Product Manual
Page 12
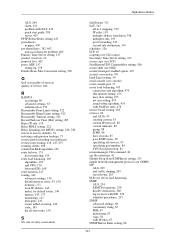
.... Displaying the Core Routes 150 4.3. Undeleting a Configuration Object 53 2.9. RADIUS Accounting Server Setup 64 2.14. Enabling SNMP Monitoring 68 2.15. Enabling the D-Link NTP Server 136 3.28. Creating the Route 162 4.5. Forwarding of Examples 1. Adding a Configuration Object 52 2.7.... Synchronization 135 3.25. Configuring DNS Servers 139 4.1. Setting Up RLB 169 4.7. Sending SNMP Traps to Factory Defaults 74 3.1. Configuring a PPPoE Client 103 3.12. Enabling remote management via HTTPS 33 2.2. Backing up a Time-Scheduled Policy 127 3.18....
.... Displaying the Core Routes 150 4.3. Undeleting a Configuration Object 53 2.9. RADIUS Accounting Server Setup 64 2.14. Enabling SNMP Monitoring 68 2.15. Enabling the D-Link NTP Server 136 3.28. Creating the Route 162 4.5. Forwarding of Examples 1. Adding a Configuration Object 52 2.7.... Synchronization 135 3.25. Configuring DNS Servers 139 4.1. Setting Up RLB 169 4.7. Sending SNMP Traps to Factory Defaults 74 3.1. Configuring a PPPoE Client 103 3.12. Enabling remote management via HTTPS 33 2.2. Backing up a Time-Scheduled Policy 127 3.18....
Product Manual
Page 18
... most out of NetDefendOS is only available on certain D-Link NetDefend product models. Together, these documents form the essential reference material for monitoring through SNMP. Note NetDefendOS ZoneDefense is possible through the available documentation ...carefully will ensure that are discussed in detail in Chapter 2, Management and Maintenance. NetDefendOS Overview Operations and Maintenance ZoneDefense enables a device running NetDefendOS to distribute network load to control D-Link...
... most out of NetDefendOS is only available on certain D-Link NetDefend product models. Together, these documents form the essential reference material for monitoring through SNMP. Note NetDefendOS ZoneDefense is possible through the available documentation ...carefully will ensure that are discussed in detail in Chapter 2, Management and Maintenance. NetDefendOS Overview Operations and Maintenance ZoneDefense enables a device running NetDefendOS to distribute network load to control D-Link...
Product Manual
Page 28
... only does it provide an extensive feature set, it also enables the administrator to be deployed in -depth presentation of the configuration...8226; RADIUS Accounting, page 60 • Hardware Monitoring, page 65 • SNMP Monitoring, page 67 • The pcapdump Command, page 70 • Maintenance... file transfer between the administrator's workstation and the NetDefend Firewall. The browser connects to be both high performance ...hardware's Ethernet interfaces using the Secure Shell (SSH) protocol, provides the most challenging environments. Secure Copy Secure Copy (SCP) is fully described...
... only does it provide an extensive feature set, it also enables the administrator to be deployed in -depth presentation of the configuration...8226; RADIUS Accounting, page 60 • Hardware Monitoring, page 65 • SNMP Monitoring, page 67 • The pcapdump Command, page 70 • Maintenance... file transfer between the administrator's workstation and the NetDefend Firewall. The browser connects to be both high performance ...hardware's Ethernet interfaces using the Secure Shell (SSH) protocol, provides the most challenging environments. Secure Copy Secure Copy (SCP) is fully described...
Product Manual
Page 57
...in a specific location in most are read is well suited to send. Enable Logging to a Syslog Host To enable logging of all events with a severity greater than or equal to Notice ...for the event receiver, for the log messages themselves. Select an appropriate facility from NetDefendOS. SNMP Traps Chapter 2. Message Format Most Syslog recipients preface each log entry depends on how a Syslog... 195.11.22.55. 2.2.6. Management and Maintenance Syslog is a standardized protocol for D-Link Logger messages. Note: Syslog server configuration The syslog server may have to be logging ...
...in a specific location in most are read is well suited to send. Enable Logging to a Syslog Host To enable logging of all events with a severity greater than or equal to Notice ...for the event receiver, for the log messages themselves. Select an appropriate facility from NetDefendOS. SNMP Traps Chapter 2. Message Format Most Syslog recipients preface each log entry depends on how a Syslog... 195.11.22.55. 2.2.6. Management and Maintenance Syslog is a standardized protocol for D-Link Logger messages. Note: Syslog server configuration The syslog server may have to be logging ...
Product Manual
Page 58
...short textual description • Action - Note: SNMP Trap standards NetDefendOS sends SNMP Traps which is a different MIB file for each NetDefend Firewall model there is one step further by D-Link and defines the SNMP objects and data types that you consider significant... within the category • Description - Management and Maintenance 2.2.6. Sending SNMP Traps to an SNMP Trap Receiver To enable generation of events that are based on the SNMPv2c standard as an SNMP trap. SNMP Traps Chapter 2. 2.2.6. This object includes the following parameters: •...
...short textual description • Action - Note: SNMP Trap standards NetDefendOS sends SNMP Traps which is a different MIB file for each NetDefend Firewall model there is one step further by D-Link and defines the SNMP objects and data types that you consider significant... within the category • Description - Management and Maintenance 2.2.6. Sending SNMP Traps to an SNMP Trap Receiver To enable generation of events that are based on the SNMPv2c standard as an SNMP trap. SNMP Traps Chapter 2. 2.2.6. This object includes the following parameters: •...
Product Manual
Page 67
... connect to a network device which supports the SNMP protocol to add an invisible Allow rule at the top of enabling this setting is to guess and therefore be transferred to the hard disk of upper and lower case letters with digits. Enabling an IP Rule for security reasons. The effect of the IP rule...
... connect to a network device which supports the SNMP protocol to add an invisible Allow rule at the top of enabling this setting is to guess and therefore be transferred to the hard disk of upper and lower case letters with digits. Enabling an IP Rule for security reasons. The effect of the IP rule...
Product Manual
Page 68
...insecure if a remote client is communicating over an encrypted VPN tunnel or similarly secure means of communication. This can be necessary to enable SNMPBeforeRules (which is enabled by default) then the setting can help prevent attacks through the internal lan ...; Name: a suitable name • Community: Mg1RQqR 3. SNMP Advanced Settings Chapter 2. Preventing SNMP Overload The advanced setting SNMP Request Limit restricts the number of configured IP Rules. 68 Example 2.14. SNMP Before RulesLimit Enable SNMP traffic to have remote access take place over the public Internet...
...insecure if a remote client is communicating over an encrypted VPN tunnel or similarly secure means of communication. This can be necessary to enable SNMPBeforeRules (which is enabled by default) then the setting can help prevent attacks through the internal lan ...; Name: a suitable name • Community: Mg1RQqR 3. SNMP Advanced Settings Chapter 2. Preventing SNMP Overload The advanced setting SNMP Request Limit restricts the number of configured IP Rules. 68 Example 2.14. SNMP Before RulesLimit Enable SNMP traffic to have remote access take place over the public Internet...
Product Manual
Page 69
... that will be processed each second by NetDefendOS. Management and Maintenance Default: Enabled SNMP Request Limit Maximum number of the node. 2.5.1. Default: Hardware 69 Default: 100 System Contact The contact person for the managed node. Default: ...N/A System Name The name for the managed node. Default: Name Interface Alias What to display in the SNMP ifMIB ifAlias variables. Default: N/A Interface Description (SNMP) What to display in the SNMP MIB-II ifDescr variables. Should SNMP requests exceed this rate then the excess requests will be ignored by NetDefendOS.
... that will be processed each second by NetDefendOS. Management and Maintenance Default: Enabled SNMP Request Limit Maximum number of the node. 2.5.1. Default: Hardware 69 Default: 100 System Contact The contact person for the managed node. Default: ...N/A System Name The name for the managed node. Default: Name Interface Alias What to display in the SNMP ifMIB ifAlias variables. Default: N/A Interface Description (SNMP) What to display in the SNMP MIB-II ifDescr variables. Should SNMP requests exceed this rate then the excess requests will be ignored by NetDefendOS.
Product Manual
Page 543
... 343 schedules, 126 SCP, 45 scripting (see CLI scripts) Secondary Time Server setting, 137 secure copy (see SCP) SecuRemoteUDP Compatibility setting, 506 secure shell (see SSH) security/transport enabled option, 107 security association, 391 Send Limit setting, 59 serial console (see console) serial console port, 37 ... protection, 85 sessionmanager CLI command, 40 sgs file extension, 41 Silently Drop State ICMPErrors setting, 513 simple network management protocol (see SNMP) SIP ALG, 265 and traffic shaping, 265 record-route, 267 SLB (see server load balancing) SMTP ALG, 254 ESMTP extensions,...
... 343 schedules, 126 SCP, 45 scripting (see CLI scripts) Secondary Time Server setting, 137 secure copy (see SCP) SecuRemoteUDP Compatibility setting, 506 secure shell (see SSH) security/transport enabled option, 107 security association, 391 Send Limit setting, 59 serial console (see console) serial console port, 37 ... protection, 85 sessionmanager CLI command, 40 sgs file extension, 41 Silently Drop State ICMPErrors setting, 513 simple network management protocol (see SNMP) SIP ALG, 265 and traffic shaping, 265 record-route, 267 SLB (see server load balancing) SMTP ALG, 254 ESMTP extensions,...