WGT624v3 Reference Manual
Page 9
Overview of WEP Parameters D-5 Key Size ...D-6 WEP Configuration Options D-7 Wireless Channels ...D-7 WPA and WPA2 Wireless Security D-8 How Does WPA Compare to WEP D-9 How Does WPA Compare to WPA2 (IEEE 802.11i D-10 What are the Key Features ...Data Encryption Key Management D-14 Is WPA/WPA2 Perfect D-16 Product Support for WPA/WPA2 D-16 Supporting a Mixture of WPA, WPA2, and WEP Wireless Clients is Discouraged D-16 Changes to Wireless Access Points D-17 Changes to Wireless Network Adapters D-17 Changes to Wireless Client Programs D-18 Glossary Contents ix 202-10090-01, April 2005
Overview of WEP Parameters D-5 Key Size ...D-6 WEP Configuration Options D-7 Wireless Channels ...D-7 WPA and WPA2 Wireless Security D-8 How Does WPA Compare to WEP D-9 How Does WPA Compare to WPA2 (IEEE 802.11i D-10 What are the Key Features ...Data Encryption Key Management D-14 Is WPA/WPA2 Perfect D-16 Product Support for WPA/WPA2 D-16 Supporting a Mixture of WPA, WPA2, and WEP Wireless Clients is Discouraged D-16 Changes to Wireless Access Points D-17 Changes to Wireless Network Adapters D-17 Changes to Wireless Client Programs D-18 Glossary Contents ix 202-10090-01, April 2005
WGT624v3 Reference Manual
Page 16
... network name (SSID) can connect. Reference Manual for the 108 Mbps Wireless Firewall Router WGT624 v3 • Flash memory for Wi-Fi Protected Access (WPA) data encryption which provides strong data encryption and authentication based on a pre-shared key. • Wireless access can be restricted by MAC address. • Wireless network name broadcast can be generated manually or by...
... network name (SSID) can connect. Reference Manual for the 108 Mbps Wireless Firewall Router WGT624 v3 • Flash memory for Wi-Fi Protected Access (WPA) data encryption which provides strong data encryption and authentication based on a pre-shared key. • Wireless access can be restricted by MAC address. • Wireless network name broadcast can be generated manually or by...
WGT624v3 Reference Manual
Page 33
... 108 Mbps Wireless Firewall Router WGT624 v3 Note: Failure to 32 alphanumeric characters. The same Name (SSID) must be used if they can operate in a region other than the region shown here. Auto 108 Mbps: All 802.11g, 802.11b and NETGEAR 108 Mbps wireless stations can be assigned to operate the router in 802.11b mode. - 108 Mbps only: Only compatible 802.11g wireless...
... 108 Mbps Wireless Firewall Router WGT624 v3 Note: Failure to 32 alphanumeric characters. The same Name (SSID) must be used if they can operate in a region other than the region shown here. Auto 108 Mbps: All 802.11g, 802.11b and NETGEAR 108 Mbps wireless stations can be assigned to operate the router in 802.11b mode. - 108 Mbps only: Only compatible 802.11g wireless...
WGT624v3 Reference Manual
Page 34
...8226; Security Encryption (WPA-PSK): Enter a word or group of 0-9, A-F). - These values must be identical on all PCs and Access Points in your network in the selected key box. The Passphrase must be 8 to automatically configure the WEP Key(s). If encryption strength is set... twenty-six hexadecimal digits (any combination of the four keys will automatically be used and enter the matching WEP key information for the 108 Mbps Wireless Firewall Router WGT624 v3 • Encryption Strength: Select the WEP Encryption level: 64-bit (sometimes called 40-bit) encryption 128-bit encryption ...
...8226; Security Encryption (WPA-PSK): Enter a word or group of 0-9, A-F). - These values must be identical on all PCs and Access Points in your network in the selected key box. The Passphrase must be 8 to automatically configure the WEP Key(s). If encryption strength is set... twenty-six hexadecimal digits (any combination of the four keys will automatically be used and enter the matching WEP key information for the 108 Mbps Wireless Firewall Router WGT624 v3 • Encryption Strength: Select the WEP Encryption level: 64-bit (sometimes called 40-bit) encryption 128-bit encryption ...
WGT624v3 Reference Manual
Page 117
... The WGT624 v3 wireless router conforms to the Institute of coverage, interacting with wireless nodes via a wired Ethernet backbone can freely roam from 11 Mbps to 5.5, 2, and 1 Mbps when the radio signal is weak or when interference is 11 Mbps, but it will automatically back down from one access point, it moves into wired Ethernet data, acting as...
... The WGT624 v3 wireless router conforms to the Institute of coverage, interacting with wireless nodes via a wired Ethernet backbone can freely roam from 11 Mbps to 5.5, 2, and 1 Mbps when the radio signal is weak or when interference is 11 Mbps, but it will automatically back down from one access point, it moves into wired Ethernet data, acting as...
WGT624v3 Reference Manual
Page 118
... this is used , but may still be configured with no structure or fixed points to set up a wireless network. As long as the stations are brought together as SSID. Reference Manual for the 108 Mbps Wireless Firewall Router WGT624 v3 Ad Hoc Mode (Peer-to-Peer Workgroup) In an ad hoc ... the IEEE 802.11 standard has defined these two types of Service Set Identification (SSID). For the wireless devices in the air from an access point. With Open System authentication, a wireless computer can join any network and receive any other , all devices must be referred to as needed;...
... this is used , but may still be configured with no structure or fixed points to set up a wireless network. As long as the stations are brought together as SSID. Reference Manual for the 108 Mbps Wireless Firewall Router WGT624 v3 Ad Hoc Mode (Peer-to-Peer Workgroup) In an ad hoc ... the IEEE 802.11 standard has defined these two types of Service Set Identification (SSID). For the wireless devices in the air from an access point. With Open System authentication, a wireless computer can join any network and receive any other , all devices must be referred to as needed;...
WGT624v3 Reference Manual
Page 119
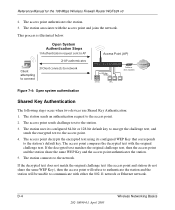
... join the network, assuming that the device SSID matches the access point SSID. Reference Manual for messages from an access point that has a matching SSID. 4. The station listens for the 108 Mbps Wireless Firewall Router WGT624 v3 • Shared Key. The station finds a message from any device to the access point. 7. With Shared Key authentication, only those PCs that possess the...
... join the network, assuming that the device SSID matches the access point SSID. Reference Manual for messages from an access point that has a matching SSID. 4. The station listens for the 108 Mbps Wireless Firewall Router WGT624 v3 • Shared Key. The station finds a message from any device to the access point. 7. With Shared Key authentication, only those PCs that possess the...
WGT624v3 Reference Manual
Page 120
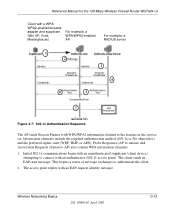
... DLS modem Figure 7-4: Open system authentication Shared Key Authentication The following steps occur when two devices use Shared Key Authentication: 1. Reference Manual for the 108 Mbps Wireless Firewall Router WGT624 v3 2. The access point authenticates the station. 3. Open System Authentication Steps 1) Authentication request sent to AP 2) AP authenticates Client attempting to connect 3) Client connects to the network...
... DLS modem Figure 7-4: Open system authentication Shared Key Authentication The following steps occur when two devices use Shared Key Authentication: 1. Reference Manual for the 108 Mbps Wireless Firewall Router WGT624 v3 2. The access point authenticates the station. 3. Open System Authentication Steps 1) Authentication request sent to AP 2) AP authenticates Client attempting to connect 3) Client connects to the network...
WGT624v3 Reference Manual
Page 121
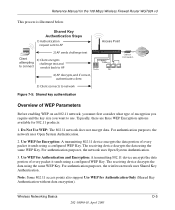
... WEP Key. Reference Manual for Authentication and Encryption: A transmitting 802.11 device encrypts the data portion of every packet it back to AP Access Point Cable/DSL ProSafeWirelessVPN Security Firewall PWR TEST IN TER N ET LNK W LA N LO CA L MODEL FVM318 100 ACT Enable LNK/ACT 1 2 3 4 5 6 7 8 Cable or DLS modem 4) AP decrypts, and... on an 802.11 network, you must first consider what type of every packet it sends using the same WEP Key. Use WEP for the 108 Mbps Wireless Firewall Router WGT624 v3 This process is illustrated below.
... WEP Key. Reference Manual for Authentication and Encryption: A transmitting 802.11 device encrypts the data portion of every packet it back to AP Access Point Cable/DSL ProSafeWirelessVPN Security Firewall PWR TEST IN TER N ET LNK W LA N LO CA L MODEL FVM318 100 ACT Enable LNK/ACT 1 2 3 4 5 6 7 8 Cable or DLS modem 4) AP decrypts, and... on an 802.11 network, you must first consider what type of every packet it sends using the same WEP Key. Use WEP for the 108 Mbps Wireless Firewall Router WGT624 v3 This process is illustrated below.
WGT624v3 Reference Manual
Page 122
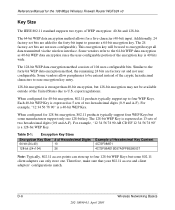
...for 128-bit encryption, 802.11 products typically support four WEP Keys but some manufacturers support only one . Reference Manual for the 108 Mbps Wireless Firewall Router WGT624 v3 Key Size The IEEE 802.11 standard supports two types of two hexadecimal digits (0-9 and A-F). The 24 factory-set ...expressed as 40-bit WEP data encryption since the user-configurable portion of Hexadecimal Key Content 4C72F08AE1 4C72F08AE19D57A3FF6B260037 Note: Typically, 802.11 access points can only store one 128-bit key. The 128-bit WEP Key is 40 bits wide. Additionally, 24 factory-set and ...
...for 128-bit encryption, 802.11 products typically support four WEP Keys but some manufacturers support only one . Reference Manual for the 108 Mbps Wireless Firewall Router WGT624 v3 Key Size The IEEE 802.11 standard supports two types of two hexadecimal digits (0-9 and A-F). The 24 factory-set ...expressed as 40-bit WEP data encryption since the user-configurable portion of Hexadecimal Key Content 4C72F08AE1 4C72F08AE19D57A3FF6B260037 Note: Typically, 802.11 access points can only store one 128-bit key. The 128-bit WEP Key is 40 bits wide. Additionally, 24 factory-set and ...
WGT624v3 Reference Manual
Page 123
...WEP key 3 as its default key to transmit while a client adapter can have the same WEP settings. Reference Manual for the 108 Mbps Wireless Firewall Router WGT624 v3 WEP Configuration Options The WEP settings must match on all of the 802.11 client adapters on the network must have... interfere with each other using neighboring channels (for the client adapter in the ISM (Industrial, Scientific, and Medical) band between access points, then all of the 802.11 access points and all 802.11 devices that are listed in Table D-2: Table D-2: 802.11b/g Radio Frequency Channels Channel 1 2 3...
...WEP key 3 as its default key to transmit while a client adapter can have the same WEP settings. Reference Manual for the 108 Mbps Wireless Firewall Router WGT624 v3 WEP Configuration Options The WEP settings must match on all of the 802.11 client adapters on the network must have... interfere with each other using neighboring channels (for the client adapter in the ISM (Industrial, Scientific, and Medical) band between access points, then all of the 802.11 access points and all 802.11 devices that are listed in Table D-2: Table D-2: 802.11b/g Radio Frequency Channels Channel 1 2 3...
WGT624v3 Reference Manual
Page 125
...NETGEAR is implemented using Temporal Key Integrity Protocol (TKIP) is required in 2004. WPA user authentication is implementing WPA and WPA2 on Wi-Fi Protected Access products. Support for 802.1x authentication is required. For WPA, encryption using 802.1x and the Extensible Authentication Protocol (EAP). With 802.11 WEP, all access points... method and is now performing interoperability certification testing on client and access point products. Reference Manual for the 108 Mbps Wireless Firewall Router WGT624 v3 WPA and WPA2 offer the following benefits: •...
...NETGEAR is implemented using Temporal Key Integrity Protocol (TKIP) is required in 2004. WPA user authentication is implementing WPA and WPA2 on Wi-Fi Protected Access products. Support for 802.1x authentication is required. For WPA, encryption using 802.1x and the Extensible Authentication Protocol (EAP). With 802.11 WEP, all access points... method and is now performing interoperability certification testing on client and access point products. Reference Manual for the 108 Mbps Wireless Firewall Router WGT624 v3 WPA and WPA2 offer the following benefits: •...
WGT624v3 Reference Manual
Page 126
...Manual for the 108 Mbps Wireless Firewall Router WGT624 v3 How Does WPA Compare to the network. Information in the WPA and WPA2 standard: • WPA and WPA2 Authentication • WPA and WPA2 Encryption Key Management - The RADIUS server holds (or has access to) user credentials...authenticates wireless users before they gain access to WPA2 (IEEE 802.11i)? What are discussed below. This occurs at the 802.11 level and is forward compatible with the WPA2 security specification. Temporal Key Integrity Protocol (TKIP) - This infrastructure includes stations, access points, and...
...Manual for the 108 Mbps Wireless Firewall Router WGT624 v3 How Does WPA Compare to the network. Information in the WPA and WPA2 standard: • WPA and WPA2 Authentication • WPA and WPA2 Encryption Key Management - The RADIUS server holds (or has access to) user credentials...authenticates wireless users before they gain access to WPA2 (IEEE 802.11i)? What are discussed below. This occurs at the 802.11 level and is forward compatible with the WPA2 security specification. Temporal Key Integrity Protocol (TKIP) - This infrastructure includes stations, access points, and...
WGT624v3 Reference Manual
Page 127
...must simply prove to the access point that it is required by WPA. 802.1X port access control prevents full access to wrap WEP in many home and small office environments will not be available nor desirable. Reference Manual for the 108 Mbps Wireless Firewall Router WGT624 v3 The primary ...those stations successfully authenticated. Wireless Networking Basics 202-10090-01, April 2005 D-11 Mutual authentication is gained by choosing an EAP type supporting this feature and is in order to access the network. • Key management. For example, if the access point is used for an...
...must simply prove to the access point that it is required by WPA. 802.1X port access control prevents full access to wrap WEP in many home and small office environments will not be available nor desirable. Reference Manual for the 108 Mbps Wireless Firewall Router WGT624 v3 The primary ...those stations successfully authenticated. Wireless Networking Basics 202-10090-01, April 2005 D-11 Mutual authentication is gained by choosing an EAP type supporting this feature and is in order to access the network. • Key management. For example, if the access point is used for an...
WGT624v3 Reference Manual
Page 128
... supports Extensible Authentication Protocol (EAP). Together, these technologies provide a framework for example. Windows XP implements 802.1x natively, and several NETGEAR switch and wireless access point products support 802.1x. Reference Manual for the 108 Mbps Wireless Firewall Router WGT624 v3 WPA/WPA2 Authentication: Enterprise-level User Authentication via EAP from a RADIUS server, for strong user authentication. It is...
... supports Extensible Authentication Protocol (EAP). Together, these technologies provide a framework for example. Windows XP implements 802.1x natively, and several NETGEAR switch and wireless access point products support 802.1x. Reference Manual for the 108 Mbps Wireless Firewall Router WGT624 v3 WPA/WPA2 Authentication: Enterprise-level User Authentication via EAP from a RADIUS server, for strong user authentication. It is...
WGT624v3 Reference Manual
Page 129
... Responses (AP to station) and Association Requests (station to authenticate the client. 2. Wireless Networking Basics 202-10090-01, April 2005 D-13 The access point replies with an authenticator (802.11 access point). Reference Manual for the 108 Mbps Wireless Firewall Router WGT624 v3 Client with a WPA/ WPA2-enabled wireless adapter and supplicant (Win XP, Funk, Meetinghouse) For example, a WPA/WPA2-enabled...
... Responses (AP to station) and Association Requests (station to authenticate the client. 2. Wireless Networking Basics 202-10090-01, April 2005 D-13 The access point replies with an authenticator (802.11 access point). Reference Manual for the 108 Mbps Wireless Firewall Router WGT624 v3 Client with a WPA/ WPA2-enabled wireless adapter and supplicant (Win XP, Funk, Meetinghouse) For example, a WPA/WPA2-enabled...
WGT624v3 Reference Manual
Page 130
... enough time to crack the key in current use of unicast encryption keys is synchronized between the wireless client and the wireless access point (AP). For the global encryption key, WPA includes a facility (the Information Element) for the 108 Mbps Wireless Firewall Router WGT624 v3 3. In typical 802.1x implementations, the client can update the EAP authentication type to...
... enough time to crack the key in current use of unicast encryption keys is synchronized between the wireless client and the wireless access point (AP). For the global encryption key, WPA includes a facility (the Information Element) for the 108 Mbps Wireless Firewall Router WGT624 v3 3. In typical 802.1x implementations, the client can update the EAP authentication type to...
WGT624v3 Reference Manual
Page 131
...is a pragmatic compromise that calculates an 8-byte message integrity check (MIC) using the calculation facilities available on existing wireless devices. Reference Manual for the 108 Mbps Wireless Firewall Router WGT624 v3 Temporal Key Integrity Protocol (TKIP) WPA uses TKIP to provide important data encryption enhancements including a per...initially for security conscience organizations, but the problem with WEP. A new frame counter in both the station and the access point. Wireless Networking Basics 202-10090-01, April 2005 D-15 AES Support for WPA2 One of the NIC's hardware in the...
...is a pragmatic compromise that calculates an 8-byte message integrity check (MIC) using the calculation facilities available on existing wireless devices. Reference Manual for the 108 Mbps Wireless Firewall Router WGT624 v3 Temporal Key Integrity Protocol (TKIP) WPA uses TKIP to provide important data encryption enhancements including a per...initially for security conscience organizations, but the problem with WEP. A new frame counter in both the station and the access point. Wireless Networking Basics 202-10090-01, April 2005 D-15 AES Support for WPA2 One of the NIC's hardware in the...
WGT624v3 Reference Manual
Page 132
... the access point receives two data packets that is no single security tactic is a definite step forward in August, 2003, NETGEAR, Inc. WPA/WPA2 is under an active attack, and as to WPA/WPA2, a wireless AP can support both WEP and WPA/WPA2 clients at the same time. Product Support for the 108 Mbps Wireless Firewall Router WGT624 v3...
... the access point receives two data packets that is no single security tactic is a definite step forward in August, 2003, NETGEAR, Inc. WPA/WPA2 is under an active attack, and as to WPA/WPA2, a wireless AP can support both WEP and WPA/WPA2 clients at the same time. Product Support for the 108 Mbps Wireless Firewall Router WGT624 v3...
WGT624v3 Reference Manual
Page 133
... support WPA/WPA2, obtain a WPA/WPA2 update from your wireless AP vendor and upload it to your wireless network adapter vendor and update the wireless network adapter driver. For wireless network adapter drivers that supports WPA. Reference Manual for the 108 Mbps Wireless Firewall Router WGT624 v3 Changes to Wireless Access Points Wireless access points must have their firmware updated to support the following : •...
... support WPA/WPA2, obtain a WPA/WPA2 update from your wireless AP vendor and upload it to your wireless network adapter vendor and update the wireless network adapter driver. For wireless network adapter drivers that supports WPA. Reference Manual for the 108 Mbps Wireless Firewall Router WGT624 v3 Changes to Wireless Access Points Wireless access points must have their firmware updated to support the following : •...