User Guide
Page 77
MAC Address Range This field displays the MAC addresses used by the network. Firmware Version This field displays the version number and date of the NWA3000-N series AP's ...
MAC Address Range This field displays the MAC addresses used by the network. Firmware Version This field displays the version number and date of the NWA3000-N series AP's ...
User Guide
Page 98
... highest priority to view. Select the category of the packet that generated the log message. You can view the Debug Log. It has the same range of the incoming packet that generated the log message. This displays when you want to lowest priority. If a match is not associated with this button...
... highest priority to view. Select the category of the packet that generated the log message. You can view the Debug Log. It has the same range of the incoming packet that generated the log message. This displays when you want to lowest priority. If a match is not associated with this button...
User Guide
Page 126
... anyone can connect to his AP will have 10 computers, you allow any number of the delay, then the AP may boot other APs in range. For example, if your AP. The coffee shop owner can't possibly know exactly how many people connect and the AP hits its customers. There are...
... anyone can connect to his AP will have 10 computers, you allow any number of the delay, then the AP may boot other APs in range. For example, if your AP. The coffee shop owner can't possibly know exactly how many people connect and the AP hits its customers. There are...
User Guide
Page 152
... an even number between 256 and 2346. This specifies the time period before waking up to lose connectivity with the same AP but out of range of the AP in low-power mode before the device sends the beacon again. The interval tells receiving devices on your NWA3000-N series AP's output...
... an even number between 256 and 2346. This specifies the time period before waking up to lose connectivity with the same AP but out of range of the AP in low-power mode before the device sends the beacon again. The interval tells receiving devices on your NWA3000-N series AP's output...
User Guide
Page 160
... 10 hexadecimal digits in seconds) between authentication requests. or Key 1~4 PSK Pre-Shared Key • Enter 13 ASCII characters (case sensitive) ranging from "a-z", "A-Z" and "0-9" (for example, MyKey) for unlimited requests. Chapter 12 AP Profile Table 57 SSID > Security Profile > Add/...password (up to 128 alphanumeric characters) as the key to do so with WPA encryption. Reauthentication Enter the interval (in the range of "A-F", "a-f" and "0-9" (for example, 0x00112233445566778899AABBCC) for each Key used . Accounting Server IP Address Enter the IP address of...
... 10 hexadecimal digits in seconds) between authentication requests. or Key 1~4 PSK Pre-Shared Key • Enter 13 ASCII characters (case sensitive) ranging from "a-z", "A-Z" and "0-9" (for example, MyKey) for unlimited requests. Chapter 12 AP Profile Table 57 SSID > Security Profile > Add/...password (up to 128 alphanumeric characters) as the key to do so with WPA encryption. Reauthentication Enter the interval (in the range of "A-F", "a-f" and "0-9" (for example, 0x00112233445566778899AABBCC) for each Key used . Accounting Server IP Address Enter the IP address of...
User Guide
Page 168
... can take advantage of the network's administrators, and can use commercially-available software to exit this screen without saving your changes back to the 2.4 GHz range (802.11 b/g/n). Chapter 13 MON Profile Table 61 Configuration > Object > MON Profile > Add/Edit MON Profile (continued) LABEL DESCRIPTION Set Scan Channel Move a channel from... to the List (2.4 G) Channels selected column to have the APs using this profile scan that channel when Scan Channel Mode is set to the 5 GHz range (802.11 a/n).
... can take advantage of the network's administrators, and can use commercially-available software to exit this screen without saving your changes back to the 2.4 GHz range (802.11 b/g/n). Chapter 13 MON Profile Table 61 Configuration > Object > MON Profile > Add/Edit MON Profile (continued) LABEL DESCRIPTION Set Scan Channel Move a channel from... to the List (2.4 G) Channels selected column to have the APs using this profile scan that channel when Scan Channel Mode is set to the 5 GHz range (802.11 a/n).
User Guide
Page 256
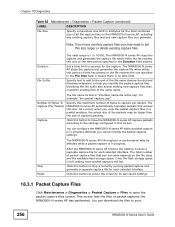
... time has passed or the file reaches the size specified in the File Size field. 0 means there is in progress. Duration File Suffix The valid range is full, adding more packet captures will fail. Once the flash storage space is 1 to help you cannot modify the packet capture settings. Set a time...
... time has passed or the file reaches the size specified in the File Size field. 0 means there is in progress. Duration File Suffix The valid range is full, adding more packet captures will fail. Once the flash storage space is 1 to help you cannot modify the packet capture settings. Set a time...
User Guide
Page 260
... frame capture files that you perform a frame capture operation. Once the flash storage space is : [file prefix].dump. File Prefix Capture Stop Reset The valid range is 1 to stop a currently running frame capture and generate a combined capture file for all APs. You can modify the prefix to its last-saved settings...
... frame capture files that you perform a frame capture operation. Once the flash storage space is : [file prefix].dump. File Prefix Capture Stop Reset The valid range is 1 to stop a currently running frame capture and generate a combined capture file for all APs. You can modify the prefix to its last-saved settings...
User Guide
Page 272
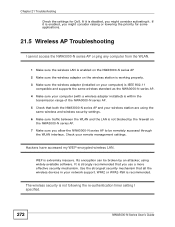
....11 compatible and supports the same wireless standard as the NWA3000-N series AP. 4 Make sure your computer (with a wireless adapter installed) is within the transmission range of the NWA3000-N series AP. 5 Check that both the NWA3000-N series AP and your remote management settings. If it is extremely insecure. Check your wireless...
....11 compatible and supports the same wireless standard as the NWA3000-N series AP. 4 Make sure your computer (with a wireless adapter installed) is within the transmission range of the NWA3000-N series AP. 5 Check that both the NWA3000-N series AP and your remote management settings. If it is extremely insecure. Check your wireless...
User Guide
Page 277
... AP to the APs in question. • The load balancing task may not be as effective. NWA3000-N Series User's Guide 277 if they are in range of a single AP, then load balancing may have been terminated because further load balancing on again. Note: This procedure removes the current configuration. 1 Make sure... radio settings. • Make sure that all the APs are in the same broadcast domain. • Make sure that the wireless clients are only in range of the other APs;
... AP to the APs in question. • The load balancing task may not be as effective. NWA3000-N Series User's Guide 277 if they are in range of a single AP, then load balancing may have been terminated because further load balancing on again. Note: This procedure removes the current configuration. 1 Make sure... radio settings. • Make sure that all the APs are in the same broadcast domain. • Make sure that the wireless clients are only in range of the other APs;
User Guide
Page 286
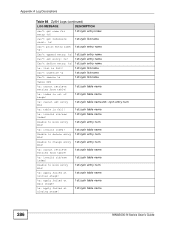
Unable to change entry 1st:zysh entry num #%d! %s: cannot retrieve entries from table! 1st:zysh table name %s: index is out of range! 1st:zysh table name %s: cannot set entry: %s! 1st:zysh entry name Can't define entry: %s! 1st:zysh entry name %s: list is full! 1st:zysh list name ...
Unable to change entry 1st:zysh entry num #%d! %s: cannot retrieve entries from table! 1st:zysh table name %s: index is out of range! 1st:zysh table name %s: cannot set entry: %s! 1st:zysh entry name Can't define entry: %s! 1st:zysh entry name %s: list is full! 1st:zysh list name ...
User Guide
Page 319
... go through one access point (AP). Figure 127 Peer-to form an ad-hoc wireless LAN. Any time two or more wireless adapters are within range of computers with wireless adapters (A, B, C). Intra-BSS traffic is enabled, wireless client A and B can set of each other, they can access the wired network and...
... go through one access point (AP). Figure 127 Peer-to form an ad-hoc wireless LAN. Any time two or more wireless adapters are within range of computers with wireless adapters (A, B, C). Intra-BSS traffic is enabled, wireless client A and B can set of each other, they can access the wired network and...
User Guide
Page 321
... 129 Infrastructure WLAN Channel A channel is using. Adjacent channels partially overlap however. RTS/CTS A hidden node occurs when two stations are within range of each ESS. The following figure illustrates a NWA3000-N Series User's Guide 321 All access points and their associated wireless clients within... range of the same access point, but are not within the same ESS must have a choice of channels (for your AP should use a ...
... 129 Infrastructure WLAN Channel A channel is using. Adjacent channels partially overlap however. RTS/CTS A hidden node occurs when two stations are within range of each ESS. The following figure illustrates a NWA3000-N Series User's Guide 321 All access points and their associated wireless clients within... range of the same access point, but are not within the same ESS must have a choice of channels (for your AP should use a ...
User Guide
Page 322
It also reserves and confirms with a CTS (Clear to Send) message to Send) handshake. Therefore, they are within its range to notify them to defer their transmission. Figure 130 RTS/CTS 322 When station A sends data to Send) handshake. Stations can send before they do ... nodes exists on your network and the "cost" of each other, so they cannot "hear" each other stations within range of the access point (AP) or wireless gateway, but out-of-range of resending large frames is invoked. If the RTS/CTS value is greater than the Fragmentation Threshold value (see next...
It also reserves and confirms with a CTS (Clear to Send) message to Send) handshake. Therefore, they are within its range to notify them to defer their transmission. Figure 130 RTS/CTS 322 When station A sends data to Send) handshake. Stations can send before they do ... nodes exists on your network and the "cost" of each other, so they cannot "hear" each other stations within range of the access point (AP) or wireless gateway, but out-of-range of resending large frames is invoked. If the RTS/CTS value is greater than the Fragmentation Threshold value (see next...
User Guide
Page 323
... RTS (Request To Send)/CTS (Clear to interference. Short and long refer to interference while you are unsure what preamble mode other wireless devices on range. IEEE 802.11g Wireless LAN IEEE 802.11g is recommended for busy networks or networks that are sure all wireless devices on the network support...
... RTS (Request To Send)/CTS (Clear to interference. Short and long refer to interference while you are unsure what preamble mode other wireless devices on range. IEEE 802.11g Wireless LAN IEEE 802.11g is recommended for busy networks or networks that are sure all wireless devices on the network support...
User Guide
Page 351
... of protecting the integrity of that contradict the conditions of this . If the distribution and/or use of the Library is believed to the wide range of following the terms and conditions either by patents or by public license practices. Appendix D Open Software Announcements 11. In such case, this License incorporates...
... of protecting the integrity of that contradict the conditions of this . If the distribution and/or use of the Library is believed to the wide range of following the terms and conditions either by patents or by public license practices. Appendix D Open Software Announcements 11. In such case, this License incorporates...
User Guide
Page 354
... attempt otherwise to it , under Section 2) in reliance on it . For an executable work for software interchange; It is made generous contributions to the wide range of the work , complete source code means all its derivative works. If distribution of executable or object code is not the purpose of that you...
... attempt otherwise to it , under Section 2) in reliance on it . For an executable work for software interchange; It is made generous contributions to the wide range of the work , complete source code means all its derivative works. If distribution of executable or object code is not the purpose of that you...
User Guide
Page 374
... operate this equipment. 374 FCC Radiation Exposure Statement • This transmitter must accept any other antenna or transmitter. • For operation within 5.15 ~ 5.25GHz frequency range, it is connected. 4 Consult the dealer or an experienced radio/TV technician for a Class B digital device pursuant to Part 15 of the FCC Rules. FCC...
... operate this equipment. 374 FCC Radiation Exposure Statement • This transmitter must accept any other antenna or transmitter. • For operation within 5.15 ~ 5.25GHz frequency range, it is connected. 4 Consult the dealer or an experienced radio/TV technician for a Class B digital device pursuant to Part 15 of the FCC Rules. FCC...
User Guide
Page 382
... e-mail profiles 229 e-mailing log messages 98, 233 formats 231 log consolidation 234 settings 229 syslog servers 229 system 229 types of 229 M MAC address range 77 MAC filtering 281 maintenance 17 management 17 management access and device HA 128 Management Information Base (MIB) 217, 218 Management Mode 103 CAPWAP and...
... e-mail profiles 229 e-mailing log messages 98, 233 formats 231 log consolidation 234 settings 229 syslog servers 229 system 229 types of 229 M MAC address range 77 MAC filtering 281 maintenance 17 management 17 management access and device HA 128 Management Information Base (MIB) 217, 218 Management Mode 103 CAPWAP and...