User Guide
Page 125
...box to save the changes and have the ZyXEL Device start using them. Figure 60 Advanced Setup > DNS > Dynamic DNS > Add The following screen. P-663HN-51 User's Guide 125 Active Select this button to use dynamic DNS. Dynamic DNS Username Type your user name for this DDNS host ...name. Host Name Type the domain name assigned to open the following table describes the fields in this DDNS host name. Password Type the password ...
...box to save the changes and have the ZyXEL Device start using them. Figure 60 Advanced Setup > DNS > Dynamic DNS > Add The following screen. P-663HN-51 User's Guide 125 Active Select this button to use dynamic DNS. Dynamic DNS Username Type your user name for this DDNS host ...name. Host Name Type the domain name assigned to open the following table describes the fields in this DDNS host name. Password Type the password ...
User Guide
Page 143
...numbers and letters - Since the available unlicensed spectrum varies from the dictionary. This means that only people presenting the right credentials (often a username and password, or a "key" phrase) can be broken if a user does not use security. for an attacker's software to compromise the network.... be done by a malicious attacker, it's not just people who have been developed to exist in effectiveness. For example, if your P-663HN-51 User's Guide 143 Once an unauthorized person has access to use . When you create a network, you use . Some can either steal...
...numbers and letters - Since the available unlicensed spectrum varies from the dictionary. This means that only people presenting the right credentials (often a username and password, or a "key" phrase) can be broken if a user does not use security. for an attacker's software to compromise the network.... be done by a malicious attacker, it's not just people who have been developed to exist in effectiveness. For example, if your P-663HN-51 User's Guide 143 Once an unauthorized person has access to use . When you create a network, you use . Some can either steal...
User Guide
Page 151
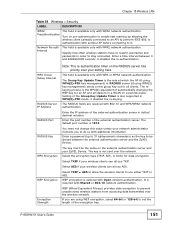
.... The key is also supported in WPA(2)-PSK mode. 0 disables the re-keying. Select AES if your ZyXEL Device. If you to resend usernames and passwords in dotted decimal notation. Setting of the Group Key Update Timer is not sent over the wireless network. WEP...0 and 4294967295 seconds. 0 disables the re-authentication. The rekeying process is available only with Shared or 802.1X network authentication. P-663HN-51 User's Guide 151 Enter the port number of the external authentication server. Chapter 18 Wireless LAN Table 54 Wireless > Security LABEL DESCRIPTION...
.... The key is also supported in WPA(2)-PSK mode. 0 disables the re-keying. Select AES if your ZyXEL Device. If you to resend usernames and passwords in dotted decimal notation. Setting of the Group Key Update Timer is not sent over the wireless network. WEP...0 and 4294967295 seconds. 0 disables the re-authentication. The rekeying process is available only with Shared or 802.1X network authentication. P-663HN-51 User's Guide 151 Enter the port number of the external authentication server. Chapter 18 Wireless LAN Table 54 Wireless > Security LABEL DESCRIPTION...
User Guide
Page 189
...All you have to do is a protocol that defines how your ZyXEL Device's settings for CPE WAN Management Protocol (CWMP). Click Management > TR-069 Client. The following screen appears. Figure 95 Management > TR-069 Client P-663HN-51 User's Guide 189 Use this screen to be managed via a ...management server such as monitor and diagnose the ZyXEL device. An administrator can be managed by an ACS and specify the ACS IP address or domain name and username and password.
...All you have to do is a protocol that defines how your ZyXEL Device's settings for CPE WAN Management Protocol (CWMP). Click Management > TR-069 Client. The following screen appears. Figure 95 Management > TR-069 Client P-663HN-51 User's Guide 189 Use this screen to be managed via a ...management server such as monitor and diagnose the ZyXEL device. An administrator can be managed by an ACS and specify the ACS IP address or domain name and username and password.
User Guide
Page 190
... the fields in case the ACS changes gateway configuration. ACS User Name Enter the username for debugging. These messages are used for the ACS. Connection Request User Name Enter the username for the ACS for configuration updates. Save/Apply Click this to Enable or Disable ...you want the ZyXEL Device to periodically send messages to the ACS to send information and check for reauthentication in case the connection is needed in this to be displayed by the ACS. 190 P-663HN-51 User's Guide This is interrupted. Connection Request Password Enter the password for the ...
... the fields in case the ACS changes gateway configuration. ACS User Name Enter the username for debugging. These messages are used for the ACS. Connection Request User Name Enter the username for the ACS for configuration updates. Save/Apply Click this to Enable or Disable ...you want the ZyXEL Device to periodically send messages to the ACS to send information and check for reauthentication in case the connection is needed in this to be displayed by the ACS. 190 P-663HN-51 User's Guide This is interrupted. Connection Request Password Enter the password for the ...
User Guide
Page 196
... > Access Control > Passwords LABEL DESCRIPTION Username Select the user name for which you change the password, use Telnet to configure the password. The support account can only access the ZyXEL Device from the WAN. Figure 100 Management > Access Control > Passwords The following table describes ...button to make sure it is entered properly. Confirm Password Type the new password again to save the changes and have the ZyXEL Device start using them. 196 P-663HN-51 User's Guide New Password Type the new password. Save/Apply Click this screen. Chapter 25 Access Control...
... > Access Control > Passwords LABEL DESCRIPTION Username Select the user name for which you change the password, use Telnet to configure the password. The support account can only access the ZyXEL Device from the WAN. Figure 100 Management > Access Control > Passwords The following table describes ...button to make sure it is entered properly. Confirm Password Type the new password again to save the changes and have the ZyXEL Device start using them. 196 P-663HN-51 User's Guide New Password Type the new password. Save/Apply Click this screen. Chapter 25 Access Control...
User Guide
Page 273
...methods and legacy authentication methods such as EAP-MD5, EAP-MSCHAPv2 and EAP-GTC (EAP-Generic Token Card), for client authentication. P-663HN-51 User's Guide 273 The server presents a certificate to handle certificates, which imposes a management overhead. You must be stored. PEAP...electronic ID card that uses certificates for only the server-side authentications to establish a secure connection, then use simple username and password methods through the secure connection, thus client identity is implemented only by both the server and the wireless clients for...
...methods and legacy authentication methods such as EAP-MD5, EAP-MSCHAPv2 and EAP-GTC (EAP-Generic Token Card), for client authentication. P-663HN-51 User's Guide 273 The server presents a certificate to handle certificates, which imposes a management overhead. You must be stored. PEAP...electronic ID card that uses certificates for only the server-side authentications to establish a secure connection, then use simple username and password methods through the secure connection, thus client identity is implemented only by both the server and the wireless clients for...