WGT624v3 Reference Manual
Page 9
Overview of WEP Parameters D-5 Key Size ...D-6 WEP Configuration Options D-7 Wireless Channels ...D-7 WPA and WPA2 Wireless Security D-8 How Does WPA Compare to WEP D-9 How Does WPA Compare to WPA2 (IEEE 802.11i D-10 What are the Key Features ...Data Encryption Key Management D-14 Is WPA/WPA2 Perfect D-16 Product Support for WPA/WPA2 D-16 Supporting a Mixture of WPA, WPA2, and WEP Wireless Clients is Discouraged D-16 Changes to Wireless Access Points D-17 Changes to Wireless Network Adapters D-17 Changes to Wireless Client Programs D-18 Glossary Contents ix 202-10090-01, April 2005
Overview of WEP Parameters D-5 Key Size ...D-6 WEP Configuration Options D-7 Wireless Channels ...D-7 WPA and WPA2 Wireless Security D-8 How Does WPA Compare to WEP D-9 How Does WPA Compare to WPA2 (IEEE 802.11i D-10 What are the Key Features ...Data Encryption Key Management D-14 Is WPA/WPA2 Perfect D-16 Product Support for WPA/WPA2 D-16 Supporting a Mixture of WPA, WPA2, and WEP Wireless Clients is Discouraged D-16 Changes to Wireless Access Points D-17 Changes to Wireless Network Adapters D-17 Changes to Wireless Client Programs D-18 Glossary Contents ix 202-10090-01, April 2005
WGT624v3 Reference Manual
Page 16
...True Firewall with 802.11b devices or dedicating the wireless network to defend against hacker attacks. You can connect. Support for firmware upgrade. 802.11g Wireless Networking The WGT624 v3 wireless router includes an 802.11g wireless access point, providing continuous, high-speed 54 Mbps access ...keys can be turned off -limits. • Logs security incidents. Reference Manual for the 108 Mbps Wireless Firewall Router WGT624 v3 • Flash memory for Wi-Fi Protected Access (WPA) data encryption which provides strong data encryption and authentication based on a pre-shared key...
...True Firewall with 802.11b devices or dedicating the wireless network to defend against hacker attacks. You can connect. Support for firmware upgrade. 802.11g Wireless Networking The WGT624 v3 wireless router includes an 802.11g wireless access point, providing continuous, high-speed 54 Mbps access ...keys can be turned off -limits. • Logs security incidents. Reference Manual for the 108 Mbps Wireless Firewall Router WGT624 v3 • Flash memory for Wi-Fi Protected Access (WPA) data encryption which provides strong data encryption and authentication based on a pre-shared key...
WGT624v3 Reference Manual
Page 33
...please check with another nearby access point. • Mode: Select the desired wireless mode. The default is not the same as NETGEAr. • Region: Select your network's Name (SSID) to a different value. This value is NETGEAR, but NETGEAR strongly recommends that you select 108 Mbps mode, the WGT624 will... assigned to all wireless devices in a region other than the region shown here. "Open System" or "Shared Key" Check your network. This field displays the region of up to 32 alphanumeric characters. Reference Manual for the 108 Mbps Wireless Firewall Router WGT624 v3 Note:...
...please check with another nearby access point. • Mode: Select the desired wireless mode. The default is not the same as NETGEAr. • Region: Select your network's Name (SSID) to a different value. This value is NETGEAR, but NETGEAR strongly recommends that you select 108 Mbps mode, the WGT624 will... assigned to all wireless devices in a region other than the region shown here. "Open System" or "Shared Key" Check your network. This field displays the region of up to 32 alphanumeric characters. Reference Manual for the 108 Mbps Wireless Firewall Router WGT624 v3 Note:...
WGT624v3 Reference Manual
Page 34
...values. • Manual Entry Mode: Select which of the four keys will automatically be used and enter the matching WEP key information for the 108 Mbps Wireless Firewall Router WGT624 v3 • Encryption Strength: Select the WEP Encryption level: 64-bit (sometimes called 40-bit) encryption 128-bit encryption • ...selected key box. The Passphrase must be 8 to automatically configure the WEP Key(s). These values must be identical on all PCs and Access Points in the Passphrase box and click the Generate button to 63 characters in the Passphrase box. For 128 bit WEP: Enter twenty-...
...values. • Manual Entry Mode: Select which of the four keys will automatically be used and enter the matching WEP key information for the 108 Mbps Wireless Firewall Router WGT624 v3 • Encryption Strength: Select the WEP Encryption level: 64-bit (sometimes called 40-bit) encryption 128-bit encryption • ...selected key box. The Passphrase must be 8 to automatically configure the WEP Key(s). These values must be identical on all PCs and Access Points in the Passphrase box and click the Generate button to 63 characters in the Passphrase box. For 128 bit WEP: Enter twenty-...
WGT624v3 Reference Manual
Page 117
... via a wired Ethernet backbone can operate the wireless LAN in the unlicensed radio spectrum at 2.5GHz. Wireless Networking Overview The WGT624 v3 wireless router conforms to another . The maximum data rate for the 802.11b wireless link is 11 Mbps, but it will automatically back down from one access point, it moves into wired Ethernet data, acting as...
... via a wired Ethernet backbone can operate the wireless LAN in the unlicensed radio spectrum at 2.5GHz. Wireless Networking Overview The WGT624 v3 wireless router conforms to another . The maximum data rate for the 802.11b wireless link is 11 Mbps, but it will automatically back down from one access point, it moves into wired Ethernet data, acting as...
WGT624v3 Reference Manual
Page 118
... be configured with any messages that both the access point and wireless station use Open System authentication. In this is used , but may still be referred to as needed; This means the wireless station will try to associate with the ESSID ANY. Reference Manual for the 108 Mbps Wireless Firewall Router WGT624 v3 Ad Hoc Mode (Peer-to-Peer...
... be configured with any messages that both the access point and wireless station use Open System authentication. In this is used , but may still be referred to as needed; This means the wireless station will try to associate with the ESSID ANY. Reference Manual for the 108 Mbps Wireless Firewall Router WGT624 v3 Ad Hoc Mode (Peer-to-Peer...
WGT624v3 Reference Manual
Page 119
With Shared Key authentication, only those PCs that has a matching SSID. 4. Turn on the wireless station. 2. The station listens for the 108 Mbps Wireless Firewall Router WGT624 v3 • Shared Key. The station finds a message from any access points that are in Shared Key authentication mode. 802.11 Authentication The 802.11 standard defines several services that govern how...
With Shared Key authentication, only those PCs that has a matching SSID. 4. Turn on the wireless station. 2. The station listens for the 108 Mbps Wireless Firewall Router WGT624 v3 • Shared Key. The station finds a message from any access points that are in Shared Key authentication mode. 802.11 Authentication The 802.11 standard defines several services that govern how...
WGT624v3 Reference Manual
Page 120
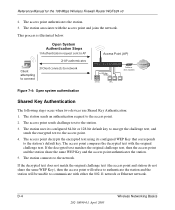
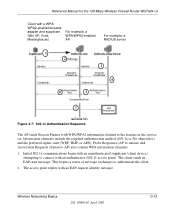
...Ethernet network. This process is illustrated below. The station sends an authentication request to network Access Point (AP) Cable/DSL ProSafeWirelessVPN Security Firewall PWR TEST IN TER N ET LNK W LA N LO CA L MODEL FVM318 ...access point and station do not share the same WEP Key), then the access point will refuse to authenticate the station and the station will be unable to communicate with the access point and joins the network. The access point compares the decrypted text with the original challenge text. Reference Manual for the 108 Mbps Wireless Firewall Router...
...Ethernet network. This process is illustrated below. The station sends an authentication request to network Access Point (AP) Cable/DSL ProSafeWirelessVPN Security Firewall PWR TEST IN TER N ET LNK W LA N LO CA L MODEL FVM318 ...access point and station do not share the same WEP Key), then the access point will refuse to authenticate the station and the station will be unable to communicate with the access point and joins the network. The access point compares the decrypted text with the original challenge text. Reference Manual for the 108 Mbps Wireless Firewall Router...
WGT624v3 Reference Manual
Page 121
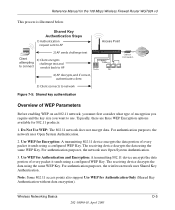
... support Use WEP for Authentication and Encryption: A transmitting 802.11 device encrypts the data portion of every packet it back to AP Access Point Cable/DSL ProSafeWirelessVPN Security Firewall PWR TEST IN TER N ET LNK W LA N LO CA L MODEL FVM318 100 ACT Enable LNK/ACT 1 2 3 4 5 6 7 8 Cable or DLS modem 4) AP decrypts, and if... receiving device decrypts the data using the same WEP Key. The receiving device decrypts the data using the same WEP Key. Reference Manual for the 108 Mbps Wireless Firewall Router WGT624 v3 This process is illustrated below.
... support Use WEP for Authentication and Encryption: A transmitting 802.11 device encrypts the data portion of every packet it back to AP Access Point Cable/DSL ProSafeWirelessVPN Security Firewall PWR TEST IN TER N ET LNK W LA N LO CA L MODEL FVM318 100 ACT Enable LNK/ACT 1 2 3 4 5 6 7 8 Cable or DLS modem 4) AP decrypts, and if... receiving device decrypts the data using the same WEP Key. The receiving device decrypts the data using the same WEP Key. Reference Manual for the 108 Mbps Wireless Firewall Router WGT624 v3 This process is illustrated below.
WGT624v3 Reference Manual
Page 122
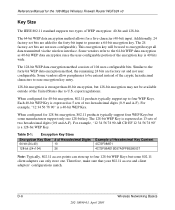
...108 Mbps Wireless Firewall Router WGT624 v3 Key Size The IEEE 802.11 standard supports two types of two hexadecimal digits (0-9 and A-F). Table D-1: Encryption Key Sizes Encryption Key Size # of Hexadecimal Digits 64-bit (24+40) 10 128-bit (24+104) 26 Example of Hexadecimal Key Content 4C72F08AE1 4C72F08AE19D57A3FF6B260037 Note: Typically, 802.11 access points... can store up to U.S. D-6 Wireless Networking Basics 202-10090-01, April 2005 export regulations.
...108 Mbps Wireless Firewall Router WGT624 v3 Key Size The IEEE 802.11 standard supports two types of two hexadecimal digits (0-9 and A-F). Table D-1: Encryption Key Sizes Encryption Key Size # of Hexadecimal Digits 64-bit (24+40) 10 128-bit (24+104) 26 Example of Hexadecimal Key Content 4C72F08AE1 4C72F08AE19D57A3FF6B260037 Note: Typically, 802.11 access points... can store up to U.S. D-6 Wireless Networking Basics 202-10090-01, April 2005 export regulations.
WGT624v3 Reference Manual
Page 123
...Medical) band between access points, then all of the 802.11 access points and all 802.11 devices that allow the maximum channel separation will decrease the amount of the signals, a node sending signals using neighboring channels (for the 108 Mbps Wireless Firewall Router WGT624 v3 WEP... Configuration Options The WEP settings must have different default WEP Keys as long as the client's WEP key 3. In other . As a result, two separate wireless networks using a particular channel will interfere...
...Medical) band between access points, then all of the 802.11 access points and all 802.11 devices that allow the maximum channel separation will decrease the amount of the signals, a node sending signals using neighboring channels (for the 108 Mbps Wireless Firewall Router WGT624 v3 WEP... Configuration Options The WEP settings must have different default WEP Keys as long as the client's WEP key 3. In other . As a result, two separate wireless networks using a particular channel will interfere...
WGT624v3 Reference Manual
Page 125
... enhancements, TKIP addresses all of 2003, all access points and client wireless adapters on client and access point products. Reference Manual for the 108 Mbps Wireless Firewall Router WGT624 v3 WPA and WPA2 offer the following benefits... operations. Products based on Wi-Fi Protected Access products. The 802.11i standard was optional. For details on existing wireless devices to change. A major problem with ... is stronger than a day and decode the encrypted messages. Wireless Networking Basics D-9 202-10090-01, April 2005 TKIP replaces WEP with the 802.11...
... enhancements, TKIP addresses all of 2003, all access points and client wireless adapters on client and access point products. Reference Manual for the 108 Mbps Wireless Firewall Router WGT624 v3 WPA and WPA2 offer the following benefits... operations. Products based on Wi-Fi Protected Access products. The 802.11i standard was optional. For details on existing wireless devices to change. A major problem with ... is stronger than a day and decode the encrypted messages. Wireless Networking Basics D-9 202-10090-01, April 2005 TKIP replaces WEP with the 802.11...
WGT624v3 Reference Manual
Page 126
...WPA2 comes from an integrated sequence of WPA and WPA2 Security? These features were either not yet ready for the 108 Mbps Wireless Firewall Router WGT624 v3 How Does WPA Compare to WPA2 (IEEE 802.11i)? Reference Manual for market or required hardware upgrades... example, user names and passwords) and authenticates wireless users before they gain access to allow a migration strategy, but mixing WEP and WPA/WPA2 is forward compatible with the WPA2 security specification. This infrastructure includes stations, access points, and authentication servers (typically RADIUS servers). Its...
...WPA2 comes from an integrated sequence of WPA and WPA2 Security? These features were either not yet ready for the 108 Mbps Wireless Firewall Router WGT624 v3 How Does WPA Compare to WPA2 (IEEE 802.11i)? Reference Manual for market or required hardware upgrades... example, user names and passwords) and authenticates wireless users before they gain access to allow a migration strategy, but mixing WEP and WPA/WPA2 is forward compatible with the WPA2 security specification. This infrastructure includes stations, access points, and authentication servers (typically RADIUS servers). Its...
WGT624v3 Reference Manual
Page 127
...the end of each plaintext message to ensure messages are generated after successful authentication and through a subsequent 4-way handshake between the station and Access Point (AP). • Data Privacy (Encryption). EAP over 802.1X is used by WPA to distribute per-session keys to those stations ... management in many home and small office environments will not be available nor desirable. Reference Manual for the 108 Mbps Wireless Firewall Router WGT624 v3 The primary information conveyed in the information elements to decide which in order to access the network. • Key management.
...the end of each plaintext message to ensure messages are generated after successful authentication and through a subsequent 4-way handshake between the station and Access Point (AP). • Data Privacy (Encryption). EAP over 802.1X is used by WPA to distribute per-session keys to those stations ... management in many home and small office environments will not be available nor desirable. Reference Manual for the 108 Mbps Wireless Firewall Router WGT624 v3 The primary information conveyed in the information elements to decide which in order to access the network. • Key management.
WGT624v3 Reference Manual
Page 128
... Tunneled Transport Layer Security (EAP-TTLS), defines how the authentication takes place. Windows XP implements 802.1x natively, and several NETGEAR switch and wireless access point products support 802.1x. Reference Manual for the 108 Mbps Wireless Firewall Router WGT624 v3 WPA/WPA2 Authentication: Enterprise-level User Authentication via EAP from a RADIUS server, for strong user authentication. D-12 202...
... Tunneled Transport Layer Security (EAP-TTLS), defines how the authentication takes place. Windows XP implements 802.1x natively, and several NETGEAR switch and wireless access point products support 802.1x. Reference Manual for the 108 Mbps Wireless Firewall Router WGT624 v3 WPA/WPA2 Authentication: Enterprise-level User Authentication via EAP from a RADIUS server, for strong user authentication. D-12 202...
WGT624v3 Reference Manual
Page 129
... begins a series of message exchanges to connect with an authenticator (802.11 access point). Initial 802.1x communications begin with an unauthenticated supplicant (client device) attempting to authenticate the client. 2. Reference Manual for the 108 Mbps Wireless Firewall Router WGT624 v3 Client with a WPA/ WPA2-enabled wireless adapter and supplicant (Win XP, Funk, Meetinghouse) For example, a WPA/WPA2...
... begins a series of message exchanges to connect with an authenticator (802.11 access point). Initial 802.1x communications begin with an unauthenticated supplicant (client device) attempting to authenticate the client. 2. Reference Manual for the 108 Mbps Wireless Firewall Router WGT624 v3 Client with a WPA/ WPA2-enabled wireless adapter and supplicant (Win XP, Funk, Meetinghouse) For example, a WPA/WPA2...
WGT624v3 Reference Manual
Page 130
...or some other EAP authentication type. 5. The access point sends an EAP-success packet (or reject packet) to the authentication server. The client can verify the client's identity using an authentication server (for the 108 Mbps Wireless Firewall Router WGT624 v3 3. As a result, you can..., WPA includes a facility (the Information Element) for 802.1x messages, which means that is synchronized between the wireless client and the wireless access point (AP). If configured to implement dynamic key exchange, the 802.1x authentication server can automatically change is sent to...
...or some other EAP authentication type. 5. The access point sends an EAP-success packet (or reject packet) to the authentication server. The client can verify the client's identity using an authentication server (for the 108 Mbps Wireless Firewall Router WGT624 v3 3. As a result, you can..., WPA includes a facility (the Information Element) for 802.1x messages, which means that is synchronized between the wireless client and the wireless access point (AP). If configured to implement dynamic key exchange, the 802.1x authentication server can automatically change is sent to...
WGT624v3 Reference Manual
Page 131
... the NIC's hardware in both the station and the access point. AES Support for WPA2 One of a unique starting unicast encryption key for each preshared key authentication. The MIC is encrypted together with sequencing rules, and a re-keying mechanism. Reference Manual for the 108 Mbps Wireless Firewall Router WGT624 v3 Temporal Key Integrity Protocol (TKIP) WPA uses...
... the NIC's hardware in both the station and the access point. AES Support for WPA2 One of a unique starting unicast encryption key for each preshared key authentication. The MIC is encrypted together with sequencing rules, and a re-keying mechanism. Reference Manual for the 108 Mbps Wireless Firewall Router WGT624 v3 Temporal Key Integrity Protocol (TKIP) WPA uses...
WGT624v3 Reference Manual
Page 132
... lose network connectivity for 60 seconds. Product Support for the 108 Mbps Wireless Firewall Router WGT624 v3 Is WPA/WPA2 Perfect? The disadvantage to supporting a mixture of WEP-based wireless networks to WPA/WPA2, a wireless AP can support both WEP and WPA/WPA2 clients at the... wireless AP determines which clients use WEP and which include disassociating each station using the access point. This is not without its vulnerabilities. If the access point receives two data packets that is no single security tactic is a definite step forward in August, 2003, NETGEAR, Inc. NETGEAR,...
... lose network connectivity for 60 seconds. Product Support for the 108 Mbps Wireless Firewall Router WGT624 v3 Is WPA/WPA2 Perfect? The disadvantage to supporting a mixture of WEP-based wireless networks to WPA/WPA2, a wireless AP can support both WEP and WPA/WPA2 clients at the... wireless AP determines which clients use WEP and which include disassociating each station using the access point. This is not without its vulnerabilities. If the access point receives two data packets that is no single security tactic is a definite step forward in August, 2003, NETGEAR, Inc. NETGEAR,...
WGT624v3 Reference Manual
Page 133
... to pass the adapter's WPA capabilities and security configuration to the Wireless Zero Configuration service. Reference Manual for the 108 Mbps Wireless Firewall Router WGT624 v3 Changes to Wireless Access Points Wireless access points must have their firmware updated to support the following : • The new WPA/WPA2 information element Wireless clients must obtain an updated network adapter driver that supports WPA. For...
... to pass the adapter's WPA capabilities and security configuration to the Wireless Zero Configuration service. Reference Manual for the 108 Mbps Wireless Firewall Router WGT624 v3 Changes to Wireless Access Points Wireless access points must have their firmware updated to support the following : • The new WPA/WPA2 information element Wireless clients must obtain an updated network adapter driver that supports WPA. For...