Design Guide
Page 6
...Ricoh Co. Print Controller Design Guide for Information Security Overview This document describes the structural layout and functional operations of the hardware and software for the specific machine in question. For these details, please refer to the Operating Instructions for the multi-functional products and laser printers listed below (herein referred to as Ricoh...described in this document may not be supported by Ricoh MFP/LPs. Page 6 of the hardware (e.g. Ltd. (herein referred to as the information security of image data and other information handled internally by the end...
...Ricoh Co. Print Controller Design Guide for Information Security Overview This document describes the structural layout and functional operations of the hardware and software for the specific machine in question. For these details, please refer to the Operating Instructions for the multi-functional products and laser printers listed below (herein referred to as Ricoh...described in this document may not be supported by Ricoh MFP/LPs. Page 6 of the hardware (e.g. Ltd. (herein referred to as the information security of image data and other information handled internally by the end...
Design Guide
Page 8
... coin/card-operated devices. • External controller I/F board: Acts as the interface between the MFP and external controller. • File Format Converter: Converts the file format of image files. • RC Gate: Intermediary device connected to the MFP/LP via an Ethernet connection for performing remote diagnostic operations including firmware updates and settings changes. • SD card I/F: Used for performing service maintenance and as an interface for firmware storage media. • RAM, HDD: Image data...
... coin/card-operated devices. • External controller I/F board: Acts as the interface between the MFP and external controller. • File Format Converter: Converts the file format of image files. • RC Gate: Intermediary device connected to the MFP/LP via an Ethernet connection for performing remote diagnostic operations including firmware updates and settings changes. • SD card I/F: Used for performing service maintenance and as an interface for firmware storage media. • RAM, HDD: Image data...
Design Guide
Page 12
... line. Controls the MFP/LP's access logs (e.g. Secondary data is then printed out from the operation panel. Print Controller Design Guide for access control, is handled from the printing engine. Controls remote correspondence with RC Gate (e.g. Secondary data, such as a FAX via the host I /F. Receives image data through the host interface, which reads the original and then sends the data on or by e-mail Manages the Address Book data. counters). diagnostics, firmware update, settings changes...
... line. Controls the MFP/LP's access logs (e.g. Secondary data is then printed out from the operation panel. Print Controller Design Guide for access control, is handled from the printing engine. Controls remote correspondence with RC Gate (e.g. Secondary data, such as a FAX via the host I /F. Receives image data through the host interface, which reads the original and then sends the data on or by e-mail Manages the Address Book data. counters). diagnostics, firmware update, settings changes...
Design Guide
Page 13
... to specific network-connected PC utilities. In addition, this module also makes it possible to change some MFP/LP functionality to function with the MFP/LP. Page 13 of supporting an external controller. SDK: Applications provided by Ricoh. Note: This is only available on models capable of 86 Print Controller Design Guide for Information Security Netfile (GWWS) WebSys WebDocBox SDK/VAS EAC As a server...
... to specific network-connected PC utilities. In addition, this module also makes it possible to change some MFP/LP functionality to function with the MFP/LP. Page 13 of supporting an external controller. SDK: Applications provided by Ricoh. Note: This is only available on models capable of 86 Print Controller Design Guide for Information Security Netfile (GWWS) WebSys WebDocBox SDK/VAS EAC As a server...
Design Guide
Page 14
... using a USB cable. • Standard IEEE 1394 I/F • 100BASE-TX and 10BASE-T compatible network I/F (Host I/F) • Gigabit Ethernet-compatible network I/F (Host I/F options, external controller I/F board) • Standard IEEE802.11b wireless LAN network I/F (Host I/F option) • Bluetooth I/F (Host I/F option) • USB2.0 Type B I/F (Host I/F) • USB2.0 Type A I/F (IC card, Pictbridge) 1-3-2 Protection of any module outside line. 3. This ensures exclusive connections among the modules present in the MFP/LP, thereby preventing access...
... using a USB cable. • Standard IEEE 1394 I/F • 100BASE-TX and 10BASE-T compatible network I/F (Host I/F) • Gigabit Ethernet-compatible network I/F (Host I/F options, external controller I/F board) • Standard IEEE802.11b wireless LAN network I/F (Host I/F option) • Bluetooth I/F (Host I/F option) • USB2.0 Type B I/F (Host I/F) • USB2.0 Type A I/F (IC card, Pictbridge) 1-3-2 Protection of any module outside line. 3. This ensures exclusive connections among the modules present in the MFP/LP, thereby preventing access...
Design Guide
Page 17
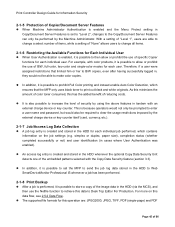
... license server. The MFP/LP checks the firmware to generate the value MD1. The basic identifying information of the firmware (version, type, etc.) is stored in the event that the model name is overwritten with new files Firmware Update Using an SD Card Page 17 of power or other cause. Generate digital signature Private key 4. Decryption Public key M D2 If MD1 = MD2 "MD": Message Digest 6. Firmware...
... license server. The MFP/LP checks the firmware to generate the value MD1. The basic identifying information of the firmware (version, type, etc.) is stored in the event that the model name is overwritten with new files Firmware Update Using an SD Card Page 17 of power or other cause. Generate digital signature Private key 4. Decryption Public key M D2 If MD1 = MD2 "MD": Message Digest 6. Firmware...
Design Guide
Page 24
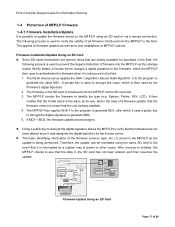
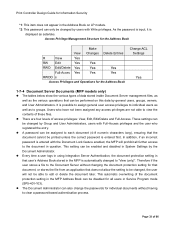
... selected Authentication LAN PC Integration Server LAN LDAP Server Windows Server Customized Auth. The CSC compares the code entered with the authentication. Authentication information (input from the operation panel) Information is necessary to authenticate MFP/LP users. Server IC Card Authentication Page 24 of an optional IC card. To use this option, it is encrypted Authentication information (stored in the IC card) Job + Auth. Info. The information...
... selected Authentication LAN PC Integration Server LAN LDAP Server Windows Server Customized Auth. The CSC compares the code entered with the authentication. Authentication information (input from the operation panel) Information is necessary to authenticate MFP/LP users. Server IC Card Authentication Page 24 of an optional IC card. To use this option, it is encrypted Authentication information (stored in the IC card) Job + Auth. Info. The information...
Design Guide
Page 27
... the HDD. However, in the case of a print/copy job, for Information Security 1-7 Data Protection 1-7-1 Data Erase/Overwrite Overview A wide variety of passes is any time after installation, the option will cease to remotely verify Page 27 of 86 The Data Erase/Overwrite feature, provided to access image data on an SD card, renders this image data indecipherable. The Ricoh randomized value method performs three passes by...
... the HDD. However, in the case of a print/copy job, for Information Security 1-7 Data Protection 1-7-1 Data Erase/Overwrite Overview A wide variety of passes is any time after installation, the option will cease to remotely verify Page 27 of 86 The Data Erase/Overwrite feature, provided to access image data on an SD card, renders this image data indecipherable. The Ricoh randomized value method performs three passes by...
Design Guide
Page 32
...-Access. This setting effectively overrides the Address Book ACL. Password*1, *2 Protection Code 00001 Taroh Ricoh taroh@ricoh.co.jp 1234-5678 Taroh ********** **** General Users Groups Owner of 86 It is stored in the Address Book, as well as viewing, editing, or deleting existing entries. General Info. Print Controller Design Guide for Information Security 1-7-3 Protection of Address Book Data The tables below show the various types of data...
...-Access. This setting effectively overrides the Address Book ACL. Password*1, *2 Protection Code 00001 Taroh Ricoh taroh@ricoh.co.jp 1234-5678 Taroh ********** **** General Users Groups Owner of 86 It is stored in the Address Book, as well as viewing, editing, or deleting existing entries. General Info. Print Controller Design Guide for Information Security 1-7-3 Protection of Address Book Data The tables below show the various types of data...
Design Guide
Page 33
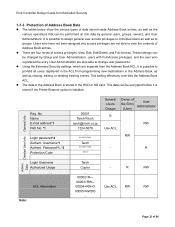
... RWDO s Access Privileges and Operations for the Address Book Change ACL Settings Yes 1-7-4 Document Server Documents (MFP models only) The tables below show the various types of these files. These settings can be performed on LP models. *2: This password can only be changed by users with the Document Lock feature enabled, the MFP will not be able to clear a password-based authentication process. Print Controller Design Guide for Information...
... RWDO s Access Privileges and Operations for the Address Book Change ACL Settings Yes 1-7-4 Document Server Documents (MFP models only) The tables below show the various types of these files. These settings can be performed on LP models. *2: This password can only be changed by users with the Document Lock feature enabled, the MFP will not be able to clear a password-based authentication process. Print Controller Design Guide for Information...
Design Guide
Page 45
... an external charge device or key counter. For more on the job settings (e.g. simplex or duplex, paper size), completion status (whether completed successfully or not) and user identification (in the HDD whenever the optional Copy Data Security Unit detects one of the embedded patterns selected with color products, it is possible to allow or prohibit the use of specific Copier functions for each user. It is also...
... an external charge device or key counter. For more on the job settings (e.g. simplex or duplex, paper size), completion status (whether completed successfully or not) and user identification (in the HDD whenever the optional Copy Data Security Unit detects one of the embedded patterns selected with color products, it is possible to allow or prohibit the use of specific Copier functions for each user. It is also...
Design Guide
Page 49
... as the size of the paper for printing, job settings (simplex or duplex, etc.) and general job data (time, username, etc.). Once the file is recognized as an encrypted PDF file, the password registered in volatile memory and is therefore deleted when the MFP/LP main power is turned off . • The user ID can be accessed from one another. After this, the decrypted data is converted to image data, stored...
... as the size of the paper for printing, job settings (simplex or duplex, etc.) and general job data (time, username, etc.). Once the file is recognized as an encrypted PDF file, the password registered in volatile memory and is therefore deleted when the MFP/LP main power is turned off . • The user ID can be accessed from one another. After this, the decrypted data is converted to image data, stored...
Design Guide
Page 54
... at the POP server before making the connection to the SMTP server (POP before SMTP), and at the SMTP server itself (SMTP authentication). • When sending image data to an SMTP server or Windows PC (SMB), it is only allowed after the MFP main power is possible to encrypt the password using a DIGEST algorithm. Print Controller Design Guide for Information Security 2-3 Scanner (MFP Models Only) 2-3-1 Overview...
... at the POP server before making the connection to the SMTP server (POP before SMTP), and at the SMTP server itself (SMTP authentication). • When sending image data to an SMTP server or Windows PC (SMB), it is only allowed after the MFP main power is possible to encrypt the password using a DIGEST algorithm. Print Controller Design Guide for Information Security 2-3 Scanner (MFP Models Only) 2-3-1 Overview...
Design Guide
Page 55
... e-mail. - In all versions of ScanRouter), or Page 55 of 86 When using the "Restrict use the TWAIN V4 driver. Require user identification when sending to an SMTP server or folder (Basic Authentication). Print Controller Design Guide for Information Security password necessary to open the encrypted PDF data at the MFP and the forwarding server software must first set as the alteration of the e-mail contents...
... e-mail. - In all versions of ScanRouter), or Page 55 of 86 When using the "Restrict use the TWAIN V4 driver. Require user identification when sending to an SMTP server or folder (Basic Authentication). Print Controller Design Guide for Information Security password necessary to open the encrypted PDF data at the MFP and the forwarding server software must first set as the alteration of the e-mail contents...
Design Guide
Page 58
... Mail Transfer Protocol) [RFC2822]: A protocol used to the job log stored in the HDD. Page 58 of e-mail over a TCP/IP network. The entry contains information on job and access logs, please refer to dictionary and brute-force attacks. scanning settings, destinations), completion status (whether completed successfully or not) and user identification (in cases where User Authentication was enabled). Print Controller Design Guide for Information...
... Mail Transfer Protocol) [RFC2822]: A protocol used to the job log stored in the HDD. Page 58 of e-mail over a TCP/IP network. The entry contains information on job and access logs, please refer to dictionary and brute-force attacks. scanning settings, destinations), completion status (whether completed successfully or not) and user identification (in cases where User Authentication was enabled). Print Controller Design Guide for Information...
Design Guide
Page 70
... the WebImageMonitor GUI. WebImageMonitor prevents such trouble by Administrators. 2-6-2 WebDocBox (MFP models only) Overview of any settings can only be introduced via a Web browser to view, capture, print, send (e-mail, FAX, forward) and delete Document Sever image files that were saved to the MFP HDD using Desk Top Editor For Production. Print Controller Design Guide for Information Security Protection Against URL...
... the WebImageMonitor GUI. WebImageMonitor prevents such trouble by Administrators. 2-6-2 WebDocBox (MFP models only) Overview of any settings can only be introduced via a Web browser to view, capture, print, send (e-mail, FAX, forward) and delete Document Sever image files that were saved to the MFP HDD using Desk Top Editor For Production. Print Controller Design Guide for Information Security Protection Against URL...
Design Guide
Page 71
... a specific IP address when the session is possible to all documents. Print Controller Design Guide for decrypting the PDF data at the PC side. When sending stored image files to the PC in accordance with a password (see 1.7.2 Document Server Documents (MFP models only) for access and clear the authentication process are allowed to send (FAX, e-mail, forward), capture or print out the documents. With the use of User...
... a specific IP address when the session is possible to all documents. Print Controller Design Guide for decrypting the PDF data at the PC side. When sending stored image files to the PC in accordance with a password (see 1.7.2 Document Server Documents (MFP models only) for access and clear the authentication process are allowed to send (FAX, e-mail, forward), capture or print out the documents. With the use of User...
Design Guide
Page 76
Print Controller Design Guide for Information Security Special pattern embedded when image is printed out MFP with optional Copy Data Security Unit installed and enabled Contract When pattern is detected, buzzer sounds and image is replaced with Copy Data Security setting disabled, ・ MFP without Copy Data Security Unit, or ・ Non-Ricoh product Buzzer Contract ‥J‥a‥n‥. ‥1‥'05 ‥‥‥ Previous deterrent feature still used Pattern cannot...
Print Controller Design Guide for Information Security Special pattern embedded when image is printed out MFP with optional Copy Data Security Unit installed and enabled Contract When pattern is detected, buzzer sounds and image is replaced with Copy Data Security setting disabled, ・ MFP without Copy Data Security Unit, or ・ Non-Ricoh product Buzzer Contract ‥J‥a‥n‥. ‥1‥'05 ‥‥‥ Previous deterrent feature still used Pattern cannot...
Design Guide
Page 78
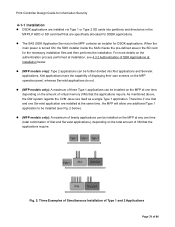
... MFP at any one time (total combination of Xlet and Servelet applications), depending on the amount of 86 Print Controller Design Guide for Information Security 4-1-1 Installation DSDK applications are installed via Type 1 or Type 2 SD cards into Xlet applications and Servelet applications. Fig. 2: Three Examples of Simultaneous Installation of Type 1 and 2 Applications Page 78 of virtual memory (VM) that are specifically allocated for DSDK...
... MFP at any one time (total combination of Xlet and Servelet applications), depending on the amount of 86 Print Controller Design Guide for Information Security 4-1-1 Installation DSDK applications are installed via Type 1 or Type 2 SD cards into Xlet applications and Servelet applications. Fig. 2: Three Examples of Simultaneous Installation of Type 1 and 2 Applications Page 78 of virtual memory (VM) that are specifically allocated for DSDK...
Design Guide
Page 81
... amount of the loop-back address (the 127.0.0.1 local address), which allows the application to edit the incoming printing data received by the MFP/LP, convert it to a different PDL, and change job control commands such as a standard feature. The SDK application creates the log files and writes them to the printer port of time has passed. Page 81 of the application. SDK...
... amount of the loop-back address (the 127.0.0.1 local address), which allows the application to edit the incoming printing data received by the MFP/LP, convert it to a different PDL, and change job control commands such as a standard feature. The SDK application creates the log files and writes them to the printer port of time has passed. Page 81 of the application. SDK...