WGR614v5 Reference Manual
Page 10
How Does WPA Compare to WEP D-9 How Does WPA Compare to IEEE 802.11i D-10 What are the Key Features of WPA Security D-10 WPA Authentication: Enterprise-level User Authentication via 802.1x/EAP and RADIUS D-12 WPA Data Encryption Key Management D-14 Is WPA Perfect? ...D-16 Product Support for WPA D-16 Supporting a Mixture of WPA and WEP Wireless Clients D-16 Changes to Wireless Access Points D-16 Changes to Wireless Network Adapters D-17 Changes to Wireless Client Programs D-18 Glossary List of Glossary Terms G-1 Index x Contents July 2004 202-10036-01
How Does WPA Compare to WEP D-9 How Does WPA Compare to IEEE 802.11i D-10 What are the Key Features of WPA Security D-10 WPA Authentication: Enterprise-level User Authentication via 802.1x/EAP and RADIUS D-12 WPA Data Encryption Key Management D-14 Is WPA Perfect? ...D-16 Product Support for WPA D-16 Supporting a Mixture of WPA and WEP Wireless Clients D-16 Changes to Wireless Access Points D-16 Changes to Wireless Network Adapters D-17 Changes to Wireless Client Programs D-18 Glossary List of Glossary Terms G-1 Index x Contents July 2004 202-10036-01
WGR614v5 Reference Manual
Page 16
...54 Mbps Wireless Router WGR614 v5 • Ethernet connection to a wide area network (WAN) device, such as a cable modem or DSL modem. • Extensive Protocol Support. • Login capability. • Front panel LEDs for easy monitoring of status and activity. • Flash memory for Wi-Fi Protected Access (WPA) data encryption... (DoS) protection. Support for firmware upgrades. 802.11g Wireless Networking The WGR614 v5 router includes an 802.11g wireless access point, providing continuous, high-speed 54 Mbps access between your LAN to defend against hacker attacks. Automatically...
...54 Mbps Wireless Router WGR614 v5 • Ethernet connection to a wide area network (WAN) device, such as a cable modem or DSL modem. • Extensive Protocol Support. • Login capability. • Front panel LEDs for easy monitoring of status and activity. • Flash memory for Wi-Fi Protected Access (WPA) data encryption... (DoS) protection. Support for firmware upgrades. 802.11g Wireless Networking The WGR614 v5 router includes an 802.11g wireless access point, providing continuous, high-speed 54 Mbps access between your LAN to defend against hacker attacks. Automatically...
WGR614v5 Reference Manual
Page 22
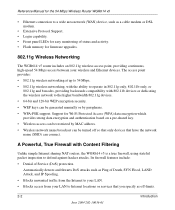
... "Implement Appropriate of networking. Configure my WGR614 v5 with the settings from snooping, hacking, or information theft. 1. To use encryption security built into browsers like Internet Explorer and Netscape. Set up the 54 Mbps Wireless Router WGR614 v5 2. Note: Secure Internet sites such as range, interference, signal quality, and security to understand. security features. Reference...
... "Implement Appropriate of networking. Configure my WGR614 v5 with the settings from snooping, hacking, or information theft. 1. To use encryption security built into browsers like Internet Explorer and Netscape. Set up the 54 Mbps Wireless Router WGR614 v5 2. Note: Secure Internet sites such as range, interference, signal quality, and security to understand. security features. Reference...
WGR614v5 Reference Manual
Page 41
...2.4 GHz cordless phones. • Away from sources of the wireless firewall. Also, WEP encryption can take slightly longer to Appendix D, "Wireless Networking Basics. For best results, place your firewall: • ...Near the center of the area in significant performance degradation or inability to wirelessly connect to the router. In planning your configuration choices. The latency, data throughput performance, and notebook power consumption of wireless...
...2.4 GHz cordless phones. • Away from sources of the wireless firewall. Also, WEP encryption can take slightly longer to Appendix D, "Wireless Networking Basics. For best results, place your firewall: • ...Near the center of the area in significant performance degradation or inability to wirelessly connect to the router. In planning your configuration choices. The latency, data throughput performance, and notebook power consumption of wireless...
WGR614v5 Reference Manual
Page 42
... network. Such distances can allow for the 54 Mbps Wireless Router WGR614 v5 Implement Appropriate Wireless Security Note: Indoors, computers can connect over the wireless link is still fully exposed to a determined snoop using specialized test equipment like wireless sniffers. • WEP. WEP Shared Key authentication and WEP data encryption will block all but the data is fully...
... network. Such distances can allow for the 54 Mbps Wireless Router WGR614 v5 Implement Appropriate Wireless Security Note: Indoors, computers can connect over the wireless link is still fully exposed to a determined snoop using specialized test equipment like wireless sniffers. • WEP. WEP Shared Key authentication and WEP data encryption will block all but the data is fully...
WGR614v5 Reference Manual
Page 43
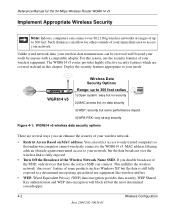
...where there is also known as shown below. Wireless Configuration 4-3 June 2004 202-10036-01 Wi-Fi Protected Access (WPA) data encryption provides strong data security. Enter a value of the browser interface. Figure 4-2: Wireless Settings menu • Name (SSID). WPA...wireless the LAN when you disable the wireless LAN, wireless devices cannot communicate with the router at all use this is : NETGEAR. • Region. The WGR614 v5 default SSID is a new standard, wireless device driver and software availability may not be used. Because this SSID for the 54 Mbps Wireless Router...
...where there is also known as shown below. Wireless Configuration 4-3 June 2004 202-10036-01 Wi-Fi Protected Access (WPA) data encryption provides strong data security. Enter a value of the browser interface. Figure 4-2: Wireless Settings menu • Name (SSID). WPA...wireless the LAN when you disable the wireless LAN, wireless devices cannot communicate with the router at all use this is : NETGEAR. • Region. The WGR614 v5 default SSID is a new standard, wireless device driver and software availability may not be used. Because this SSID for the 54 Mbps Wireless Router...
WGR614v5 Reference Manual
Page 44
... WPA-Pre-shared Key does perform authentication, uses 128-bit data encryption and dynamically changes the encryption keys making it nearly impossible to communicating with the higher bandwidth 802.11g wireless devices exclusively. A full explanation of printable characters in the Passphrase...Encryption Strength (64- Windows XP and Windows 2000 with the slower 802.11b wireless devices while still enabling 802.11g communications. • Security Options. or 128-bit WEP Data Encryption, the WGR614 v5 does perform 64- You can enable. Reference Manual for the 54 Mbps Wireless Router...
... WPA-Pre-shared Key does perform authentication, uses 128-bit data encryption and dynamically changes the encryption keys making it nearly impossible to communicating with the higher bandwidth 802.11g wireless devices exclusively. A full explanation of printable characters in the Passphrase...Encryption Strength (64- Windows XP and Windows 2000 with the slower 802.11b wireless devices while still enabling 802.11g communications. • Security Options. or 128-bit WEP Data Encryption, the WGR614 v5 does perform 64- You can enable. Reference Manual for the 54 Mbps Wireless Router...
WGR614v5 Reference Manual
Page 46
...for the 54 Mbps Wireless Router WGR614 v5 Information to Gather Before Changing Basic Wireless Settings Before customizing your wireless network in the spaces below . • Wireless Network Name (SSID The SSID, identifies the wireless network. Whichever method you are working with an existing wireless network,...information in the network will be the same for creating WEP data encryption keys. For 64-bit WEP, enter 10 hex digits (any combination of the wireless router. Not all wireless devices support the passphrase method. • Manual method. You ...
...for the 54 Mbps Wireless Router WGR614 v5 Information to Gather Before Changing Basic Wireless Settings Before customizing your wireless network in the spaces below . • Wireless Network Name (SSID The SSID, identifies the wireless network. Whichever method you are working with an existing wireless network,...information in the network will be the same for creating WEP data encryption keys. For 64-bit WEP, enter 10 hex digits (any combination of the wireless router. Not all wireless devices support the passphrase method. • Manual method. You ...
WGR614v5 Reference Manual
Page 48
... test, leave the Wireless Card Access List set to "Everyone" and the Encryption Strength set to "Wireless Channels" on page D-2. 6. Click Wireless Settings in the 54 Mbps Wireless Router WGR614 v5. The ...default SSID is case sensitive; This field determines which the wireless interface will not get a wireless connection to save your firewall. Select a channel that is not being used . Figure 4-4: Wireless Settings menu 3. Note: The SSID is NETGEAR...
... test, leave the Wireless Card Access List set to "Everyone" and the Encryption Strength set to "Wireless Channels" on page D-2. 6. Click Wireless Settings in the 54 Mbps Wireless Router WGR614 v5. The ...default SSID is case sensitive; This field determines which the wireless interface will not get a wireless connection to save your firewall. Select a channel that is not being used . Figure 4-4: Wireless Settings menu 3. Note: The SSID is NETGEAR...
WGR614v5 Reference Manual
Page 49
Typing nETgear will lose your computers for the 54 Mbps Wireless Router WGR614 v5 Note: If you are able to Configure WEP To configure WEP data encryption, follow these steps: Note: If you use a wireless computer configure WEP settings, you will be disconnected when you can configure the advanced wireless security functions of the firewall. How to obtain an...
Typing nETgear will lose your computers for the 54 Mbps Wireless Router WGR614 v5 Note: If you are able to Configure WEP To configure WEP data encryption, follow these steps: Note: If you use a wireless computer configure WEP settings, you will be disconnected when you can configure the advanced wireless security functions of the firewall. How to obtain an...
WGR614v5 Reference Manual
Page 50
You can manually or automatically program the four data encryption keys. These values must be identical on page D-4 for the 54 Mbps Wireless Router WGR614 v5 4. Enter a word or group of 0-9, a-f, or A-F). The four key boxes will be automatically populated with key values. •...the Generate button. Select which of the four keys will be active. Please refer to save your network. • Automatic - Wireless Settings encryption menu 5. NETGEAR is case sensitive; The passphrase is not the same as aa. Reference Manual for a full explanation of each of these options,...
You can manually or automatically program the four data encryption keys. These values must be identical on page D-4 for the 54 Mbps Wireless Router WGR614 v5 4. Enter a word or group of 0-9, a-f, or A-F). The four key boxes will be automatically populated with key values. •...the Generate button. Select which of the four keys will be active. Please refer to save your network. • Automatic - Wireless Settings encryption menu 5. NETGEAR is case sensitive; The passphrase is not the same as aa. Reference Manual for a full explanation of each of these options,...
WGR614v5 Reference Manual
Page 144
... point within range, regardless of its SSID. The station listens for the 54 Mbps Wireless Router WGR614 v5 WEP Wireless Security The absence of authentication methods, Open System and Shared Key. D-4 Wireless Networking Basics June 2004 202-10036-01 WPA will soon be incorporated into ... 4. Reference Manual for messages from an access point that are not encrypted. An access point must occur before the station can communicate with the network. With Open System authentication, a wireless computer can now communicate with the Ethernet network through an access point such...
... point within range, regardless of its SSID. The station listens for the 54 Mbps Wireless Router WGR614 v5 WEP Wireless Security The absence of authentication methods, Open System and Shared Key. D-4 Wireless Networking Basics June 2004 202-10036-01 WPA will soon be incorporated into ... 4. Reference Manual for messages from an access point that are not encrypted. An access point must occur before the station can communicate with the network. With Open System authentication, a wireless computer can now communicate with the Ethernet network through an access point such...
WGR614v5 Reference Manual
Page 146
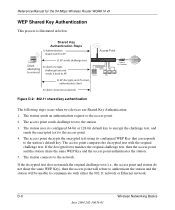
...that corresponds to the station's default key. The access point decrypts the encrypted text using its configured 64-bit or 128-bit default key to encrypt the challenge text, and sends the encrypted text to communicate with the original challenge text. The access point compares the...sends an authentication request to the station. 3. The access point sends challenge text to the access point. 2. Reference Manual for the 54 Mbps Wireless Router WGR614 v5 WEP Shared Key Authentication This process is illustrated in below. If the decrypted text matches the original challenge text, then the ...
...that corresponds to the station's default key. The access point decrypts the encrypted text using its configured 64-bit or 128-bit default key to encrypt the challenge text, and sends the encrypted text to communicate with the original challenge text. The access point compares the...sends an authentication request to the station. 3. The access point sends challenge text to the access point. 2. Reference Manual for the 54 Mbps Wireless Router WGR614 v5 WEP Shared Key Authentication This process is illustrated in below. If the decrypted text matches the original challenge text, then the ...
WGR614v5 Reference Manual
Page 147
...to the 64-bit WEP data encryption as the client's WEP key 2 and the AP's WEP key 3 is a 128-bit WEP Key. The 128-bit WEP Key is expressed as 5 sets of two hexadecimal digits (0-9 and A-F). Reference Manual for the 54 Mbps Wireless Router WGR614 v5 Key Size and ...Configuration The IEEE 802.11 standard supports two types of 104 user-configurable bits. The 64-bit WEP data encryption method, allows for 40-bit encryption, 802.11 products typically support up to encrypt/decrypt all data transmitted via the wireless interface. When...
...to the 64-bit WEP data encryption as the client's WEP key 2 and the AP's WEP key 3 is a 128-bit WEP Key. The 128-bit WEP Key is expressed as 5 sets of two hexadecimal digits (0-9 and A-F). Reference Manual for the 54 Mbps Wireless Router WGR614 v5 Key Size and ...Configuration The IEEE 802.11 standard supports two types of 104 user-configurable bits. The 64-bit WEP data encryption method, allows for 40-bit encryption, 802.11 products typically support up to encrypt/decrypt all data transmitted via the wireless interface. When...
WGR614v5 Reference Manual
Page 148
... for 802.11 products: 1. For authentication purposes, the network uses Open System Authentication. 2. Reference Manual for the 54 Mbps Wireless Router WGR614 v5 How to Use WEP Parameters Wired Equivalent Privacy (WEP) data encryption is used when the wireless devices are configured to operate in the IEEE. The receiving 802.11 device decrypts the data using...
... for 802.11 products: 1. For authentication purposes, the network uses Open System Authentication. 2. Reference Manual for the 54 Mbps Wireless Router WGR614 v5 How to Use WEP Parameters Wired Equivalent Privacy (WEP) data encryption is used when the wireless devices are configured to operate in the IEEE. The receiving 802.11 device decrypts the data using...
WGR614v5 Reference Manual
Page 149
... algorithm, but that the keys are cumbersome to add WPA support or they will implement WPA on a particular wireless LAN must use the same encryption key. NETGEAR will loose their Wi-Fi certification. In the 802.11 standard, 802.1x authentication was optional. The 802...change. Support for the 54 Mbps Wireless Router WGR614 v5 • Enhanced data privacy • Robust key management • Data origin authentication • Data integrity protection The Wi-Fi Alliance is being ratified, wireless vendors have to update the keys. For 802.11, WEP encryption is stronger than a day...
... algorithm, but that the keys are cumbersome to add WPA support or they will implement WPA on a particular wireless LAN must use the same encryption key. NETGEAR will loose their Wi-Fi certification. In the 802.11 standard, 802.1x authentication was optional. The 802...change. Support for the 54 Mbps Wireless Router WGR614 v5 • Enhanced data privacy • Robust key management • Data origin authentication • Data integrity protection The Wi-Fi Alliance is being ratified, wireless vendors have to update the keys. For 802.11, WEP encryption is stronger than a day...
WGR614v5 Reference Manual
Page 150
...a subset of the current 802.11i draft and uses certain pieces of WPA and WEP Wireless Clients These features are either not yet ready for the 54 Mbps Wireless Router WGR614 v5 How Does WPA Compare to implement. Reference Manual for market or will be forward...in the enterprise. The following security features are the Key Features of operations that encompass 802.1X/EAP authentication and sophisticated key management and encryption techniques. Temporal Key Integrity Protocol (TKIP) - These features are discussed below. Michael message integrity code (MIC) - Information in the...
...a subset of the current 802.11i draft and uses certain pieces of WPA and WEP Wireless Clients These features are either not yet ready for the 54 Mbps Wireless Router WGR614 v5 How Does WPA Compare to implement. Reference Manual for market or will be forward...in the enterprise. The following security features are the Key Features of operations that encompass 802.1X/EAP authentication and sophisticated key management and encryption techniques. Temporal Key Integrity Protocol (TKIP) - These features are discussed below. Michael message integrity code (MIC) - Information in the...
WGR614v5 Reference Manual
Page 151
...of each plaintext message to use pre-WPA 802.1X authentication and key management in order to those stations successfully authenticated. Wireless Networking Basics June 2004 202-10036-01 D-11 This obviates the need not authenticate using the Pre-shared key method ...AP). • Data Privacy (Encryption). Possible cipher suites include: WEP, TKIP, and AES (Advanced Encryption Standard). The supplicant in the station uses the authentication and cipher suite information contained in the Beacon frames is used for the 54 Mbps Wireless Router WGR614 v5 The primary information conveyed...
...of each plaintext message to use pre-WPA 802.1X authentication and key management in order to those stations successfully authenticated. Wireless Networking Basics June 2004 202-10036-01 D-11 This obviates the need not authenticate using the Pre-shared key method ...AP). • Data Privacy (Encryption). Possible cipher suites include: WEP, TKIP, and AES (Advanced Encryption Standard). The supplicant in the station uses the authentication and cipher suite information contained in the Beacon frames is used for the 54 Mbps Wireless Router WGR614 v5 The primary information conveyed...
WGR614v5 Reference Manual
Page 152
...of a preshared key. Windows XP implements 802.1x natively, and several Netgear switch and wireless access point products support 802.1x. D-12 June 2004 202-10036-01 Wireless Networking Basics Note: For environments with Optional 802.1x Port Based Network...54 Mbps Wireless Router WGR614 v5 WPA Authentication: Enterprise-level User Authentication via EAP from a RADIUS server, for example. Together, these technologies provide a framework for strong user authentication. This framework enables using 802.1x, the EAP type, such as providing a vehicle for dynamically varying data encryption...
...of a preshared key. Windows XP implements 802.1x natively, and several Netgear switch and wireless access point products support 802.1x. D-12 June 2004 202-10036-01 Wireless Networking Basics Note: For environments with Optional 802.1x Port Based Network...54 Mbps Wireless Router WGR614 v5 WPA Authentication: Enterprise-level User Authentication via EAP from a RADIUS server, for example. Together, these technologies provide a framework for strong user authentication. This framework enables using 802.1x, the EAP type, such as providing a vehicle for dynamically varying data encryption...
WGR614v5 Reference Manual
Page 154
...point is that is required. The important part to the authentication server. The access point responds by enabling a port for the 54 Mbps Wireless Router WGR614 v5 3. The access point sends an EAP-success packet (or reject packet) to upgrade an 802.1x-compliant access point.... result, you can verify the client's identity using an authentication server (e.g., RADIUS). 4. For the global encryption key, WPA includes a facility (the Information Element) for security change encryption keys as often as HTTP, DHCP, and POP3 packets, until the access point can specify any EAP type...
...point is that is required. The important part to the authentication server. The access point responds by enabling a port for the 54 Mbps Wireless Router WGR614 v5 3. The access point sends an EAP-success packet (or reject packet) to upgrade an 802.1x-compliant access point.... result, you can verify the client's identity using an authentication server (e.g., RADIUS). 4. For the global encryption key, WPA includes a facility (the Information Element) for security change encryption keys as often as HTTP, DHCP, and POP3 packets, until the access point can specify any EAP type...