User Manual
Page 5
...Networking - UPnP 3-31 Control Panel - Content Policy 3-10 Parental Control - NAT 3-22 Networking - Virtual Server 3-25 Networking - Device Security 3-27 Control Panel - CONTENTS Section 3:Configuration 3-1 Using the Configuration Utility 3-1 Log In ...3-1 Navigation ...3-2 Help, Restart, and Log ... 4:Troubleshooting 4-1 Contact Us ...4-1 Hardware Solutions 4-1 My computer is experiencing difficulty in connecting to the router 4-1 My broadband modem already uses a built-in router 4-2 Software Solutions 4-2 I would like to test to see if my Internet connection is alive 4-2...
...Networking - UPnP 3-31 Control Panel - Content Policy 3-10 Parental Control - NAT 3-22 Networking - Virtual Server 3-25 Networking - Device Security 3-27 Control Panel - CONTENTS Section 3:Configuration 3-1 Using the Configuration Utility 3-1 Log In ...3-1 Navigation ...3-2 Help, Restart, and Log ... 4:Troubleshooting 4-1 Contact Us ...4-1 Hardware Solutions 4-1 My computer is experiencing difficulty in connecting to the router 4-1 My broadband modem already uses a built-in router 4-2 Software Solutions 4-2 I would like to test to see if my Internet connection is alive 4-2...
User Manual
Page 6
... connected computers and devices. Section 1:Overview Congratulations on purchasing the Motorola Ethernet Broadband Router BR700. Firewall and NAT protection Internet Sharing Enables you the security to share your broadband Internet connection with all of convenience and independence. SECTION 1, OVERVIEW 1-1 Ethernet Broadband Router BR700 Your router is robust and secure, giving you to use the Internet without fear that stays...
... connected computers and devices. Section 1:Overview Congratulations on purchasing the Motorola Ethernet Broadband Router BR700. Firewall and NAT protection Internet Sharing Enables you the security to share your broadband Internet connection with all of convenience and independence. SECTION 1, OVERVIEW 1-1 Ethernet Broadband Router BR700 Your router is robust and secure, giving you to use the Internet without fear that stays...
User Manual
Page 9
...verifies delivery from client to server. SECTION 1 OVERVIEW Understanding Functions The various technologies and features utilized by your router require some explanation so you can be shared, therefore they are able to assign devices on the network. See...fixed address that is automatically reassigned a new IP address, ensuring smooth communication. If using your router to a device on your router. Routers provide bandwidth security by a DHCP server. Router Routers connect two networks together, or in situations where the address should never change, like print servers...
...verifies delivery from client to server. SECTION 1 OVERVIEW Understanding Functions The various technologies and features utilized by your router require some explanation so you can be shared, therefore they are able to assign devices on the network. See...fixed address that is automatically reassigned a new IP address, ensuring smooth communication. If using your router to a device on your router. Routers provide bandwidth security by a DHCP server. Router Routers connect two networks together, or in situations where the address should never change, like print servers...
User Manual
Page 29
... in, for security reasons you should change the User ID and Password. 5 Click Log In to enter the Router's Web-based Configuration Utility. 2-16 SECTION 2, INSTALLATION The default factory setting is "admin", without the quotation marks. The default factory setting is "motorola", without the ...quotation marks. 4 Enter the PASSWORD. SECTION 2 Log In INSTALLATION Log into the URL field http://192.168.20.1 (the router's default IP address) and Enter. 2 The login screen appears. 3 ...
... in, for security reasons you should change the User ID and Password. 5 Click Log In to enter the Router's Web-based Configuration Utility. 2-16 SECTION 2, INSTALLATION The default factory setting is "admin", without the quotation marks. The default factory setting is "motorola", without the ...quotation marks. 4 Enter the PASSWORD. SECTION 2 Log In INSTALLATION Log into the URL field http://192.168.20.1 (the router's default IP address) and Enter. 2 The login screen appears. 3 ...
User Manual
Page 53
... is sent out to cancel changes. The default is 8 hours. 3-22 SECTION 3, CONFIGURATION To access the screen, click NETWORKING > NAT. The default is disabled. For security purposes, turn off your ISP. The default is disabled. The time that it is assumed the session has timed out. SECTION 3 CONFIGURATION Networking - NAT Network...
... is sent out to cancel changes. The default is 8 hours. 3-22 SECTION 3, CONFIGURATION To access the screen, click NETWORKING > NAT. The default is disabled. For security purposes, turn off your ISP. The default is disabled. The time that it is assumed the session has timed out. SECTION 3 CONFIGURATION Networking - NAT Network...
User Manual
Page 57
... the first rule deletes a 'bad' packet of 32 characters for the forwarding service to enable. Networking - Click to be active. Firewall This security device shields your settings or CANCEL to perform the action. To access the screen, click NETWORKING > FIREWALL. Click to modify how and what can...by allowing you to enable. 2 Filter Action: From the drop down box, select either Discard or Forward. A firewall, working closely with a router, examines each network packet to determine whether to forward it and then click Update or Remove to cancel changes. 3-26 To add a Packet ...
... the first rule deletes a 'bad' packet of 32 characters for the forwarding service to enable. Networking - Click to be active. Firewall This security device shields your settings or CANCEL to perform the action. To access the screen, click NETWORKING > FIREWALL. Click to modify how and what can...by allowing you to enable. 2 Filter Action: From the drop down box, select either Discard or Forward. A firewall, working closely with a router, examines each network packet to determine whether to forward it and then click Update or Remove to cancel changes. 3-26 To add a Packet ...
User Manual
Page 58
... from TCP, UDP, ICMP, or All. 5 Source and Destination: Enter the IP range and Port ranges (0 to enable. UPnP ! Device Security This screen enables you to change your User ID and password and enables you to manage your configuration. Firmware Update ! Event Log Control Panel -... firmware, or backing up your router remotely. The following screens are available in Control Panel: ! SECTION 3, CONFIGURATION 3-27 Click to 65535). 6 Schedule: This is an optional feature. To update or remove an entry, select it and then click Update or Remove to be active. Device Security !
... from TCP, UDP, ICMP, or All. 5 Source and Destination: Enter the IP range and Port ranges (0 to enable. UPnP ! Device Security This screen enables you to change your User ID and password and enables you to manage your configuration. Firmware Update ! Event Log Control Panel -... firmware, or backing up your router remotely. The following screens are available in Control Panel: ! SECTION 3, CONFIGURATION 3-27 Click to 65535). 6 Schedule: This is an optional feature. To update or remove an entry, select it and then click Update or Remove to be active. Device Security !
User Manual
Page 59
...than 63 bytes. Use this option to log into the router from the Internet. The default is "motorola". SECTION 3, CONFIGURATION The default is 8080. Enables you to change the Password, used for logging into the router's web based utility. Re-enter the User Password. This... enables you to specify different ports on the router to enable. A blank user name is not allowed. SECTION 3 CONFIGURATION To access the screen, click CONTROL PANEL > DEVICE SECURITY.
...than 63 bytes. Use this option to log into the router from the Internet. The default is "motorola". SECTION 3, CONFIGURATION The default is 8080. Enables you to change the Password, used for logging into the router's web based utility. Re-enter the User Password. This... enables you to specify different ports on the router to enable. A blank user name is not allowed. SECTION 3 CONFIGURATION To access the screen, click CONTROL PANEL > DEVICE SECURITY.
User Manual
Page 64
Check all . This includes the cables from the wall to your modem, between the router and modem or router and PC. Ensure that your LEDs are tight and secured. For further information about LED descriptions, see Section 1: Overview. ! Ensure that you are using 4 to 6 wires. use the ...11 style plug using Ethernet cables and not telephone cables between the router and modem, and, if available, from the router to your cabling connections that they are not lit Red or not at www.motorola.com/broadband/networking for the latest information. Section 4:Troubleshooting This section details ...
Check all . This includes the cables from the wall to your modem, between the router and modem or router and PC. Ensure that your LEDs are tight and secured. For further information about LED descriptions, see Section 1: Overview. ! Ensure that you are using 4 to 6 wires. use the ...11 style plug using Ethernet cables and not telephone cables between the router and modem, and, if available, from the router to your cabling connections that they are not lit Red or not at www.motorola.com/broadband/networking for the latest information. Section 4:Troubleshooting This section details ...
User Manual
Page 70
...-T) provides speeds up to 10 Mbps, usually over unshielded, twisted-pair wire terminated with a network or other files to a computer. Also see MAC address. F Firewall A security software system on Internet servers. Firmware Code that enforces an access control policy between computers. Once firmware has been written onto the ROM or PROM...
...-T) provides speeds up to 10 Mbps, usually over unshielded, twisted-pair wire terminated with a network or other files to a computer. Also see MAC address. F Firewall A security software system on Internet servers. Firmware Code that enforces an access control policy between computers. Once firmware has been written onto the ROM or PROM...
User Manual
Page 73
... one or two PC Cards to portable computers. P Packet The unit of IP addresses for a reply. Laptop computers typically have traditionally been connected using some security because the IP addresses of LAN computers are invisible on the size of wiring. Multicast A data transmission sent from one set of IP addresses for...
... one or two PC Cards to portable computers. P Packet The unit of IP addresses for a reply. Laptop computers typically have traditionally been connected using some security because the IP addresses of LAN computers are invisible on the size of wiring. Multicast A data transmission sent from one set of IP addresses for...
User Manual
Page 76
..., or tunnel interface, where the packet enters and exits the network. Voice and fax have traditionally been carried over Internet Protocol is a method to create a secure network. A passenger protocol, such as printers, scanners, mice, modems, or keyboards. USB 2.0 supports data rates of 480 Mbps. TCP/IP The Transmission Control Protocol/Internet...
..., or tunnel interface, where the packet enters and exits the network. Voice and fax have traditionally been carried over Internet Protocol is a method to create a secure network. A passenger protocol, such as printers, scanners, mice, modems, or keyboards. USB 2.0 supports data rates of 480 Mbps. TCP/IP The Transmission Control Protocol/Internet...
User Manual
Page 77
...convergence of computers, telephones, and television into a single integrated information network. The bandwidth depends on shared lines. A VPN connection provides security and performance similar to information. 5-10 SECTION 5, GLOSSARY An interface to travel as a country or the whole world. VoIP enables ...large geographic area, such as discrete data packets on need and cost, but at home or in small branch offices. usually to provide a secure and fast connection; WWW World Wide Web. VoIP is usually much lower cost. SECTION 5 GLOSSARY circuit for a LAN. W WAN A ...
...convergence of computers, telephones, and television into a single integrated information network. The bandwidth depends on shared lines. A VPN connection provides security and performance similar to information. 5-10 SECTION 5, GLOSSARY An interface to travel as a country or the whole world. VoIP enables ...large geographic area, such as discrete data packets on need and cost, but at home or in small branch offices. usually to provide a secure and fast connection; WWW World Wide Web. VoIP is usually much lower cost. SECTION 5 GLOSSARY circuit for a LAN. W WAN A ...
User Guide
Page 6
... to the router 4-2 My broadband modem already uses a built-in router 4-2 Software Solutions...4-3 I would like to test to see if my Internet connection is live 4-3 I cannot access the Web-based Configuration Utility for the router 4-4 How do I extend my wireless network to : RESTRICTING WIRELESS ACCESS TO SPECIFIC USERS 3-55 WIRELESS Page Action Buttons 3-56 The SECURITY Configuration Page...
... to the router 4-2 My broadband modem already uses a built-in router 4-2 Software Solutions...4-3 I would like to test to see if my Internet connection is live 4-3 I cannot access the Web-based Configuration Utility for the router 4-4 How do I extend my wireless network to : RESTRICTING WIRELESS ACCESS TO SPECIFIC USERS 3-55 WIRELESS Page Action Buttons 3-56 The SECURITY Configuration Page...
User Guide
Page 7
... a package that accelerates your wireless network and your wireless connections are robust and secure, giving you can share files, pictures, peripherals, printers and more with Performance Enhancement technology that stays current, protects your signal might be compromised. The WR850GP comes loaded with everyone else on purchasing the Motorola® WR850GP Wireless Broadband Router or Motorola WR850G Wireless Broadband Router.1 The WR850 includes...
... a package that accelerates your wireless network and your wireless connections are robust and secure, giving you can share files, pictures, peripherals, printers and more with Performance Enhancement technology that stays current, protects your signal might be compromised. The WR850GP comes loaded with everyone else on purchasing the Motorola® WR850GP Wireless Broadband Router or Motorola WR850G Wireless Broadband Router.1 The WR850 includes...
User Guide
Page 8
...firewall - Enables you to form a Local Area Network (LAN) Security and Protection - Protects against Internet intruders with Virtual Private Network (VPN) compatibility 1-2 WR850 Connects your router to your laptop wirelessly and allows you to roam unfettered - Supports wired connection of devices...-Fi Protected Access version 2 (WPA2TM), 802.1X, and Wired Equivalent Privacy (WEP) security algorithms - Frees you to connect to 4 computers or devices - Protects your networked devices - Shares a broadband Internet (cable, DSL, or other) connection with both 802.11g and 802.11b...
...firewall - Enables you to form a Local Area Network (LAN) Security and Protection - Protects against Internet intruders with Virtual Private Network (VPN) compatibility 1-2 WR850 Connects your router to your laptop wirelessly and allows you to roam unfettered - Supports wired connection of devices...-Fi Protected Access version 2 (WPA2TM), 802.1X, and Wired Equivalent Privacy (WEP) security algorithms - Frees you to connect to 4 computers or devices - Protects your networked devices - Shares a broadband Internet (cable, DSL, or other) connection with both 802.11g and 802.11b...
User Guide
Page 22
...Configuring Computers to Communicate with the WR850. Performing the INITIAL configuration using a wireless connection is not secure and is a number between 2 and 254). After you have now connected your connection will be secure and you can safely use a second Ethernet cable and connect it to... Address (i.e., 192.168.10.x, where x is not recommended. Manual Install - Wireless Connection WARNING! If you are not running broadband to a single computer: Unplug the Ethernet cable that you have now connected the router to the modem. By default, the WR850 has a LAN IP Address of ...
...Configuring Computers to Communicate with the WR850. Performing the INITIAL configuration using a wireless connection is not secure and is a number between 2 and 254). After you have now connected your connection will be secure and you can safely use a second Ethernet cable and connect it to... Address (i.e., 192.168.10.x, where x is not recommended. Manual Install - Wireless Connection WARNING! If you are not running broadband to a single computer: Unplug the Ethernet cable that you have now connected the router to the modem. By default, the WR850 has a LAN IP Address of ...
User Guide
Page 24
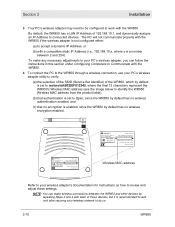
...set to Open, since the WR850 by default has no wireless authentication enabled, and (c) that no wireless encryption enabled. MODEL WR850G INPUT VOLTAGE: +5VDC, 2A PART NUMBER: AAAAAA-BBB-CC FCC ID: F2NWR850G S/N: PPPPMMYJJJSSSSSCAABBCCCC MODEL: WR850G Tested To Comply With FCC Standards FOR HOME OR OFFICE USE... WR850 has a LAN IP Address of those devices, but it is recommended to wait until after securing your PC's wireless adapter, you can make any necessary adjustments to your wireless network to connected devices. The PC will not communicate properly with the WR850 if the...
...set to Open, since the WR850 by default has no wireless authentication enabled, and (c) that no wireless encryption enabled. MODEL WR850G INPUT VOLTAGE: +5VDC, 2A PART NUMBER: AAAAAA-BBB-CC FCC ID: F2NWR850G S/N: PPPPMMYJJJSSSSSCAABBCCCC MODEL: WR850G Tested To Comply With FCC Standards FOR HOME OR OFFICE USE... WR850 has a LAN IP Address of those devices, but it is recommended to wait until after securing your PC's wireless adapter, you can make any necessary adjustments to your wireless network to connected devices. The PC will not communicate properly with the WR850 if the...
User Guide
Page 25
...configure the WR850: • For a typical WR850 configuration as a wired/wireless router, review and adjust as necessary only those configuration options designated as desired. WR850 2-11 These fields are labeled with the router. To do this, you can proceed to Section 3: Configuration to access ...automatically obtain an IP address. Installation Section 2 5 Once the PC is recommended that you will be part of your wireless network, and re-connect securely to the WR850, prior to making any and all configuration options as "commonly used" or "recommended". Field codes requiring ...
...configure the WR850: • For a typical WR850 configuration as a wired/wireless router, review and adjust as necessary only those configuration options designated as desired. WR850 2-11 These fields are labeled with the router. To do this, you can proceed to Section 3: Configuration to access ...automatically obtain an IP address. Installation Section 2 5 Once the PC is recommended that you will be part of your wireless network, and re-connect securely to the WR850, prior to making any and all configuration options as "commonly used" or "recommended". Field codes requiring ...
User Guide
Page 35
Section 3 Configuration Accessing the Web-Based Configuration Utility Logging In 1 Once the router is admin. 3 Enter the Password. The default factory setting is connected, open your web browser. Press the Enter key. The login window will appear when ... below . 4 Click OK to enter the Web-based Configuration Utility. The BASIC configuration page will appear (the WR850GP login window is motorola. The default factory setting is shown in , for security reasons you should change the User ID and Password. See below ): 2 Enter the User Name. In the URL field enter http...
Section 3 Configuration Accessing the Web-Based Configuration Utility Logging In 1 Once the router is admin. 3 Enter the Password. The default factory setting is connected, open your web browser. Press the Enter key. The login window will appear when ... below . 4 Click OK to enter the Web-based Configuration Utility. The BASIC configuration page will appear (the WR850GP login window is motorola. The default factory setting is shown in , for security reasons you should change the User ID and Password. See below ): 2 Enter the User Name. In the URL field enter http...