User Guide
Page 28
...supports TCP/UDP inspection, DoS detection and prevention, real time alerts, reports and logs. PPTP Encapsulation Point-to-Point Tunneling Protocol (PPTP) is a stateful inspection firewall with an Internet modem to achieve access to highspeed data networks via a familiar "dial-up networking" user interface. IP address to 192...Play (UPnP) Using the standard TCP/IP protocol, the Prestige and other UPnP enabled devices can also set the time manually. P-320W User's Guide Reset Button The Prestige reset button is initiated from an external server when you to get the current time and date ...
...supports TCP/UDP inspection, DoS detection and prevention, real time alerts, reports and logs. PPTP Encapsulation Point-to-Point Tunneling Protocol (PPTP) is a stateful inspection firewall with an Internet modem to achieve access to highspeed data networks via a familiar "dial-up networking" user interface. IP address to 192...Play (UPnP) Using the standard TCP/IP protocol, the Prestige and other UPnP enabled devices can also set the time manually. P-320W User's Guide Reset Button The Prestige reset button is initiated from an external server when you to get the current time and date ...
User Guide
Page 31
...ZyXEL wireless adapters must also have OTIST enabled. Figure 1 Secure Internet Access via Cable, DSL or Wireless Modem Chapter 1 Getting to help keep network communications private. Wireless LAN MAC Address Filtering Your Prestige can do with a 2dBi fixed antenna to provide clear radio signal between the wireless stations and the access points... examples of what you can see the list of allowed or denied MAC addresses. P-320W User's Guide Antenna The Prestige is equipped with your Prestige. 1.3.1 Secure Broadband Internet Access via an Ethernet or a wireless port on the modem.
...ZyXEL wireless adapters must also have OTIST enabled. Figure 1 Secure Internet Access via Cable, DSL or Wireless Modem Chapter 1 Getting to help keep network communications private. Wireless LAN MAC Address Filtering Your Prestige can do with a 2dBi fixed antenna to provide clear radio signal between the wireless stations and the access points... examples of what you can see the list of allowed or denied MAC addresses. P-320W User's Guide Antenna The Prestige is equipped with your Prestige. 1.3.1 Secure Broadband Internet Access via an Ethernet or a wireless port on the modem.
User Guide
Page 53
... authentication method that works with a broadband modem (for example DSL, cable, wireless, etc.) to achieve access to -Point Protocol over Ethernet option for a dial-up connection. Select the PPP over Ethernet (PPPoE) functions as a dial-up connection. 3.4.1 ... is an IETF (Internet Engineering Task Force) standard specifying how a host personal computer interacts with existing access control systems (for a dial-up connection. Select the PPTP option for instance, RADIUS). P-320W User's Guide The following table describes the labels in this screen, Table 13 Connection Wizard: STEP 3:...
... authentication method that works with a broadband modem (for example DSL, cable, wireless, etc.) to achieve access to -Point Protocol over Ethernet option for a dial-up connection. Select the PPP over Ethernet (PPPoE) functions as a dial-up connection. 3.4.1 ... is an IETF (Internet Engineering Task Force) standard specifying how a host personal computer interacts with existing access control systems (for a dial-up connection. Select the PPTP option for instance, RADIUS). P-320W User's Guide The following table describes the labels in this screen, Table 13 Connection Wizard: STEP 3:...
User Guide
Page 61
Wireless security methods available on protocols used when a client authenticates with wireless LAN adapters communicating through access points which bridge network traffic to the wired LAN. See the appendices for more detailed information on WLANs. 4.2... Prestige. P-320W User's Guide CHAPTER 4 Wireless LAN This chapter discusses how to configure Wireless LAN. 4.1 Introduction A wireless LAN can also configure IEEE 802.1x to use a RADIUS server to authenticate wireless clients before joining your network to protect wireless communication between wireless stations, access points and the...
Wireless security methods available on protocols used when a client authenticates with wireless LAN adapters communicating through access points which bridge network traffic to the wired LAN. See the appendices for more detailed information on WLANs. 4.2... Prestige. P-320W User's Guide CHAPTER 4 Wireless LAN This chapter discusses how to configure Wireless LAN. 4.1 Introduction A wireless LAN can also configure IEEE 802.1x to use a RADIUS server to authenticate wireless clients before joining your network to protect wireless communication between wireless stations, access points and the...
User Guide
Page 62
... Security Technology) allows you to transfer your wireless network by MAC address. 3 If you have the same SSID and security settings as the access point (AP) or wireless router (we will refer to both as "AP" here) in the Wireless screen. OTIST transfers device SSID and WEP...the OTIST screen. Traditionally this meant that support OTIST and are within transmission range. P-320W User's Guide 4.2.3 Restricted Access The MAC Filter screen allows you to configure the AP to give exclusive access to configure the settings on the AP and then manually configure the exact same settings on...
... Security Technology) allows you to transfer your wireless network by MAC address. 3 If you have the same SSID and security settings as the access point (AP) or wireless router (we will refer to both as "AP" here) in the Wireless screen. OTIST transfers device SSID and WEP...the OTIST screen. Traditionally this meant that support OTIST and are within transmission range. P-320W User's Guide 4.2.3 Restricted Access The MAC Filter screen allows you to configure the AP to give exclusive access to configure the settings on the AP and then manually configure the exact same settings on...
User Guide
Page 64
... You must have the same SSID. Click Apply to save your network is accessible to 32 printable 7-bit ASCII characters) for information on channels. Note: If you press Apply to confirm. P-320W User's Guide The following table describes the general wireless LAN labels in the .... Refer to the Connection Wizard chapter for this screen. 4.4.1 No Security Select No Security to allow wireless stations to communicate with the access points without any wireless security on your computer to activate wireless LAN. (Service Set IDentity) The SSID identifies the Service Set with which a...
... You must have the same SSID. Click Apply to save your network is accessible to 32 printable 7-bit ASCII characters) for information on channels. Note: If you press Apply to confirm. P-320W User's Guide The following table describes the general wireless LAN labels in the .... Refer to the Connection Wizard chapter for this screen. 4.4.1 No Security Select No Security to allow wireless stations to communicate with the access points without any wireless security on your computer to activate wireless LAN. (Service Set IDentity) The SSID identifies the Service Set with which a...
User Guide
Page 65
...unicast and multicast communications in this screen. 4.4.2 WEP Encryption WEP encryption scrambles the data transmitted between the wireless stations and the access points to keep network communications private. click Wireless LAN and Wireless to four 64-bit or 128-bit WEP keys but only one... Static WEP from the drop-down list box. Figure 28 Wireless: No Security P-320W User's Guide The following table describes the labels in a network. Click Reset to reload the previous configuration for this screen. Both the wireless stations and the access points must use the same WEP key.
...unicast and multicast communications in this screen. 4.4.2 WEP Encryption WEP encryption scrambles the data transmitted between the wireless stations and the access points to keep network communications private. click Wireless LAN and Wireless to four 64-bit or 128-bit WEP keys but only one... Static WEP from the drop-down list box. Figure 28 Wireless: No Security P-320W User's Guide The following table describes the labels in a network. Click Reset to reload the previous configuration for this screen. Both the wireless stations and the access points must use the same WEP key.
User Guide
Page 67
.... If you should use WPA for this screen. 4.4.3 Introduction to WPA Wi-Fi Protected Access (WPA) is a subset of between 8 and 63 ASCII characters (including spaces and symbols). 2 The AP checks each access point, wireless gateway and wireless client. P-320W User's Guide Table 22 Wireless: Static WEP Encryption LABEL DESCRIPTION Key 1 to Key 4 The...
.... If you should use WPA for this screen. 4.4.3 Introduction to WPA Wi-Fi Protected Access (WPA) is a subset of between 8 and 63 ASCII characters (including spaces and symbols). 2 The AP checks each access point, wireless gateway and wireless client. P-320W User's Guide Table 22 Wireless: Static WEP Encryption LABEL DESCRIPTION Key 1 to Key 4 The...
User Guide
Page 195
...Service Set (BSS) exists when all communications between wireless stations or between a wireless station and a wired network client go through one access point (AP). When Intra-BSS is commonly referred to as an Ad-hoc network or Independent Basic Service Set (IBSS). Figure 138 ... traffic is disabled, wireless station A and B can set of notebook computers using wireless adapters to -Peer Communication in the BSS. P-320W User's Guide APPENDIX F Wireless LANs Wireless LAN Topologies This section discusses ad-hoc and infrastructure wireless LAN topologies. Ad-hoc Wireless LAN...
...Service Set (BSS) exists when all communications between wireless stations or between a wireless station and a wired network client go through one access point (AP). When Intra-BSS is commonly referred to as an Ad-hoc network or Independent Basic Service Set (IBSS). Figure 138 ... traffic is disabled, wireless station A and B can set of notebook computers using wireless adapters to -Peer Communication in the BSS. P-320W User's Guide APPENDIX F Wireless LANs Wireless LAN Topologies This section discusses ad-hoc and infrastructure wireless LAN topologies. Ad-hoc Wireless LAN...
User Guide
Page 196
This type of overlapping BSSs, each containing an access point, with the wired network but also mediate wireless network traffic in order to communicate. 196 Appendix F Wireless LANs P-320W User's Guide Figure 139 Basic Service Set ESS An Extended Service Set (ESS) consists of a series of wireless LAN topology is called an Infrastructure WLAN...
This type of overlapping BSSs, each containing an access point, with the wired network but also mediate wireless network traffic in order to communicate. 196 Appendix F Wireless LANs P-320W User's Guide Figure 139 Basic Service Set ESS An Extended Service Set (ESS) consists of a series of wireless LAN topology is called an Infrastructure WLAN...
User Guide
Page 197
... region has 11 channels and an adjacent AP is using channel 1, then you should use a different channel than an adjacent AP (access point) to reduce interference. The following figure illustrates a hidden node. To avoid interference due to select a channel between 6 or 11....depend on a channel at least five channels away from different access points overlap causing interference and degrading performance. You may have a choice of each other . Adjacent channels partially overlap however. Figure 140 Infrastructure WLAN P-320W User's Guide Channel A channel is currently being used by...
... region has 11 channels and an adjacent AP is using channel 1, then you should use a different channel than an adjacent AP (access point) to reduce interference. The following figure illustrates a hidden node. To avoid interference due to select a channel between 6 or 11....depend on a channel at least five channels away from different access points overlap causing interference and degrading performance. You may have a choice of each other . Adjacent channels partially overlap however. Figure 140 Infrastructure WLAN P-320W User's Guide Channel A channel is currently being used by...
User Guide
Page 199
... transmission timing in a good wireless network environment when all IEEE 802.11b compliant wireless adapters must support long preamble. P-320W User's Guide A large Fragmentation Threshold is fully compatible with an IEEE 802.11g access point (and vice versa) at 11 Mbps or lower depending on range. Preamble Type A preamble is smaller than the...
... transmission timing in a good wireless network environment when all IEEE 802.11b compliant wireless adapters must support long preamble. P-320W User's Guide A large Fragmentation Threshold is fully compatible with an IEEE 802.11g access point (and vice versa) at 11 Mbps or lower depending on range. Preamble Type A preamble is smaller than the...
User Guide
Page 200
...320W User's Guide IEEE 802.1x In June 2001, the IEEE 802.1x standard was designed to extend the features of IEEE 802.11 to support extended authentication as well as a message relay between the access point and the RADIUS server for user authentication: • Access-Request Sent by an access point requesting authentication. • Access...-Reject Sent by a RADIUS server rejecting access. • Access-Accept Sent by Windows...
...320W User's Guide IEEE 802.1x In June 2001, the IEEE 802.1x standard was designed to extend the features of IEEE 802.11 to support extended authentication as well as a message relay between the access point and the RADIUS server for user authentication: • Access-Request Sent by an access point requesting authentication. • Access...-Reject Sent by a RADIUS server rejecting access. • Access-Accept Sent by Windows...
User Guide
Page 201
P-320W User's Guide • Access-Challenge Sent by the RADIUS server to indicate that runs on top of the IEEE802.1x transport mechanism in order to allow access. In order to ensure network security, the access point and the RADIUS server use depends on your access point. EAP ...device. 2 The device sends a "request identity" message to the wireless station for user accounting: • Accounting-Request Sent by the access point requesting accounting. • Accounting-Response Sent by a RADIUS server requesting more information in order to protect the network from the user and...
P-320W User's Guide • Access-Challenge Sent by the RADIUS server to indicate that runs on top of the IEEE802.1x transport mechanism in order to allow access. In order to ensure network security, the access point and the RADIUS server use depends on your access point. EAP ...device. 2 The device sends a "request identity" message to the wireless station for user accounting: • Accounting-Request Sent by the access point requesting accounting. • Accounting-Response Sent by a RADIUS server requesting more information in order to protect the network from the user and...
User Guide
Page 203
WEP Encryption WEP encryption scrambles the data transmitted between the wireless stations and the access points to the network: Open System, Shared Key, and Auto. The following figure illustrates the steps involved. P-320W User's Guide PEAP (Protected EAP) Like EAP-TTLS, server-side certificate authentication is used to authenticate wireless stations to keep network...
WEP Encryption WEP encryption scrambles the data transmitted between the wireless stations and the access points to the network: Open System, Shared Key, and Auto. The following figure illustrates the steps involved. P-320W User's Guide PEAP (Protected EAP) Like EAP-TTLS, server-side certificate authentication is used to authenticate wireless stations to keep network...
User Guide
Page 206
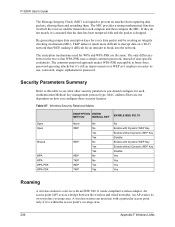
... WPA-PSK uses a simple common password, instead of user-specific credentials. MAC address filters are the same. P-320W User's Guide The Message Integrity Check (MIC) is within the access point's coverage area. 206 Appendix F Wireless LANs By generating unique data encryption keys for every data packet and by ...1X No Enable with Dynamic WEP Key Enable without Dynamic WEP Key Disable Enable with an IEEE 802.11 mode compliant wireless adapter. An access point (AP) acts as it much more difficult to prevent an attacker from capturing data packets, altering them and resending them. An AP...
... WPA-PSK uses a simple common password, instead of user-specific credentials. MAC address filters are the same. P-320W User's Guide The Message Integrity Check (MIC) is within the access point's coverage area. 206 Appendix F Wireless LANs By generating unique data encryption keys for every data packet and by ...1X No Enable with Dynamic WEP Key Enable without Dynamic WEP Key Disable Enable with an IEEE 802.11 mode compliant wireless adapter. An access point (AP) acts as it much more difficult to prevent an attacker from capturing data packets, altering them and resending them. An AP...
User Guide
Page 207
... Y moves from a coverage area to the other . P-320W User's Guide In a network environment with other factors. If the roaming feature is not enabled on the LAN. Appendix F Wireless LANs 207 When a wireless station moves from the coverage area of access point P1 to that of access point 2 P2, it is then propagated to another as...
... Y moves from a coverage area to the other . P-320W User's Guide In a network environment with other factors. If the roaming feature is not enabled on the LAN. Appendix F Wireless LANs 207 When a wireless station moves from the coverage area of access point P1 to that of access point 2 P2, it is then propagated to another as...
User Guide
Page 208
P-320W User's Guide Requirements for Roaming The following requirements must be met in order for wireless stations to roam between the coverage areas. 1 All the access points must be on the same subnet and configured with the same ESSID. 2 If IEEE 802.1x user authentication...done locally on the access point, the new access point must have the user profile for the wireless station. 3 The adjacent access points should use different radio channels when their coverage areas overlap. 4 All access points must use the same port number to relay roaming information. 5 The access points must be connected ...
P-320W User's Guide Requirements for Roaming The following requirements must be met in order for wireless stations to roam between the coverage areas. 1 All the access points must be on the same subnet and configured with the same ESSID. 2 If IEEE 802.1x user authentication...done locally on the access point, the new access point must have the user profile for the wireless station. 3 The adjacent access points should use different radio channels when their coverage areas overlap. 4 All access points must use the same port number to relay roaming information. 5 The access points must be connected ...
User Guide
Page 210
...directional antennas mounted on a table, desk, and so on a wall or ceiling, point the antenna down. P-320W User's Guide Types of Antennas For WLAN There are ideal for hallways and outdoor point-to-point applications. The directional antennas are two types of antennas used for wireless LAN applications.... be mounted as high as practically possible and free of the coverage area as close to make circular overlapping coverage areas with multiple access points. • Directional antennas concentrate the RF signal in a direct line of the coverage pattern; For a single AP application, place...
...directional antennas mounted on a table, desk, and so on a wall or ceiling, point the antenna down. P-320W User's Guide Types of Antennas For WLAN There are ideal for hallways and outdoor point-to-point applications. The directional antennas are two types of antennas used for wireless LAN applications.... be mounted as high as practically possible and free of the coverage area as close to make circular overlapping coverage areas with multiple access points. • Directional antennas concentrate the RF signal in a direct line of the coverage pattern; For a single AP application, place...
User Guide
Page 211
... Notation 167 American Wire Gauge 6 Antenna Directional 210 Omni-directional 210 Antenna gain 209 AP (access point) 197 Authentication 203 Authority 4 AWG 6 B Backup 147 Basement 6 Basic wireless security 49 BSS 195 C CA 202 Cables, Connecting 6 Certificate Authority 202 P-320W User's Guide Index Certifications 5 Changes or Modifications 4 Channel 197 Interference 197 Channel ID 64...
... Notation 167 American Wire Gauge 6 Antenna Directional 210 Omni-directional 210 Antenna gain 209 AP (access point) 197 Authentication 203 Authority 4 AWG 6 B Backup 147 Basement 6 Basic wireless security 49 BSS 195 C CA 202 Cables, Connecting 6 Certificate Authority 202 P-320W User's Guide Index Certifications 5 Changes or Modifications 4 Channel 197 Interference 197 Channel ID 64...