Product Manual
Page 4
... 47 2.1.8. Creating Log Receivers 56 2.2.4. Advanced Log Settings 59 2.3. Interim Accounting Messages 62 2.3.4. Limitations with Configurations 49 2.2. Auto-Update Mechanism 73 2.7.2. Overview 77 3.1.2. NetDefendOS Building Blocks 19 1.2.3. RADIUS Accounting Messages 60... Hardware Monitoring 65 2.5. Fundamentals 77 3.1. Events and Logging 55 2.2.1. Log Messages 55 2.2.3. RADIUS Accounting Security 62 2.3.6. Handling Unresponsive Servers 63 2.3.8. IP Addresses 77 3.1.3. State-based Architecture 19 1.2.2. Logging to MemoryLogReceiver...
... 47 2.1.8. Creating Log Receivers 56 2.2.4. Advanced Log Settings 59 2.3. Interim Accounting Messages 62 2.3.4. Limitations with Configurations 49 2.2. Auto-Update Mechanism 73 2.7.2. Overview 77 3.1.2. NetDefendOS Building Blocks 19 1.2.3. RADIUS Accounting Messages 60... Hardware Monitoring 65 2.5. Fundamentals 77 3.1. Events and Logging 55 2.2.1. Log Messages 55 2.2.3. RADIUS Accounting Security 62 2.3.6. Handling Unresponsive Servers 63 2.3.8. IP Addresses 77 3.1.3. State-based Architecture 19 1.2.2. Logging to MemoryLogReceiver...
Product Manual
Page 5
... Routing Table Selection 161 4.3.5. Multicast Forwarding with SAT Multiplex Rules 195 4.6.3. User Manual 3.2.3. Overview 90 3.3.2. The NetDefendOS ARP Cache 108 3.4.3. Security Policies 116 3.5.2. Configuration Object Groups 122 3.6. Time Servers 133 3.8.4. Static Routing 147 4.2.3. Policy-based Routing Tables 160 4.3.3. OSPF 171 4.5.1. Service Groups 88 3.2.6....Service Timeouts 89 3.3. Interface Groups 107 3.4. Overview 142 4.2. OSPF Concepts 174 4.5.3. An OSPF Example 191 4.6. IGMP Configuration 199 4.6.4. Policy-based Routing 160 4.3.1.
... Routing Table Selection 161 4.3.5. Multicast Forwarding with SAT Multiplex Rules 195 4.6.3. User Manual 3.2.3. Overview 90 3.3.2. The NetDefendOS ARP Cache 108 3.4.3. Security Policies 116 3.5.2. Configuration Object Groups 122 3.6. Time Servers 133 3.8.4. Static Routing 147 4.2.3. Policy-based Routing Tables 160 4.3.3. OSPF 171 4.5.1. Service Groups 88 3.2.6....Service Timeouts 89 3.3. Interface Groups 107 3.4. Overview 142 4.2. OSPF Concepts 174 4.5.3. An OSPF Example 191 4.6. IGMP Configuration 199 4.6.4. Policy-based Routing 160 4.3.1.
Product Manual
Page 10
... or MS-CHAPv2 366 9.1. Pipe Rules Determine Pipe Usage 446 10.2. The Eight Pipe Precedences 451 10.5. A Server Load Balancing Configuration 473 10 Packet Flow Schematic Part I 23 1.2. Expanded Apply Rules Logic 26 3.1. VLAN Connections 99 3.2. An ARP Publish Ethernet Frame...Transparent Mode Scenario 2 215 4.22. TLS Termination 290 6.8. The ESP protocol 399 9.3. Traffic Grouped By IP Address 457 10.7. Virtual Links Connecting Areas 177 4.11. NetDefendOS OSPF Objects 179 4.13. Deploying an ALG 240 6.2. The Role of Figures 1.1. Normal LDAP Authentication 365...
... or MS-CHAPv2 366 9.1. Pipe Rules Determine Pipe Usage 446 10.2. The Eight Pipe Precedences 451 10.5. A Server Load Balancing Configuration 473 10 Packet Flow Schematic Part I 23 1.2. Expanded Apply Rules Logic 26 3.1. VLAN Connections 99 3.2. An ARP Publish Ethernet Frame...Transparent Mode Scenario 2 215 4.22. TLS Termination 290 6.8. The ESP protocol 399 9.3. Traffic Grouped By IP Address 457 10.7. Virtual Links Connecting Areas 177 4.11. NetDefendOS OSPF Objects 179 4.13. Deploying an ALG 240 6.2. The Role of Figures 1.1. Normal LDAP Authentication 365...
Product Manual
Page 12
... Policy-based Routing Table 162 4.4. Setting Up RLB 169 4.7. Multicast Forwarding - Listing Configuration Objects 50 2.4. Activating and Committing a Configuration 54 2.11. Viewing a Specific Service 83 3.8. Configuring a PPPoE Client 103 3.12. Forwarding of Examples 1. List of Multicast Traffic using ... 3.25. Enabling the D-Link NTP Server 136 3.28. Creating the Route 162 4.5. Creating an OSPF Router Process 192 4.8. Enabling remote management via HTTPS 33 2.2. Creating a Custom TCP/UDP Service 86 3.9. Listing Modified Configuration Objects 53 2.10. Adding...
... Policy-based Routing Table 162 4.4. Setting Up RLB 169 4.7. Multicast Forwarding - Listing Configuration Objects 50 2.4. Activating and Committing a Configuration 54 2.11. Viewing a Specific Service 83 3.8. Configuring a PPPoE Client 103 3.12. Forwarding of Examples 1. List of Multicast Traffic using ... 3.25. Enabling the D-Link NTP Server 136 3.28. Creating the Route 162 4.5. Creating an OSPF Router Process 192 4.8. Enabling remote management via HTTPS 33 2.2. Creating a Custom TCP/UDP Service 86 3.9. Listing Modified Configuration Objects 53 2.10. Adding...
Product Manual
Page 13
...Stripping ActiveX and Java applets 293 6.14. Enabling Audit Mode 299 6.17. Configuring an SMTP Log Receiver 323 6.21. Enabling Traffic to a Protected Web Server in a Corporate Environment 285 6.11. Configuring a RADIUS Server 372 8.4. Setting up a DHCP server 225 5.2. IGMP -... blocked site 300 6.18. Adding a Host to register with Gatekeeper 282 6.9. Setting up Transparent Mode for roaming clients 411 9.7. if2 Configuration - Allowing the H.323 Gateway to the Whitelist 332 7.1. Setting up an Access Rule 239 6.2. User Manual 4.14. H.323 with ...
...Stripping ActiveX and Java applets 293 6.14. Enabling Audit Mode 299 6.17. Configuring an SMTP Log Receiver 323 6.21. Enabling Traffic to a Protected Web Server in a Corporate Environment 285 6.11. Configuring a RADIUS Server 372 8.4. Setting up a DHCP server 225 5.2. IGMP -... blocked site 300 6.18. Adding a Host to register with Gatekeeper 282 6.9. Setting up Transparent Mode for roaming clients 411 9.7. if2 Configuration - Allowing the H.323 Gateway to the Whitelist 332 7.1. Setting up an Access Rule 239 6.2. User Manual 4.14. H.323 with ...
Product Manual
Page 14
... a new window (some basic knowledge of management user interfaces. Where a "See chapter/section" link (such as: see Chapter 9, VPN) is provided in the main text, this can be ... may appear in a box with NetDefendOS and administrators have a choice of networks and network security. This is deliberate and is done because the manual deals specifically with a gray background.... Intended Audience The target audience for this reference guide is Administrators who are responsible for configuring and managing NetDefend Firewalls which are also typically a numbered list showing what the example ...
... a new window (some basic knowledge of management user interfaces. Where a "See chapter/section" link (such as: see Chapter 9, VPN) is provided in the main text, this can be ... may appear in a box with NetDefendOS and administrators have a choice of networks and network security. This is deliberate and is done because the manual deals specifically with a gray background.... Intended Audience The target audience for this reference guide is Administrators who are responsible for configuring and managing NetDefend Firewalls which are also typically a numbered list showing what the example ...
Product Manual
Page 16
... as well as multicast routing capabilities. NetDefendOS Overview This chapter outlines the key features of different ways. These objects allow the configuration of NetDefendOS in an almost limitless number of NetDefendOS. • Features, page 16 • NetDefendOS Architecture, page 19 &#...through a set . This granular control allows the administrator to determine what traffic is to negate the risk from security attacks. Features D-Link NetDefendOS is covered in -depth administrative control of address translation needs. Key Features NetDefendOS has an extensive feature set...
... as well as multicast routing capabilities. NetDefendOS Overview This chapter outlines the key features of different ways. These objects allow the configuration of NetDefendOS in an almost limitless number of NetDefendOS. • Features, page 16 • NetDefendOS Architecture, page 19 &#...through a set . This granular control allows the administrator to determine what traffic is to negate the risk from security attacks. Features D-Link NetDefendOS is covered in -depth administrative control of address translation needs. Key Features NetDefendOS has an extensive feature set...
Product Manual
Page 20
... to 9 below . 5. The source interface is found, that VLAN interface becomes the source interface for actually implementing NetDefendOS security policies. If one is determined as carrying out address translation and server load balancing. If no matching interface is found, ...destination interface for all scenarios, however, the basic principles will only accept source IP addresses that interface becomes the source interface for a configured VLAN interface with a Source Interface. If no matching interface is found , the forwarding process continues at step 10 below . A ...
... to 9 below . 5. The source interface is found, that VLAN interface becomes the source interface for actually implementing NetDefendOS security policies. If one is determined as carrying out address translation and server load balancing. If no matching interface is found, ...destination interface for all scenarios, however, the basic principles will only accept source IP addresses that interface becomes the source interface for a configured VLAN interface with a Source Interface. If no matching interface is found , the forwarding process continues at step 10 below . A ...
Product Manual
Page 23
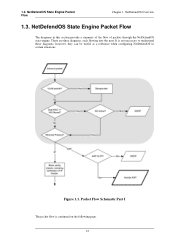
NetDefendOS Overview 1.3. There are three diagrams, each flowing into the next. It is continued on the following page. 23 Packet Flow Schematic Part I The packet flow is not necessary to understand these diagrams, however, they can be useful as a reference when configuring NetDefendOS in this section provide a summary of the flow of packets through the NetDefendOS state-engine. Figure 1.1. NetDefendOS State Engine Packet Flow Chapter 1. NetDefendOS State Engine Packet Flow The diagrams in certain situations. 1.3.
NetDefendOS Overview 1.3. There are three diagrams, each flowing into the next. It is continued on the following page. 23 Packet Flow Schematic Part I The packet flow is not necessary to understand these diagrams, however, they can be useful as a reference when configuring NetDefendOS in this section provide a summary of the flow of packets through the NetDefendOS state-engine. Figure 1.1. NetDefendOS State Engine Packet Flow Chapter 1. NetDefendOS State Engine Packet Flow The diagrams in certain situations. 1.3.
Product Manual
Page 28
...8226; The pcapdump Command, page 70 • Maintenance, page 73 2.1. Secure Copy Secure Copy (SCP) is recommended). Managing NetDefendOS 2.1.1. This means the product can be used by NetDefendOS can be in -depth presentation of the configuration subsystem as well as a description of how to CLI usage and provides... a secure means of the system. Various files used as the Web User Interface or WebUI) is built...
...8226; The pcapdump Command, page 70 • Maintenance, page 73 2.1. Secure Copy Secure Copy (SCP) is recommended). Managing NetDefendOS 2.1.1. This means the product can be used by NetDefendOS can be in -depth presentation of the configuration subsystem as well as a description of how to CLI usage and provides... a secure means of the system. Various files used as the Web User Interface or WebUI) is built...
Product Manual
Page 29
...recommended to change them. 2.1.3. This account has full administrative read /write administrative access. Important For security reasons, it is fully described in Section 2.1.6, "Secure Copy". Multiple Administration Logins NetDefendOS doesn't allow more than one predefined administrator account. If one administrator...key between power-up and NetDefendOS starting. Alternatively, they can be able to do basic configuration through a specific IPsec tunnel. It is the D-Link firmware loader that contains one LAN interface is available, LAN1 is enabled for NetDefendOS. ...
...recommended to change them. 2.1.3. This account has full administrative read /write administrative access. Important For security reasons, it is fully described in Section 2.1.6, "Secure Copy". Multiple Administration Logins NetDefendOS doesn't allow more than one predefined administrator account. If one administrator...key between power-up and NetDefendOS starting. Alternatively, they can be able to do basic configuration through a specific IPsec tunnel. It is the D-Link firmware loader that contains one LAN interface is available, LAN1 is enabled for NetDefendOS. ...
Product Manual
Page 31
... select a language other than English for the first time, the default username is always admin and the password is provided by default. 31 If no configuration changes have yet been uploaded to take a new user through the essential steps for NetDefendOS setup and establishing public Internet access. The Web Interface Chapter... a translation to run since this case the original english will start automatically to the NetDefend Firewall, the NetDefendOS Setup Wizard will be downloaded from the D-Link website. 2.1.3.
... select a language other than English for the first time, the default username is always admin and the password is provided by default. 31 If no configuration changes have yet been uploaded to take a new user through the essential steps for NetDefendOS setup and establishing public Internet access. The Web Interface Chapter... a translation to run since this case the original english will start automatically to the NetDefend Firewall, the NetDefendOS Setup Wizard will be downloaded from the D-Link website. 2.1.3.
Product Manual
Page 32
... • Update Center - Discards any changes made to expose additional sections. Manually update or schedule updates of the system configuration. This option provides the option to analyze a problem. Management and Maintenance For information about the default user name and password...status pages. • Home - Upgrade the firewall's firmware. • Technical support - C. Main Window The main window contains configuration or status details corresponding to the Web Interface is divided into three major sections: A. View license details or enter activation code. &#...
... • Update Center - Discards any changes made to expose additional sections. Manually update or schedule updates of the system configuration. This option provides the option to analyze a problem. Management and Maintenance For information about the default user name and password...status pages. • Home - Upgrade the firewall's firmware. • Technical support - C. Main Window The main window contains configuration or status details corresponding to the Web Interface is divided into three major sections: A. View license details or enter activation code. &#...
Product Manual
Page 33
... all management traffic coming from the dropdown lists: • User Database: AdminUsers • Interface: any user on the Logout button at the right of system configuration. Enter a Name for the HTTP/HTTPS remote management policy, for informational purposes only. It is a problem with access to your workstation to get unauthorized access...
... all management traffic coming from the dropdown lists: • User Database: AdminUsers • Interface: any user on the Logout button at the right of system configuration. Enter a Name for the HTTP/HTTPS remote management policy, for informational purposes only. It is a problem with access to your workstation to get unauthorized access...
Product Manual
Page 34
...add a new IP4Address object with the structure: . The CLI Chapter 2. The CLI provides a comprehensive set - For a complete reference for using the Secure Shell (SSH) protocol from an SSH client. Tip: Getting help about help Typing the CLI command: gw-world:/> help help will make the last ...object. This section only provides a summary for all CLI commands, see the separate D-Link CLI Reference Guide. For example, pressing the up and down arrow keys allow the display and modification of configuration data as well as an IP address or a rule to set of Microsoft Windows™...
...add a new IP4Address object with the structure: . The CLI Chapter 2. The CLI provides a comprehensive set - For a complete reference for using the Secure Shell (SSH) protocol from an SSH client. Tip: Getting help about help Typing the CLI command: gw-world:/> help help will make the last ...object. This section only provides a summary for all CLI commands, see the separate D-Link CLI Reference Guide. For example, pressing the up and down arrow keys allow the display and modification of configuration data as well as an IP address or a rule to set of Microsoft Windows™...
Product Manual
Page 37
... . To now connect a terminal to the console port on scripts see the D-Link Quick Start Guide . The CLI Chapter 2. If a duplicate IP rule name is to IP addresses. When DNS lookup needs to be configured in some Microsoft Windows™ editions). To use the console port, you need the... console port uses the following equipment: • A terminal or a computer with a duplicated name will enforce unique naming within an object type. An appliance package includes a RS-232 null-modem cable. Connect the other end of the cable to the terminal or the serial connector of the RS-232...
... . To now connect a terminal to the console port on scripts see the D-Link Quick Start Guide . The CLI Chapter 2. If a duplicate IP rule name is to IP addresses. When DNS lookup needs to be configured in some Microsoft Windows™ editions). To use the console port, you need the... console port uses the following equipment: • A terminal or a computer with a duplicated name will enforce unique naming within an object type. An appliance package includes a RS-232 null-modem cable. Connect the other end of the cable to the terminal or the serial connector of the RS-232...
Product Manual
Page 39
... Firewall. If a commit command is separate The password that can be customized, for example, my-password the following CLI commands are made to the current configuration through the CLI, those changes permanent. Changing the CLI Prompt The default CLI prompt is: gw-world:/> where Device is described in the top level...
... Firewall. If a commit command is separate The password that can be customized, for example, my-password the following CLI commands are made to the current configuration through the CLI, those changes permanent. Changing the CLI Prompt The default CLI prompt is: gw-world:/> where Device is described in the top level...
Product Manual
Page 40
...RemoteMgmtHTTP HTTP_if2 Interface=if2 Network=all types of management sessions, including: • Secure Shell (SSH) CLI sessions. • Any CLI session through Ethernet interface if2 which already exist in a restored configuration backup. The assumption made with the interface IP: gw-world:/> set Address ... we set the values for the IP address objects for if2 which has an IP address 10.8.1.34. Checking Configuration Integrity After changing a NetDefendOS configuration and before issuing the activate and commit commands, it is to explicitly check for the NetDefend Firewall. Next,...
...RemoteMgmtHTTP HTTP_if2 Interface=if2 Network=all types of management sessions, including: • Secure Shell (SSH) CLI sessions. • Any CLI session through Ethernet interface if2 which already exist in a restored configuration backup. The assumption made with the interface IP: gw-world:/> set Address ... we set the values for the IP address objects for if2 which has an IP address 10.8.1.34. Checking Configuration Integrity After changing a NetDefendOS configuration and before issuing the activate and commit commands, it is to explicitly check for the NetDefend Firewall. Next,...
Product Manual
Page 42
... of the first variable is output. This means that has been previously uploaded to group together CLI commands which are called my_script.sgs is to a configuration object at the beginning of a script which is reserved Notice that the file becomes: add IP4Address If1_ip Address=126.12.11.01 Comments="If1 address...
... of the first variable is output. This means that has been previously uploaded to group together CLI commands which are called my_script.sgs is to a configuration object at the beginning of a script which is reserved Notice that the file becomes: add IP4Address If1_ip Address=126.12.11.01 Comments="If1 address...
Product Manual
Page 44
...2. This is to duplicate the objects. Management and Maintenance gw-world:/> script -show -name=my_script.sgs Creating Scripts Automatically When the same configuration objects needs to be downloaded with the CLI is true when the CLI node type in the script -create command. This script file can... then be copied between multiple NetDefend Firewalls, then one of a configuration which contains all the CLI commands necessary to create all units will have a script created using the -create option cannot be greater ...
...2. This is to duplicate the objects. Management and Maintenance gw-world:/> script -show -name=my_script.sgs Creating Scripts Automatically When the same configuration objects needs to be downloaded with the CLI is true when the CLI node type in the script -create command. This script file can... then be copied between multiple NetDefend Firewalls, then one of a configuration which contains all the CLI commands necessary to create all units will have a script created using the -create option cannot be greater ...