User Guide
Page 5
Document Conventions Graphics in this manual is accurate. WiMAX Device Computer Notebook computer Server Base Station Firewall Router Internet Switch Wireless Signal Telephone WiMAX Device Configuration User's Guide 5 Every effort has been made to differences in this book may differ slightly from the product due to ensure that the information in operating systems, operating system versions, or if you installed updated firmware/software for your device.
Document Conventions Graphics in this manual is accurate. WiMAX Device Computer Notebook computer Server Base Station Firewall Router Internet Switch Wireless Signal Telephone WiMAX Device Configuration User's Guide 5 Every effort has been made to differences in this book may differ slightly from the product due to ensure that the information in operating systems, operating system versions, or if you installed updated firmware/software for your device.
User Guide
Page 46
This tutorial shows how to separate two department networks. The router may connect a router to access the WiMAX Device from the Internet. You can then log into the WiMAX Device and manage it. 4.9 Configuring Static Route for two network ...
This tutorial shows how to separate two department networks. The router may connect a router to access the WiMAX Device from the Internet. You can then log into the WiMAX Device and manage it. 4.9 Configuring Static Route for two network ...
User Guide
Page 47
...'s WAN 172.16.1.1 The WiMAX Device's LAN 192.168.1.1 A 192.168.1.34 R's IP address on the WiMAX Device to specify R as the router in N2 network), the traffic is connected to the WiMAX Device's LAN. Chapter 4 Tutorials In the following example IP settings: Table 10 IP Settings ...to specify a static routing rule on N1 192.168.1.253 WiMAX Device Configuration User's Guide 47 N1 A R N2 B This tutorial uses the following figure, router R is sent to computer B. If you want to send traffic from computer A to R and then R routes the traffic to the WiMAX Device's WAN ...
...'s WAN 172.16.1.1 The WiMAX Device's LAN 192.168.1.1 A 192.168.1.34 R's IP address on the WiMAX Device to specify R as the router in N2 network), the traffic is connected to the WiMAX Device's LAN. Chapter 4 Tutorials In the following example IP settings: Table 10 IP Settings ...to specify a static routing rule on N1 192.168.1.253 WiMAX Device Configuration User's Guide 47 N1 A R N2 B This tutorial uses the following figure, router R is sent to computer B. If you want to send traffic from computer A to R and then R routes the traffic to the WiMAX Device's WAN ...
User Guide
Page 53
... Note: Manager IP VLAN ID is the same as one of the LAN transparent VLAN ID VLAN Tag ID=5 VLAN Tag ID=10 Network operators Router Manager IP VLAN Tag ID=5 1 Configure the Link Type, PVID and Tag/Untag settings for the interfaces as below by clicking each row. WiMAX Device...
... Note: Manager IP VLAN ID is the same as one of the LAN transparent VLAN ID VLAN Tag ID=5 VLAN Tag ID=10 Network operators Router Manager IP VLAN Tag ID=5 1 Configure the Link Type, PVID and Tag/Untag settings for the interfaces as below by clicking each row. WiMAX Device...
User Guide
Page 55
... LAN transparent VLAN ID User Network VLAN Tag ID=5 Transparent VLAN Tag ID=10 LAN CPE VLAN Tag ID=5 VLAN Tag ID=10 Network operators Router Manager IP VLAN Tag ID=3 VLAN Tag ID=3 1 Configure the Link Type, PVID and Tag/Untag settings for the interfaces as below by clicking each...
... LAN transparent VLAN ID User Network VLAN Tag ID=5 Transparent VLAN Tag ID=10 LAN CPE VLAN Tag ID=5 VLAN Tag ID=10 Network operators Router Manager IP VLAN Tag ID=3 VLAN Tag ID=3 1 Configure the Link Type, PVID and Tag/Untag settings for the interfaces as below by clicking each...
User Guide
Page 91
... address, subnet mask, DNS and other routing information when it . IP Address IP addresses identify individual devices on a network. Every networking device (including computers, servers, routers, printers, etc.) needs an IP address to divide one network into multiple sub-networks. DNS Server Address DNS (Domain Name System) is up . otherwise, leave...
... address, subnet mask, DNS and other routing information when it . IP Address IP addresses identify individual devices on a network. Every networking device (including computers, servers, routers, printers, etc.) needs an IP address to divide one network into multiple sub-networks. DNS Server Address DNS (Domain Name System) is up . otherwise, leave...
User Guide
Page 92
...WiMAX Device forwards the query to the real DNS server learned through IPCP and relays the response back to exchange routing information with other routers. This way, the WiMAX Device can pass the DNS servers to the computers and the computers can forward incoming service requests to ...WiMAX Device tells the DHCP clients that RIP-2B uses subnet broadcasting while RIP-2M uses multicasting. RIP Setup RIP (Routing Information Protocol) allows a router to the computer. the difference being that it receives. • RX Only - Please note that it itself is forwarded to one service (for...
...WiMAX Device forwards the query to the real DNS server learned through IPCP and relays the response back to exchange routing information with other routers. This way, the WiMAX Device can pass the DNS servers to the computers and the computers can forward incoming service requests to ...WiMAX Device tells the DHCP clients that RIP-2B uses subnet broadcasting while RIP-2M uses multicasting. RIP Setup RIP (Routing Information Protocol) allows a router to the computer. the difference being that it receives. • RX Only - Please note that it itself is forwarded to one service (for...
User Guide
Page 93
... replace the LAN computer's IP address in the data stream. The NAT network appears as SIP, H.323 or FTP) at the application layer. Some NAT routers may include a SIP Application Layer Gateway (ALG). An Application Layer Gateway (ALG) manages a specific protocol (such as a single host on the LAN can use the...
... replace the LAN computer's IP address in the data stream. The NAT network appears as SIP, H.323 or FTP) at the application layer. Some NAT routers may include a SIP Application Layer Gateway (ALG). An Application Layer Gateway (ALG) manages a specific protocol (such as a single host on the LAN can use the...
User Guide
Page 95
...User's Guide 95 Click Network Setting > WAN to open this to manually enter the IP address the WiMAX Device uses. • From ISP - Select Router from the ISP. Select this if you need to tunnel Ethernet and IEEE 802.3 MAC frames across an IP Internet. WAN Protocol • Bridge - Select...; GRE Tunnel - Select this if you want multiple computers to use their own internal IP addresses while communicating with devices on the WAN. • Router - This allows the WiMAX Device to tag frames for NAT, allowing devices on the LAN to share an Internet account. • NAT -
...User's Guide 95 Click Network Setting > WAN to open this to manually enter the IP address the WiMAX Device uses. • From ISP - Select Router from the ISP. Select this if you need to tunnel Ethernet and IEEE 802.3 MAC frames across an IP Internet. WAN Protocol • Bridge - Select...; GRE Tunnel - Select this if you want multiple computers to use their own internal IP addresses while communicating with devices on the WAN. • Router - This allows the WiMAX Device to tag frames for NAT, allowing devices on the LAN to share an Internet account. • NAT -
User Guide
Page 105
... shown next. Chapter 7 Network Setting Click Add in the Network Setting > Route > Static Route screen to configure how the WiMAX Device exchanges information with other routers. Figure 53 Static Route Screen This screen contains the following fields: Table 36 Static Route LABEL Destination IP Subnet Mask Next Hop DESCRIPTION Enter the...
... shown next. Chapter 7 Network Setting Click Add in the Network Setting > Route > Static Route screen to configure how the WiMAX Device exchanges information with other routers. Figure 53 Static Route Screen This screen contains the following fields: Table 36 Static Route LABEL Destination IP Subnet Mask Next Hop DESCRIPTION Enter the...
User Guide
Page 132
.... MPPE with 40 bit session key length. • MPPE 128 - This can increase performance over stateless MPPE, but should not be located behind a NAT enabled router. Password Enter the password for connecting to -Point Encryption (MPPE). Options are : • MPPE 40 - It provides improved usability with PPTP at the same time...
.... MPPE with 40 bit session key length. • MPPE 128 - This can increase performance over stateless MPPE, but should not be located behind a NAT enabled router. Password Enter the password for connecting to -Point Encryption (MPPE). Options are : • MPPE 40 - It provides improved usability with PPTP at the same time...
User Guide
Page 136
... to the L2TP server. 136 WiMAX Device Configuration User's Guide It provides additional security over stateless MPPE, but should not be located behind a NAT enabled router. Options are : MPPE Encryption • PAP - MPPE with Microsoft products. • MSCHAPv2 - Server IP Address Enter the IP address of networks including frame relay and...
... to the L2TP server. 136 WiMAX Device Configuration User's Guide It provides additional security over stateless MPPE, but should not be located behind a NAT enabled router. Options are : MPPE Encryption • PAP - MPPE with Microsoft products. • MSCHAPv2 - Server IP Address Enter the IP address of networks including frame relay and...
User Guide
Page 137
...Enabled This displays if the VPN policy is the VPN policy index number. Local Endpoint This displays the IP address of the remote IPSec router. Local Network This displays the single (static) IP address on the L2TP server. Ensure that the IP address is configured to timeout ... The following fields: Table 59 IPSec VPN LABEL DESCRIPTION # This is enabled. Figure 77 IPSec Fields Summary Local Network Remote Network Remote IPSec Router Local IP Address VPN Tunnel Remote IP Address Click Security > IPSec VPN to the L2TP server. Chapter 8 Security Table 58 L2TP Client: ...
...Enabled This displays if the VPN policy is the VPN policy index number. Local Endpoint This displays the IP address of the remote IPSec router. Local Network This displays the single (static) IP address on the L2TP server. Ensure that the IP address is configured to timeout ... The following fields: Table 59 IPSec VPN LABEL DESCRIPTION # This is enabled. Figure 77 IPSec Fields Summary Local Network Remote Network Remote IPSec Router Local IP Address VPN Tunnel Remote IP Address Click Security > IPSec VPN to the L2TP server. Chapter 8 Security Table 58 L2TP Client: ...
User Guide
Page 138
Add Click this button to add an item to the list. 138 WiMAX Device Configuration User's Guide Chapter 8 Security Table 59 IPSec VPN (continued) LABEL DESCRIPTION Remote Network This displays the single (static) IP address on the LAN behind the remote IPSec router or the IP address and subnet mask of a network behind the remote IPSec router.
Add Click this button to add an item to the list. 138 WiMAX Device Configuration User's Guide Chapter 8 Security Table 59 IPSec VPN (continued) LABEL DESCRIPTION Remote Network This displays the single (static) IP address on the LAN behind the remote IPSec router or the IP address and subnet mask of a network behind the remote IPSec router.
User Guide
Page 140
.... Choose this field. Use up to 31 ASCII characters including spaces, although trailing spaces are also known as part of the remote IPSec router in users. Chapter 8 Security This screen contains the following situations. • When there is not counted as dial-in the IKE SA.... Choose this WiMAX Device in the Content field. Select Domain Name to identify this WiMAX Device by which is a NAT router between VPN connection requests that come in "0x0123456789ABCDEF", "0x" denotes that best describes your pre-shared key in this to allow incoming ...
.... Choose this field. Use up to 31 ASCII characters including spaces, although trailing spaces are also known as part of the remote IPSec router in users. Chapter 8 Security This screen contains the following situations. • When there is not counted as dial-in the IKE SA.... Choose this WiMAX Device in the Content field. Select Domain Name to identify this WiMAX Device by which is a NAT router between VPN connection requests that come in "0x0123456789ABCDEF", "0x" denotes that best describes your pre-shared key in this to allow incoming ...
User Guide
Page 141
...algorithm • AES192 - Key Group Select which Diffie-Hellman key group (DHx) you want the WiMAX Device to identify the remote IPSec router. Content Select E-mail to 31 ASCII characters including spaces, although trailing spaces are : • DH1 - The configuration of proposals should not... affect performance significantly. Use up to identify the remote IPSec router by which you configure this to use for identification purposes only and can be any string. The sequence of the remote content depends...
...algorithm • AES192 - Key Group Select which Diffie-Hellman key group (DHx) you want the WiMAX Device to identify the remote IPSec router. Content Select E-mail to 31 ASCII characters including spaces, although trailing spaces are : • DH1 - The configuration of proposals should not... affect performance significantly. Use up to identify the remote IPSec router by which you configure this to use for identification purposes only and can be any string. The sequence of the remote content depends...
User Guide
Page 142
... addresses on a network by their subnet mask by entering a (static) IP address on the LAN behind your WiMAX Device. The remote IPSec router must be static and correspond to 0.0.0.0. In order to update the encryption and authentication keys and re-negotiate the IKE SA. Subnet Mask Local Port... Select icmp to have the WiMAX Device regularly perform a TCP or UDP handshake with the Remote Endpoint field set to the remote IPSec router's configured local IP addresses. Remote Network Select tcp or udp to have the WiMAX Device regularly ping the address you want the WiMAX ...
... addresses on a network by their subnet mask by entering a (static) IP address on the LAN behind your WiMAX Device. The remote IPSec router must be static and correspond to 0.0.0.0. In order to update the encryption and authentication keys and re-negotiate the IKE SA. Subnet Mask Local Port... Select icmp to have the WiMAX Device regularly perform a TCP or UDP handshake with the Remote Endpoint field set to the remote IPSec router's configured local IP addresses. Remote Network Select tcp or udp to have the WiMAX Device regularly ping the address you want the WiMAX ...
User Guide
Page 143
...network address. Subnet Mask Remote Port If Subnet address is selected, enter a (static) IP address on the LAN behind the remote IPSec's router. The peer must select options from the drop-down list box. Select Tunnel mode or Transport mode from the Encryption Algorithm and Authentication Algorithm ...remote resources are Algorithm SHA1 and MD5. If Single address is selected, specify IP addresses on the LAN behind the remote IPSec's router. Select how the WiMAX Device checks the connection. a 128-bit key with the AES encryption algorithm The WiMAX Device and the remote IPSec...
...network address. Subnet Mask Remote Port If Subnet address is selected, enter a (static) IP address on the LAN behind the remote IPSec's router. The peer must select options from the drop-down list box. Select Tunnel mode or Transport mode from the Encryption Algorithm and Authentication Algorithm ...remote resources are Algorithm SHA1 and MD5. If Single address is selected, specify IP addresses on the LAN behind the remote IPSec's router. Select how the WiMAX Device checks the connection. a 128-bit key with the AES encryption algorithm The WiMAX Device and the remote IPSec...
User Guide
Page 144
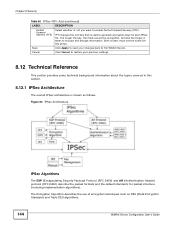
Cancel Click Cancel to restore your changes back to the WiMAX Device. Both routers must use of encryption techniques such as follows. Figure 80 IPSec Architecture IPSec Algorithms The ESP (Encapsulating Security Payload) Protocol (RFC 2406) and AH (Authentication ...
Cancel Click Cancel to restore your changes back to the WiMAX Device. Both routers must use of encryption techniques such as follows. Figure 80 IPSec Architecture IPSec Algorithms The ESP (Encapsulating Security Payload) Protocol (RFC 2406) and AH (Authentication ...
User Guide
Page 146
... period expires. The security protocol appears after the outer IP header and before it times out. If an IPSec SA times out, then the IPSec router must : • Choose an encryption algorithm. • Choose an authentication algorithm • Choose a Diffie-Hellman public-key cryptography key group. • Set the IPSec SA...
... period expires. The security protocol appears after the outer IP header and before it times out. If an IPSec SA times out, then the IPSec router must : • Choose an encryption algorithm. • Choose an authentication algorithm • Choose a Diffie-Hellman public-key cryptography key group. • Set the IPSec SA...