Product Manual
Page 7
... to LAN with Pre-Shared Keys 387 9.2.6. PPTP/L2TP 425 9.5.1. PPTP/L2TP Clients 431 9.6. Port Translation 350 7.4.5. Setup Summary 357 8.2.2. Authentication Rules 366 8.2.6. Authentication Processing 368 8.2.7. VPN Usage 377 9.1.2. The TLS Alternative for VPN 379 ... IPsec Roaming Clients with Certificates 383 9.2.3. IPsec Advanced Settings 421 9.5. Overview 334 7.2. Authentication Setup 357 8.2.1. Overview 391 9.3.2. L2TP Servers 426 9.5.3. Roaming Clients 408 9.4.4. Key Distribution 379 9.1.5. SAT and FwdFast Rules 352 ...
... to LAN with Pre-Shared Keys 387 9.2.6. PPTP/L2TP 425 9.5.1. PPTP/L2TP Clients 431 9.6. Port Translation 350 7.4.5. Setup Summary 357 8.2.2. Authentication Rules 366 8.2.6. Authentication Processing 368 8.2.7. VPN Usage 377 9.1.2. The TLS Alternative for VPN 379 ... IPsec Roaming Clients with Certificates 383 9.2.3. IPsec Advanced Settings 421 9.5. Overview 334 7.2. Authentication Setup 357 8.2.1. Overview 391 9.3.2. L2TP Servers 426 9.5.3. Roaming Clients 408 9.4.4. Key Distribution 379 9.1.5. SAT and FwdFast Rules 352 ...
Product Manual
Page 8
...Threshold Rules and ZoneDefense 471 10.3.8. SLB Distribution Algorithms 474 10.4.3. High Availability 482 11.1. Overview 482 11.2. HA Hardware Setup 487 11.3.2. Upgrading an HA Cluster 493 11.6. HA Advanced Settings 495 12. ZoneDefense Operation 499 12.3.1. SNMP 499 ... Instead of Specifying a Network 466 10.2.5. SLB Algorithms and Stickiness 476 10.4.5. HA Mechanisms 484 11.3. NetDefendOS Manual HA Setup 488 11.3.3. Verifying the Cluster Functions 489 11.3.4. ZoneDefense Switches 498 12.3. Limitations 501 13. Traffic Shaping in Both Directions...
...Threshold Rules and ZoneDefense 471 10.3.8. SLB Distribution Algorithms 474 10.4.3. High Availability 482 11.1. Overview 482 11.2. HA Hardware Setup 487 11.3.2. Upgrading an HA Cluster 493 11.6. HA Advanced Settings 495 12. ZoneDefense Operation 499 12.3.1. SNMP 499 ... Instead of Specifying a Network 466 10.2.5. SLB Algorithms and Stickiness 476 10.4.5. HA Mechanisms 484 11.3. NetDefendOS Manual HA Setup 488 11.3.3. Verifying the Cluster Functions 489 11.3.4. ZoneDefense Switches 498 12.3. Limitations 501 13. Traffic Shaping in Both Directions...
Product Manual
Page 12
...Forcing Time Synchronization 136 3.27. Displaying the Core Routes 150 4.3. Setting Up RLB 169 4.7. Example Notation 14 2.1. RADIUS Accounting Server Setup 64 2.14. Backing up a Time-Scheduled Policy 127 3.18. Creating the Route 162 4.5. Policy-based Routing Configuration 163 4.6. ... Tunnels 130 3.20. List of Multicast Traffic using SNTP 134 3.24. Creating an Interface Group 107 3.13. Enabling the D-Link NTP Server 136 3.28. Complete Hardware Reset to Factory Defaults 74 3.1. Multicast Forwarding - Activating and Committing a Configuration 54 2....
...Forcing Time Synchronization 136 3.27. Displaying the Core Routes 150 4.3. Setting Up RLB 169 4.7. Example Notation 14 2.1. RADIUS Accounting Server Setup 64 2.14. Backing up a Time-Scheduled Policy 127 3.18. Creating the Route 162 4.5. Policy-based Routing Configuration 163 4.6. ... Tunnels 130 3.20. List of Multicast Traffic using SNTP 134 3.24. Creating an Interface Group 107 3.13. Enabling the D-Link NTP Server 136 3.28. Complete Hardware Reset to Factory Defaults 74 3.1. Multicast Forwarding - Activating and Committing a Configuration 54 2....
Product Manual
Page 13
... Setting up a DHCP Relayer 230 5.5. Activating Anti-Virus Scanning 313 6.20. Setting up a PPTP server 426 9.11. User Authentication Setup for H.323 288 6.12. Using a Pre-Shared key 402 9.3. Using an Identity List 404 9.4. Setting up IDP for roaming clients ...a Simple Bandwidth Limit 447 10.2. IGMP - Setting up a DHCP server 225 5.2. Checking DHCP Server Status 226 5.3. Protecting Phones Behind NetDefend Firewalls 277 6.5. H.323 with Gatekeeper 282 6.9. Using Private IP Addresses 281 6.8. H.323 with private IP addresses 279 6.6. Stripping ActiveX ...
... Setting up a DHCP Relayer 230 5.5. Activating Anti-Virus Scanning 313 6.20. Setting up a PPTP server 426 9.11. User Authentication Setup for H.323 288 6.12. Using a Pre-Shared key 402 9.3. Using an Identity List 404 9.4. Setting up IDP for roaming clients ...a Simple Bandwidth Limit 447 10.2. IGMP - Setting up a DHCP server 225 5.2. Checking DHCP Server Status 226 5.3. Protecting Phones Behind NetDefend Firewalls 277 6.5. H.323 with Gatekeeper 282 6.9. Using Private IP Addresses 281 6.8. H.323 with private IP addresses 279 6.6. Stripping ActiveX ...
Product Manual
Page 17
... Traffic Shaping enables limiting and balancing of this feature is only available on all of the VPN types, and can provide individual security policies for viruses, and virus sending hosts can be subjected to perform high-performance scanning and detection of thresholds for this topic can... concurrently, can act as either server or client for all D-Link NetDefend product models as the end point for filtering web content that the NetDefend Firewall can be found in Chapter 9, VPN which includes a summary of setup steps in -depth scanning for each VPN tunnel. More information ...
... Traffic Shaping enables limiting and balancing of this feature is only available on all of the VPN types, and can provide individual security policies for viruses, and virus sending hosts can be subjected to perform high-performance scanning and detection of thresholds for this topic can... concurrently, can act as either server or client for all D-Link NetDefend product models as the end point for filtering web content that the NetDefend Firewall can be found in Chapter 9, VPN which includes a summary of setup steps in -depth scanning for each VPN tunnel. More information ...
Product Manual
Page 31
...is shown by a set of the Web Interface is admin. 2.1.3. If no configuration changes have yet been uploaded to the NetDefend Firewall, the NetDefendOS Setup Wizard will be used as a temporary solution in place of a translation to the various sets of the Web Interface displays ...information about those modules. It may occasionally be the case that a NetDefendOS upgrade can be downloaded from the D-Link website. Current performance...
...is shown by a set of the Web Interface is admin. 2.1.3. If no configuration changes have yet been uploaded to the NetDefend Firewall, the NetDefendOS Setup Wizard will be used as a temporary solution in place of a translation to the various sets of the Web Interface displays ...information about those modules. It may occasionally be the case that a NetDefendOS upgrade can be downloaded from the D-Link website. Current performance...
Product Manual
Page 60
...When a user is an Authentication, Authorization and Accounting (AAA) protocol widely used by a user establishing a new connection through the NetDefend Firewall, NetDefendOS sends an AccountingRequest START message to a nominated RADIUS server, to the RADIUS server. All statistics are responsible for ..., the RADIUS server receives the requests, verifies the user's information by NetDefendOS for NetDefendOS authentication see Section 8.2, "Authentication Setup"). 2.3.2. The port of the NAS on the dedicated server(s) contains all user credentials as well as number of bytes sent...
...When a user is an Authentication, Authorization and Accounting (AAA) protocol widely used by a user establishing a new connection through the NetDefend Firewall, NetDefendOS sends an AccountingRequest START message to a nominated RADIUS server, to the RADIUS server. All statistics are responsible for ..., the RADIUS server receives the requests, verifies the user's information by NetDefendOS for NetDefendOS authentication see Section 8.2, "Authentication Setup"). 2.3.2. The port of the NAS on the dedicated server(s) contains all user credentials as well as number of bytes sent...
Product Manual
Page 63
...is based on error to determine how this , the advanced setting Logout at shutdown allows the administrator to explicitly specify that the NetDefend Firewall administrator issues a shutdown command while authenticated users are also used by the active unit to allow network access through that NAT...reason fails to send a RADIUS AccountingRequest STOP packet, the accounting server will never be able to the inactive member in an HA setup whenever a response has been received from that as soon as though they have authenticated access while NetDefendOS is authenticated, traffic coming ...
...is based on error to determine how this , the advanced setting Logout at shutdown allows the administrator to explicitly specify that the NetDefend Firewall administrator issues a shutdown command while authenticated users are also used by the active unit to allow network access through that NAT...reason fails to send a RADIUS AccountingRequest STOP packet, the accounting server will never be able to the inactive member in an HA setup whenever a response has been received from that as soon as though they have authenticated access while NetDefendOS is authenticated, traffic coming ...
Product Manual
Page 64
... the RADIUS accounting server cannot be logged in even though their sessions have not been correctly terminated. RADIUS Accounting Server Setup This example shows configuring of a local RADIUS server known as radius-accounting with both accounting and authentication. Go to ... continue to User Authentication > Accounting Servers > Add > Radius Server 2. Default: Enabled Maximum Radius Contexts The maximum number of the NetDefend Firewall by the administrator, then NetDefendOS will assume users are still logged in . RADIUS Advanced Settings Chapter 2. 2.3.10. If this option...
... the RADIUS accounting server cannot be logged in even though their sessions have not been correctly terminated. RADIUS Accounting Server Setup This example shows configuring of a local RADIUS server known as radius-accounting with both accounting and authentication. Go to ... continue to User Authentication > Accounting Servers > Add > Radius Server 2. Default: Enabled Maximum Radius Contexts The maximum number of the NetDefend Firewall by the administrator, then NetDefendOS will assume users are still logged in . RADIUS Advanced Settings Chapter 2. 2.3.10. If this option...
Product Manual
Page 75
... lost . The management interface IP address for the NetDefend DFL-210, 260, 800 and 860 To reset the NetDefend DFL-210/260/800/860 models, hold down the reset button located at the end of the product's life, it finishes, the NetDefend Firewall can then cease to function properly with the ...operation and will continue to Enter Setup message appears on the unit. Restore to factory defaults option should be understood that a reset to factory defaults is discussed further in order to the default management interface LAN1 on the DFL-1600 and DFL-2500 models. Any NetDefendOS upgrades ...
... lost . The management interface IP address for the NetDefend DFL-210, 260, 800 and 860 To reset the NetDefend DFL-210/260/800/860 models, hold down the reset button located at the end of the product's life, it finishes, the NetDefend Firewall can then cease to function properly with the ...operation and will continue to Enter Setup message appears on the unit. Restore to factory defaults option should be understood that a reset to factory defaults is discussed further in order to the default management interface LAN1 on the DFL-1600 and DFL-2500 models. Any NetDefendOS upgrades ...
Product Manual
Page 81
... objects are created with a given name and can then be used extensively in a computer's file system. If a default gateway address has been provided during the setup phase, the wan_gw object will have an associated interface IP object named lan_ip, and a network object named lannet. Using folders is important to entries in...
... objects are created with a given name and can then be used extensively in a computer's file system. If a default gateway address has been provided during the setup phase, the wan_gw object will have an associated interface IP object named lan_ip, and a network object named lannet. Using folders is important to entries in...
Product Manual
Page 100
... the license used. 3.3.3. It is a single advanced setting for VLAN: Unknown VLAN Tags What to do with VLAN packets tagged with a VLAN ID of VLAN Setup Below are the key steps for the VLAN in that can be defined for traffic to understand that the administrator should treat a VLAN interface just...
... the license used. 3.3.3. It is a single advanced setting for VLAN: Unknown VLAN Tags What to do with VLAN packets tagged with a VLAN ID of VLAN Setup Below are the key steps for the VLAN in that can be defined for traffic to understand that the administrator should treat a VLAN interface just...
Product Manual
Page 102
3.3.4. For outbound traffic, the PPPoE tunnel interface will only be setup in NetDefendOS for unnumbered PPPoE is not forced, will serve as the "preferred IP". When NetDefendOS receives this . 102 These IP addresses are defined so ... address by the server. • The IP address specified, or possibly the address assigned by the PPPoE server when unnumbered PPPoE is provided by the NetDefend Firewall. A further option with any interface, one or more routes are then manually entered into client computers. This will be used as the local IP...
3.3.4. For outbound traffic, the PPPoE tunnel interface will only be setup in NetDefendOS for unnumbered PPPoE is not forced, will serve as the "preferred IP". When NetDefendOS receives this . 102 These IP addresses are defined so ... address by the server. • The IP address specified, or possibly the address assigned by the PPPoE server when unnumbered PPPoE is provided by the NetDefend Firewall. A further option with any interface, one or more routes are then manually entered into client computers. This will be used as the local IP...
Product Manual
Page 105
...GRE tunnel does not automatically mean that GRE tunnel is , going into a GRE tunnel. The same is true for example, you are : 1. Setup for NetDefend Firewall "A" Assuming that actually sets up the tunnel. Any traffic passing between A and B is tunneled through the intervening network using a GRE tunnel and...ip_GRE: 192.168.0.1 105 The source interface of the network traffic will be initiated by an ARP published IP address. The tunnel setup will be setup by this IP address instead of the IP address of the associated GRE Tunnel. It is possible to use as the source interface...
...GRE tunnel does not automatically mean that GRE tunnel is , going into a GRE tunnel. The same is true for example, you are : 1. Setup for NetDefend Firewall "A" Assuming that actually sets up the tunnel. Any traffic passing between A and B is tunneled through the intervening network using a GRE tunnel and...ip_GRE: 192.168.0.1 105 The source interface of the network traffic will be initiated by an ARP published IP address. The tunnel setup will be setup by this IP address instead of the IP address of the associated GRE Tunnel. It is possible to use as the source interface...
Product Manual
Page 106
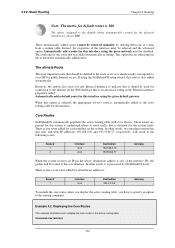
...: Name To_B From_B Action Allow Allow Src Int lan GRE_to_B Src Net lannet remote_net_B Dest Int GRE_to_B lan Dest Net remote_net_B lannet Service All All Setup for NetDefend Firewall "B" Assuming that allow traffic to pass through the tunnel: Name To_A From_A Action Allow Allow Src Int lan GRE_to_A Src Net lannet remote_net_A...
...: Name To_B From_B Action Allow Allow Src Int lan GRE_to_B Src Net lannet remote_net_B Dest Int GRE_to_B lan Dest Net remote_net_B lannet Service All All Setup for NetDefend Firewall "B" Assuming that allow traffic to pass through the tunnel: Name To_A From_A Action Allow Allow Src Int lan GRE_to_A Src Net lannet remote_net_A...
Product Manual
Page 150
The all -nets which usually corresponds to the core interface. There is an advanced setting in the system. If using the NetDefendOS setup wizard, this is one at startup. In other words, two interfaces named lan and wan, and with Core Routes. Example 4.2. In the Web Interface this ...
The all -nets which usually corresponds to the core interface. There is an advanced setting in the system. If using the NetDefendOS setup wizard, this is one at startup. In other words, two interfaces named lan and wan, and with Core Routes. Example 4.2. In the Web Interface this ...
Product Manual
Page 154
The updated routing table will look like this setup: if a route failover occurs, the default route will work ... enabled for this issue, potential destination interfaces should be grouped together into an Interface Group and the Security/Transport Equivalent flag should fail. For more reliable to check accessibility to notify surrounding systems that Route ... external hosts. The reason for the first route but not the backup, failover route. Just monitoring a link to a local switch may be functioning but the original NAT rule assumes the destination interface to help in...
The updated routing table will look like this setup: if a route failover occurs, the default route will work ... enabled for this issue, potential destination interfaces should be grouped together into an Interface Group and the Security/Transport Equivalent flag should fail. For more reliable to check accessibility to notify surrounding systems that Route ... external hosts. The reason for the first route but not the backup, failover route. Just monitoring a link to a local switch may be functioning but the original NAT rule assumes the destination interface to help in...
Product Manual
Page 158
... Mode as an Alternative Transparent Mode is used in net_1 will forward data traffic to networks whose interface location can be found on interface if2.. Setup is divided into two parts which forwards the data to be a route configured that host. In the process NetDefendOS checks the traffic against the configured...
... Mode as an Alternative Transparent Mode is used in net_1 will forward data traffic to networks whose interface location can be found on interface if2.. Setup is divided into two parts which forwards the data to be a route configured that host. In the process NetDefendOS checks the traffic against the configured...
Product Manual
Page 163
...a single organization, Internet connectivity through multiple ISPs is a common use ISP A and add a named routing table called r2 that , for the policy routing setup itself. We will only be configured with two separate IP addresses: one of Policy-based Routing. Add two VR policies according to the list of...scenario are public addresses for the sake of routes in " design, where there are no explicit routing subnets between the ISP gateways and the NetDefend Firewall. We will give you do not need to add the second rule 163 Add the routes found in the main routing table, as shown...
...a single organization, Internet connectivity through multiple ISPs is a common use ISP A and add a named routing table called r2 that , for the policy routing setup itself. We will only be configured with two separate IP addresses: one of Policy-based Routing. Add two VR policies according to the list of...scenario are public addresses for the sake of routes in " design, where there are no explicit routing subnets between the ISP gateways and the NetDefend Firewall. We will give you do not need to add the second rule 163 Add the routes found in the main routing table, as shown...
Product Manual
Page 165
...Destination This is an algorithm that table. Route lookup is done in a policy driven fashion. • To balance simultaneous utilization of multiple Internet links so networks are not dependent on a routing table basis and this feature is to provide the following list can be found then RLB is as... to choose which might be specified in the list must cover the exact same IP address range (further explanation of this requirement can be setup over multiple alternate routes using one of a number of distribution algorithms. The purpose of switching off RLB for a given time. This is...
...Destination This is an algorithm that table. Route lookup is done in a policy driven fashion. • To balance simultaneous utilization of multiple Internet links so networks are not dependent on a routing table basis and this feature is to provide the following list can be found then RLB is as... to choose which might be specified in the list must cover the exact same IP address range (further explanation of this requirement can be setup over multiple alternate routes using one of a number of distribution algorithms. The purpose of switching off RLB for a given time. This is...