST is upheld by this objective. Copyright (c) 2012 RICOH COMPANY, LTD. A.USER.TRAINING A.USER.TRAINING is upheld by OE.ADMIN.TRUSTED. By OE.ADMIN.TRUSTED, the responsible manager of MFP ... to make them aware of the security policies and procedures of their organisation, and the users follow the guidance documents, and correctly configure and operate the TOE in accordance with those policies and procedures. A.ADMIN.TRAINING is upheld by OE.USER.TRAINED. All rights reserved...
Security Target
Page 58
... the TOE's restart. Dependencies: FIA_UAU.1 Timing of authentication FIA_AFL.1.1 The TSF shall detect when [selection: an administrator configurable positive integer within [assignment: 1 to 5]] unsuccessful authentication attempts occur related to [assignment: the authentication events of Basic Authentication... shown in Table 23]. Copyright (c) 2012 RICOH COMPANY, LTD. FDP_RIP.1 Subset residual information protection Hierarchical to: No other components. FDP_RIP.1.1 The TSF shall ensure ...
... the TOE's restart. Dependencies: FIA_UAU.1 Timing of authentication FIA_AFL.1.1 The TSF shall detect when [selection: an administrator configurable positive integer within [assignment: 1 to 5]] unsuccessful authentication attempts occur related to [assignment: the authentication events of Basic Authentication... shown in Table 23]. Copyright (c) 2012 RICOH COMPANY, LTD. FDP_RIP.1 Subset residual information protection Hierarchical to: No other components. FDP_RIP.1.1 The TSF shall ensure ...