User Guide
Page 9
Contents Overview Contents Overview Introduction and Wizards ...37 Getting To Know Your ZyXEL Device 39 Introducing the Web Configurator 43 Wizard Setup for Internet Access 59 Bandwidth Management Wizard 73 Network ...79 WAN Setup...NAT) Screens 141 Security ...155 Firewalls ...157 Firewall Configuration ...169 Content Filtering ...191 Content Access Control ...195 Register ...211 Introduction to IPSec ...215 VPN Screens ...221 Certificates ...247 Advanced ...271 Static Route ...273 Bandwidth Management ...277 Dynamic DNS Setup ...287 Remote Management Configuration 291 Universal Plug-and-...
Contents Overview Contents Overview Introduction and Wizards ...37 Getting To Know Your ZyXEL Device 39 Introducing the Web Configurator 43 Wizard Setup for Internet Access 59 Bandwidth Management Wizard 73 Network ...79 WAN Setup...NAT) Screens 141 Security ...155 Firewalls ...157 Firewall Configuration ...169 Content Filtering ...191 Content Access Control ...195 Register ...211 Introduction to IPSec ...215 VPN Screens ...221 Certificates ...247 Advanced ...271 Static Route ...273 Bandwidth Management ...277 Dynamic DNS Setup ...287 Remote Management Configuration 291 Universal Plug-and-...
User Guide
Page 11
......23 List of Tables...31 Part I: Introduction and Wizards 37 Chapter 1 Getting To Know Your ZyXEL Device 39 1.1 Introducing the ZyXEL Device 39 1.1.1 Applications of the ZyXEL Device 39 1.1.2 Firewall for Secure Broadband Internet Access 40 1.1.3 Front Panel LEDs ...41 Chapter ...2 Introducing the Web Configurator 43 2.1 Web Configurator Overview 43 2.2 Accessing the Web Configurator 43 2.3 Resetting the ZyXEL Device 46 2.3.1 Using the Reset Button 46 2.4 Navigating the Web Configurator 47 2.4.1 Navigation Panel ...47 2.4.2 Status Screen ...50 2.4.3 Status...
......23 List of Tables...31 Part I: Introduction and Wizards 37 Chapter 1 Getting To Know Your ZyXEL Device 39 1.1 Introducing the ZyXEL Device 39 1.1.1 Applications of the ZyXEL Device 39 1.1.2 Firewall for Secure Broadband Internet Access 40 1.1.3 Front Panel LEDs ...41 Chapter ...2 Introducing the Web Configurator 43 2.1 Web Configurator Overview 43 2.2 Accessing the Web Configurator 43 2.3 Resetting the ZyXEL Device 46 2.3.1 Using the Reset Button 46 2.4 Navigating the Web Configurator 47 2.4.1 Navigation Panel ...47 2.4.2 Status Screen ...50 2.4.3 Status...
User Guide
Page 16
...Register...211 14.1 myZyXEL.com overview 211 14.1.1 Subscription Services Available on the ZyXEL Device 211 14.2 Registration ...212 14.3 Service ...213 Chapter 15 Introduction to IPSec...215 15.1 VPN Overview ...215 15.1.1 IPSec ...215 15.1.2 Security Association 215 15.1.3 Other Terminology... 215 15.1.4 VPN Applications 216 15.2 IPSec Architecture ...216 15.2.1 IPSec Algorithms ...217 15.2.2 Key Management 217 15.3 Encapsulation ...217 16 P-662H/HW-D Series User's Guide
...Register...211 14.1 myZyXEL.com overview 211 14.1.1 Subscription Services Available on the ZyXEL Device 211 14.2 Registration ...212 14.3 Service ...213 Chapter 15 Introduction to IPSec...215 15.1 VPN Overview ...215 15.1.1 IPSec ...215 15.1.2 Security Association 215 15.1.3 Other Terminology... 215 15.1.4 VPN Applications 216 15.2 IPSec Architecture ...216 15.2.1 IPSec Algorithms ...217 15.2.2 Key Management 217 15.3 Encapsulation ...217 16 P-662H/HW-D Series User's Guide
User Guide
Page 17
... ...226 16.9 ID Type and Content ...227 16.9.1 ID Type and Content Examples 228 16.10 Pre-Shared Key ...229 16.11 Editing VPN Policies ...229 16.12 IKE Phases ...233 16.12.1 Negotiation Mode 234 16.12.2 Diffie-Hellman (DH) Key Groups 235 16.12.3 ...Sharing One VPN Rule Example 243 16.18.2 Telecommuters Using Unique VPN Rules Example 244 16.19 VPN and Remote Management 245 Chapter 17 Certificates ...247 17.1 Certificates Overview ...247 17.1.1 Advantages of Certificates 248 17.2 Self-signed Certificates ...248 17.3 Configuration Summary 248 17.4 My Certificates ...248 P-662H/HW-D Series...
... ...226 16.9 ID Type and Content ...227 16.9.1 ID Type and Content Examples 228 16.10 Pre-Shared Key ...229 16.11 Editing VPN Policies ...229 16.12 IKE Phases ...233 16.12.1 Negotiation Mode 234 16.12.2 Diffie-Hellman (DH) Key Groups 235 16.12.3 ...Sharing One VPN Rule Example 243 16.18.2 Telecommuters Using Unique VPN Rules Example 244 16.19 VPN and Remote Management 245 Chapter 17 Certificates ...247 17.1 Certificates Overview ...247 17.1.1 Advantages of Certificates 248 17.2 Self-signed Certificates ...248 17.3 Configuration Summary 248 17.4 My Certificates ...248 P-662H/HW-D Series...
User Guide
Page 23
List of Figures List of Figures Figure 1 ZyXEL Device Internet Access Application 40 Figure 2 ZyXEL Device LAN-to-LAN Application Example 40 Figure 3 Firewall Application ...41 Figure 4 P-662H Front Panel ...41 Figure 5 P-662HW Front Panel ...41 Figure 6 Password Screen ...44 Figure 7 Change Password at Login ...45 Figure 8...Figure 12 Status: Any IP Table ...53 Figure 13 Status: WLAN Status ...54 Figure 14 Status: Bandwidth Status ...54 Figure 15 Status: VPN Status ...55 Figure 16 Status: Packet Statistics ...56 Figure 17 System General ...57 Figure 18 Select a Mode ...59 Figure 19 Wizard: ...
List of Figures List of Figures Figure 1 ZyXEL Device Internet Access Application 40 Figure 2 ZyXEL Device LAN-to-LAN Application Example 40 Figure 3 Firewall Application ...41 Figure 4 P-662H Front Panel ...41 Figure 5 P-662HW Front Panel ...41 Figure 6 Password Screen ...44 Figure 7 Change Password at Login ...45 Figure 8...Figure 12 Status: Any IP Table ...53 Figure 13 Status: WLAN Status ...54 Figure 14 Status: Bandwidth Status ...54 Figure 15 Status: VPN Status ...55 Figure 16 Status: Packet Statistics ...56 Figure 17 System General ...57 Figure 18 Select a Mode ...59 Figure 19 Wizard: ...
User Guide
Page 26
... to Set Up the IPSec SA 233 Figure 134 Advanced VPN Policies ...236 Figure 135 VPN: Manual Key ...239 Figure 136 VPN: SA Monitor ...242 Figure 137 VPN: Global Setting ...242 Figure 138 Telecommuters Sharing One VPN Rule Example 243 Figure 139 Telecommuters Using Unique VPN Rules Example 244 Figure 140 Certificate Configuration Overview 248 Figure... Management: WWW 293 Figure 165 Telnet Configuration on a TCP/IP Network 294 Figure 166 Remote Management: Telnet 294 Figure 167 Remote Management: FTP 295 26 P-662H/HW-D Series User's Guide
... to Set Up the IPSec SA 233 Figure 134 Advanced VPN Policies ...236 Figure 135 VPN: Manual Key ...239 Figure 136 VPN: SA Monitor ...242 Figure 137 VPN: Global Setting ...242 Figure 138 Telecommuters Sharing One VPN Rule Example 243 Figure 139 Telecommuters Using Unique VPN Rules Example 244 Figure 140 Certificate Configuration Overview 248 Figure... Management: WWW 293 Figure 165 Telnet Configuration on a TCP/IP Network 294 Figure 166 Remote Management: Telnet 294 Figure 167 Remote Management: FTP 295 26 P-662H/HW-D Series User's Guide
User Guide
Page 31
... LEDs ...41 Table 2 Web Configurator Screens Summary 47 Table 3 Status Screen ...51 Table 4 Status: Any IP Table ...53 Table 5 Status: WLAN Status ...54 Table 6 Status: VPN Status ...55 Table 7 Status: Packet Statistics ...56 Table 8 System General: Password ...57 Table 9 Internet Access Wizard Setup: ISP Parameters 62 Table 10 Internet Connection with... Table 35 Additional Wireless Terms ...116 Table 36 Wireless LAN: General ...118 Table 37 Wireless No Security ...119 Table 38 Wireless: Static WEP Encryption 120 P-662H/HW-D Series User's Guide 31
... LEDs ...41 Table 2 Web Configurator Screens Summary 47 Table 3 Status Screen ...51 Table 4 Status: Any IP Table ...53 Table 5 Status: WLAN Status ...54 Table 6 Status: VPN Status ...55 Table 7 Status: Packet Statistics ...56 Table 8 System General: Password ...57 Table 9 Internet Access Wizard Setup: ISP Parameters 62 Table 10 Internet Connection with... Table 35 Additional Wireless Terms ...116 Table 36 Wireless LAN: General ...118 Table 37 Wireless No Security ...119 Table 38 Wireless: Static WEP Encryption 120 P-662H/HW-D Series User's Guide 31
User Guide
Page 33
...: Trusted-external Website 209 Table 83 Security > Register ...212 Table 84 Security > Register > Service 214 Table 85 VPN and NAT ...219 Table 86 AH and ESP ...222 Table 87 VPN Setup ...224 Table 88 VPN and NAT ...226 Table 89 Local ID Type and Content Fields 227 Table 90 Peer ID Type and... 282 Table 121 Bandwidth Management Rule Configuration 284 Table 122 Dynamic DNS ...288 Table 123 Remote Management: WWW 293 Table 124 Remote Management: Telnet 295 P-662H/HW-D Series User's Guide 33
...: Trusted-external Website 209 Table 83 Security > Register ...212 Table 84 Security > Register > Service 214 Table 85 VPN and NAT ...219 Table 86 AH and ESP ...222 Table 87 VPN Setup ...224 Table 88 VPN and NAT ...226 Table 89 Local ID Type and Content Fields 227 Table 90 Peer ID Type and... 282 Table 121 Bandwidth Management Rule Configuration 284 Table 122 Dynamic DNS ...288 Table 123 Remote Management: WWW 293 Table 124 Remote Management: Telnet 295 P-662H/HW-D Series User's Guide 33
User Guide
Page 49
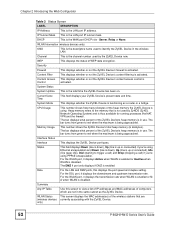
...to update your ZyXEL Device. Trusted-external Use this screen to register with myZyXEL.com and activate services on your license key information and update the status of each VPN tunnel. Service Use this screen to view information about users accessing the Internet. VPN Global Setting ...this screen to look at the current status of the services you subscribe to configure computers excluded from Content Website Access Control settings. P-662H/HW-D Series User's Guide 49 Monitor Use this screen to exclude a range of valid and revoked certificates). Trusted Device Use this ...
...to update your ZyXEL Device. Trusted-external Use this screen to register with myZyXEL.com and activate services on your license key information and update the status of each VPN tunnel. Service Use this screen to view information about users accessing the Internet. VPN Global Setting ...this screen to look at the current status of the services you subscribe to configure computers excluded from Content Website Access Control settings. P-662H/HW-D Series User's Guide 49 Monitor Use this screen to exclude a range of valid and revoked certificates). Trusted Device Use this ...
User Guide
Page 52
... heap memory (in use . For the WLAN port, it displays Active when WLAN is enabled or Inactive when WLAN is functioning as the ZyXEL Device. only) 52 P-662H/HW-D Series User's Guide System Status System Uptime This is the WAN port DHCP role - The bar turns from green to red when...) and is being approached. Heap memory refers to red when the maximum is thus available for running processes like NAT, VPN and the firewall. The bar displays what percent of the ZyXEL Device's heap memory is up or connected) if you 're using . The bar turns from green to the memory...
... heap memory (in use . For the WLAN port, it displays Active when WLAN is enabled or Inactive when WLAN is functioning as the ZyXEL Device. only) 52 P-662H/HW-D Series User's Guide System Status System Uptime This is the WAN port DHCP role - The bar turns from green to red when...) and is being approached. Heap memory refers to red when the maximum is thus available for running processes like NAT, VPN and the firewall. The bar displays what percent of the ZyXEL Device's heap memory is up or connected) if you 're using . The bar turns from green to the memory...
User Guide
Page 53
P-662H/HW-D Series User's Guide 53 MAC Address This field displays the MAC (Media Access Control) address of the network device. VPN Status Use this screen to view VPN status and settings. 2.4.3 Status: Any IP Table Click the Any IP Table hyperlink in the Status screen to ... has a unique MAC address. Figure 12 Status: Any IP Table The following table describes the labels in this screen to view the ZyXEL Device's bandwidth usage and allotments. Chapter 2 Introducing the Web Configurator Table 3 Status Screen LABEL DESCRIPTION Bandwidth Status Use this screen to view...
P-662H/HW-D Series User's Guide 53 MAC Address This field displays the MAC (Media Access Control) address of the network device. VPN Status Use this screen to view VPN status and settings. 2.4.3 Status: Any IP Table Click the Any IP Table hyperlink in the Status screen to ... has a unique MAC address. Figure 12 Status: Any IP Table The following table describes the labels in this screen to view the ZyXEL Device's bandwidth usage and allotments. Chapter 2 Introducing the Web Configurator Table 3 Status Screen LABEL DESCRIPTION Bandwidth Status Use this screen to view...
User Guide
Page 54
...number of an associated wireless station. Refresh Click Refresh to reload this screen. Figure 14 Status: Bandwidth Status 2.4.6 Status: VPN Status Click the VPN Status hyperlink in use. MAC Address This field displays the MAC (Media Access Control) address of bandwidth in the Status ... rules. Association TIme This field displays the time a wireless station first associated with the P-662H/HW-Dx. View the bandwidth usage of any VPN tunnels the ZyXEL Device has negotiated. 54 P-662H/HW-D Series User's Guide Table 5 Status: WLAN Status LABEL DESCRIPTION # This is also...
...number of an associated wireless station. Refresh Click Refresh to reload this screen. Figure 14 Status: Bandwidth Status 2.4.6 Status: VPN Status Click the VPN Status hyperlink in use. MAC Address This field displays the MAC (Media Access Control) address of bandwidth in the Status ... rules. Association TIme This field displays the time a wireless station first associated with the P-662H/HW-Dx. View the bandwidth usage of any VPN tunnels the ZyXEL Device has negotiated. 54 P-662H/HW-D Series User's Guide Table 5 Status: WLAN Status LABEL DESCRIPTION # This is also...
User Guide
Page 55
... interval(s)". Encapsulation This field displays Tunnel or Transport mode. Read-only information here includes port status and packet specific statistics. P-662H/HW-D Series User's Guide 55 Refresh Click Refresh to stop that security association. Figure 15 Status: VPN Status Chapter 2 Introducing the Web Configurator The following table describes the labels in this...
... interval(s)". Encapsulation This field displays Tunnel or Transport mode. Read-only information here includes port status and packet specific statistics. P-662H/HW-D Series User's Guide 55 Refresh Click Refresh to stop that security association. Figure 15 Status: VPN Status Chapter 2 Introducing the Web Configurator The following table describes the labels in this...
User Guide
Page 155
PART III Security Firewalls (157) Firewall Configuration (169) Content Filtering (191) Content Access Control (195) Register (211) Introduction to IPSec (215) VPN Screens (221) Certificates (247) 155
PART III Security Firewalls (157) Firewall Configuration (169) Content Filtering (191) Content Access Control (195) Register (211) Introduction to IPSec (215) VPN Screens (221) Certificates (247) 155
User Guide
Page 215
P-662H/HW-D Series User's Guide 215 A secure VPN is a combination of encryption: it is a standards-based VPN that offers flexible solutions for secure data communications across a public network like the Internet. Decryption also requires a key. ...leads to the data scrambling that makes encryption secure. CHAPTER 15 Introduction to IPSec This chapter introduces the basics of IPSec VPNs. 15.1 VPN Overview A VPN (Virtual Private Network) provides secure communications between sites without the expense of standardized cryptographic techniques to provide confidentiality, data integrity...
P-662H/HW-D Series User's Guide 215 A secure VPN is a combination of encryption: it is a standards-based VPN that offers flexible solutions for secure data communications across a public network like the Internet. Decryption also requires a key. ...leads to the data scrambling that makes encryption secure. CHAPTER 15 Introduction to IPSec This chapter introduces the basics of IPSec VPNs. 15.1 VPN Overview A VPN (Virtual Private Network) provides secure communications between sites without the expense of standardized cryptographic techniques to provide confidentiality, data integrity...
User Guide
Page 216
...that the data has not been altered during transmission. 15.1.3.4 Data Origin Authentication The IPSec receiver can verify the source of a VPN application. 15.2 IPSec Architecture The overall IPSec architecture is designated a public LAN server for unsupported emerging IP applications. Chapter 15 ...hosts on the LAN unless the host is shown as follows. 216 P-662H/HW-D Series User's Guide This service depends on the data integrity service. 15.1.4 VPN Applications The ZyXEL Device supports the following VPN applications. • Linking Two or More Private Networks Together Connect branch...
...that the data has not been altered during transmission. 15.1.3.4 Data Origin Authentication The IPSec receiver can verify the source of a VPN application. 15.2 IPSec Architecture The overall IPSec architecture is designated a public LAN server for unsupported emerging IP applications. Chapter 15 ...hosts on the LAN unless the host is shown as follows. 216 P-662H/HW-D Series User's Guide This service depends on the data integrity service. 15.1.4 VPN Applications The ZyXEL Device supports the following VPN applications. • Linking Two or More Private Networks Together Connect branch...
User Guide
Page 217
Figure 126 IPSec Architecture Chapter 15 Introduction to set up a VPN. 15.3 Encapsulation The two modes of encryption techniques such as DES (Data Encryption Standard) and Triple DES algorithms. The Authentication Algorithms, HMAC-MD5 (RFC ... page 221for more information. 15.2.2 Key Management Key management allows you to determine whether to use of operation for packet structure (including implementation algorithms). P-662H/HW-D Series User's Guide 217 The Encryption Algorithm describes the use IKE (ISAKMP) or manual key configuration in order to IPSec 15.2.1 IPSec Algorithms The...
Figure 126 IPSec Architecture Chapter 15 Introduction to set up a VPN. 15.3 Encapsulation The two modes of encryption techniques such as DES (Data Encryption Standard) and Triple DES algorithms. The Authentication Algorithms, HMAC-MD5 (RFC ... page 221for more information. 15.2.2 Key Management Key management allows you to determine whether to use of operation for packet structure (including implementation algorithms). P-662H/HW-D Series User's Guide 217 The Encryption Algorithm describes the use IKE (ISAKMP) or manual key configuration in order to IPSec 15.2.1 IPSec Algorithms The...
User Guide
Page 218
...extended forward into the IP header to verify the integrity of the entire packet by use of portions of the final system behind the ZyXEL Device. The security protocol appears after the original IP header and options, but before the inside IP header contains the destination IP address.... An IPSec VPN using AH protocol, packet contents (the data payload) are not used to protect upper layer protocols and only affects the data in both data payload and headers, with authentication and encryption. The IP header information and options are not encrypted. 218 P-662H/HW-D Series User's ...
...extended forward into the IP header to verify the integrity of the entire packet by use of portions of the final system behind the ZyXEL Device. The security protocol appears after the original IP header and options, but before the inside IP header contains the destination IP address.... An IPSec VPN using AH protocol, packet contents (the data payload) are not used to protect upper layer protocols and only affects the data in both data payload and headers, with authentication and encryption. The IP header information and options are not encrypted. 218 P-662H/HW-D Series User's ...
User Guide
Page 219
... AH Tunnel N ESP Transport N ESP Tunnel Y P-662H/HW-D Series User's Guide 219 IPSec using ESP protocol with authentication, the packet contents (in this case, the entire original packet) are signed with authentication is the inbound address of the VPN device at the receiving end. The new IP packet's ...has been maliciously altered. When using ESP in Tunnel mode encapsulates the entire original packet (including headers) in a new IP packet. The VPN device at the receiving end doesn't know about the NAT in the middle, so it assumes that the hash value appended to the ...
... AH Tunnel N ESP Transport N ESP Tunnel Y P-662H/HW-D Series User's Guide 219 IPSec using ESP protocol with authentication, the packet contents (in this case, the entire original packet) are signed with authentication is the inbound address of the VPN device at the receiving end. The new IP packet's ...has been maliciously altered. When using ESP in Tunnel mode encapsulates the entire original packet (including headers) in a new IP packet. The VPN device at the receiving end doesn't know about the NAT in the middle, so it assumes that the hash value appended to the ...
User Guide
Page 221
... the Logs chapter for information on viewing logs and the appendix for IPSec log descriptions. 16.1 VPN/IPSec Overview Use the screens documented in this chapter to configure rules for VPN connections and manage VPN connections. 16.2 IPSec Algorithms The ESP and AH protocols are limited compared to the AH due to ensure... if only the upper layer protocols need to create a Security Association (SA), the foundation of the IP header information during the authentication process. CHAPTER 16 VPN Screens This chapter introduces the VPN screens. P-662H/HW-D Series User's Guide 221
... the Logs chapter for information on viewing logs and the appendix for IPSec log descriptions. 16.1 VPN/IPSec Overview Use the screens documented in this chapter to configure rules for VPN connections and manage VPN connections. 16.2 IPSec Algorithms The ESP and AH protocols are limited compared to the AH due to ensure... if only the upper layer protocols need to create a Security Association (SA), the foundation of the IP header information during the authentication process. CHAPTER 16 VPN Screens This chapter introduces the VPN screens. P-662H/HW-D Series User's Guide 221