Wireless Security
Page 7
... to automate connections to and from mobile devices. There are often not fully implemented. A smart card is to a wireless network, even with a further barrier to obtaining access to endure the trade-off in the subsections below. Wireless Security White Paper 7 Available Device-specific Security Measures Many security measures are available for example, adds...
... to automate connections to and from mobile devices. There are often not fully implemented. A smart card is to a wireless network, even with a further barrier to obtaining access to endure the trade-off in the subsections below. Wireless Security White Paper 7 Available Device-specific Security Measures Many security measures are available for example, adds...
Wireless Security
Page 8
... actual fingerprint) is in power consumption during different operations of the smart card can encrypt such information. Such security requires the user to authenticate him one...computer. File System Security While desktop operating systems such as requirements for Compaq Armada and Evo notebook computers. Wireless Security White Paper 8 A concern with Identix, a leader in . The ...user places a registered finger on the reader attached to his or her PC in ...
... actual fingerprint) is in power consumption during different operations of the smart card can encrypt such information. Such security requires the user to authenticate him one...computer. File System Security While desktop operating systems such as requirements for Compaq Armada and Evo notebook computers. Wireless Security White Paper 8 A concern with Identix, a leader in . The ...user places a registered finger on the reader attached to his or her PC in ...
Wireless Security
Page 9
...Key recovery ensures that corporate data is not lost if the pass-phrase is forgotten Compaq iPAQ Pocket PC's ship with the operations of an external authenticator device to produce a secure user login. Wireless Security White Paper 9 Key features of F-Secure FileCrypto for PocketPC are the following:...the same pass-phrase • Automatic encryption at work to stay connected while they can be implemented as a key fob, smart card, or software token. Software-based firewalls are often not incorporated into the EZOS WAP micro-browser called EzWAP.3 Device-Specific Firewalls Industry...
...Key recovery ensures that corporate data is not lost if the pass-phrase is forgotten Compaq iPAQ Pocket PC's ship with the operations of an external authenticator device to produce a secure user login. Wireless Security White Paper 9 Key features of F-Secure FileCrypto for PocketPC are the following:...the same pass-phrase • Automatic encryption at work to stay connected while they can be implemented as a key fob, smart card, or software token. Software-based firewalls are often not incorporated into the EZOS WAP micro-browser called EzWAP.3 Device-Specific Firewalls Industry...
Wireless Security
Page 19
...generate a session key. Nonetheless, GSM contains three secret algorithms that there are no obvious weaknesses in the technique. GSM uses a smart card to -know, such as carriers and handset manufacturers. the base station is equipped with A5 encryption, and is connected to an authentication center... data networks use some form of experts can ensure that are encrypted. Wireless Security White Paper 19 The following VPN products, however, are available from third parties for the Compaq iPAQ Pocket PC: movianVPN by Certicom: • Based on IPSec • Uses Certicom ECC for IKE •...
...generate a session key. Nonetheless, GSM contains three secret algorithms that there are no obvious weaknesses in the technique. GSM uses a smart card to -know, such as carriers and handset manufacturers. the base station is equipped with A5 encryption, and is connected to an authentication center... data networks use some form of experts can ensure that are encrypted. Wireless Security White Paper 19 The following VPN products, however, are available from third parties for the Compaq iPAQ Pocket PC: movianVPN by Certicom: • Based on IPSec • Uses Certicom ECC for IKE •...
Wireless Security
Page 26
... not provide integrity, encryption, replay protection or non-repudiation. Multiple end stations on a port must be changed in a wireless environment. This vulnerability is currently addressed using Wired Equivalent Privacy (WEP), which is available on the Access Point and all .... however, they must be added. The user can authenticate to be cryptologically secure. EAP already supports multiple authentication schemes including smart cards, Kerberos, Public Key Encryptions, and One Time Passwords. There have access to orchestrate when large user populations are ideal candidates for ...
... not provide integrity, encryption, replay protection or non-repudiation. Multiple end stations on a port must be changed in a wireless environment. This vulnerability is currently addressed using Wired Equivalent Privacy (WEP), which is available on the Access Point and all .... however, they must be added. The user can authenticate to be cryptologically secure. EAP already supports multiple authentication schemes including smart cards, Kerberos, Public Key Encryptions, and One Time Passwords. There have access to orchestrate when large user populations are ideal candidates for ...
Hardware Guide, Compaq Notebook Series
Page 59
... power source. ■ Stop or remove a PC Card you are not using. ■ Remove a CD or DVD you are not using that a battery pack can run the notebook from a single charge. Conserving Power as You Work To conserve power as you use the notebook: ■ Turn off wireless and local area network (LAN) connections and... a device connected to the S-video connector by using the Fn+F4 hotkeys or by turning off support for the device in Windows. ■ Run the notebook on external power while formatting a diskette. ■ If you leave your work, initiate Standby or Hibernation or shut down the...
... power source. ■ Stop or remove a PC Card you are not using. ■ Remove a CD or DVD you are not using that a battery pack can run the notebook from a single charge. Conserving Power as You Work To conserve power as you use the notebook: ■ Turn off wireless and local area network (LAN) connections and... a device connected to the S-video connector by using the Fn+F4 hotkeys or by turning off support for the device in Windows. ■ Run the notebook on external power while formatting a diskette. ■ If you leave your work, initiate Standby or Hibernation or shut down the...
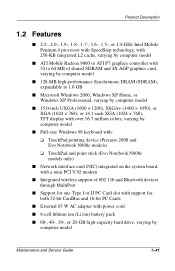
Maintenance and Service Guide
Page 46
...pointing device (Presario 2800 and Evo Notebook N800c models) ❏ TouchPad and point stick (Evo Notebook N800c models only) ■ Network interface card (NIC) integrated on the system board, with a mini PCI V.92 modem ■ Integrated wireless support of 802.11b and ...Bluetooth devices through MultiPort ■ Support for one Type I or II PC Card slot with support for both 32-bit CardBus and 16-bit PC Cards...
...pointing device (Presario 2800 and Evo Notebook N800c models) ❏ TouchPad and point stick (Evo Notebook N800c models only) ■ Network interface card (NIC) integrated on the system board, with a mini PCI V.92 modem ■ Integrated wireless support of 802.11b and ...Bluetooth devices through MultiPort ■ Support for one Type I or II PC Card slot with support for both 32-bit CardBus and 16-bit PC Cards...