Design Guide
Page 6
... Instructions for the multi-functional products and laser printers listed below (herein referred to as the information security of image data and other information handled internally by Ricoh MFP/LPs. Ltd. (herein referred to as Ricoh), as well as the "MFP" and "LP", respectively), which were designed and developed by Ricoh Co. external I/F) and functions described in question. Print Controller Design Guide...
... Instructions for the multi-functional products and laser printers listed below (herein referred to as the information security of image data and other information handled internally by Ricoh MFP/LPs. Ltd. (herein referred to as Ricoh), as well as the "MFP" and "LP", respectively), which were designed and developed by Ricoh Co. external I/F) and functions described in question. Print Controller Design Guide...
Design Guide
Page 8
... the external charge device I/F and external coin/card-operated devices. • External controller I/F board: Acts as the interface between the MFP and external controller. • File Format Converter: Converts the file format of image files. • RC Gate: Intermediary device connected to the MFP/LP via an Ethernet connection for performing remote diagnostic operations including firmware updates and settings changes. • SD card I/F: Used for performing service maintenance and as an...
... the external charge device I/F and external coin/card-operated devices. • External controller I/F board: Acts as the interface between the MFP and external controller. • File Format Converter: Converts the file format of image files. • RC Gate: Intermediary device connected to the MFP/LP via an Ethernet connection for performing remote diagnostic operations including firmware updates and settings changes. • SD card I/F: Used for performing service maintenance and as an...
Design Guide
Page 12
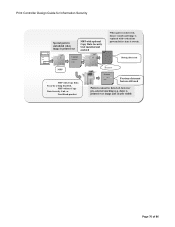
... link between SP settings and machine operations. Page 12 of machine configuration settings by the system as a FAX via the connection protocols between the principal machine function and external charge device during the image creation process. diagnostics, firmware update, settings changes). Also contains a printer language processing subsystem (e.g. Scanning can be initiated from both the operation panel and from the printing engine. Receives image data through the host interface, which...
... link between SP settings and machine operations. Page 12 of machine configuration settings by the system as a FAX via the connection protocols between the principal machine function and external charge device during the image creation process. diagnostics, firmware update, settings changes). Also contains a printer language processing subsystem (e.g. Scanning can be initiated from both the operation panel and from the printing engine. Receives image data through the host interface, which...
Design Guide
Page 13
... allows machine configuration settings to specific network-connected PC utilities. In addition, this module also makes it possible to change some MFP/LP functionality to be peformed on the MFP/LP. Print Controller Design Guide for Information Security Netfile (GWWS) WebSys WebDocBox SDK/VAS EAC As a server, GWWS provides some of the internal settings of the external controller from the MFP operation panel. GWWS...
... allows machine configuration settings to specific network-connected PC utilities. In addition, this module also makes it possible to change some MFP/LP functionality to be peformed on the MFP/LP. Print Controller Design Guide for Information Security Netfile (GWWS) WebSys WebDocBox SDK/VAS EAC As a server, GWWS provides some of the internal settings of the external controller from the MFP operation panel. GWWS...
Design Guide
Page 14
... devices. • Serial I/F for connection of 86 This arrangement prevents illegal access to directly access the memory space of Program Data from Illegal Access via an external I/F. User data, such as the Address Book data stored in the HDD/flash ROM and User Code data stored in the Image Memory is allocated specifically for each module, which can only be sent to this pre-determined set. Page 14 of peripheral devices (e.g. Print Controller Design Guide...
... devices. • Serial I/F for connection of 86 This arrangement prevents illegal access to directly access the memory space of Program Data from Illegal Access via an external I/F. User data, such as the Address Book data stored in the HDD/flash ROM and User Code data stored in the Image Memory is allocated specifically for each module, which can only be sent to this pre-determined set. Page 14 of peripheral devices (e.g. Print Controller Design Guide...
Design Guide
Page 17
... the firmware (version, type, etc.) is stored in the MFP/LP as its own, and in the case of MFP/LP options. Therefore, the update can be reinitiated using an SD card or via a remote connection. Generate MD1 ins ta lled Program using SHA-1 MD 2. Files are widely available for Information Security 1-4 Protection of power or other cause. Print Controller Design Guide for...
... the firmware (version, type, etc.) is stored in the MFP/LP as its own, and in the case of MFP/LP options. Therefore, the update can be reinitiated using an SD card or via a remote connection. Generate MD1 ins ta lled Program using SHA-1 MD 2. Files are widely available for Information Security 1-4 Protection of power or other cause. Print Controller Design Guide for...
Design Guide
Page 24
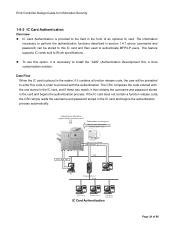
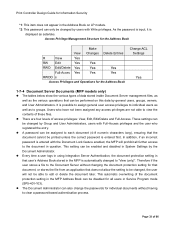
... IC card) Job + Auth. Authentication information (input from the operation panel) Information is encrypted Authentication information (stored in the IC card and begins the authentication process automatically. One server is necessary to install the "ADK" (Authentication Development Kit), a local customization solution. Info. This feature supports IC cards built to Ricoh specifications. To use this IC card and then used to authenticate MFP/LP users. Print Controller Design Guide for...
... IC card) Job + Auth. Authentication information (input from the operation panel) Information is encrypted Authentication information (stored in the IC card and begins the authentication process automatically. One server is necessary to install the "ADK" (Authentication Development Kit), a local customization solution. Info. This feature supports IC cards built to Ricoh specifications. To use this IC card and then used to authenticate MFP/LP users. Print Controller Design Guide for...
Design Guide
Page 27
... level, leaving the possibility of partial reconstruction of user information. The HDD stores data such as image data, e-mail destinations, and Address Book data containing various types of the original data. Print Controller Design Guide for example, although the MFP/LP completely erases the page location data (the storage location information necessary to access image data on the HDD), the image data itself remains in the temporary storage stored area...
... level, leaving the possibility of partial reconstruction of user information. The HDD stores data such as image data, e-mail destinations, and Address Book data containing various types of the original data. Print Controller Design Guide for example, although the MFP/LP completely erases the page location data (the storage location information necessary to access image data on the HDD), the image data itself remains in the temporary storage stored area...
Design Guide
Page 32
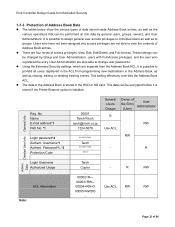
... change user passwords. Using the Extended Security settings, which are four levels of access privileges: View, Edit, Edit/Delete, and Full-Access. Data Reg. Username*1 Authent. This setting effectively overrides the Address Book ACL. It is stored in the HDD or SD card. ACL Information Note: Taroh Copier - R RW ... 00002=R--- 00003=RW-- 00004=RW-O Use ACL RW RW 00005=RWDO ... Print Controller Design Guide...
... change user passwords. Using the Extended Security settings, which are four levels of access privileges: View, Edit, Edit/Delete, and Full-Access. Data Reg. Username*1 Authent. This setting effectively overrides the Address Book ACL. It is stored in the HDD or SD card. ACL Information Note: Taroh Copier - R RW ... 00002=R--- 00003=RW-- 00004=RW-O Use ACL RW RW 00005=RWDO ... Print Controller Design Guide...
Design Guide
Page 33
.... Print Controller Design Guide for the Address Book Change ACL Settings Yes 1-7-4 Document Server Documents (MFP models only) The tables below show the various types of data stored inside Document Server management files, as well as the various operations that can be performed on LP models. *2: This password can only be changed , the user will prohibit all users in the Address Book on this data by general users, groups, owners, and User...
.... Print Controller Design Guide for the Address Book Change ACL Settings Yes 1-7-4 Document Server Documents (MFP models only) The tables below show the various types of data stored inside Document Server management files, as well as the various operations that can be performed on LP models. *2: This password can only be changed , the user will prohibit all users in the Address Book on this data by general users, groups, owners, and User...
Design Guide
Page 45
... User Authentication was enabled). In addition, it is possible to set to "Level 2", changes to the Copy/Document Server Features can only be performed by the external charge device or key counter itself (card, currency, etc.). 2-1-7 Job/Access Log Data Collection A job log entry is possible to allow or prohibit the use of B/W, full-color, two-color and single-color modes for each user. For more on the job settings (e.g. The supported file...
... User Authentication was enabled). In addition, it is possible to set to "Level 2", changes to the Copy/Document Server Features can only be performed by the external charge device or key counter itself (card, currency, etc.). 2-1-7 Job/Access Log Data Collection A job log entry is possible to allow or prohibit the use of B/W, full-color, two-color and single-color modes for each user. For more on the job settings (e.g. The supported file...
Design Guide
Page 49
... User Authentication when sending data to print out an encrypted PDF file. The username and password are sent along with the file. The print job history can then use as a unique marker for documents to set the passwords for Locked Print and Stored Print documents as well as the "page location data" for the image data stored in volatile memory and is therefore deleted when the MFP/LP main power is used...
... User Authentication when sending data to print out an encrypted PDF file. The username and password are sent along with the file. The print job history can then use as a unique marker for documents to set the passwords for Locked Print and Stored Print documents as well as the "page location data" for the image data stored in volatile memory and is therefore deleted when the MFP/LP main power is used...
Design Guide
Page 54
... sent back to the TWAIN driver. • Access to the Scanner function itself (SMTP authentication). • When sending image data to an SMTP server or Windows PC (SMB), it is turned off. 2-3-2 Data Flow Security Considerations • Forwarding operations are created for both scanning and forwarding jobs. Print Controller Design Guide for Information Security 2-3 Scanner (MFP Models Only) 2-3-1 Overview of Scanner Operations •...
... sent back to the TWAIN driver. • Access to the Scanner function itself (SMTP authentication). • When sending image data to an SMTP server or Windows PC (SMB), it is turned off. 2-3-2 Data Flow Security Considerations • Forwarding operations are created for both scanning and forwarding jobs. Print Controller Design Guide for Information Security 2-3 Scanner (MFP Models Only) 2-3-1 Overview of Scanner Operations •...
Design Guide
Page 55
Print Controller Design Guide for Information Security password necessary to open the encrypted PDF data at the MFP and the forwarding server software must first set the necessary authentication information in the MFP, whether obtained from an LDAP server. - The supported protocols are SNMPv1, v2 and v3. By requiring the operator to select from the forwarding server, Basic Authentication must be enabled at the PC...
Print Controller Design Guide for Information Security password necessary to open the encrypted PDF data at the MFP and the forwarding server software must first set the necessary authentication information in the MFP, whether obtained from an LDAP server. - The supported protocols are SNMPv1, v2 and v3. By requiring the operator to select from the forwarding server, Basic Authentication must be enabled at the PC...
Design Guide
Page 58
... a large number of e-mail for secure sending/receiving. • LDAP (Lightweight Directory Access Protocol) [RFC1777], [RFC2251]: A protocol used for accessing directory services that uses the MD5 algorithm to encrypt the challenge string and password. • DIGEST-MD5 [RFC2831]: A message digest functional algorithm developed as user address books. • SMB (Server Message Block): A protocol used to enable file sharing between Windows PCs. DIGEST-MD5 also supports realm designation...
... a large number of e-mail for secure sending/receiving. • LDAP (Lightweight Directory Access Protocol) [RFC1777], [RFC2251]: A protocol used for accessing directory services that uses the MD5 algorithm to encrypt the challenge string and password. • DIGEST-MD5 [RFC2831]: A message digest functional algorithm developed as user address books. • SMB (Server Message Block): A protocol used to enable file sharing between Windows PCs. DIGEST-MD5 also supports realm designation...
Design Guide
Page 70
... view by changing the Service mode settings in WebImageMonitor can be changed, ensuring that exceed this limit. Print Controller Design Guide for Information Security Protection Against URL Buffer Overflows URL buffer overflow attacks occur when intentionally oversized URL strings are sent to a Web server with the intent of overflowing the buffer's storage capacity, causing the server to illegally access or otherwise use a session...
... view by changing the Service mode settings in WebImageMonitor can be changed, ensuring that exceed this limit. Print Controller Design Guide for Information Security Protection Against URL Buffer Overflows URL buffer overflow attacks occur when intentionally oversized URL strings are sent to a Web server with the intent of overflowing the buffer's storage capacity, causing the server to illegally access or otherwise use a session...
Design Guide
Page 71
... capable of image data. In addition, it is possible to view Document Server data. the file attachment), as well as view, edit and delete all Web applications, it is possible to disable the password lock as well as attach a digital signature. Print Controller Design Guide for Information Security Data Flow WebDocBox supports HTTP, a protocol used by allowing connection only with users who provide a specific IP address when the...
... capable of image data. In addition, it is possible to view Document Server data. the file attachment), as well as view, edit and delete all Web applications, it is possible to disable the password lock as well as attach a digital signature. Print Controller Design Guide for Information Security Data Flow WebDocBox supports HTTP, a protocol used by allowing connection only with users who provide a specific IP address when the...
Design Guide
Page 76
...; MFP with vertical line pattern (before data is printed over image and clearly visible Page 76 of 86 date) is stored). Print Controller Design Guide for Information Security Special pattern embedded when image is printed out MFP with optional Copy Data Security Unit installed and enabled Contract When pattern is detected, buzzer sounds and image is replaced with Copy Data Security setting disabled, ・ MFP without Copy Data Security Unit, or ・ Non-Ricoh product Buzzer Contract...
...; MFP with vertical line pattern (before data is printed over image and clearly visible Page 76 of 86 date) is stored). Print Controller Design Guide for Information Security Special pattern embedded when image is printed out MFP with optional Copy Data Security Unit installed and enabled Contract When pattern is detected, buzzer sounds and image is replaced with Copy Data Security setting disabled, ・ MFP without Copy Data Security Unit, or ・ Non-Ricoh product Buzzer Contract...
Design Guide
Page 78
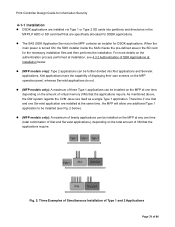
... (SDK Application Service) in the SD card for the necessary installation files and then performs the installation. When the main power is turned ON, the SDK installer inside the SAS checks the pre-defined area in the MPF contains an installer for DSDK applications. Xlet applications have the capability of displaying their own screens on the MFP operation panel, whereas Servelet applications...
... (SDK Application Service) in the SD card for the necessary installation files and then performs the installation. When the main power is turned ON, the SDK installer inside the SAS checks the pre-defined area in the MPF contains an installer for DSDK applications. Xlet applications have the capability of displaying their own screens on the MFP operation panel, whereas Servelet applications...
Design Guide
Page 81
... amount of time has passed. It is possible to create a user interface for communication with the IC Card Authentication explained in the "Function Priority Setting" so that it to a different PDL, and change job control commands such as a standard feature. Print Controller Design Guide for Information Security 4-2-3 Network Functions As mentioned above, a Type 1 SDK application is able to perform network communication either by using the GWWS...
... amount of time has passed. It is possible to create a user interface for communication with the IC Card Authentication explained in the "Function Priority Setting" so that it to a different PDL, and change job control commands such as a standard feature. Print Controller Design Guide for Information Security 4-2-3 Network Functions As mentioned above, a Type 1 SDK application is able to perform network communication either by using the GWWS...