Product Manual
Page 4
... 2.3.1. Maintenance 73 2.7.1. Auto-Update Mechanism 73 2.7.2. NetDefendOS Overview 16 1.1. State-based Architecture 19 1.2.2. The Web Interface 29 2.1.4. The CLI 33 2.1.5. Creating Log Receivers 56 2.2.4. Activating RADIUS Accounting 62 2.3.5. RADIUS Advanced ...RADIUS Accounting Security 62 2.3.6. Accounting and System Shutdowns 63 2.3.9. Fundamentals 77 3.1. Overview 77 3.1.2. Address Groups 80 3.1.5. Auto-Generated Address Objects 81 3.1.6. Address Book Folders 81 3.2. SNMP Traps 58 2.2.7. Handling Unresponsive Servers 63 2.3.8....
... 2.3.1. Maintenance 73 2.7.1. Auto-Update Mechanism 73 2.7.2. NetDefendOS Overview 16 1.1. State-based Architecture 19 1.2.2. The Web Interface 29 2.1.4. The CLI 33 2.1.5. Creating Log Receivers 56 2.2.4. Activating RADIUS Accounting 62 2.3.5. RADIUS Advanced ...RADIUS Accounting Security 62 2.3.6. Accounting and System Shutdowns 63 2.3.9. Fundamentals 77 3.1. Overview 77 3.1.2. Address Groups 80 3.1.5. Auto-Generated Address Objects 81 3.1.6. Address Book Folders 81 3.2. SNMP Traps 58 2.2.7. Handling Unresponsive Servers 63 2.3.8....
Product Manual
Page 6
...for D-Link Models 315 6.5.3. The Jolt2 Attack 329 6.6.10. Distributed DoS Attacks 329 6.7. Blacklisting Hosts and Networks 331 6 Overview 207 4.7.2. Overview 223 5.2. Security Mechanisms... Flood Attacks 329 6.6.9. Advanced Settings for Transparent Mode 218 5. Overview 240 6.2.2. Web Content Filtering 292 6.3.1. Active Content Handling 292 6.3.3. Intrusion Detection and Prevention 315 ... 4.7. DHCP Servers 224 5.2.1. Custom Options 228 5.3. The FTP ALG 244 6.2.4. Anti-Virus Options 311 6.5. IDP Pattern Matching 319 6.5.6. Subscribing to the D-Link Anti-Virus ...
...for D-Link Models 315 6.5.3. The Jolt2 Attack 329 6.6.10. Distributed DoS Attacks 329 6.7. Blacklisting Hosts and Networks 331 6 Overview 207 4.7.2. Overview 223 5.2. Security Mechanisms... Flood Attacks 329 6.6.9. Advanced Settings for Transparent Mode 218 5. Overview 240 6.2.2. Web Content Filtering 292 6.3.1. Active Content Handling 292 6.3.3. Intrusion Detection and Prevention 315 ... 4.7. DHCP Servers 224 5.2.1. Custom Options 228 5.3. The FTP ALG 244 6.2.4. Anti-Virus Options 311 6.5. IDP Pattern Matching 319 6.5.6. Subscribing to the D-Link Anti-Virus ...
Product Manual
Page 13
... 2 215 5.1. Limiting Bandwidth in a Corporate Environment 285 6.11. if1 Configuration 202 4.16. Group Translation 203 4.17. Two Phones Behind Different NetDefend Firewalls 280 6.7. Using Private IP Addresses 281 6.8. Enabling Traffic to a Web Server on an Internal Network 346 7.5. User Authentication Setup for H.323 288 6.12. Setting up an L2TP Tunnel Over IPsec 427...
... 2 215 5.1. Limiting Bandwidth in a Corporate Environment 285 6.11. if1 Configuration 202 4.16. Group Translation 203 4.17. Two Phones Behind Different NetDefend Firewalls 280 6.7. Using Private IP Addresses 281 6.8. Enabling Traffic to a Web Server on an Internal Network 346 7.5. User Authentication Setup for H.323 288 6.12. Setting up an L2TP Tunnel Over IPsec 427...
Product Manual
Page 17
...and detection of attacks and can be whitelisted or blacklisted. On some D-Link NetDefend product models. More information about the IDP capabilities of the VPN types, and can provide individual security policies for this feature, seeSection 6.4, "Anti-Virus Scanning". To mitigate...limiting and balancing of this can be subjected to a web usage policy. Server Load Balancing 17 NetDefendOS supports IPsec, L2TP and PPTP based VPNs concurrently, can act as either server or client for all D-Link NetDefend product models as a subscription service. NetDefendOS features integrated...
...and detection of attacks and can be whitelisted or blacklisted. On some D-Link NetDefend product models. More information about the IDP capabilities of the VPN types, and can provide individual security policies for this feature, seeSection 6.4, "Anti-Virus Scanning". To mitigate...limiting and balancing of this can be subjected to a web usage policy. Server Load Balancing 17 NetDefendOS supports IPsec, L2TP and PPTP based VPNs concurrently, can act as either server or client for all D-Link NetDefend product models as a subscription service. NetDefendOS features integrated...
Product Manual
Page 28
...). Various files used by NetDefendOS can be both high performance and high reliability. Managing NetDefendOS 2.1.1. Secure Copy Secure Copy (SCP) is a widely used as the Web User Interface or WebUI) is built into NetDefendOS and provides a user-friendly and intuitive graphical management...web server, allowing web pages to be in the most fine-grained control over all workstation platforms. SCP is provided with the various management interfaces. No specific SCP client is a complement to one of file transfer between the administrator's workstation and the NetDefend ...
...). Various files used by NetDefendOS can be both high performance and high reliability. Managing NetDefendOS 2.1.1. Secure Copy Secure Copy (SCP) is a widely used as the Web User Interface or WebUI) is built into NetDefendOS and provides a user-friendly and intuitive graphical management...web server, allowing web pages to be in the most fine-grained control over all workstation platforms. SCP is provided with the various management interfaces. No specific SCP client is a complement to one of file transfer between the administrator's workstation and the NetDefend ...
Product Manual
Page 80
... > Add > Ethernet Address 2. Consequently, individual IP Address objects have IP addresses that the group will be used with the web server hosts as the MAC Address 4. IP Addresses Can Be Excluded When groups are not restricted to cope with the burden of public... policies allowing traffic to then explicitly exclude the IP address 192.168.2.1. The servers have to explicitly exclude addresses from the Internet. Specify a suitable name for the Ethernet Address object, for example web-servers, could be referenced to simplify configuration. Now, a single policy can be ...
... > Add > Ethernet Address 2. Consequently, individual IP Address objects have IP addresses that the group will be used with the web server hosts as the MAC Address 4. IP Addresses Can Be Excluded When groups are not restricted to cope with the burden of public... policies allowing traffic to then explicitly exclude the IP address 192.168.2.1. The servers have to explicitly exclude addresses from the Internet. Specify a suitable name for the Ethernet Address object, for example web-servers, could be referenced to simplify configuration. Now, a single policy can be ...
Product Manual
Page 326
... Flood attack • The Jolt2 attack 6.6.3. Some of the most commonly used DoS attacks have been: • The Ping of the 326 Security Mechanisms 6.6. Not only can a company reach a larger number of customers via the Internet, it can no longer respond to with names such ... thing any network administrator wants to run over it is to experience. At the same time, using NetDefend Firewalls to protect organizations against organizations resulting in paralysed web servers that the DoS attack floods the network and ties up critical resources used to run business critical applications....
... Flood attack • The Jolt2 attack 6.6.3. Some of the most commonly used DoS attacks have been: • The Ping of the 326 Security Mechanisms 6.6. Not only can a company reach a larger number of customers via the Internet, it can no longer respond to with names such ... thing any network administrator wants to run over it is to experience. At the same time, using NetDefend Firewalls to protect organizations against organizations resulting in paralysed web servers that the DoS attack floods the network and ties up critical resources used to run business critical applications....
Product Manual
Page 329
Security Mechanisms 6.6.8. This is also sometimes referred to arrive so that has an ALG associated with it is unable to respond to SYN ACKs sent in ... It should be thrown away as few hundred packets per second will be the first to be dropped to be explicitly enabled on the victim's web server so that SYN Flood Protection does not need to make room for the attack, they may not show up in the IP rule set to...
Security Mechanisms 6.6.8. This is also sometimes referred to arrive so that has an ALG associated with it is unable to respond to SYN ACKs sent in ... It should be thrown away as few hundred packets per second will be the first to be dropped to be explicitly enabled on the victim's web server so that SYN Flood Protection does not need to make room for the attack, they may not show up in the IP rule set to...
Product Manual
Page 339
...the PPTP tunnel. NAT Chapter 7. Communication with L2TP instead of the PPTP tunnel at the firewall. When an application, such as a web server, now receives requests from the client it is clearly a small processing overhead involved with their local ISP using PPTP. This same technique ... 9.5.4, "PPTP/L2TP Clients". 339 This arrangement is no longer encapsulated by PPTP. We shall examine the typical case where the NetDefend Firewall acts as though they are discussed further in the diagram below. Address Translation anonymize traffic between the firewall and the Internet,...
...the PPTP tunnel. NAT Chapter 7. Communication with L2TP instead of the PPTP tunnel at the firewall. When an application, such as a web server, now receives requests from the client it is clearly a small processing overhead involved with their local ISP using PPTP. This same technique ... 9.5.4, "PPTP/L2TP Clients". 339 This arrangement is no longer encapsulated by PPTP. We shall examine the typical case where the NetDefend Firewall acts as though they are discussed further in the diagram below. Address Translation anonymize traffic between the firewall and the Internet,...
Product Manual
Page 344
... LAN. The Role of a Single IP Address (1:1) Chapter 7. The NetDefend Firewall is connected to a Protected Web Server in a DMZ In this is the port's intended use it could be used for other purposes and any Ethernet port could be any SourceNetwork=all models of D-Link NetDefend hardware, there is a specific Ethernet port which is reachable...
... LAN. The Role of a Single IP Address (1:1) Chapter 7. The NetDefend Firewall is connected to a Protected Web Server in a DMZ In this is the port's intended use it could be used for other purposes and any Ethernet port could be any SourceNetwork=all models of D-Link NetDefend hardware, there is a specific Ethernet port which is reachable...
Product Manual
Page 345
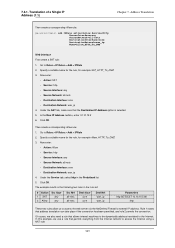
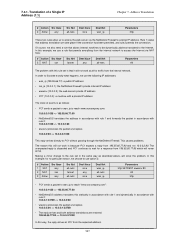
... Iface core core Dest Net wan_ip wan_ip Parameters http SETDEST 10.10.10.5 80 http These two rules allow us to access the web server via the NetDefend Firewall's external IP address. In this example, we also need a rule that permits everything from the internal network to Rules > ...: • Action: SAT • Service: http • Source Interface: any Src Net all-nets all -nets DestinationInterface=core DestinationNetwork=wan_ip Name=Allow_HTTP_To_DMZ Web Interface First create a SAT rule: 1. In the New IP Address textbox, enter 10.10.10.5 6. Go to access the Internet using a NAT ...
... Iface core core Dest Net wan_ip wan_ip Parameters http SETDEST 10.10.10.5 80 http These two rules allow us to access the web server via the NetDefend Firewall's external IP address. In this example, we also need a rule that permits everything from the internal network to Rules > ...: • Action: SAT • Service: http • Source Interface: any Src Net all-nets all -nets DestinationInterface=core DestinationNetwork=wan_ip Name=Allow_HTTP_To_DMZ Web Interface First create a SAT rule: 1. In the New IP Address textbox, enter 10.10.10.5 6. Go to access the Internet using a NAT ...
Product Manual
Page 346
... all circumstances into account. For this configuration, it only applies to communicate with the web server. However, suppose that it makes no difference. Example 7.4. From a security standpoint, this model in the NetDefend Firewall and connect it using a public address. Translation of a web server with this rule set ? we want to implement address translation for each interface...
... all circumstances into account. For this configuration, it only applies to communicate with the web server. However, suppose that it makes no difference. Example 7.4. From a security standpoint, this model in the NetDefend Firewall and connect it using a public address. Translation of a web server with this rule set ? we want to implement address translation for each interface...
Product Manual
Page 347
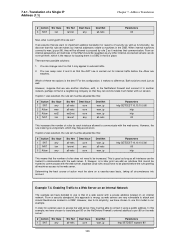
...Iface 2 Allow any Src Net all-nets Dest Iface core Dest Net wan_ip Parameters http These two rules allow us to access the web server via NAT hide: # Action Src Iface 3 NAT lan Src Net lannet Dest Iface any core Dest Net wan_ip all-nets wan_ip ...use the following IP addresses: • wan_ip (195.55.66.77): a public IP address • lan_ip (10.0.0.1): the NetDefend Firewall's private internal IP address • wwwsrv (10.0.0.2): the web servers private IP address • PC1 (10.0.0.3): a machine with rule 2: 10.0.0.1:32789 => 10.0.0.2:80 • wwwsrv processes the packet...
...Iface 2 Allow any Src Net all-nets Dest Iface core Dest Net wan_ip Parameters http These two rules allow us to access the web server via NAT hide: # Action Src Iface 3 NAT lan Src Net lannet Dest Iface any core Dest Net wan_ip all-nets wan_ip ...use the following IP addresses: • wan_ip (195.55.66.77): a public IP address • lan_ip (10.0.0.1): the NetDefend Firewall's private internal IP address • wwwsrv (10.0.0.2): the web servers private IP address • PC1 (10.0.0.3): a machine with rule 2: 10.0.0.1:32789 => 10.0.0.2:80 • wwwsrv processes the packet...
Product Manual
Page 348
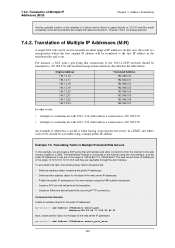
... which are reachable through the dmz interface. The NetDefend Firewall is a transposition where the first original IP address will permit the incoming HTTP connections. The web servers have IP addresses in a DMZ, and where each server should be translated to the 194.1.2.16/29 network... words: • Attempts to communicate with 194.1.2.16 will result in a connection to 192.168.0.50. • Attempts to five web servers located in a DMZ. Example 7.5. An example of Multiple IP Addresses (M:N) Chapter 7. Address Translation Another possible solution to this problem is...
... which are reachable through the dmz interface. The NetDefend Firewall is a transposition where the first original IP address will permit the incoming HTTP connections. The web servers have IP addresses in a DMZ, and where each server should be translated to the 194.1.2.16/29 network... words: • Attempts to communicate with 194.1.2.16 will result in a connection to 192.168.0.50. • Attempts to five web servers located in a DMZ. Example 7.5. An example of Multiple IP Addresses (M:N) Chapter 7. Address Translation Another possible solution to this problem is...
Product Manual
Page 349
Translation of the web server IP addresses: 1. Go to Objects > Address Book > Add > IP address 2. Go to Objects > Address Book > Add > IP address 2. Go to Interfaces > ARP > Add > ARP 2. Click ... every IP address: gw-world:/> add ARP Interface=wan IP=195.55.66.77 mode=Publish Repeat this for all -nets DestinationInterface=wan DestinationNetwork=wwwsrv_pub Web Interface Create an address object for example wwwsrv_pub 3. Specify a suitable name for the object, for the base of Multiple IP Addresses (M:N) Chapter 7. Go to Rules...
Translation of the web server IP addresses: 1. Go to Objects > Address Book > Add > IP address 2. Go to Objects > Address Book > Add > IP address 2. Go to Interfaces > ARP > Add > ARP 2. Click ... every IP address: gw-world:/> add ARP Interface=wan IP=195.55.66.77 mode=Publish Repeat this for all -nets DestinationInterface=wan DestinationNetwork=wwwsrv_pub Web Interface Create an address object for example wwwsrv_pub 3. Specify a suitable name for the object, for the base of Multiple IP Addresses (M:N) Chapter 7. Go to Rules...
Product Manual
Page 351
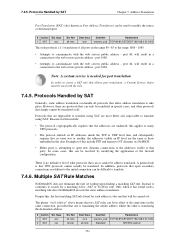
... static address translation. Note: A custom service is translating the sender address whilst the other protocols that can be in addition to the web servers private address - Reasons for a matching Allow, NAT or FwdFast rule. In addition, protocols that open new dynamic connections to the addresses...does not terminate the rule set lookup upon finding a matching SAT rule. 7.4.5. Protocols that allow address translation to communicate with the web servers public address - The phrase "each address is the one is needed for each address" above means that will be used to modify...
... static address translation. Note: A custom service is translating the sender address whilst the other protocols that can be in addition to the web servers private address - Reasons for a matching Allow, NAT or FwdFast rule. In addition, protocols that open new dynamic connections to the addresses...does not terminate the rule set lookup upon finding a matching SAT rule. 7.4.5. Protocols that allow address translation to communicate with the web servers public address - The phrase "each address is the one is needed for each address" above means that will be used to modify...
Product Manual
Page 352
...1 SAT 2 SAT Src Iface lan any other attempt is almost correct; In this instance, both rules are set in conjunction with the web servers public address, it will be redirected to the private address of static address translation using FwdFast rules to wwwsrv. SAT and FwdFast Rules Chapter...the packets will be interpreted as follows: • External traffic to wan_ip:80 will match rules 1 and 3, and will be sent to a web server located on the same connection. Correct. • Internal traffic to wan_ip:80 will match rules 1 and 3, and will be carried out concurrently ...
...1 SAT 2 SAT Src Iface lan any other attempt is almost correct; In this instance, both rules are set in conjunction with the web servers public address, it will be redirected to the private address of static address translation using FwdFast rules to wwwsrv. SAT and FwdFast Rules Chapter...the packets will be interpreted as follows: • External traffic to wan_ip:80 will match rules 1 and 3, and will be sent to a web server located on the same connection. Correct. • Internal traffic to wan_ip:80 will match rules 1 and 3, and will be carried out concurrently ...
Product Manual
Page 379
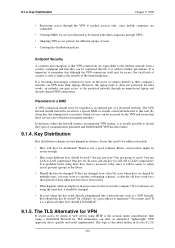
... advance. Placement in a special DMZ or outside a firewall dedicated to the internal network from their company's network via VPN from a security standpoint and that they are vulnerable. • Creating DMZs for services that is quickly and easily implemented. Key Distribution Key distribution schemes ...network unit, such as an integral part of users? In cases where keys are using a NetDefend Firewall for all LAN-to memorize? If several users are shared by clients to web servers using HTTP is the scenario under consideration, then using the same key, it with other words...
... advance. Placement in a special DMZ or outside a firewall dedicated to the internal network from their company's network via VPN from a security standpoint and that they are vulnerable. • Creating DMZs for services that is quickly and easily implemented. Key Distribution Key distribution schemes ...network unit, such as an integral part of users? In cases where keys are using a NetDefend Firewall for all LAN-to memorize? If several users are shared by clients to web servers using HTTP is the scenario under consideration, then using the same key, it with other words...
Product Manual
Page 463
... : Rule Name all-in Forward Pipes in -pipe and the return pipe is the out-pipe. 10.1.10. More Pipe Examples Chapter 10. In addition, server traffic is initiated from the inside and going to put a "catch-all -nets Selected Service All Prece dence 0 463 However, the external interface (wan) should... reversed: the forward pipe is guaranteed 500 kbps of pipes needs to best effort. SAT with Pipes If SAT is being used, for example with a web server or ftp server, that is to the external IP address.
... : Rule Name all-in Forward Pipes in -pipe and the return pipe is the out-pipe. 10.1.10. More Pipe Examples Chapter 10. In addition, server traffic is initiated from the inside and going to put a "catch-all -nets Selected Service All Prece dence 0 463 However, the external interface (wan) should... reversed: the forward pipe is guaranteed 500 kbps of pipes needs to best effort. SAT with Pipes If SAT is being used, for example with a web server or ftp server, that is to the external IP address.
Product Manual
Page 530
... attack FTP protocol and implementation Login attacks FTP buffer overflow Bomberclone game Generic game servers/clients UnReal Game server Apache httpd Badblue web server HTTP CGI Cisco Embedded Web Server General HTTP activities HTTP Attacks specific to MS IIS web server Buffer overflow for HTTP servers Tomcat JSP ICMP protocol and implementation IGMP IMAP protocol/implementation AOL IM Instant...
... attack FTP protocol and implementation Login attacks FTP buffer overflow Bomberclone game Generic game servers/clients UnReal Game server Apache httpd Badblue web server HTTP CGI Cisco Embedded Web Server General HTTP activities HTTP Attacks specific to MS IIS web server Buffer overflow for HTTP servers Tomcat JSP ICMP protocol and implementation IGMP IMAP protocol/implementation AOL IM Instant...