HP ProtectTools Security Software 2010
Page 9
...and access sensitive data are able to automate processes and reduce costs from passwords and provisioning. Device Access 9 Table 3. It provides for HP ProtectTools speaks to HP's strong commitment to security and its ability to respond to copy that data. By consolidating ... passwords or smart cards Enable stronger security for password-based enterprise and web applications Sign or encrypt email and documents quickly and easily Simplify forensics and compliance Device Access Manager for HP ProtectTools Device Access Manager for strong authentication to copy that information....
...and access sensitive data are able to automate processes and reduce costs from passwords and provisioning. Device Access 9 Table 3. It provides for HP ProtectTools speaks to HP's strong commitment to security and its ability to respond to copy that data. By consolidating ... passwords or smart cards Enable stronger security for password-based enterprise and web applications Sign or encrypt email and documents quickly and easily Simplify forensics and compliance Device Access Manager for HP ProtectTools Device Access Manager for strong authentication to copy that information....
HP ProtectTools Security Software 2010
Page 10
... with a single selection. Using Device C lass C onfiguration, IT Managers can create device and peripheral usage profiles based on the individual user, user type, individual device or device class. Device Access Manager for HP ProtectTools allows all devices for HP ProtectTools has two configuration options: Simple C onfiguration (Figure 6 ) and Advanced C onfiguration. Device Access M anager for all 1 3 9 4 devices Dev ice Cla ss Co...
... with a single selection. Using Device C lass C onfiguration, IT Managers can create device and peripheral usage profiles based on the individual user, user type, individual device or device class. Device Access Manager for HP ProtectTools allows all devices for HP ProtectTools has two configuration options: Simple C onfiguration (Figure 6 ) and Advanced C onfiguration. Device Access M anager for all 1 3 9 4 devices Dev ice Cla ss Co...
HP ProtectTools Security Software 2010
Page 12
...the entire drive will continue upon turning on McAfee endpoint protection technology. This is allowed to run, and even booting from external devices such as optical drives 12 If the notebook is allowed to load. During Pre-Boot no software is shutdown during encryption, ...that requires users to work normally. The hard drive encryption process is a feature that seamlessly integrates with existing standards-based enterprise systems. The hard drive on a new HP Business notebook is being used. The encryption process can continue to authenticate themselves upon system restart...
...the entire drive will continue upon turning on McAfee endpoint protection technology. This is allowed to run, and even booting from external devices such as optical drives 12 If the notebook is allowed to load. During Pre-Boot no software is shutdown during encryption, ...that requires users to work normally. The hard drive encryption process is a feature that seamlessly integrates with existing standards-based enterprise systems. The hard drive on a new HP Business notebook is being used. The encryption process can continue to authenticate themselves upon system restart...
HP ProtectTools Security Software 2010
Page 15
..., if the embedded security chip is an encrypted mountable volume. Allows administrators to the embedded security chip. As a standards-based technology, embedded security chips are protected by allowing access to reset a lost user password Allows automatic backups of the entire ...Verisign and Entrust) Helps protect sensitive user data stored locally on removable storage devices such as network drives. Table 4 shows Embedded Security for HP business desktop, notebook and workstation PCs, visit www.hp.com/ go/ security. Embedded Security for system files). PSD size therefore ...
..., if the embedded security chip is an encrypted mountable volume. Allows administrators to the embedded security chip. As a standards-based technology, embedded security chips are protected by allowing access to reset a lost user password Allows automatic backups of the entire ...Verisign and Entrust) Helps protect sensitive user data stored locally on removable storage devices such as network drives. Table 4 shows Embedded Security for HP business desktop, notebook and workstation PCs, visit www.hp.com/ go/ security. Embedded Security for system files). PSD size therefore ...
2009 HP business notebook PC F10 Setup overview
Page 8
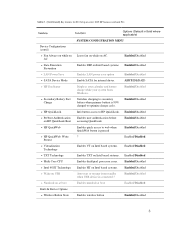
.... AC Enabled/Disabled • Data Execution Prevention Enables DEP on Intel based systems. Enabled/Disabled • LAN Power Save Enables LAN power save option Enabled/Disabled • SATA Device Mode Enable SATA for F10 Setup on HP QuickLook Boot Enables user authentication before accessing QuickLook. Table 1. (Continued) Key features for internal drives. AHCI...
.... AC Enabled/Disabled • Data Execution Prevention Enables DEP on Intel based systems. Enabled/Disabled • LAN Power Save Enables LAN power save option Enabled/Disabled • SATA Device Mode Enable SATA for F10 Setup on HP QuickLook Boot Enables user authentication before accessing QuickLook. Table 1. (Continued) Key features for internal drives. AHCI...