Product Manual
Page 5
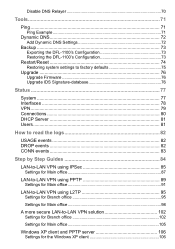
... 73 Restoring the DFL-1100's Configuration 73 Restart/Reset 74 Restoring system settings to factory defaults 75 Upgrade 76 Upgrade Firmware 76 Upgrade IDS Signature-database 76 Status 77 System 77 Interfaces 78 VPN...79 Connections 80 DHCP Server 81 Users 81 How to read the logs 82 USAGE events 82 DROP events... 83 Step by Step Guides 84 LAN-to-LAN VPN using IPSec 85 Settings for Main office 87 LAN-to-LAN VPN using PPTP 89 Settings for Main office 91 LAN-to-LAN VPN using L2TP 95 Settings for Branch office 95 Settings for Main office 98 A more secure LAN-to-LAN...
... 73 Restoring the DFL-1100's Configuration 73 Restart/Reset 74 Restoring system settings to factory defaults 75 Upgrade 76 Upgrade Firmware 76 Upgrade IDS Signature-database 76 Status 77 System 77 Interfaces 78 VPN...79 Connections 80 DHCP Server 81 Users 81 How to read the logs 82 USAGE events 82 DROP events... 83 Step by Step Guides 84 LAN-to-LAN VPN using IPSec 85 Settings for Main office 87 LAN-to-LAN VPN using PPTP 89 Settings for Main office 91 LAN-to-LAN VPN using L2TP 95 Settings for Branch office 95 Settings for Main office 98 A more secure LAN-to-LAN...
Product Manual
Page 84
... use of symbols, letters, and numbers to exchange the example information with your own values. Passwords used in these guides for real life use of example IP Addresses, users, sites and passwords. You will mean that the Firewall tab should first be selected from the menu at the top... of the screen, followed by Step Guides The following guides make use . In these examples are not recommended for example Firewall->Users will have to decrease the likelihood of a brute force dictionary attack success. Step by the...
... use of symbols, letters, and numbers to exchange the example information with your own values. Passwords used in these guides for real life use of example IP Addresses, users, sites and passwords. You will mean that the Firewall tab should first be selected from the menu at the top... of the screen, followed by Step Guides The following guides make use . In these examples are not recommended for example Firewall->Users will have to decrease the likelihood of a brute force dictionary attack success. Step by the...
Product Manual
Page 88
Setup policies for the firewall to -LAN VPN solution section of this user guide. 88 To get a more secure solution read the A more secure LAN-to restart This example will allow all VPN traffic: internal->VPN, VPN->internal and VPN->VPN Click Apply 4. Click Activate and wait for the new tunnel, Firewall->Policy: Click Global policy parameters Enable Allow all traffic between the two offices. 3.
Setup policies for the firewall to -LAN VPN solution section of this user guide. 88 To get a more secure solution read the A more secure LAN-to restart This example will allow all VPN traffic: internal->VPN, VPN->internal and VPN->VPN Click Apply 4. Click Activate and wait for the new tunnel, Firewall->Policy: Click Global policy parameters Enable Allow all traffic between the two offices. 3.