User Guide
Page 5
......1-1 1.1 About Your G-162 ...1-1 1.2 Syntax Conventions ...1-1 1.3 Graphics Icons Key ...1-2 1.4 Application Overview...1-2 1.4.1 Infrastructure ...1-2 1.4.2 Ad-Hoc...1-3 1.5 G-162 Hardware and Utility Installation 1-3 1.6 Configuration Methods ...1-3 1.7 Accessing the ZyXEL Utility...1-4 1.7.1 ZyXEL Utility Screen Summary 1-4...Encryption with WEP 4-1 4.2 Authentication Type ...4-2 4.3 Configuring Security Settings...4-2 4.3.1 WEP Encryption...4-3 4.3.2 WPA-PSK/WPA2-PSK...4-5 4.3.3 WPA/WPA2 or 802.1x...4-6 Chapter 5 Profile...5-1 5.1 Configuring the Profile screen...5-1 5.1.1 Adding a New ...
......1-1 1.1 About Your G-162 ...1-1 1.2 Syntax Conventions ...1-1 1.3 Graphics Icons Key ...1-2 1.4 Application Overview...1-2 1.4.1 Infrastructure ...1-2 1.4.2 Ad-Hoc...1-3 1.5 G-162 Hardware and Utility Installation 1-3 1.6 Configuration Methods ...1-3 1.7 Accessing the ZyXEL Utility...1-4 1.7.1 ZyXEL Utility Screen Summary 1-4...Encryption with WEP 4-1 4.2 Authentication Type ...4-2 4.3 Configuring Security Settings...4-2 4.3.1 WEP Encryption...4-3 4.3.2 WPA-PSK/WPA2-PSK...4-5 4.3.3 WPA/WPA2 or 802.1x...4-6 Chapter 5 Profile...5-1 5.1 Configuring the Profile screen...5-1 5.1.1 Adding a New ...
User Guide
Page 7
ZyXEL G-162 User's Guide List of Figures Figure 1-1 Infrastructure Example ...1-2 Figure 1-2 Ad-Hoc Example ...1-3 Figure 1-3 ZyXEL Utility: System Tray Icon 1-4 Figure 1-4 Screen Overview ...1-5 Figure 1-5 Site Survey ...1-6 Figure 1-6 Site Survey: Security......2-2 Figure 2-2 Link Info: Trend Chart ...2-4 Figure 3-1 Site Survey ...3-1 Figure 4-1 Security Settings: WEP ...4-3 Figure 4-2 Security Settings: WPA-PSK/WPA2-PSK 4-5 Figure 4-3 Security Settings: WPA/WPA2 or 802.1x 4-6 Figure 5-1 Profile ...5-1 Figure 5-2 Profile: Add New Profile ...5-3 Figure 5-3 Profile: Select a Channel ...5-5 ...
ZyXEL G-162 User's Guide List of Figures Figure 1-1 Infrastructure Example ...1-2 Figure 1-2 Ad-Hoc Example ...1-3 Figure 1-3 ZyXEL Utility: System Tray Icon 1-4 Figure 1-4 Screen Overview ...1-5 Figure 1-5 Site Survey ...1-6 Figure 1-6 Site Survey: Security......2-2 Figure 2-2 Link Info: Trend Chart ...2-4 Figure 3-1 Site Survey ...3-1 Figure 4-1 Security Settings: WEP ...4-3 Figure 4-2 Security Settings: WPA-PSK/WPA2-PSK 4-5 Figure 4-3 Security Settings: WPA/WPA2 or 802.1x 4-6 Figure 5-1 Profile ...5-1 Figure 5-2 Profile: Add New Profile ...5-3 Figure 5-3 Profile: Select a Channel ...5-5 ...
User Guide
Page 8
ZyXEL G-162 User's Guide List of Tables Table 1-1ZyXEL Utility: System Tray Icon 1-4 Table 1-2 Screen Summary...1-5 Table 2-1 Link Info ...2-2 Table 2-2 Link Info: Trend Chart...2-4 Table 3-1 Site Survey...3-2 Table 4-1 Wireless LAN Security Levels ...4-1 Table 4-2 Security Settings: WEP...4-3 Table 4-3 Security Settings: WPA-PSK/WPA2-PSK 4-5 Table 4-4 Security Settings: WPA/WPA2 or 802.1x 4-6 Table 5-1 Profile ...5-2 Table 5-2 Profile...
ZyXEL G-162 User's Guide List of Tables Table 1-1ZyXEL Utility: System Tray Icon 1-4 Table 1-2 Screen Summary...1-5 Table 2-1 Link Info ...2-2 Table 2-2 Link Info: Trend Chart...2-4 Table 3-1 Site Survey...3-2 Table 4-1 Wireless LAN Security Levels ...4-1 Table 4-2 Security Settings: WEP...4-3 Table 4-3 Security Settings: WPA-PSK/WPA2-PSK 4-5 Table 4-4 Security Settings: WPA/WPA2 or 802.1x 4-6 Table 5-1 Profile ...5-2 Table 5-2 Profile...
User Guide
Page 9
... to that of the associated wireless network • Security: WEP (Wired Equivalent Privacy), IEEE 802.1x, WPA-PSK, WPA (Wi-Fi Protected Access), WPA2-PSK and WPA2 • A built-in Bold Arial font. The ZyXEL G-162 802.11g Wireless CardBus Card is an IEEE 802.11g compliant wireless LAN adapter.... ZyXEL G-162 User's Guide Chapter 1 Getting Started This chapter introduces the G-162 and prepares you to type one ...
... to that of the associated wireless network • Security: WEP (Wired Equivalent Privacy), IEEE 802.1x, WPA-PSK, WPA (Wi-Fi Protected Access), WPA2-PSK and WPA2 • A built-in Bold Arial font. The ZyXEL G-162 802.11g Wireless CardBus Card is an IEEE 802.11g compliant wireless LAN adapter.... ZyXEL G-162 User's Guide Chapter 1 Getting Started This chapter introduces the G-162 and prepares you to type one ...
User Guide
Page 19
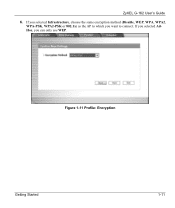
Figure 1-11 Profile: Encryption Getting Started 1-11 If you selected AdHoc, you want to connect. ZyXEL G-162 User's Guide 6. If you selected Infrastructure, choose the same encryption method (Disable, WEP, WPA, WPA2, WPA-PSK, WPA2-PSK or 802.1x) as the AP to which you can only use WEP.
Figure 1-11 Profile: Encryption Getting Started 1-11 If you selected AdHoc, you want to connect. ZyXEL G-162 User's Guide 6. If you selected Infrastructure, choose the same encryption method (Disable, WEP, WPA, WPA2, WPA-PSK, WPA2-PSK or 802.1x) as the AP to which you can only use WEP.
User Guide
Page 25
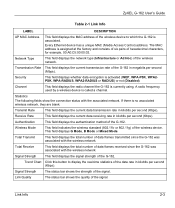
... field displays G Mode, B Mode or Mixed Mode. Total Receive This field displays the total number of the G-162. If there is activated (WEP, WPA-PSK, WPA2PSK, WPA-RADIUS, WPA2-RADIUS or RADIUS) or not (Disabled). Signal Strength This field displays the signal strength of data frames....11g) of the signal. Signal Strength The status bar shows the strength of data frames transmitted since the G-162 was associated with the associated network. ZyXEL G-162 User's Guide Table 2-1 Link Info LABEL DESCRIPTION AP MAC Address This field displays the MAC address of the ...
... field displays G Mode, B Mode or Mixed Mode. Total Receive This field displays the total number of the G-162. If there is activated (WEP, WPA-PSK, WPA2PSK, WPA-RADIUS, WPA2-RADIUS or RADIUS) or not (Disabled). Signal Strength This field displays the signal strength of data frames....11g) of the signal. Signal Strength The status bar shows the strength of data frames transmitted since the G-162 was associated with the associated network. ZyXEL G-162 User's Guide Table 2-1 Link Info LABEL DESCRIPTION AP MAC Address This field displays the MAC address of the ...
User Guide
Page 28
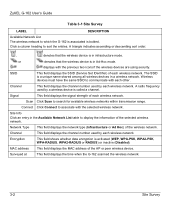
or denotes that the wireless device is activated (WEP, WPA-PSK, WPA2-PSK, WPA-RADIUS, WPA2-RADIUS or RADIUS) or inactive (Disabled). Scan Click Scan to sort the entries. Network Type This field displays the network type (Infrastructure... or descending sort order. , denotes that the wireless device is called a channel. The SSID is bolded. ZyXEL G-162 User's Guide Table 3-1 Site Survey LABEL DESCRIPTION Available Network List The wireless network to which the G-162 is associated is a unique name shared among all wireless devices in a wireless network. Click a column heading ...
or denotes that the wireless device is activated (WEP, WPA-PSK, WPA2-PSK, WPA-RADIUS, WPA2-RADIUS or RADIUS) or inactive (Disabled). Scan Click Scan to sort the entries. Network Type This field displays the network type (Infrastructure... or descending sort order. , denotes that the wireless device is called a channel. The SSID is bolded. ZyXEL G-162 User's Guide Table 3-1 Site Survey LABEL DESCRIPTION Available Network List The wireless network to which the G-162 is associated is a unique name shared among all wireless devices in a wireless network. Click a column heading ...
User Guide
Page 29
... Secure Wi-Fi Protected Access (WPA) WPA2 (IEEE 802.11i) Configure the wireless LAN security using the Profile Security Settings screen. Security Settings 4-1 You must use the same passphrase for all data packets transmitted between the G-162 and the AP or other peer...User Service) server either on your LAN to provide authentication service for wireless clients. The passphrase is used for data encryption and decryption. ZyXEL G-162 User's Guide Chapter 4 Security Settings This chapter discusses how to configure wireless security on a "password phrase" called a passphrase. EAP ...
... Secure Wi-Fi Protected Access (WPA) WPA2 (IEEE 802.11i) Configure the wireless LAN security using the Profile Security Settings screen. Security Settings 4-1 You must use the same passphrase for all data packets transmitted between the G-162 and the AP or other peer...User Service) server either on your LAN to provide authentication service for wireless clients. The passphrase is used for data encryption and decryption. ZyXEL G-162 User's Guide Chapter 4 Security Settings This chapter discusses how to configure wireless security on a "password phrase" called a passphrase. EAP ...
User Guide
Page 30
... shared secret key to authenticate the wireless client to the selected encryption method. ZyXEL G-162 User's Guide For WLAN adapters without the passphrase feature, you can associate with wireless security activated. Your G-162 allows you add a new profile or edit an existing profile. This screen ...also displays when you to configure up to join. 4-2 Security Settings Enter the exact same settings (for more information about WPA, WPA2 and IEEE 802.1x. ...
... shared secret key to authenticate the wireless client to the selected encryption method. ZyXEL G-162 User's Guide For WLAN adapters without the passphrase feature, you can associate with wireless security activated. Your G-162 allows you add a new profile or edit an existing profile. This screen ...also displays when you to configure up to join. 4-2 Security Settings Enter the exact same settings (for more information about WPA, WPA2 and IEEE 802.1x. ...
User Guide
Page 33
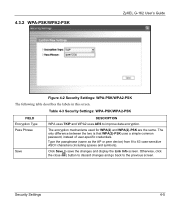
... Pass Phrase Save DESCRIPTION WPA uses TKIP and WPA2 uses AES to save the changes and display the Link Info screen. Click Save to improve data encryption. Security Settings 4-5 4.3.2 WPA-PSK/WPA2-PSK ZyXEL G-162 User's Guide Figure 4-2 Security Settings: WPA-PSK/WPA2-PSK The ...following table describes the labels in this screen. The encryption mechanisms used for WPA(2) and WPA(2)-PSK are the same.
... Pass Phrase Save DESCRIPTION WPA uses TKIP and WPA2 uses AES to save the changes and display the Link Info screen. Click Save to improve data encryption. Security Settings 4-5 4.3.2 WPA-PSK/WPA2-PSK ZyXEL G-162 User's Guide Figure 4-2 Security Settings: WPA-PSK/WPA2-PSK The ...following table describes the labels in this screen. The encryption mechanisms used for WPA(2) and WPA(2)-PSK are the same.
User Guide
Page 34
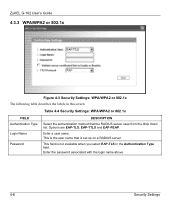
... Type Login Name Password DESCRIPTION Select the authentication method that is not available when you select EAP-TLS in this screen. ZyXEL G-162 User's Guide 4.3.3 WPA/WPA2 or 802.1x Figure 4-3 Security Settings: WPA/WPA2 or 802.1x The following table describes the labels in the Authentication Type field. This field is set up...
... Type Login Name Password DESCRIPTION Select the authentication method that is not available when you select EAP-TLS in this screen. ZyXEL G-162 User's Guide 4.3.3 WPA/WPA2 or 802.1x Figure 4-3 Security Settings: WPA/WPA2 or 802.1x The following table describes the labels in the Authentication Type field. This field is set up...
User Guide
Page 35
... in the Authentication Type field. Use the drop-down list box to select a PEAP protocol that the RADIUS server uses. Security Settings 4-7 ZyXEL G-162 User's Guide Table 4-4 Security Settings: WPA/WPA2 or 802.1x FIELD Certificate DESCRIPTION This field is only available when you select EAP-TLS in the Authentication Type field. Browse...
... in the Authentication Type field. Use the drop-down list box to select a PEAP protocol that the RADIUS server uses. Security Settings 4-7 ZyXEL G-162 User's Guide Table 4-4 Security Settings: WPA/WPA2 or 802.1x FIELD Certificate DESCRIPTION This field is only available when you select EAP-TLS in the Authentication Type field. Browse...
User Guide
Page 38
...Hoc mode. Click Add in the Profile screen to add a new profile. or denotes that the wireless device is activated (WEP, WPA-PSK, WPA2-PSK, WPA-RADIUS, WPA2-RADIUS or RADIUS) or inactive (Disabled). 5.1.1 Adding a New Profile Follow the steps below to display the screen as..., select a profile name in the table and click Delete. displays with the previous two icons if the wireless devices are using this profile. ZyXEL G-162 User's Guide Table 5-1 Profile LABEL DESCRIPTION Profile List Click a column heading to continue. 5-2 Profile Add To add a new profile into the...
...Hoc mode. Click Add in the Profile screen to add a new profile. or denotes that the wireless device is activated (WEP, WPA-PSK, WPA2-PSK, WPA-RADIUS, WPA2-RADIUS or RADIUS) or inactive (Disabled). 5.1.1 Adding a New Profile Follow the steps below to display the screen as..., select a profile name in the table and click Delete. displays with the previous two icons if the wireless devices are using this profile. ZyXEL G-162 User's Guide Table 5-1 Profile LABEL DESCRIPTION Profile List Click a column heading to continue. 5-2 Profile Add To add a new profile into the...
User Guide
Page 42
If you select Infrastructure network type in the first screen, you select Ad-Hoc network type in the first screen, select the same encryption method as the AP (WEP, WPA-PSK, WPA2-PSK, WPA, WPA2 or 802.1x) from the drop-down list box to Step 5. Figure 5-4 Profile: Wireless Settings 5-6 Profile ZyXEL G-162 User's Guide Step 3. Otherwise, select Disabled to allow the G-162 to communicate with the access points or other peer wireless devices without any data encryption and skip to enable data encryption. If you can only use WEP encryption method.
If you select Infrastructure network type in the first screen, you select Ad-Hoc network type in the first screen, select the same encryption method as the AP (WEP, WPA-PSK, WPA2-PSK, WPA, WPA2 or 802.1x) from the drop-down list box to Step 5. Figure 5-4 Profile: Wireless Settings 5-6 Profile ZyXEL G-162 User's Guide Step 3. Otherwise, select Disabled to allow the G-162 to communicate with the access points or other peer wireless devices without any data encryption and skip to enable data encryption. If you can only use WEP encryption method.
User Guide
Page 47
ZyXEL G-162 User's Guide Chapter 6 Adapter This chapter discusses OTIST and how to configure the Adapter screen. 6.1 ... same settings on both as "AP" here) in order to wireless clients that you have to have OTIST generate a WPA(2)-PSK key for you if you didn't configure one manually. 6.1.1 Enabling OTIST You must have the same SSID and security... settings as your AP's SSID and WEP or WPA(2)-PSK security settings to associate with it. Select the OTIST check box, enter the same Setup Key as the access point...
ZyXEL G-162 User's Guide Chapter 6 Adapter This chapter discusses OTIST and how to configure the Adapter screen. 6.1 ... same settings on both as "AP" here) in order to wireless clients that you have to have OTIST generate a WPA(2)-PSK key for you if you didn't configure one manually. 6.1.1 Enabling OTIST You must have the same SSID and security... settings as your AP's SSID and WEP or WPA(2)-PSK security settings to associate with it. Select the OTIST check box, enter the same Setup Key as the access point...
User Guide
Page 48
... go to the factory defaults! This screen appears while OTIST settings are being transferred. It closes when the transfer is used to transfer. ZyXEL G-162 User's Guide AP You can start OTIST in the wireless clients and AP in the wireless client(s) Adapter screen all be within three minutes... (at the time of writing). To have OTIST enabled. 1. If you manually configured a WEP key or a WPA(2)-PSK key and you also selected this check box, then the key you manually configured is complete. 6-2 Adapter In the AP, a web configurator screen...
... go to the factory defaults! This screen appears while OTIST settings are being transferred. It closes when the transfer is used to transfer. ZyXEL G-162 User's Guide AP You can start OTIST in the wireless clients and AP in the wireless client(s) Adapter screen all be within three minutes... (at the time of writing). To have OTIST enabled. 1. If you manually configured a WEP key or a WPA(2)-PSK key and you also selected this check box, then the key you manually configured is complete. 6-2 Adapter In the AP, a web configurator screen...
User Guide
Page 50
... the AP after using OTIST, you need to run OTIST again or enter them manually in the wireless client(s). 5. If you configure OTIST to generate a WPA(2)-PSK key, this screen. ZyXEL G-162 User's Guide 4.
... the AP after using OTIST, you need to run OTIST again or enter them manually in the wireless client(s). 5. If you configure OTIST to generate a WPA(2)-PSK key, this screen. ZyXEL G-162 User's Guide 4.
User Guide
Page 59
... Operating Frequencies Operating Channels Data Rate Modulation Security Operating Temperature Storage Temperature Operating Humidity Storage Humidity Power Consumption Voltage Weight Dimension ZyXEL G-162 802.11g Wireless CardBus Card 3.3V 32-bit CardBus card IEEE 802.11b IEEE 802.11g Infrastructure Ad-Hoc 2.412-2....64QAM, 16QAM, QPSK and BPSK) IEEE 802.11b: PBCC, Direct Sequence Spread Spectrum (CCK, DQPSK, DBPSK). 64/128/256-bit WEP, 802.1x, WPA-PSK, WPA, WPA2-PSK, WPA2 0 ~ 50 degrees Centigrade -30 ~ 60 degrees Centigrade 20 ~ 95% (non-condensing) 20 ~ 95% (non-condensing) IEEE...
... Operating Frequencies Operating Channels Data Rate Modulation Security Operating Temperature Storage Temperature Operating Humidity Storage Humidity Power Consumption Voltage Weight Dimension ZyXEL G-162 802.11g Wireless CardBus Card 3.3V 32-bit CardBus card IEEE 802.11b IEEE 802.11g Infrastructure Ad-Hoc 2.412-2....64QAM, 16QAM, QPSK and BPSK) IEEE 802.11b: PBCC, Direct Sequence Spread Spectrum (CCK, DQPSK, DBPSK). 64/128/256-bit WEP, 802.1x, WPA-PSK, WPA, WPA2-PSK, WPA2 0 ~ 50 degrees Centigrade -30 ~ 60 degrees Centigrade 20 ~ 95% (non-condensing) 20 ~ 95% (non-condensing) IEEE...
User Guide
Page 69
...that you want the information about and click to article 871122 on the Microsoft web site for WPA from the Microsoft web site. Windows XP SP2 screen shots are shown unless otherwise specified. ZyXEL G-162 User's Guide Appendix C Management with Wireless Zero Configuration K Be sure you how to manage ... This appendix shows you have the Windows XP service pack 1 already on your computer and download the support patch for information on your G-162 using the Windows XP wireless zero configuration tool. If you should at least have the Windows XP service pack 2 installed on starting WZC...
...that you want the information about and click to article 871122 on the Microsoft web site for WPA from the Microsoft web site. Windows XP SP2 screen shots are shown unless otherwise specified. ZyXEL G-162 User's Guide Appendix C Management with Wireless Zero Configuration K Be sure you how to manage ... This appendix shows you have the Windows XP service pack 1 already on your computer and download the support patch for information on your G-162 using the Windows XP wireless zero configuration tool. If you should at least have the Windows XP service pack 2 installed on starting WZC...
User Guide
Page 75
...Windows XP SP2: Wireless Network Connection: WEP or WPA-PSK Diagram 17 Windows XP SP2: Wireless Network Connection: No Security 5. Refer to the wireless network. If there is not available. This denotes the G-162 is an available wireless network. This denotes the wireless... the connection icon in the Wireless Network Connection screen to another wireless network without data encryption. Management with Wireless Zero Configuration Q ZyXEL G-162 User's Guide 4. Click Connect Anyway if wireless security is activated for more information. Chart 3 Windows XP: Wireless Networks ICON...
...Windows XP SP2: Wireless Network Connection: WEP or WPA-PSK Diagram 17 Windows XP SP2: Wireless Network Connection: No Security 5. Refer to the wireless network. If there is not available. This denotes the G-162 is an available wireless network. This denotes the wireless... the connection icon in the Wireless Network Connection screen to another wireless network without data encryption. Management with Wireless Zero Configuration Q ZyXEL G-162 User's Guide 4. Click Connect Anyway if wireless security is activated for more information. Chart 3 Windows XP: Wireless Networks ICON...