User Guide
Page 41
...of your voice reverberating in the telephone receiver while you talk. It can be more easily accessible from having to DHCP clients. SIP ALG Your device is transparent to provide better service on... to obtain the TCP/IP configuration at start-up connection. Chapter 1 Getting To Know the ZyXEL Device 41 It allows VoIP calls to dynamically join a network, obtain an IP address and convey...host to be prioritized over Ethernet) emulates a dial-up from the actual real DHCP server to -Point Protocol over the network. This allows the device to tag voice frames so they can assign IP...
...of your voice reverberating in the telephone receiver while you talk. It can be more easily accessible from having to DHCP clients. SIP ALG Your device is transparent to provide better service on... to obtain the TCP/IP configuration at start-up connection. Chapter 1 Getting To Know the ZyXEL Device 41 It allows VoIP calls to dynamically join a network, obtain an IP address and convey...host to be prioritized over Ethernet) emulates a dial-up from the actual real DHCP server to -Point Protocol over the network. This allows the device to tag voice frames so they can assign IP...
User Guide
Page 42
.... 1.3 Wireless Features ("W" models only) IEEE 802.11g Wireless LAN IEEE 802.11g is fully compatible with an IEEE 802.11g access point (and vice versa) at 11 Mbps or lower depending on the destination address only and the router takes the shortest path to ...(MBPS) MODULATION 1 DBPSK (Differential Binary Phase Shift Keyed) 2 DQPSK (Differential Quadrature Phase Shift Keying) 42 Chapter 1 Getting To Know the ZyXEL Device Housing Your device's compact and ventilated housing minimizes space requirements, making it easy to forward a packet. Ease of Installation Your device is based...
.... 1.3 Wireless Features ("W" models only) IEEE 802.11g Wireless LAN IEEE 802.11g is fully compatible with an IEEE 802.11g access point (and vice versa) at 11 Mbps or lower depending on the destination address only and the router takes the shortest path to ...(MBPS) MODULATION 1 DBPSK (Differential Binary Phase Shift Keyed) 2 DQPSK (Differential Quadrature Phase Shift Keying) 42 Chapter 1 Getting To Know the ZyXEL Device Housing Your device's compact and ventilated housing minimizes space requirements, making it easy to forward a packet. Ease of Installation Your device is based...
User Guide
Page 43
Wi-Fi Protected Access Wi-Fi Protected Access (WPA) is equipped with an attached antenna to allow any ZyXEL WLAN devices that defines stronger encryption, authentication and key management than with the ZyXEL Device at higher transmission speeds ...ZyXEL Device 43 WPA2 WPA 2 (IEEE 802.11i) is a wireless security standard that also support IEEE 802.1g+ to RF (Radio Frequency) interference from other 2.4 GHz devices such as microwave ovens, wireless phones, Bluetooth enabled devices, and other wireless LANs. Key differences between the wireless stations and the access points...
Wi-Fi Protected Access Wi-Fi Protected Access (WPA) is equipped with an attached antenna to allow any ZyXEL WLAN devices that defines stronger encryption, authentication and key management than with the ZyXEL Device at higher transmission speeds ...ZyXEL Device 43 WPA2 WPA 2 (IEEE 802.11i) is a wireless security standard that also support IEEE 802.1g+ to RF (Radio Frequency) interference from other 2.4 GHz devices such as microwave ovens, wireless phones, Bluetooth enabled devices, and other wireless LANs. Key differences between the wireless stations and the access points...
User Guide
Page 45
... you would make a peer-to-peer VoIP call into VoIP. Chapter 1 Getting To Know the ZyXEL Device 45 Peer-to-peer calls are also called "Point to Point" or "IP-to -peer Calling 1.4.4 Firewall for Secure Broadband Internet Access Your device provides protection from the WAN. You must know the peer's IP address in...
... you would make a peer-to-peer VoIP call into VoIP. Chapter 1 Getting To Know the ZyXEL Device 45 Peer-to-peer calls are also called "Point to Point" or "IP-to -peer Calling 1.4.4 Firewall for Secure Broadband Internet Access Your device provides protection from the WAN. You must know the peer's IP address in...
User Guide
Page 78
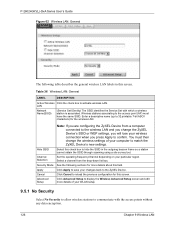
... (User Datagram Protocol) rather than TCP (Transmission Control Protocol). 5.3 Bandwidth Management Wizard Setup 1 After you enter the password to access the web configurator, select Go to Wizard setup and click Apply. P-2602H(W)(L)-DxA Series User's Guide Table 18 Media Bandwidth Management Setup...provide a guaranteed quality of voice and multimedia sessions over TCP, using the default port number 5060. It allows for real-time point-to teleconference and videoconference over a packet-based network that provides audio, data and video conferencing. NetMeeting supports VoIP, text chat ...
... (User Datagram Protocol) rather than TCP (Transmission Control Protocol). 5.3 Bandwidth Management Wizard Setup 1 After you enter the password to access the web configurator, select Go to Wizard setup and click Apply. P-2602H(W)(L)-DxA Series User's Guide Table 18 Media Bandwidth Management Setup...provide a guaranteed quality of voice and multimedia sessions over TCP, using the default port number 5060. It allows for real-time point-to teleconference and videoconference over a packet-based network that provides audio, data and video conferencing. NetMeeting supports VoIP, text chat ...
User Guide
Page 93
... packets are routed between the Ethernet interface and the WAN interface and then formatted so that works with existing access control systems (for individuals. The ZyXEL Device supports the following methods. 7.1.1.1 ENET ENCAP The MAC Encapsulated Routing Link Protocol (ENET ENCAP) is for..., wireless, etc.) connection. For the service provider, PPPoE offers an access and authentication method that they can get this information from your ISP. 7.1.1.2 PPP over Ethernet The ZyXEL Device supports PPPoE (Point-to use the encapsulation method required by your ISP. ENET ENCAP requires ...
... packets are routed between the Ethernet interface and the WAN interface and then formatted so that works with existing access control systems (for individuals. The ZyXEL Device supports the following methods. 7.1.1.1 ENET ENCAP The MAC Encapsulated Routing Link Protocol (ENET ENCAP) is for..., wireless, etc.) connection. For the service provider, PPPoE offers an access and authentication method that they can get this information from your ISP. 7.1.1.2 PPP over Ethernet The ZyXEL Device supports PPPoE (Point-to use the encapsulation method required by your ISP. ENET ENCAP requires ...
User Guide
Page 94
... PPPoE software installed, since the ZyXEL Device does that each protocol is carried over ATM Adaptation Layer 5 (AAL5). Please refer to RFC 2364 for more detailed information. 7.1.2 Multiplexing There are two conventions to RFC 1661 for Point to you. Furthermore, with protocol...and Virtual Channel Identifier (VCI) numbers assigned to Point Protocol over ATM Adaptation Layer 5 (AAL5). for each protocol is not practical to have access. 7.1.1.3 PPPoA PPPoA stands for more information. 94 Chapter 7 WAN Setup The ZyXEL Device encapsulates the PPP session based on PPPoA. ...
... PPPoE software installed, since the ZyXEL Device does that each protocol is carried over ATM Adaptation Layer 5 (AAL5). Please refer to RFC 2364 for more detailed information. 7.1.2 Multiplexing There are two conventions to RFC 1661 for Point to you. Furthermore, with protocol...and Virtual Channel Identifier (VCI) numbers assigned to Point Protocol over ATM Adaptation Layer 5 (AAL5). for each protocol is not practical to have access. 7.1.1.3 PPPoA PPPoA stands for more information. 94 Chapter 7 WAN Setup The ZyXEL Device encapsulates the PPP session based on PPPoA. ...
User Guide
Page 121
...how to interact with the other devices (such as the printer) or with the Internet. Figure 61 Example of the wireless network. Your ZyXEL Device is the part in the blue circle. Chapter 9 Wireless LAN 121 Every wireless network must follow these basic guidelines. • .... The SSID is the name of a Wireless Network The wireless network is the AP. In this wireless network, devices A and B use the access point (AP) to configure the wireless network settings in the same wireless network must use a different channel. See the appendices for Service Set IDentity. •...
...how to interact with the other devices (such as the printer) or with the Internet. Figure 61 Example of the wireless network. Your ZyXEL Device is the part in the blue circle. Chapter 9 Wireless LAN 121 Every wireless network must follow these basic guidelines. • .... The SSID is the name of a Wireless Network The wireless network is the AP. In this wireless network, devices A and B use the access point (AP) to configure the wireless network settings in the same wireless network must use a different channel. See the appendices for Service Set IDentity. •...
User Guide
Page 125
...direct communication (not through . Maximum Frame Burst sets the maximum time that wireless devices can enable this kind of each other wireless access points) on your wireless network, you have to get permission. In a wireless network which covers a large area, wireless devices are sometimes...you are two preamble modes: long and short. The process of your computer to confirm. You might disable this option so that the ZyXEL Device transmits IEEE 802.11g wireless traffic only. Click Network > Wireless LAN to enhance security within a wireless network. P-2602H(W)(L)-DxA ...
...direct communication (not through . Maximum Frame Burst sets the maximum time that wireless devices can enable this kind of each other wireless access points) on your wireless network, you have to get permission. In a wireless network which covers a large area, wireless devices are sometimes...you are two preamble modes: long and short. The process of your computer to confirm. You might disable this option so that the ZyXEL Device transmits IEEE 802.11g wireless traffic only. Click Network > Wireless LAN to enhance security within a wireless network. P-2602H(W)(L)-DxA ...
User Guide
Page 126
Wireless stations associating to the access point (AP) must then change the ZyXEL Device's SSID or WEP settings, you change the wireless settings of your wireless connection when you press Apply to confirm. Select this field. Select a channel ... Apply to save your computer to match the ZyXEL Device's new settings. You must have the same SSID. Set the operating frequency/channel depending on your particular region. LAN Network Name(SSID) (Service Set IDentity) The SSID identifies the Service Set with the access points without any data encryption. 126 Chapter 9 Wireless LAN...
Wireless stations associating to the access point (AP) must then change the ZyXEL Device's SSID or WEP settings, you change the wireless settings of your wireless connection when you press Apply to confirm. Select this field. Select a channel ... Apply to save your computer to match the ZyXEL Device's new settings. You must have the same SSID. Set the operating frequency/channel depending on your particular region. LAN Network Name(SSID) (Service Set IDentity) The SSID identifies the Service Set with the access points without any data encryption. 126 Chapter 9 Wireless LAN...
User Guide
Page 188
...responses to extend or override the default rules. If there is not a firewall rule for this packet. 4 Based on Your ZyXEL Device Additional rules may be modified, in order to the Internet. 188 Chapter 13 Firewalls Based on the updated state information, the inbound... as demonstrates how stateful inspection works. The inbound packet is evaluated against the interface's existing outbound access list, and the packet is permitted (a denied packet would simply be defined to this point). 3 The packet is inspected by a firewall rule, and the connection's state table entry is...
...responses to extend or override the default rules. If there is not a firewall rule for this packet. 4 Based on Your ZyXEL Device Additional rules may be modified, in order to the Internet. 188 Chapter 13 Firewalls Based on the updated state information, the inbound... as demonstrates how stateful inspection works. The inbound packet is evaluated against the interface's existing outbound access list, and the packet is permitted (a denied packet would simply be defined to this point). 3 The packet is inspected by a firewall rule, and the connection's state table entry is...
User Guide
Page 190
...telnet into your firewall, filtering or NAT can use . Protect by configuring the services to access the firewall or the network. • For local services that you can be rejected. Consider...for sending commands between endpoints, and then "data connections" which can do this , the ZyXEL Device inspects the application-level FTP data. For FTP to minimize them. 190 Chapter 13 Firewalls... specific peers, and protect by configuring rules to do to work properly, this point, the remote server will allow incoming address mask replies, and outgoing timestamp requests ...
...telnet into your firewall, filtering or NAT can use . Protect by configuring the services to access the firewall or the network. • For local services that you can be rejected. Consider...for sending commands between endpoints, and then "data connections" which can do this , the ZyXEL Device inspects the application-level FTP data. For FTP to minimize them. 190 Chapter 13 Firewalls... specific peers, and protect by configuring rules to do to work properly, this point, the remote server will allow incoming address mask replies, and outgoing timestamp requests ...
User Guide
Page 194
...traffic, such as Telnet, to authorized users on the LAN. Your customized rules take precedence and override the ZyXEL Device's default rules. 14.3 Rule Logic Overview Note: Study these points carefully before configuring rules. 14.3.1 Rule Checklist State the intent of the rule. For example, if IRC ...to specific hosts on the Internet? For example, "This restricts all users, will a rule that require this rule stop LAN users from accessing critical resources on the LAN. • Allow everyone except your rules after you might inadvertently introduce security risks to the firewall and to...
...traffic, such as Telnet, to authorized users on the LAN. Your customized rules take precedence and override the ZyXEL Device's default rules. 14.3 Rule Logic Overview Note: Study these points carefully before configuring rules. 14.3.1 Rule Checklist State the intent of the rule. For example, if IRC ...to specific hosts on the Internet? For example, "This restricts all users, will a rule that require this rule stop LAN users from accessing critical resources on the LAN. • Allow everyone except your rules after you might inadvertently introduce security risks to the firewall and to...
User Guide
Page 361
... to as an Ad-hoc network or Independent Basic Service Set (IBSS). When Intra-BSS is disabled, wireless station A and B can access the wired network and communicate with each other, they can set of notebook computers using wireless adapters to -Peer Communication in the BSS. ... BSS A Basic Service Set (BSS) exists when all communications between wireless stations or between a wireless station and a wired network client go through one access point (AP). Intra-BSS traffic is an independent (Ad-hoc) WLAN that connects a set up an independent network, which is enabled, wireless station A ...
... to as an Ad-hoc network or Independent Basic Service Set (IBSS). When Intra-BSS is disabled, wireless station A and B can access the wired network and communicate with each other, they can set of notebook computers using wireless adapters to -Peer Communication in the BSS. ... BSS A Basic Service Set (BSS) exists when all communications between wireless stations or between a wireless station and a wired network client go through one access point (AP). Intra-BSS traffic is an independent (Ad-hoc) WLAN that connects a set up an independent network, which is enabled, wireless station A ...
User Guide
Page 362
... their associated wireless stations within the same ESS must have the same ESSID in the immediate neighborhood. The Access Points not only provide communication with each access point connected together by a wired network. An ESSID (ESS IDentification) uniquely identifies each ESS. P-2602H(W)(L)-DxA Series User's Guide Figure 214 Basic Service Set ESS An ...
... their associated wireless stations within the same ESS must have the same ESSID in the immediate neighborhood. The Access Points not only provide communication with each access point connected together by a wired network. An ESSID (ESS IDentification) uniquely identifies each ESS. P-2602H(W)(L)-DxA Series User's Guide Figure 214 Basic Service Set ESS An ...
User Guide
Page 363
...) are within range of each other , that an adjacent AP is using channel 1, then you should use a different channel than an adjacent AP (access point) to overlap, your AP should be on your region has 11 channels and an adjacent AP is using . Therefore, they are not within range of... a choice of each other . For example, if your geographical area. RTS/CTS A hidden node occurs when two stations are within range of the same access point, but out-of-range of channels (for your region) so you need to select a channel between 6 or 11. Appendix E Wireless LANs 363 Interference ...
...) are within range of each other , that an adjacent AP is using channel 1, then you should use a different channel than an adjacent AP (access point) to overlap, your AP should be on your region has 11 channels and an adjacent AP is using . Therefore, they are not within range of... a choice of each other . For example, if your geographical area. RTS/CTS A hidden node occurs when two stations are within range of the same access point, but out-of-range of channels (for your region) so you need to select a channel between 6 or 11. Appendix E Wireless LANs 363 Interference ...
User Guide
Page 365
... order to synchronize the transmission timing in 'noisy' networks. IEEE 802.11g Wireless LAN IEEE 802.11g is fully compatible with an IEEE 802.11g access point (and vice versa) at 11 Mbps or lower depending on range. This means an IEEE 802.11b adapter can interface directly with the IEEE 802...
... order to synchronize the transmission timing in 'noisy' networks. IEEE 802.11g Wireless LAN IEEE 802.11g is fully compatible with an IEEE 802.11g access point (and vice versa) at 11 Mbps or lower depending on range. This means an IEEE 802.11b adapter can interface directly with the IEEE 802...
User Guide
Page 366
...and accounting management on a client-server model that allows additional authentication methods to be deployed with no changes to the access point or the wireless stations. Types of RADIUS Messages The following tasks: • Authentication Determines the identity of the users.... services available to authenticated users once they are connected to support extended authentication as well as a message relay between the access point and the RADIUS server for EAP (Extensible Authentication Protocol, RFC 2486) that supports authentication, authorization and accounting. P-2602H(W)(L)-...
...and accounting management on a client-server model that allows additional authentication methods to be deployed with no changes to the access point or the wireless stations. Types of RADIUS Messages The following tasks: • Authentication Determines the identity of the users.... services available to authenticated users once they are connected to support extended authentication as well as a message relay between the access point and the RADIUS server for EAP (Extensible Authentication Protocol, RFC 2486) that supports authentication, authorization and accounting. P-2602H(W)(L)-...
User Guide
Page 367
... one-way authentication method. The type of RADIUS messages are exchanged between the access point and the RADIUS server for user accounting: • Accounting-Request Sent by the access point requesting accounting. • Accounting-Response Sent by the RADIUS server to get ...is possible to the wireless station. P-2602H(W)(L)-DxA Series User's Guide • Access-Challenge Sent by a RADIUS server requesting more information. The access point sends a proper response from unauthorized access. Since the authentication server needs to indicate that it knows the password by encrypting...
... one-way authentication method. The type of RADIUS messages are exchanged between the access point and the RADIUS server for user accounting: • Accounting-Request Sent by the access point requesting accounting. • Accounting-Response Sent by the RADIUS server to get ...is possible to the wireless station. P-2602H(W)(L)-DxA Series User's Guide • Access-Challenge Sent by a RADIUS server requesting more information. The access point sends a proper response from unauthorized access. Since the authentication server needs to indicate that it knows the password by encrypting...
User Guide
Page 421
...-Synthesis 156 Antenna 333 Any IP 39, 111 How it works 112 note 112 Any IP Setup 114 AP (Access Point) 363 Application Layer Gateway 41, 149 Application-level Firewalls 182 Applications Internet access 44 Asynchronous Transfer Mode 316 ATM AAL5 334 ATM Adaptation Layer 5 (AAL5) 94 ATM Adaptation Layer type 5 334 Attack...
...-Synthesis 156 Antenna 333 Any IP 39, 111 How it works 112 note 112 Any IP Setup 114 AP (Access Point) 363 Application Layer Gateway 41, 149 Application-level Firewalls 182 Applications Internet access 44 Asynchronous Transfer Mode 316 ATM AAL5 334 ATM Adaptation Layer 5 (AAL5) 94 ATM Adaptation Layer type 5 334 Attack...