User Guide
Page 1
Description how to -gateway VPN using pre-shared secrets Typical client-to configure the NCP Secure Entry Client for authentication. D-Link NetDefend VPN Client (DS-601/605) A quick installation guide to setting up the D-Link NetDefend VPN Client in a VPNC scenario These scenarios were developed by : NCP Engineering GmbH Dombuehler Strasse 2, 90449 Nürnberg, Germany Phone: +49-911-99.68.0 Fax: +49-911-99.68.299 Client-to-Gateway using a preshared secret for Windows. Document version 1.00 Using D-Link NetDefend Client v1.0 Prepared by the VPN Consortium Scenario 1.
Description how to -gateway VPN using pre-shared secrets Typical client-to configure the NCP Secure Entry Client for authentication. D-Link NetDefend VPN Client (DS-601/605) A quick installation guide to setting up the D-Link NetDefend VPN Client in a VPNC scenario These scenarios were developed by : NCP Engineering GmbH Dombuehler Strasse 2, 90449 Nürnberg, Germany Phone: +49-911-99.68.0 Fax: +49-911-99.68.299 Client-to-Gateway using a preshared secret for Windows. Document version 1.00 Using D-Link NetDefend Client v1.0 Prepared by the VPN Consortium Scenario 1.
User Guide
Page 2
... quick guide, and explicitly disclaims all expressed or implied warranties of NCP engineering GmbH, Dombühler Str.2, D-90449 Nürnberg, Germany. Disclaimer Considerable care has been taken in the preparation of such revisions and changes. NCP makes no representations or warranties with respect to notify any time, without obligation to the contents or use of this manual...
... quick guide, and explicitly disclaims all expressed or implied warranties of NCP engineering GmbH, Dombühler Str.2, D-90449 Nürnberg, Germany. Disclaimer Considerable care has been taken in the preparation of such revisions and changes. NCP makes no representations or warranties with respect to notify any time, without obligation to the contents or use of this manual...
User Guide
Page 3
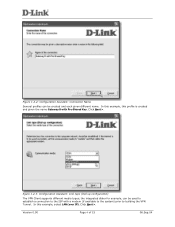
... 1: Client-to the Internet. Gateway B connects the internal LAN 172.23.9.0/24 to -gateway with no kbytes rekeying The IKE Phase 2 parameters used for testing IPsec but is a typical client-to-gateway VPN that uses a preshared secret for all IP protocols, all ports, between the client and 172.23.9.0/24, using IPv4 subnets 1.2 Using the Configuration Assistant Figure 1.2.1: Configuration Assistant The first time you start up the D-Link VPN Client...
... 1: Client-to the Internet. Gateway B connects the internal LAN 172.23.9.0/24 to -gateway with no kbytes rekeying The IKE Phase 2 parameters used for testing IPsec but is a typical client-to-gateway VPN that uses a preshared secret for all IP protocols, all ports, between the client and 172.23.9.0/24, using IPv4 subnets 1.2 Using the Configuration Assistant Figure 1.2.1: Configuration Assistant The first time you start up the D-Link VPN Client...
User Guide
Page 4
... VPN Tunnel. Version 0.90 Page 4 of 15 06.Sep.04 Click Next >. Click Next >. In this profile is created and given the name Gateway B with a modem (if available to the system) prior to the ISP with Pre-Shared Key. Figure 1.2.2: Configuration Assistant: Connection Name Several profiles can be created and each given different name. figure 1.2.3: Configuration Assistant: Link type (Dial up configuration) The VPN Client supports different media types...
... VPN Tunnel. Version 0.90 Page 4 of 15 06.Sep.04 Click Next >. Click Next >. In this profile is created and given the name Gateway B with a modem (if available to the system) prior to the ISP with Pre-Shared Key. Figure 1.2.2: Configuration Assistant: Connection Name Several profiles can be created and each given different name. figure 1.2.3: Configuration Assistant: Link type (Dial up configuration) The VPN Client supports different media types...
User Guide
Page 5
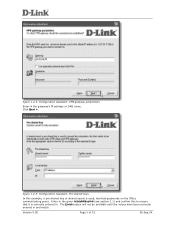
Click Next >. Enter in the given hr5xb84l6aa9r6 (see section 1.1) and confirm this example, a pre-shared key or shared secret is correctly entered in the gateway's IP address or DNS name. Version 0.90 Page 5 of 15 06.Sep.04 figure 1.2.4: Configuration Assistant: VPN gateway parameters Enter in . The Finish button will not be available until the values have been correctly entered in and match. figure 1.2.5: Configuration Assistant: Pre-shared keys In this to ensure that it is used, identical passwords on the IPSec communicating peers.
Click Next >. Enter in the given hr5xb84l6aa9r6 (see section 1.1) and confirm this example, a pre-shared key or shared secret is correctly entered in the gateway's IP address or DNS name. Version 0.90 Page 5 of 15 06.Sep.04 figure 1.2.4: Configuration Assistant: VPN gateway parameters Enter in . The Finish button will not be available until the values have been correctly entered in and match. figure 1.2.5: Configuration Assistant: Pre-shared keys In this to ensure that it is used, identical passwords on the IPSec communicating peers.
User Guide
Page 6
1.3 Checking/Modifying the Configuration figure 1.3.1: Configuration -> Profile Settings Open the Profile Settings to modify the parameters to be modified, or select the profile and then click on the profile that is going to define the specific IKE and IPSec proposals as specified in section 1.1. figure 1.3.2: Profile Settings Either double click on Configure. Version 0.90 Page 6 of 15 06.Sep.04
1.3 Checking/Modifying the Configuration figure 1.3.1: Configuration -> Profile Settings Open the Profile Settings to modify the parameters to be modified, or select the profile and then click on the profile that is going to define the specific IKE and IPSec proposals as specified in section 1.1. figure 1.3.2: Profile Settings Either double click on Configure. Version 0.90 Page 6 of 15 06.Sep.04
User Guide
Page 7
... 15 06.Sep.04 Version 0.90 Page 7 of different commonly used proposals and the VPN Gateway can then select one to use for the connection. However, in this example, (although automatic mode works) both the IKE (Phase 1) and IPSec (Phase 2) Policies, the client will be manually defined in accordance to continue... so select Policy lifetimes... Select IPSec General Settings to section 1.1; figure 1.3.3: Profile Settings: General Review the parameters and ensure...
... 15 06.Sep.04 Version 0.90 Page 7 of different commonly used proposals and the VPN Gateway can then select one to use for the connection. However, in this example, (although automatic mode works) both the IKE (Phase 1) and IPSec (Phase 2) Policies, the client will be manually defined in accordance to continue... so select Policy lifetimes... Select IPSec General Settings to section 1.1; figure 1.3.3: Profile Settings: General Review the parameters and ensure...
User Guide
Page 8
to define specific proposals to 1 hour (3600 seconds). figure 1.3.5: Policy Lifetimes The duration for the IKE Policy (SA lifetime) has been set to 8 hours (28800 seconds), and the IPSec Policy (SA) lifetime is limited to be used in this connection as lined out in section 1.1. figure 1.3.6: Profile Settings: IPSec General Settings: Policy Editor Select the Policy Editor... Click OK to return to define the Proposals... Version 0.90 Page 8 of 15 06.Sep.04
to define specific proposals to 1 hour (3600 seconds). figure 1.3.5: Policy Lifetimes The duration for the IKE Policy (SA lifetime) has been set to 8 hours (28800 seconds), and the IPSec Policy (SA) lifetime is limited to be used in this connection as lined out in section 1.1. figure 1.3.6: Profile Settings: IPSec General Settings: Policy Editor Select the Policy Editor... Click OK to return to define the Proposals... Version 0.90 Page 8 of 15 06.Sep.04
User Guide
Page 9
... previous dialog box. Version 0.90 Page 9 of this proposal. figure 1.3.8: Defining an IKE Policy Simply select the parameters for the purpose of 15 06.Sep.04 figure 1.3.7: Proposal Definitions: IKE Policy First select IKE Policy and click on New Entry to define a new IKE Policy (Phase 1 parameters) to be used , SHA (160bit SHA-1) for the authentication algorithm, and finally DH-Group 2 (1024 Bit...
... previous dialog box. Version 0.90 Page 9 of this proposal. figure 1.3.8: Defining an IKE Policy Simply select the parameters for the purpose of 15 06.Sep.04 figure 1.3.7: Proposal Definitions: IKE Policy First select IKE Policy and click on New Entry to define a new IKE Policy (Phase 1 parameters) to be used , SHA (160bit SHA-1) for the authentication algorithm, and finally DH-Group 2 (1024 Bit...
User Guide
Page 10
Click OK to define the IPSec proposal (Phase 2 parameters). figure 1.3.9: Proposal Definitions: IPSec Policy In the same way, select IPSec Policy and click on New Entry to continue... figure 1.3.10: Defining an IPSec Policy Simply select the parameters for this policy: ESP tunnel mode, Triple DES (168bit 3DES-CBC) for encryption algorithm and SHA (SHA-1 160 Bit) for the authentication code/hash algorithm. Version 0.90 Page 10 of 15 06.Sep.04
Click OK to define the IPSec proposal (Phase 2 parameters). figure 1.3.9: Proposal Definitions: IPSec Policy In the same way, select IPSec Policy and click on New Entry to continue... figure 1.3.10: Defining an IPSec Policy Simply select the parameters for this policy: ESP tunnel mode, Triple DES (168bit 3DES-CBC) for encryption algorithm and SHA (SHA-1 160 Bit) for the authentication code/hash algorithm. Version 0.90 Page 10 of 15 06.Sep.04
User Guide
Page 11
figure 1.3.11: IPSec/IKE (ISAKMP) parameters defined Click on Identities to move to the Profile Settings | IPSec General Settings dialog box. Version 0.90 Page 11 of 15 06.Sep.04 figure 1.3.12: Profile Settings: IPSec General Settings Select the newly defined IKE- (ISAKMP) and IPSec Policies, and click on Close to save the proposals created, and return to the next dialog box.
figure 1.3.11: IPSec/IKE (ISAKMP) parameters defined Click on Identities to move to the Profile Settings | IPSec General Settings dialog box. Version 0.90 Page 11 of 15 06.Sep.04 figure 1.3.12: Profile Settings: IPSec General Settings Select the newly defined IKE- (ISAKMP) and IPSec Policies, and click on Close to save the proposals created, and return to the next dialog box.
User Guide
Page 12
... the next dialog box. figure 1.3.13: Profile Settings: Identities In this scenario, the Gateway will not know what the IP Address is left blank. Other IKE-ID types can be used, but are beyond the scope of 15 06.Sep.04 Version 0.90 Page 12 of this document; Click on Remote Networks to move to the manual for more details.
... the next dialog box. figure 1.3.13: Profile Settings: Identities In this scenario, the Gateway will not know what the IP Address is left blank. Other IKE-ID types can be used, but are beyond the scope of 15 06.Sep.04 Version 0.90 Page 12 of this document; Click on Remote Networks to move to the manual for more details.
User Guide
Page 13
... subnet masks defined, these can be defined here. Version 0.90 Page 13 of 15 06.Sep.04 Select the Firewall Settings to be individual hosts or network segments) that can be reached. In this scenario, Gateway B's LAN segment, 172.23.9.0/24 (or netmask 255.255.255.0) is used in the Network address(es) (depending on OK to return to...
... subnet masks defined, these can be defined here. Version 0.90 Page 13 of 15 06.Sep.04 Select the Firewall Settings to be individual hosts or network segments) that can be reached. In this scenario, Gateway B's LAN segment, 172.23.9.0/24 (or netmask 255.255.255.0) is used in the Network address(es) (depending on OK to return to...
User Guide
Page 14
figure 1.3.17: Profile Settings Select OK to return to the monitor (the graphical user interface of the VPN Client) Version 0.90 Page 14 of 15 06.Sep.04
figure 1.3.17: Profile Settings Select OK to return to the monitor (the graphical user interface of the VPN Client) Version 0.90 Page 14 of 15 06.Sep.04
User Guide
Page 15
figure 1.4.2: Command Prompt: Ping response Version 0.90 Page 15 of the VPN Gateway to confirm the connection has been successfully established. 1.4 Establishing the connection figure 1.4.1: D-Link VPN Client Monitor Seeing as the connection is set to be reached. Depending on the VPN Gateway's configuration other hosts on the Gateway B's internal LAN can be established manually, click on Connect to create the tunnel. Then open a dos box, and ping the internal network interface of 15 06.Sep.04
figure 1.4.2: Command Prompt: Ping response Version 0.90 Page 15 of the VPN Gateway to confirm the connection has been successfully established. 1.4 Establishing the connection figure 1.4.1: D-Link VPN Client Monitor Seeing as the connection is set to be reached. Depending on the VPN Gateway's configuration other hosts on the Gateway B's internal LAN can be established manually, click on Connect to create the tunnel. Then open a dos box, and ping the internal network interface of 15 06.Sep.04