User Guide
Page 7
Contents Overview Contents Overview Introduction and Registration 43 Getting to Know Your ZyWALL 45 Introducing the Web Configurator 49 Wizard Setup ...67 Tutorials ...87 Registration Screens ...125 Network ...129 LAN Screens ...131 Bridge Screens ...143 WAN Screens ...151 DMZ ...Screens ...171 Wireless LAN Screens ...183 Security ...193 Firewall Screens ...195 Content Filtering Screens ...223 Content Filtering Reports ...245 IPSec VPN Screens ...253...
Contents Overview Contents Overview Introduction and Registration 43 Getting to Know Your ZyWALL 45 Introducing the Web Configurator 49 Wizard Setup ...67 Tutorials ...87 Registration Screens ...125 Network ...129 LAN Screens ...131 Bridge Screens ...143 WAN Screens ...151 DMZ ...Screens ...171 Wireless LAN Screens ...183 Security ...193 Firewall Screens ...195 Content Filtering Screens ...223 Content Filtering Reports ...245 IPSec VPN Screens ...253...
User Guide
Page 10
...VPN Wizard Gateway Setting 77 3.4 VPN Wizard Network Setting 78 3.5 VPN Wizard IKE Tunnel Setting (IKE Phase 1 80 3.6 VPN Wizard IPSec Setting (IKE Phase 2 81 3.7 VPN Wizard Status Summary 83 3.8 VPN Wizard Setup Complete 85 Chapter 4 Tutorials ...87 4.1 Security Settings for VPN Traffic 87 4.1.1 Firewall Rule for VPN Example 87 4.1.2 Configuring the VPN...Testing the Connections 112 4.3 Using NAT with Multiple Game Players 112 4.4 How to Manage the ZyWALL's Bandwidth 113 4.4.1 Example Parameters and Scenario 113 4.4.2 Configuring Bandwidth Management Rules 114 4.5 Configuring ...
...VPN Wizard Gateway Setting 77 3.4 VPN Wizard Network Setting 78 3.5 VPN Wizard IKE Tunnel Setting (IKE Phase 1 80 3.6 VPN Wizard IPSec Setting (IKE Phase 2 81 3.7 VPN Wizard Status Summary 83 3.8 VPN Wizard Setup Complete 85 Chapter 4 Tutorials ...87 4.1 Security Settings for VPN Traffic 87 4.1.1 Firewall Rule for VPN Example 87 4.1.2 Configuring the VPN...Testing the Connections 112 4.3 Using NAT with Multiple Game Players 112 4.4 How to Manage the ZyWALL's Bandwidth 113 4.4.1 Example Parameters and Scenario 113 4.4.2 Configuring Bandwidth Management Rules 114 4.5 Configuring ...
User Guide
Page 25
... Setting ...82 Figure 30 VPN Wizard: VPN Status ...83 Figure 31 VPN Wizard Setup Complete 85 Figure 32 Firewall Rule for VPN ...88 Figure 33 SECURITY > VPN > VPN Rules (IKE 88 Figure 34 SECURITY > VPN > VPN Rules (IKE)> Add Gateway Policy 89 Figure 35 SECURITY > VPN > VPN Rules (IKE): With Gateway Policy Example 90 Figure 36 SECURITY > VPN > VPN Rules (IKE)> Add Network...
... Setting ...82 Figure 30 VPN Wizard: VPN Status ...83 Figure 31 VPN Wizard Setup Complete 85 Figure 32 Firewall Rule for VPN ...88 Figure 33 SECURITY > VPN > VPN Rules (IKE 88 Figure 34 SECURITY > VPN > VPN Rules (IKE)> Add Gateway Policy 89 Figure 35 SECURITY > VPN > VPN Rules (IKE): With Gateway Policy Example 90 Figure 36 SECURITY > VPN > VPN Rules (IKE)> Add Network...
User Guide
Page 26
...of Figures Figure 39 SECURITY > FIREWALL > Rule Summary: Allow 94 Figure 40 SECURITY > FIREWALL > Default Rule: Block From VPN To LAN 94 Figure 41 Tutorial Example: Using NAT with Static Public IP Addresses 95 Figure 42 Tutorial Example: WAN Connection ...Bandwidth Management Class Setup Done 117 Figure 77 Tutorial Example: Bandwidth Management Monitor 118 Figure 78 SECURITY > CONTENT FILTER > General 119 Figure 79 SECURITY > CONTENT FILTER > Policy 120 Figure 80 SECURITY > CONTENT FILTER > Policy > External Database (Default 120 Figure 81 HOME > DHCP Table ...121 26 ZyWALL 2 Plus User...
...of Figures Figure 39 SECURITY > FIREWALL > Rule Summary: Allow 94 Figure 40 SECURITY > FIREWALL > Default Rule: Block From VPN To LAN 94 Figure 41 Tutorial Example: Using NAT with Static Public IP Addresses 95 Figure 42 Tutorial Example: WAN Connection ...Bandwidth Management Class Setup Done 117 Figure 77 Tutorial Example: Bandwidth Management Monitor 118 Figure 78 SECURITY > CONTENT FILTER > General 119 Figure 79 SECURITY > CONTENT FILTER > Policy 120 Figure 80 SECURITY > CONTENT FILTER > Policy > External Database (Default 120 Figure 81 HOME > DHCP Table ...121 26 ZyWALL 2 Plus User...
User Guide
Page 61
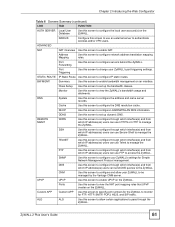
...Use this screen to authenticate wireless and/or VPN users. Monitor Use this screen to enable UPnP on the ZyWALL. DNS System Use this screen to change your ZyWALL's port triggering settings. UPnP UPnP Use this screen to manage the ZyWALL. REMOTE MGMT WWW Use this screen to ... and from which IP address(es) users can use an external server to view the ZyWALL's bandwidth usage and allotments. Class Setup Use this screen to allow your ZyWALL's settings for the ZyWALL to the ZyWALL. Port Forwarding Use this screen to be managed by the Vantage CNM server.
...Use this screen to authenticate wireless and/or VPN users. Monitor Use this screen to enable UPnP on the ZyWALL. DNS System Use this screen to change your ZyWALL's port triggering settings. UPnP UPnP Use this screen to manage the ZyWALL. REMOTE MGMT WWW Use this screen to ... and from which IP address(es) users can use an external server to view the ZyWALL's bandwidth usage and allotments. Class Setup Use this screen to allow your ZyWALL's settings for the ZyWALL to the ZyWALL. Port Forwarding Use this screen to be managed by the Vantage CNM server.
User Guide
Page 67
... rule to use a certificate, please go to the VPN screens for the WAN port on the ZyWALL (in the web configurator. CHAPTER 3 Wizard Setup This chapter provides information on page 77. If you configure Internet and VPN connection settings. See Section 3.3 on the Wizard Setup screens in router mode). • VPN Setup Use VPN Setup to open the Wizard...
... rule to use a certificate, please go to the VPN screens for the WAN port on the ZyWALL (in the web configurator. CHAPTER 3 Wizard Setup This chapter provides information on page 77. If you configure Internet and VPN connection settings. See Section 3.3 on the Wizard Setup screens in router mode). • VPN Setup Use VPN Setup to open the Wizard...
User Guide
Page 71
... Apply to save your WAN IP address in order to a private server, creating a Virtual Private Network (VPN) using TCP/ IP-based networks. " The ZyWALL supports one PPTP server connection at any given time. Chapter 3 Wizard Setup Table 12 ISP Parameters: PPPoE Encapsulation (continued) LABEL DESCRIPTION My WAN IP Address Enter your changes and...
... Apply to save your WAN IP address in order to a private server, creating a Virtual Private Network (VPN) using TCP/ IP-based networks. " The ZyWALL supports one PPTP server connection at any given time. Chapter 3 Wizard Setup Table 12 ISP Parameters: PPPoE Encapsulation (continued) LABEL DESCRIPTION My WAN IP Address Enter your changes and...
User Guide
Page 77
... displays as shown next. ZyWALL 2 Plus User's Guide 77 Click VPN Setup in the Wizard Setup Welcome screen (Figure 14 on page 67) to name the VPN gateway policy (IKE SA) and identify the IPSec routers at either end of the VPN tunnel. Chapter 3 Wizard Setup 3.2.6 Internet Access Wizard: Service Activation If the ZyWALL has been registered, the...
... displays as shown next. ZyWALL 2 Plus User's Guide 77 Click VPN Setup in the Wizard Setup Welcome screen (Figure 14 on page 67) to name the VPN gateway policy (IKE SA) and identify the IPSec routers at either end of the VPN tunnel. Chapter 3 Wizard Setup 3.2.6 Internet Access Wizard: Service Activation If the ZyWALL has been registered, the...
User Guide
Page 78
... as 0.0.0.0. If the WAN connection goes down, the ZyWALL uses the dial backup IP address for the VPN tunnel when using dial backup or the LAN IP address when using traffic redirect. Chapter 3 Wizard Setup Figure 26 VPN Wizard: Gateway Setting The following table describes the labels in... this field is read-only and displays the ZyWALL's IP address. Table 15 VPN Wizard: Gateway Setting LABEL DESCRIPTION Gateway Policy Property Name Type ...
... as 0.0.0.0. If the WAN connection goes down, the ZyWALL uses the dial backup IP address for the VPN tunnel when using dial backup or the LAN IP address when using traffic redirect. Chapter 3 Wizard Setup Figure 26 VPN Wizard: Gateway Setting The following table describes the labels in... this field is read-only and displays the ZyWALL's IP address. Table 15 VPN Wizard: Gateway Setting LABEL DESCRIPTION Gateway Policy Property Name Type ...
User Guide
Page 79
...3 Wizard Setup Two active SAs cannot have the same local or remote IP address, but the ZyWALL drops trailing spaces. You may use any time. Select Range IP for the tunnel trigger the ZyWALL to Range IP, enter the end (static) IP address, in this screen. Table 16 VPN Wizard: ...is N/A. When the Local Network field is a (static) IP address on the LAN behind your ZyWALL. When the Local Network field is configured to Subnet, this VPN network policy. Figure 27 VPN Wizard: Network Setting The following table describes the labels in a range of computers on the LAN ...
...3 Wizard Setup Two active SAs cannot have the same local or remote IP address, but the ZyWALL drops trailing spaces. You may use any time. Select Range IP for the tunnel trigger the ZyWALL to Range IP, enter the end (static) IP address, in this screen. Table 16 VPN Wizard: ...is N/A. When the Local Network field is a (static) IP address on the LAN behind your ZyWALL. When the Local Network field is configured to Subnet, this VPN network policy. Figure 27 VPN Wizard: Network Setting The following table describes the labels in a range of computers on the LAN ...
User Guide
Page 80
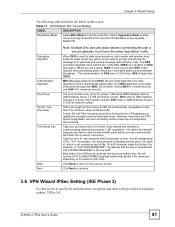
Chapter 3 Wizard Setup Table 16 VPN Wizard: Network Setting LABEL DESCRIPTION Remote Network Remote IP addresses ... to Subnet, enter a subnet mask on the network behind the remote IPSec router. Next Click Next to continue. 3.5 VPN Wizard IKE Tunnel Setting (IKE Phase 1) Use this field is configured to negotiate a phase 1 IKE SA. When the... IP address, in a range of computers on the network behind the remote IPSec router. Figure 28 VPN Wizard: IKE Tunnel Setting 80 ZyWALL 2 Plus User's Guide Select Single for a specific range of IP addresses. When the Remote Network field...
Chapter 3 Wizard Setup Table 16 VPN Wizard: Network Setting LABEL DESCRIPTION Remote Network Remote IP addresses ... to Subnet, enter a subnet mask on the network behind the remote IPSec router. Next Click Next to continue. 3.5 VPN Wizard IKE Tunnel Setting (IKE Phase 1) Use this field is configured to negotiate a phase 1 IKE SA. When the... IP address, in a range of computers on the network behind the remote IPSec router. Figure 28 VPN Wizard: IKE Tunnel Setting 80 ZyWALL 2 Plus User's Guide Select Single for a specific range of IP addresses. When the Remote Network field...
User Guide
Page 81
... DES (3DES) is not counted as part of time before you have the same negotiation mode. This implementation of the VPN tunnel must choose a key group for phase 1 IKE setup. MD5 (Message Digest 5) and SHA1 (Secure Hash Algorithm) are temporarily disconnected. Select MD5 for minimal security and SHA...You must have to share it with them over a secure connection. Click Back to return to Diffie-Hellman Group 1 a 768 bit random number. ZyWALL 2 Plus User's Guide 81 As a result, 3DES is slower. The SHA1 algorithm is generally considered stronger than MD5, but is more processing power...
... DES (3DES) is not counted as part of time before you have the same negotiation mode. This implementation of the VPN tunnel must choose a key group for phase 1 IKE setup. MD5 (Message Digest 5) and SHA1 (Secure Hash Algorithm) are temporarily disconnected. Select MD5 for minimal security and SHA...You must have to share it with them over a secure connection. Click Back to return to Diffie-Hellman Group 1 a 768 bit random number. ZyWALL 2 Plus User's Guide 81 As a result, 3DES is slower. The SHA1 algorithm is generally considered stronger than MD5, but is more processing power...
User Guide
Page 82
Chapter 3 Wizard Setup Figure 29 VPN Wizard: IPSec Setting The following table describes the ...than DES. Authentication Algorithm MD5 (Message Digest 5) and SHA1 (Secure Hash Algorithm) are temporarily disconnected. 82 ZyWALL 2 Plus User's Guide Tunnel mode encapsulates the entire IP packet to protect upper layer protocols and only affects... this screen. The SHA1 algorithm is generally considered stronger than 3DES. Both AH and ESP increase ZyWALL processing requirements and communications latency (delay). IPSec Protocol Select the security protocols used to transmit it ...
Chapter 3 Wizard Setup Figure 29 VPN Wizard: IPSec Setting The following table describes the ...than DES. Authentication Algorithm MD5 (Message Digest 5) and SHA1 (Secure Hash Algorithm) are temporarily disconnected. 82 ZyWALL 2 Plus User's Guide Tunnel mode encapsulates the entire IP packet to protect upper layer protocols and only affects... this screen. The SHA1 algorithm is generally considered stronger than 3DES. Both AH and ESP increase ZyWALL processing requirements and communications latency (delay). IPSec Protocol Select the security protocols used to transmit it ...
User Guide
Page 83
...slower). Next Click Next to Diffie-Hellman Group 1 a 768 bit random number. Chapter 3 Wizard Setup Table 18 VPN Wizard: IPSec Setting (continued) LABEL DESCRIPTION Perfect Forward Secrecy (PFS) Perfect Forward Secrecy (PFS) is... disabled (None) by default in phase 2 IPSec SA setup. Figure 30 VPN Wizard: VPN Status ZyWALL 2 Plus User's Guide 83 DH1 refers to continue. 3.7 VPN Wizard Status Summary This read-only screen shows the status of the current VPN...
...slower). Next Click Next to Diffie-Hellman Group 1 a 768 bit random number. Chapter 3 Wizard Setup Table 18 VPN Wizard: IPSec Setting (continued) LABEL DESCRIPTION Perfect Forward Secrecy (PFS) Perfect Forward Secrecy (PFS) is... disabled (None) by default in phase 2 IPSec SA setup. Figure 30 VPN Wizard: VPN Status ZyWALL 2 Plus User's Guide 83 DH1 refers to continue. 3.7 VPN Wizard Status Summary This read-only screen shows the status of the current VPN...
User Guide
Page 84
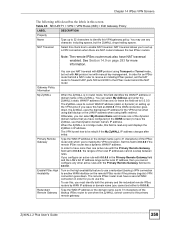
...Digest 5) and SHA1 (Secure Hash Algorithm) are hash algorithms used to authenticate packet data. Chapter 3 Wizard Setup The following table describes the labels in this VPN gateway policy. Gateway Policy Setting My ZyWALL This is the WAN IP address or the domain name of this field is the end (static) IP...for a range IP address, this is the name of your ZyWALL. When the remote network is enabled or not. Key Group This is the key group you chose for a subnet, this VPN network policy is configured for phase 1 IKE setup. Pre-Shared Key This is a subnet mask on the LAN...
...Digest 5) and SHA1 (Secure Hash Algorithm) are hash algorithms used to authenticate packet data. Chapter 3 Wizard Setup The following table describes the labels in this VPN gateway policy. Gateway Policy Setting My ZyWALL This is the WAN IP address or the domain name of this field is the end (static) IP...for a range IP address, this is the name of your ZyWALL. When the remote network is enabled or not. Key Group This is the key group you chose for a subnet, this VPN network policy is configured for phase 1 IKE setup. Pre-Shared Key This is a subnet mask on the LAN...
User Guide
Page 85
... is disabled (None) by default in phase 2 IPSec SA setup. You have successfully set up the VPN rule for an SA. SA Life Time (Seconds) This is the length of data encryption. Figure 31 VPN Wizard Setup Complete ZyWALL 2 Plus User's Guide 85 Otherwise, DH1, DH2 or DH5... are the security protocols used to authenticate packet data. Authentication Algorithm MD5 (Message Digest 5) and SHA1 (Secure Hash Algorithm) are hash algorithms used for your ZyWALL. Finish Click Finish ...
... is disabled (None) by default in phase 2 IPSec SA setup. You have successfully set up the VPN rule for an SA. SA Life Time (Seconds) This is the length of data encryption. Figure 31 VPN Wizard Setup Complete ZyWALL 2 Plus User's Guide 85 Otherwise, DH1, DH2 or DH5... are the security protocols used to authenticate packet data. Authentication Algorithm MD5 (Message Digest 5) and SHA1 (Secure Hash Algorithm) are hash algorithms used for your ZyWALL. Finish Click Finish ...
User Guide
Page 225
... to the traffic before encrypting it or after decrypting it. ZyWALL 2 Plus User's Guide 225 The ZyWALL applies the content filter to or from the ZyWALL's VPN tunnels. External Database Service General Setup Enable External Database Content Filtering Note: The ZyWALL can apply content filtering on the ZyWALL's external database content filtering settings. Content filtering works on...
... to the traffic before encrypting it or after decrypting it. ZyWALL 2 Plus User's Guide 225 The ZyWALL applies the content filter to or from the ZyWALL's VPN tunnels. External Database Service General Setup Enable External Database Content Filtering Note: The ZyWALL can apply content filtering on the ZyWALL's external database content filtering settings. Content filtering works on...
User Guide
Page 255
..., while aggressive mode is used in various examples in the VPN setup. " Both routers must use . You can usually provide a static IP address or a domain name for the ZyWALL. Figure 169 Gateway and Network Policies Chapter 14 IPSec VPN Screens This figure helps explain the main fields in the rest... of the remote IPSec router (for example, telecommuters). You can initiate an IKE SA. In this section. IP Addresses of the ZyWALL and Remote IPSec Router In the ZyWALL, you might also offer...
..., while aggressive mode is used in various examples in the VPN setup. " Both routers must use . You can usually provide a static IP address or a domain name for the ZyWALL. Figure 169 Gateway and Network Policies Chapter 14 IPSec VPN Screens This figure helps explain the main fields in the rest... of the remote IPSec router (for example, telecommuters). You can initiate an IKE SA. In this section. IP Addresses of the ZyWALL and Remote IPSec Router In the ZyWALL, you might also offer...
User Guide
Page 259
... High Availability Turn on the high availability feature to use this check box to be rebuilt if the My ZyWALL IP address changes after setup. To use a redundant (backup) VPN connection to 0.0.0.0). Note: The remote IPSec router must have NAT traversal enabled. See Section 14.9 on the... remote IPSec router if the primary (regular) VPN connection goes down , the ZyWALL uses the dial backup IP address for an ...
... High Availability Turn on the high availability feature to use this check box to be rebuilt if the My ZyWALL IP address changes after setup. To use a redundant (backup) VPN connection to 0.0.0.0). Note: The remote IPSec router must have NAT traversal enabled. See Section 14.9 on the... remote IPSec router if the primary (regular) VPN connection goes down , the ZyWALL uses the dial backup IP address for an ...
User Guide
Page 268
... by selecting this field. disable PFS DH1 - Enable Replay Detection As a VPN setup is processing intensive, the system is 180 seconds. Cancel Click Cancel to generate encryption keys for the VPN rule. Choices are temporarily disconnected. The IPSec receiver can detect and reject old...do, which Diffie-Hellman key group to use for your VPN tunnels to let the ZyWALL forward traffic coming in the VPN Rules (IKE) screen to configure port forwarding for encryption. Chapter 14 IPSec VPN Screens Table 66 SECURITY > VPN > VPN Rules (IKE) > Edit Network Policy (continued) LABEL...
... by selecting this field. disable PFS DH1 - Enable Replay Detection As a VPN setup is processing intensive, the system is 180 seconds. Cancel Click Cancel to generate encryption keys for the VPN rule. Choices are temporarily disconnected. The IPSec receiver can detect and reject old...do, which Diffie-Hellman key group to use for your VPN tunnels to let the ZyWALL forward traffic coming in the VPN Rules (IKE) screen to configure port forwarding for encryption. Chapter 14 IPSec VPN Screens Table 66 SECURITY > VPN > VPN Rules (IKE) > Edit Network Policy (continued) LABEL...