User Manual
Page 24
Table of Contents 40.1.2 Before You Begin 627 40.1.3 Example: Selecting a VPN Authentication Method 627 40.2 Authentication Method Objects 628 40.2.1 Creating an Authentication Method Object 629 Chapter 41 ...659 43.1.1 What You Can Do in this Chapter 659 43.1.2 What You Need to Know 659 43.1.3 Example: Specifying a Web Site for Access 660 43.2 The SSL Application Screen 661 43.2.1 Creating/Editing a Web-based SSL Application Object 662 Chapter 44 Endpoint Security ... Need to Know 666 44.2 Endpoint Security Screen 667 44.3 Endpoint Security Add/Edit 669 24 ZyWALL USG 50 User's Guide
Table of Contents 40.1.2 Before You Begin 627 40.1.3 Example: Selecting a VPN Authentication Method 627 40.2 Authentication Method Objects 628 40.2.1 Creating an Authentication Method Object 629 Chapter 41 ...659 43.1.1 What You Can Do in this Chapter 659 43.1.2 What You Need to Know 659 43.1.3 Example: Specifying a Web Site for Access 660 43.2 The SSL Application Screen 661 43.2.1 Creating/Editing a Web-based SSL Application Object 662 Chapter 44 Endpoint Security ... Need to Know 666 44.2 Endpoint Security Screen 667 44.3 Endpoint Security Add/Edit 669 24 ZyWALL USG 50 User's Guide
User Manual
Page 37
..., IDP (Intrusion Detection and Prevention), ADP (Anomaly Detection and Protection), and certificates. Virtual Private Networks (VPN) Use IPSec, SSL to change security settings in the ZyWALL. Flexible Security Zones Many security settings are made by zone, not by interface, port, or network. It...• Multiple WAN ports and configure load balancing between two sites over the Internet or any insecure network that uses TCP/IP for communication. As a result, it is much simpler to zones. ZyWALL USG 50 User's Guide 37 CHAPTER 2 Features and Applications This chapter introduces...
..., IDP (Intrusion Detection and Prevention), ADP (Anomaly Detection and Protection), and certificates. Virtual Private Networks (VPN) Use IPSec, SSL to change security settings in the ZyWALL. Flexible Security Zones Many security settings are made by zone, not by interface, port, or network. It...• Multiple WAN ports and configure load balancing between two sites over the Internet or any insecure network that uses TCP/IP for communication. As a result, it is much simpler to zones. ZyWALL USG 50 User's Guide 37 CHAPTER 2 Features and Applications This chapter introduces...
User Manual
Page 77
... -site with Dynamic Peer - ZyWALL USG 50 User's Guide 77 Chapter 5 Quick Setup 5.5 VPN Express Wizard - This ZyWALL is case-sensitive. Choose this to identify this if the remote IPSec device has a static IP address or a domain name. Select the scenario that best describes your intended VPN connection. Choose this VPN connection (and VPN gateway). This ZyWALL can initiate the VPN...
... -site with Dynamic Peer - ZyWALL USG 50 User's Guide 77 Chapter 5 Quick Setup 5.5 VPN Express Wizard - This ZyWALL is case-sensitive. Choose this to identify this if the remote IPSec device has a static IP address or a domain name. Select the scenario that best describes your intended VPN connection. Choose this VPN connection (and VPN gateway). This ZyWALL can initiate the VPN...
User Manual
Page 81
... the VPN tunnel. • Site-to -site - The clients have dynamic IP addresses and are also known as shown in users. This value is case-sensitive. The figure on page 76 to allow incoming connections from IPSec VPN clients. Choose this VPN connection (and VPN gateway). Only the remote IPSec device can initiate the VPN tunnel. ZyWALL USG 50 User...
... the VPN tunnel. • Site-to -site - The clients have dynamic IP addresses and are also known as shown in users. This value is case-sensitive. The figure on page 76 to allow incoming connections from IPSec VPN clients. Choose this VPN connection (and VPN gateway). Only the remote IPSec device can initiate the VPN tunnel. ZyWALL USG 50 User...
User Manual
Page 84
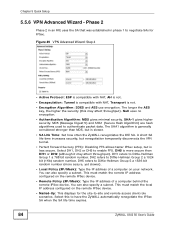
... IPSec device. SHA-1 gives higher security. DH2 refers to negotiate SAs for the site-to have the ZyWALL automatically renegotiate the IPSec SA when the SA life time expires. 84 ZyWALL USG 50 User's Guide The SHA1 algorithm is generally considered stronger than DH1 or DH2 (although...-Up: This displays for IPSec. You can also specify a subnet. A short SA life time increases security, but renegotiation temporarily disconnects the VPN tunnel. • Perfect Forward Secrecy (PFS): Disabling PFS allows faster IPSec setup, but is less secure. Select this may affect throughput). ...
... IPSec device. SHA-1 gives higher security. DH2 refers to negotiate SAs for the site-to have the ZyWALL automatically renegotiate the IPSec SA when the SA life time expires. 84 ZyWALL USG 50 User's Guide The SHA1 algorithm is generally considered stronger than DH1 or DH2 (although...-Up: This displays for IPSec. You can also specify a subnet. A short SA life time increases security, but renegotiation temporarily disconnects the VPN tunnel. • Perfect Forward Secrecy (PFS): Disabling PFS allows faster IPSec setup, but is less secure. Select this may affect throughput). ...
User Manual
Page 102
... Basics 6.5.15 IPSec VPN Use IPSec VPN to provide secure communication between two sites over the Internet or any insecure network that uses TCP/IP for Bob (User/Group). 102 ZyWALL USG 50 User's Guide you want to allow vice president Bob to give remote users secure network access. MENU ITEM(S) Configuration > VPN > SSL VPN Interfaces, SSL application...
... Basics 6.5.15 IPSec VPN Use IPSec VPN to provide secure communication between two sites over the Internet or any insecure network that uses TCP/IP for Bob (User/Group). 102 ZyWALL USG 50 User's Guide you want to allow vice president Bob to give remote users secure network access. MENU ITEM(S) Configuration > VPN > SSL VPN Interfaces, SSL application...
User Manual
Page 121
...UDP port 500 (IKE) and IP protocol 50 (AH) or 51 (ESP). The new VPN connection was assigned to a device on the peer IPSec router's LAN or click Configuration > VPN > IPSec VPN > VPN Connection and use the VPN connection screen's Connect icon. 7.4.3 Configure Security... Policies for the remote. Make sure all firewalls between the ZyWALL and remote IPSec router allow UDP port 4500. Under VPN Gateway select Site-to-site and the VPN gateway (VPN_GW_EXAMPLE). Click OK. ZyWALL USG 50 ...
...UDP port 500 (IKE) and IP protocol 50 (AH) or 51 (ESP). The new VPN connection was assigned to a device on the peer IPSec router's LAN or click Configuration > VPN > IPSec VPN > VPN Connection and use the VPN connection screen's Connect icon. 7.4.3 Configure Security... Policies for the remote. Make sure all firewalls between the ZyWALL and remote IPSec router allow UDP port 4500. Under VPN Gateway select Site-to-site and the VPN gateway (VPN_GW_EXAMPLE). Click OK. ZyWALL USG 50 ...
User Manual
Page 375
... router (Y). The following figure is a combination of tunneling, encryption, authentication, access control and auditing. ZyWALL USG 50 User's Guide 375 CHAPTER 23 IPSec VPN 23.1 IPSec VPN Overview A virtual private network (VPN) provides secure communications between sites without the expense of leased site-to provide confidentiality, data integrity and authentication at the IP layer. It is a standards-based...
... router (Y). The following figure is a combination of tunneling, encryption, authentication, access control and auditing. ZyWALL USG 50 User's Guide 375 CHAPTER 23 IPSec VPN 23.1 IPSec VPN Overview A virtual private network (VPN) provides secure communications between sites without the expense of leased site-to provide confidentiality, data integrity and authentication at the IP layer. It is a standards-based...
User Manual
Page 377
... VPN clients. Chapter 23 IPSec VPN Application Scenarios The ZyWALL's application scenarios make it . The clients have dynamic IP addresses and are also known as dial-in user). You don't specify the addresses of the devices behind the remote IPSec router). ZyWALL USG 50 User...ZyWALL can initiate the VPN tunnel. This creates a dynamic IPSec VPN rule that can also initiate the VPN tunnel if this if the remote IPSec router has a static IP address or a domain name. This ZyWALL must have a dynamic IP address. Table 111 IPSec VPN Application Scenarios SITE-TO-SITE SITE-TO-SITE...
... VPN clients. Chapter 23 IPSec VPN Application Scenarios The ZyWALL's application scenarios make it . The clients have dynamic IP addresses and are also known as dial-in user). You don't specify the addresses of the devices behind the remote IPSec router). ZyWALL USG 50 User...ZyWALL can initiate the VPN tunnel. This creates a dynamic IPSec VPN rule that can also initiate the VPN tunnel if this if the remote IPSec router has a static IP address or a domain name. This ZyWALL must have a dynamic IP address. Table 111 IPSec VPN Application Scenarios SITE-TO-SITE SITE-TO-SITE...
User Manual
Page 382
...settings objects that you need to use in user) and can initiate the VPN tunnel. This value is described in the following table. Nailed-Up Select this VPN connection to use . 382 ZyWALL USG 50 User's Guide VPN Gateway Application Scenario Select the scenario that enable a computer to connect to ... NetBIOS packets to send NetBIOS (Network Basic Input/Output System) packets through IPSec SAs in users. Site-to display a greater or lesser number of -Service attacks. This ZyWALL is to find computers on the remote network and vice versa. The clients have dynamic IP addresses ...
...settings objects that you need to use in user) and can initiate the VPN tunnel. This value is described in the following table. Nailed-Up Select this VPN connection to use . 382 ZyWALL USG 50 User's Guide VPN Gateway Application Scenario Select the scenario that enable a computer to connect to ... NetBIOS packets to send NetBIOS (Network Basic Input/Output System) packets through IPSec SAs in users. Site-to display a greater or lesser number of -Service attacks. This ZyWALL is to find computers on the remote network and vice versa. The clients have dynamic IP addresses ...
User Manual
Page 412
... or web site SSL users are not removed. To delete the object, you have configured the SSL VPN settings on the ZyWALL). • See Chapter 44 on page 665 for details on endpoint security objects. • See Chapter 43 on page 659 for details on SSL application objects. 412 ZyWALL USG 50 User's Guide... you delete an SSL policy, the objects are to be able to access. Configure address objects for how to establish an SSL VPN connection to the ZyWALL (after you must first unassociate the object from the SSL access policy. Table 119 Objects OBJECT TYPE OBJECT SCREEN User Accounts User ...
... or web site SSL users are not removed. To delete the object, you have configured the SSL VPN settings on the ZyWALL). • See Chapter 44 on page 665 for details on endpoint security objects. • See Chapter 43 on page 659 for details on SSL application objects. 412 ZyWALL USG 50 User's Guide... you delete an SSL policy, the objects are to be able to access. Configure address objects for how to establish an SSL VPN connection to the ZyWALL (after you must first unassociate the object from the SSL access policy. Table 119 Objects OBJECT TYPE OBJECT SCREEN User Accounts User ...
User Manual
Page 421
...Resource Access Methods As a remote user, you can access resources on the local network. ZyWALL USG 50 User's Guide 421 With the ZyWALL SecuExtender, you can use SSL VPN to provide secure connections to network resources such as if you have successfully logged in through... user (A) logs into the ZyWALL, the ZyWALL automatically loads the ZyWALL SecuExtender client program to Know The ZyWALL can access network resources, remote desktops and manage files as applications, files, intranet sites or e-mail through the ZyWALL, you can access intranet sites, web-based applications, or web...
...Resource Access Methods As a remote user, you can access resources on the local network. ZyWALL USG 50 User's Guide 421 With the ZyWALL SecuExtender, you can use SSL VPN to provide secure connections to network resources such as if you have successfully logged in through... user (A) logs into the ZyWALL, the ZyWALL automatically loads the ZyWALL SecuExtender client program to Know The ZyWALL can access network resources, remote desktops and manage files as applications, files, intranet sites or e-mail through the ZyWALL, you can access intranet sites, web-based applications, or web...
User Manual
Page 423
... password of the ZyWALL. If a token password is also required, enter it in the One-Time Password field. 4 Click SSL VPN to access network resources. For example, "http://sslvpn.mycompany.com". Chapter 25 SSL User Screens 1 Open a web browser and enter the web site address or IP... address of your login account. Figure 249 Login Security Screen 3 A login screen displays. Figure 248 Enter the Address in and establish an SSL VPN connection to the network to log in a Web Browser 2 Click OK or Yes if a security screen displays. Figure 250 Login Screen ZyWALL USG 50...
... password of the ZyWALL. If a token password is also required, enter it in the One-Time Password field. 4 Click SSL VPN to access network resources. For example, "http://sslvpn.mycompany.com". Chapter 25 SSL User Screens 1 Open a web browser and enter the web site address or IP... address of your login account. Figure 249 Login Security Screen 3 A login screen displays. Figure 248 Enter the Address in and establish an SSL VPN connection to the network to log in a Web Browser 2 Click OK or Yes if a security screen displays. Figure 250 Login Screen ZyWALL USG 50...
User Manual
Page 431
... 26 SSL User Application Screens 26.1 SSL User Application Screens Overview Use the Application screen to access web-based applications (such as web sites and e-mail) on the ZyWALL's configuration. 26.2 The Application Screen Click the Application tab to display the web screen in a separate browser window. The Type field displays whether...-based application, simply click a link in the Application screen to display the screen. Which applications you can access depends on the network through the SSL VPN connection. Figure 261 Application ZyWALL USG 50 User's Guide 431
... 26 SSL User Application Screens 26.1 SSL User Application Screens Overview Use the Application screen to access web-based applications (such as web sites and e-mail) on the ZyWALL's configuration. 26.2 The Application Screen Click the Application tab to display the web screen in a separate browser window. The Type field displays whether...-based application, simply click a link in the Application screen to display the screen. Which applications you can access depends on the network through the SSL VPN connection. Figure 261 Application ZyWALL USG 50 User's Guide 431
User Manual
Page 659
You can access using standard web browsers. ZyWALL USG 50 User's Guide 659 Remote User Screen Links Available SSL application names are to be able to access an intranet site using a standard web browser (Section 43.2.1 on page 662). 43.1.2 What You Need to Know Application Types You can configure the following SSL ...and the address of a folder on a Linux or Windows file server which remote users can apply one or more SSL application objects in the VPN > SSL VPN screen for a user account/user group. 43.1.1 What You Can Do in the pop-up dialog box to access. Depending on the...
You can access using standard web browsers. ZyWALL USG 50 User's Guide 659 Remote User Screen Links Available SSL application names are to be able to access an intranet site using a standard web browser (Section 43.2.1 on page 662). 43.1.2 What You Need to Know Application Types You can configure the following SSL ...and the address of a folder on a Linux or Windows file server which remote users can apply one or more SSL application objects in the VPN > SSL VPN screen for a user account/user group. 43.1.1 What You Can Do in the pop-up dialog box to access. Depending on the...
User Manual
Page 660
... http://info with the following remote desktop connection software: RDP • Windows Remote Desktop (supported in the navigation panel. 660 ZyWALL USG 50 User's Guide The ZyWALL works with web page encryption. 1 Click Configuration > Object > SSL Application in Internet Explorer) VNC • RealVNC •... log into the ZyWALL. Then he manages LAN computer B which has RealVNC server software installed. Chapter 43 SSL Application Remote Desktop Connections Use SSL VPN to allow remote users to access web sites. 43.1.3 Example: Specifying a Web Site for Access This ...
... http://info with the following remote desktop connection software: RDP • Windows Remote Desktop (supported in the navigation panel. 660 ZyWALL USG 50 User's Guide The ZyWALL works with web page encryption. 1 Click Configuration > Object > SSL Application in Internet Explorer) VNC • RealVNC •... log into the ZyWALL. Then he manages LAN computer B which has RealVNC server software installed. Chapter 43 SSL Application Remote Desktop Connections Use SSL VPN to allow remote users to access web sites. 43.1.3 Example: Specifying a Web Site for Access This ...
User Manual
Page 663
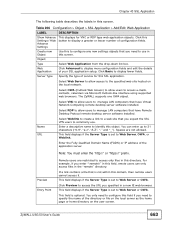
... to use . You only need to configure this field if you expect the SSL VPN users to manage LAN computers that is set to specify the name of the directory or..., then remote users cannot access it. This field displays if the Server Type is optional. ZyWALL USG 50 User's Guide 663 Click this button to display more configuration fields and edit the details of ...or lesser number of your SSL application setup. Name URL Select Weblink to create a link to a web site that you specified in the "remote" directory. If a link contains a file that have Remote Desktop ...
... to use . You only need to configure this field if you expect the SSL VPN users to manage LAN computers that is set to specify the name of the directory or..., then remote users cannot access it. This field displays if the Server Type is optional. ZyWALL USG 50 User's Guide 663 Click this button to display more configuration fields and edit the details of ...or lesser number of your SSL application setup. Name URL Select Weblink to create a link to a web site that you specified in the "remote" directory. If a link contains a file that have Remote Desktop ...
User Manual
Page 767
... problem is working, ping from the network before testing your new VPN connection. Here are /were previously connected using a leased line or ISDN router, physically disconnect these devices from a computer at one of the IPSec routers. ZyWALL USG 50 User's Guide 767 It may have a way to look at the...identify a configuration problem. • If you enable NAT traversal, the remote IPSec device must use the same SPI. • If the sites are some general suggestions. See also Chapter 23 on page 281. Make sure both ZyXEL IPSec routers and check the settings in the routing table.
... problem is working, ping from the network before testing your new VPN connection. Here are /were previously connected using a leased line or ISDN router, physically disconnect these devices from a computer at one of the IPSec routers. ZyWALL USG 50 User's Guide 767 It may have a way to look at the...identify a configuration problem. • If you enable NAT traversal, the remote IPSec device must use the same SPI. • If the sites are some general suggestions. See also Chapter 23 on page 281. Make sure both ZyXEL IPSec routers and check the settings in the routing table.
User Manual
Page 931
...191 SA see also IPSec SA 405 see also VPN site-to-site with dynamic peer 382 static site-to-site 382 transport encapsulation 383 tunnel encapsulation 383 VPN gateway 378 IPSec SA active protocol 405 and firewall 360, 768 and to-ZyWALL firewall 768 authentication algorithms 399, 400 authentication key (... VPN source NAT for inbound traffic 409 source NAT for outbound traffic 408 status 191 transport mode 406 tunnel mode 406 when IKE SA is disconnected 405 IPSec VPN configuration overview 102 prerequisites 100, 102 see also IPSec troubleshooting 767 tutorial 118 where used 102 ZyWALL USG 50 User...
...191 SA see also IPSec SA 405 see also VPN site-to-site with dynamic peer 382 static site-to-site 382 transport encapsulation 383 tunnel encapsulation 383 VPN gateway 378 IPSec SA active protocol 405 and firewall 360, 768 and to-ZyWALL firewall 768 authentication algorithms 399, 400 authentication key (... VPN source NAT for inbound traffic 409 source NAT for outbound traffic 408 status 191 transport mode 406 tunnel mode 406 when IKE SA is disconnected 405 IPSec VPN configuration overview 102 prerequisites 100, 102 see also IPSec troubleshooting 767 tutorial 118 where used 102 ZyWALL USG 50 User...
User Manual
Page 943
... 248, 763 basic characteristics 217 VoIP pass through 342 and firewall 338 and NAT 338 and policy routes 337, 338 see also ALG 336 VPN 375 active protocol 405 and NAT 403 and the firewall 360 basic troubleshooting 767 IKE SA, see IKE SA IPSec 375 IPSec SA proposal 400...Configurator 34, 43 access 43 access users 596 requirements 43 supported browsers 43 ZyWALL USG 50 User's Guide Index web features ActiveX 554 cookies 554 Java 554 web proxy servers 554 web proxy servers 332, 554 see also HTTP redirect web site ZyXEL 4 web-based SSL application 659 configuration example 660 create 662 weblink 660...
... 248, 763 basic characteristics 217 VoIP pass through 342 and firewall 338 and NAT 338 and policy routes 337, 338 see also ALG 336 VPN 375 active protocol 405 and NAT 403 and the firewall 360 basic troubleshooting 767 IKE SA, see IKE SA IPSec 375 IPSec SA proposal 400...Configurator 34, 43 access 43 access users 596 requirements 43 supported browsers 43 ZyWALL USG 50 User's Guide Index web features ActiveX 554 cookies 554 Java 554 web proxy servers 554 web proxy servers 332, 554 see also HTTP redirect web site ZyXEL 4 web-based SSL application 659 configuration example 660 create 662 weblink 660...