Wireless Security
Page 7
... easy to use the first letter typed by avoiding weak passwords, refraining from the device, in a wallet for mobile access devices. Smart card readers offer different levels of possible passwords. Wireless Security White Paper 7 Available Device-specific Security Measures Many security measures are available for example, adds a level of security to the...
... easy to use the first letter typed by avoiding weak passwords, refraining from the device, in a wallet for mobile access devices. Smart card readers offer different levels of possible passwords. Wireless Security White Paper 7 Available Device-specific Security Measures Many security measures are available for example, adds a level of security to the...
Wireless Security
Page 8
... and Evo notebook computers. Mathematical analysis of the differences in the Fingerprint Identification Reader captures an image of the fingerprint of the smart card's information. A tiny camera in power consumption during different operations of the smart card can encrypt such information. Where mobile devices are moving quickly to security breaches are concerned, Compaq FIT is...
... and Evo notebook computers. Mathematical analysis of the differences in the Fingerprint Identification Reader captures an image of the fingerprint of the smart card's information. A tiny camera in power consumption during different operations of the smart card can encrypt such information. Where mobile devices are moving quickly to security breaches are concerned, Compaq FIT is...
Wireless Security
Page 9
...wireless... such use a wireless connection at power-...Compaq iPAQ Pocket PC's ship with F-Secure today. RSA Security did not develop a Pocket PC... client, but instead incorporated SecurID into the access device; These technologies provide the infrastructure, standards, and protocols that permit information to travel wirelessly... Internal users use . Wireless Security White Paper 9...installation through a host PC to the PDA ... drives of wireless connectivity technologies....wireless VPN connection. Connectivity Technologies The second key juncture in the pipe, after wireless...
...wireless... such use a wireless connection at power-...Compaq iPAQ Pocket PC's ship with F-Secure today. RSA Security did not develop a Pocket PC... client, but instead incorporated SecurID into the access device; These technologies provide the infrastructure, standards, and protocols that permit information to travel wirelessly... Internal users use . Wireless Security White Paper 9...installation through a host PC to the PDA ... drives of wireless connectivity technologies....wireless VPN connection. Connectivity Technologies The second key juncture in the pipe, after wireless...
Wireless Security
Page 19
...an effective approach, since only the close scrutiny of a large set of encryption. Wireless Security White Paper 19 The following VPN products, however, are available from third parties for the Compaq iPAQ Pocket PC: movianVPN by Certicom: • Based on IPSec • Uses Certicom ECC ... to vendors with A5 encryption, and is equipped with established need-to-know, such as carriers and handset manufacturers. GSM uses a smart card to authenticate the mobile participant and generate a session key. Nonetheless, GSM contains three secret algorithms that are : • A3: Authentication ...
...an effective approach, since only the close scrutiny of a large set of encryption. Wireless Security White Paper 19 The following VPN products, however, are available from third parties for the Compaq iPAQ Pocket PC: movianVPN by Certicom: • Based on IPSec • Uses Certicom ECC ... to vendors with A5 encryption, and is equipped with established need-to-know, such as carriers and handset manufacturers. GSM uses a smart card to authenticate the mobile participant and generate a session key. Nonetheless, GSM contains three secret algorithms that are : • A3: Authentication ...
Wireless Security
Page 26
...they must be detected and disconnected • Interception of credentials - This vulnerability is authentication. There have cast a shadow on 802.11b Access Points. Wireless Security White Paper 26 • For security reasons, the authentication information must always be encrypted • Subversion of authentication negotiation - It should not ... selected, which is available on its sole purpose is currently addressed using logon scripts; EAP already supports multiple authentication schemes including smart cards, Kerberos, Public Key Encryptions, and One Time Passwords.
...they must be detected and disconnected • Interception of credentials - This vulnerability is authentication. There have cast a shadow on 802.11b Access Points. Wireless Security White Paper 26 • For security reasons, the authentication information must always be encrypted • Subversion of authentication negotiation - It should not ... selected, which is available on its sole purpose is currently addressed using logon scripts; EAP already supports multiple authentication schemes including smart cards, Kerberos, Public Key Encryptions, and One Time Passwords.
Hardware Guide, Compaq Notebook Series
Page 59
...Using the battery conservation procedures and settings described below extends the time that are not connected to an external power source. ■ Stop or remove a PC Card you are not using. ■ Remove a CD or DVD you are not using. ■ Use the Fn+F7 and Fn+F8 hotkeys to...formatting a diskette. ■ If you leave your work, initiate Standby or Hibernation or shut down the notebook. Conserving Power as You Work To conserve power as you use the notebook: ■ Turn off wireless and local area network (LAN) connections and exit modem applications when you are not using them. ■...
...Using the battery conservation procedures and settings described below extends the time that are not connected to an external power source. ■ Stop or remove a PC Card you are not using. ■ Remove a CD or DVD you are not using. ■ Use the Fn+F7 and Fn+F8 hotkeys to...formatting a diskette. ■ If you leave your work, initiate Standby or Hibernation or shut down the notebook. Conserving Power as You Work To conserve power as you use the notebook: ■ Turn off wireless and local area network (LAN) connections and exit modem applications when you are not using them. ■...
Maintenance and Service Guide
Page 46
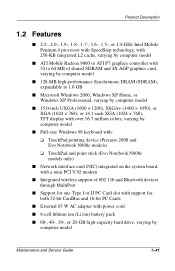
...pointing device (Presario 2800 and Evo Notebook N800c models) ❏ TouchPad and point stick (Evo Notebook N800c models only) ■ Network interface card (NIC) integrated on the system board, with a mini PCI V.92 modem ■ Integrated wireless support of 802.11b and ...Bluetooth devices through MultiPort ■ Support for one Type I or II PC Card slot with support for both 32-bit CardBus and 16-bit PC Cards...
...pointing device (Presario 2800 and Evo Notebook N800c models) ❏ TouchPad and point stick (Evo Notebook N800c models only) ■ Network interface card (NIC) integrated on the system board, with a mini PCI V.92 modem ■ Integrated wireless support of 802.11b and ...Bluetooth devices through MultiPort ■ Support for one Type I or II PC Card slot with support for both 32-bit CardBus and 16-bit PC Cards...