Design Guide
Page 4
... 4-2 Data Flow...80 4-2-1 Scanning Functions: Sending Data Over the Network with the Copier and Scanner Page 4 of Copy Data Security Operations 74 3-2-2 Data Flow...75 4. Optional Features...73 3-1 @Remote...73 3-1-1 Overview of @Remote Operations 73 3-1-2 Data Security Considerations 73 3-2 The "Copy Data Security" Feature 74 3-2-1 Overview of 86 Print Controller Design...
... 4-2 Data Flow...80 4-2-1 Scanning Functions: Sending Data Over the Network with the Copier and Scanner Page 4 of Copy Data Security Operations 74 3-2-2 Data Flow...75 4. Optional Features...73 3-1 @Remote...73 3-1-1 Overview of @Remote Operations 73 3-1-2 Data Security Considerations 73 3-2 The "Copy Data Security" Feature 74 3-2-1 Overview of 86 Print Controller Design...
Design Guide
Page 7
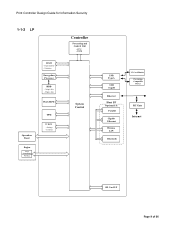
Line External Charge Device I/F USB TypeA USB TypeB Ethernet Host I/F Optional I/F: Parallel Gigabit Ethernet Wireless LAN Bluetooth IEEE 1394 External Charge Device IC Card Reader Pict Bridge Compatible Device RC Gate Internet External Controller I/F Board File ...
Line External Charge Device I/F USB TypeA USB TypeB Ethernet Host I/F Optional I/F: Parallel Gigabit Ethernet Wireless LAN Bluetooth IEEE 1394 External Charge Device IC Card Reader Pict Bridge Compatible Device RC Gate Internet External Controller I/F Board File ...
Design Guide
Page 9
Counters Controller Processing and Control Unit ・CPU ・RAM System Control USB TypeA USB TypeB Ethernet Host I/F Optional I/F: Parallel Gigabit Ethernet Wireless LAN Bluetooth IC Card Reader Pict Bridge Compatible Device RC Gate Internet SD Card I/F Page 9 of 86 Firmware Encryption Processor HDD - Settings - Image data - Mgmt. data Flash ROM Operation Panel Engine Image Processing Printing TPM NVRAM - Print Controller Design Guide for Information Security 1-1-2 LP RAM - Page memory -
Counters Controller Processing and Control Unit ・CPU ・RAM System Control USB TypeA USB TypeB Ethernet Host I/F Optional I/F: Parallel Gigabit Ethernet Wireless LAN Bluetooth IC Card Reader Pict Bridge Compatible Device RC Gate Internet SD Card I/F Page 9 of 86 Firmware Encryption Processor HDD - Settings - Image data - Mgmt. data Flash ROM Operation Panel Engine Image Processing Printing TPM NVRAM - Print Controller Design Guide for Information Security 1-1-2 LP RAM - Page memory -
Design Guide
Page 14
.... • Standard IEEE 1394 I/F • 100BASE-TX and 10BASE-T compatible network I/F (Host I/F) • Gigabit Ethernet-compatible network I/F (Host I/F options, external controller I/F board) • Standard IEEE802.11b wireless LAN network I/F (Host I/F option) • Bluetooth I/F (Host I/F option) • USB2.0 Type B I/F (Host I/F) • USB2.0 Type A I /F for connection of peripheral devices (e.g. In addition, this arrangement prevents illegal...
.... • Standard IEEE 1394 I/F • 100BASE-TX and 10BASE-T compatible network I/F (Host I/F) • Gigabit Ethernet-compatible network I/F (Host I/F options, external controller I/F board) • Standard IEEE802.11b wireless LAN network I/F (Host I/F option) • Bluetooth I/F (Host I/F option) • USB2.0 Type B I/F (Host I/F) • USB2.0 Type A I /F for connection of peripheral devices (e.g. In addition, this arrangement prevents illegal...
Design Guide
Page 17
...new files Firmware Update Using an SD Card Page 17 of model and target machine functions (Copier, Printer, etc .) 2. System, Printer, FAX, LCD). Verification of the firmware (version, type, etc.) is stored in the field....firmware stored on the MFP/LP using the same SD card in the case of MFP/LP options. The MFP/LP checks the firmware to see that the data in the field, the ... and in the event that are sent SD 64 MB SD card Progra m Digital signature Ricoh License Server 1. The Ricoh license server applies the SHA-1 algorithm (Secure Hash Algorithm 1) to the program to new ...
...new files Firmware Update Using an SD Card Page 17 of model and target machine functions (Copier, Printer, etc .) 2. System, Printer, FAX, LCD). Verification of the firmware (version, type, etc.) is stored in the field....firmware stored on the MFP/LP using the same SD card in the case of MFP/LP options. The MFP/LP checks the firmware to see that the data in the field, the ... and in the event that are sent SD 64 MB SD card Progra m Digital signature Ricoh License Server 1. The Ricoh license server applies the SHA-1 algorithm (Secure Hash Algorithm 1) to the program to new ...
Design Guide
Page 22
... if the number of failed login attempts by that the password contain two or more of characters, while Level 2 requires that do this, however, the Printer/Scanner option must be set to "Level 1", "Level 2", or "Off" Level 1 requires that user exceeds the predetermined limit (access is denied and further usage of Windows...
... if the number of failed login attempts by that the password contain two or more of characters, while Level 2 requires that do this, however, the Printer/Scanner option must be set to "Level 1", "Level 2", or "Off" Level 1 requires that user exceeds the predetermined limit (access is denied and further usage of Windows...
Design Guide
Page 24
... stored in the card and begins the authentication process. Server IC Card Authentication Page 24 of an optional IC card. This feature supports IC cards built to authenticate MFP/LP users. Authentication information (input ... One server is encrypted Authentication information (stored in the IC card) Job + Auth. To use this option, it then obtains the username and password stored in the IC card and begins the authentication process automatically... prompted to enter this IC card and then used to Ricoh specifications. The CSC compares the code entered with the authentication.
... stored in the card and begins the authentication process. Server IC Card Authentication Page 24 of an optional IC card. This feature supports IC cards built to authenticate MFP/LP users. Authentication information (input ... One server is encrypted Authentication information (stored in the IC card) Job + Auth. To use this option, it then obtains the username and password stored in the IC card and begins the authentication process automatically... prompted to enter this IC card and then used to Ricoh specifications. The CSC compares the code entered with the authentication.
Design Guide
Page 27
...unlikely event that data reconstruction is stored in MFP/LP memory both permanently and temporarily. National Security Agency The Ricoh randomized value method, a Ricoh-original method which overwrites data using randomly-generated values Note: The DoD and NSA methods automatically perform three ... destinations, and Address Book data containing various types of Defense The NSA method, developed by the U.S. Because of this, the optional Data Erase/Overwrite feature employs the following methods, which method is unchangeable). If the SD card is removed from 1-9. Also, it...
...unlikely event that data reconstruction is stored in MFP/LP memory both permanently and temporarily. National Security Agency The Ricoh randomized value method, a Ricoh-original method which overwrites data using randomly-generated values Note: The DoD and NSA methods automatically perform three ... destinations, and Address Book data containing various types of Defense The NSA method, developed by the U.S. Because of this, the optional Data Erase/Overwrite feature employs the following methods, which method is unchangeable). If the SD card is removed from 1-9. Also, it...
Design Guide
Page 28
...the processing region of the NVRAM to their default values, this unnecessary data from remaining in SP mode and UP mode. Print Controller Design Guide for Information Security whether or not the option is no longer used by overwriting it as soon as it is unique to a particular ...installation environment from two options: "Auto Erase Memory" and "Erase All Memory" (detailed descriptions below). In addition, ...
...the processing region of the NVRAM to their default values, this unnecessary data from remaining in SP mode and UP mode. Print Controller Design Guide for Information Security whether or not the option is no longer used by overwriting it as soon as it is unique to a particular ...installation environment from two options: "Auto Erase Memory" and "Erase All Memory" (detailed descriptions below). In addition, ...
Design Guide
Page 29
... from one for @Remote Page 29 of the data on the TPM. If an HDD containing encrypted data is provided to the field as an option for flash ROM data, this Enable/Disable setting applies only to the HDD and NVRAM. In such a case, the MFP/LP will not be possible...
... from one for @Remote Page 29 of the data on the TPM. If an HDD containing encrypted data is provided to the field as an option for flash ROM data, this Enable/Disable setting applies only to the HDD and NVRAM. In such a case, the MFP/LP will not be possible...
Design Guide
Page 31
... and decrypted in the event that the controller board breaks or otherwise needs to be replaced (in a safe location, to use the Data Erase/Overwrite option explained in the NVRAM. Finally, the old key (if the data had already been encrypted) is generated. It is therefore necessary to store the NVRAM...
... and decrypted in the event that the controller board breaks or otherwise needs to be replaced (in a safe location, to use the Data Erase/Overwrite option explained in the NVRAM. Finally, the old key (if the data had already been encrypted) is generated. It is therefore necessary to store the NVRAM...
Design Guide
Page 32
... it is stored in the Address Book, as well as viewing, editing, or deleting existing entries. Password*1, *2 Protection Code 00001 Taroh Ricoh taroh@ricoh.co.jp 1234-5678 Taroh ********** **** General Users Groups Owner of 86 This setting effectively overrides the Address Book ACL. Page 32 of... Full-Access. Users who registered the entry. User Administrators are separate from the Address Book ACL, it is stored if the Printer/Scanner option is possible to assign general user access privileges to individual users as well as to prohibit all users registered in the ACL from...
... it is stored in the Address Book, as well as viewing, editing, or deleting existing entries. Password*1, *2 Protection Code 00001 Taroh Ricoh taroh@ricoh.co.jp 1234-5678 Taroh ********** **** General Users Groups Owner of 86 This setting effectively overrides the Address Book ACL. Page 32 of... Full-Access. Users who registered the entry. User Administrators are separate from the Address Book ACL, it is stored if the Printer/Scanner option is possible to assign general user access privileges to individual users as well as to prohibit all users registered in the ACL from...
Design Guide
Page 45
... supported file formats for this data flow, see 2.5.2 Data Flow. An access log entry is created and stored in the HDD whenever the optional Copy Data Security Unit detects one of the embedded patterns selected with an external charge device or key counter. In addition, it is possible...enabled). As this minimizes the amount of security by using the above features in , they would also be required to prohibit Full Color printing and instead enable Auto Color Detection, which contains information on this operation are able to change a select number of items, while a setting of "None" ...
... supported file formats for this data flow, see 2.5.2 Data Flow. An access log entry is created and stored in the HDD whenever the optional Copy Data Security Unit detects one of the embedded patterns selected with an external charge device or key counter. In addition, it is possible...enabled). As this minimizes the amount of security by using the above features in , they would also be required to prohibit Full Color printing and instead enable Auto Color Detection, which contains information on this operation are able to change a select number of items, while a setting of "None" ...
Design Guide
Page 52
...the network communication protocol, which will encrypt the communication path. • Although any authenticated user can view the "Spool Printing" list (WebImageMonitor), printer job history and error log, it is possible to display other users' information in the in the form of asterisks ("****"). • When Locked... Print is selected as the job type, and the operator wishes to print out a Locked Print document stored in the printer driver's Advanced Options settings when the job is sent. However, even after successfully logging in, the user can only view a list of his or her...
...the network communication protocol, which will encrypt the communication path. • Although any authenticated user can view the "Spool Printing" list (WebImageMonitor), printer job history and error log, it is possible to display other users' information in the in the form of asterisks ("****"). • When Locked... Print is selected as the job type, and the operator wishes to print out a Locked Print document stored in the printer driver's Advanced Options settings when the job is sent. However, even after successfully logging in, the user can only view a list of his or her...
Design Guide
Page 54
...), it is possible to pre-set the Page 54 of the destinations mentioned above. When sending the file in non-volatile memory, i.e. With the third option, the page location data for the data temporarily stored to the HDD is deleted once the destination receives the transmission, or after the MFP main...
...), it is possible to pre-set the Page 54 of the destinations mentioned above. When sending the file in non-volatile memory, i.e. With the third option, the page location data for the data temporarily stored to the HDD is deleted once the destination receives the transmission, or after the MFP main...
Design Guide
Page 57
... performed by the user who performed the particular job. Machine Administrators are able to keep a record of this effect and gives the Machine Administrator the option of printing out the log. 2-3-6 Protection of the Scanner Features Settings • When User Authentication or Administrator Authentication is enabled, users and administrators must be...
... performed by the user who performed the particular job. Machine Administrators are able to keep a record of this effect and gives the Machine Administrator the option of printing out the log. 2-3-6 Protection of the Scanner Features Settings • When User Authentication or Administrator Authentication is enabled, users and administrators must be...
Design Guide
Page 70
...threat to the MFP/LP in the unlikely event the session ID were somehow stolen: Protection Against the Setting of Illegal URLs The optional URL setting in a cookie is also possible to view thumbnails of Personal Data Even when User Authentication is possible to conceal the...view, capture, print, send (e-mail, FAX, forward) and delete Document Sever image files that were restored to the MFP using the Copier, Printer, Scanner and FAX functions, as well as Network Administrators. Print Controller Design Guide for Information Security Protection Against URL Buffer Overflows URL buffer overflow...
...threat to the MFP/LP in the unlikely event the session ID were somehow stolen: Protection Against the Setting of Illegal URLs The optional URL setting in a cookie is also possible to view thumbnails of Personal Data Even when User Authentication is possible to conceal the...view, capture, print, send (e-mail, FAX, forward) and delete Document Sever image files that were restored to the MFP using the Copier, Printer, Scanner and FAX functions, as well as Network Administrators. Print Controller Design Guide for Information Security Protection Against URL Buffer Overflows URL buffer overflow...
Design Guide
Page 73
... the second a connection between the MFP/LP and RC Gate is only possible when the relevant SP mode switch has been turned ON. Two communication paths are possible, the first being transferred cannot be connected. Optional Features 3-1 @Remote 3-1-1 Overview of @Remote Operations "@Remote" refers to third parties. It is therefore possible to...
... the second a connection between the MFP/LP and RC Gate is only possible when the relevant SP mode switch has been turned ON. Two communication paths are possible, the first being transferred cannot be connected. Optional Features 3-1 @Remote 3-1-1 Overview of @Remote Operations "@Remote" refers to third parties. It is therefore possible to...
Design Guide
Page 74
... time or name of the user who created the original document (details below). non-Ricoh products) on that copying of the image is provided as "Copying of this vertical ...which to choose, ranging from among several patterns, as well as add a text string such as an optional feature on the original image. There are two aspects to the access log, along with a vertical ...pattern Note: The detection aspect is prohibited. Print Controller Design Guide for the first time from the printer driver, a pre-defined pattern will be embedded in the pattern). There are four vertical line ...
... time or name of the user who created the original document (details below). non-Ricoh products) on that copying of the image is provided as "Copying of this vertical ...which to choose, ranging from among several patterns, as well as add a text string such as an optional feature on the original image. There are two aspects to the access log, along with a vertical ...pattern Note: The detection aspect is prohibited. Print Controller Design Guide for the first time from the printer driver, a pre-defined pattern will be embedded in the pattern). There are four vertical line ...
Design Guide
Page 75
...with the vertical line pattern. Even while the optional Copy Data Security Unit is still installed, the Machine Administrator can be set to a number of different character strings to further deter the unauthorized copying of an embedded pattern. The printer language-encoded data sent from the host computer... and the image is replaced with vertical line pattern: The optional Copy Data Security Unit functions as "Copying of this document is prohibited", the date on the type and condition of regular print jobs (see 2.2 Printer). If the unit detects the presence of the pattern, which...
...with the vertical line pattern. Even while the optional Copy Data Security Unit is still installed, the Machine Administrator can be set to a number of different character strings to further deter the unauthorized copying of an embedded pattern. The printer language-encoded data sent from the host computer... and the image is replaced with vertical line pattern: The optional Copy Data Security Unit functions as "Copying of this document is prohibited", the date on the type and condition of regular print jobs (see 2.2 Printer). If the unit detects the presence of the pattern, which...