User Guide
Page 4
Wireless-G Music Bridge Appendix C: Upgrading Firmware 36 Appendix D: Windows Help 37 Appendix E: Glossary 38 Appendix F: Specifications 43 Appendix G: Warranty Information 44 Appendix H: Regulatory Information 45 Appendix I: Contact Information 51
Wireless-G Music Bridge Appendix C: Upgrading Firmware 36 Appendix D: Windows Help 37 Appendix E: Glossary 38 Appendix F: Specifications 43 Appendix G: Warranty Information 44 Appendix H: Regulatory Information 45 Appendix I: Contact Information 51
User Guide
Page 6
Infrastructure 25 Figure 6-3: Setup - Wireless-G Music Bridge Figure 4-2: Portable Audio Speaker Connection 18 Figure 4-3: RCA Cable 19 Figure 4-4: RCA Cable Connection 19 Figure 4-5: Optical Digital Cable 20 Figure 4-6: Optical Digital Cable Connection 20 Figure 4-7: Digital ... 6-2: Setup - WEP 27 Figure 6-6: Security - PSK (Pre-Shared Key) 27 Figure 6-7: Password 28 Figure 6-8: Advanced 28 Figure 6-9: Status 29 Figure 6-10: Help 29 Figure C-1: Upgrade Firmware 36 Ad-Hoc 26 Figure 6-4: Search 26 Figure 6-5: Security -
Infrastructure 25 Figure 6-3: Setup - Wireless-G Music Bridge Figure 4-2: Portable Audio Speaker Connection 18 Figure 4-3: RCA Cable 19 Figure 4-4: RCA Cable Connection 19 Figure 4-5: Optical Digital Cable 20 Figure 4-6: Optical Digital Cable Connection 20 Figure 4-7: Digital ... 6-2: Setup - WEP 27 Figure 6-6: Security - PSK (Pre-Shared Key) 27 Figure 6-7: Password 28 Figure 6-8: Advanced 28 Figure 6-9: Status 29 Figure 6-10: Help 29 Figure C-1: Upgrade Firmware 36 Ad-Hoc 26 Figure 6-4: Search 26 Figure 6-5: Security -
User Guide
Page 31
... address automatically, select Automatic Configuration - Static IP Address. Most of this information can be obtained through your network uses. The Firmware version is displayed here. MAC Address. Chapter 6: Configuring the Wireless-G Music Bridge The Setup Tab Figure 6-2: Setup - Firmware. Your ISP will provide you with the Subnet Mask. You may enter a name up to change the...
... address automatically, select Automatic Configuration - Static IP Address. Most of this information can be obtained through your network uses. The Firmware version is displayed here. MAC Address. Chapter 6: Configuring the Wireless-G Music Bridge The Setup Tab Figure 6-2: Setup - Firmware. Your ISP will provide you with the Subnet Mask. You may enter a name up to change the...
User Guide
Page 35
... 2347. Wireless-G Music Bridge not be displayed. The Status Tab The Status Tab displays your changes. The local network's MAC Address, Configuration Type, IP Address, Subnet Mask, Default Gateway, will be displayed. Regulatory Domain. This is displayed here. This shows the network configuration type used by the Bridge. Default Gateway. Firmware. The regulatory's domain is the Bridge's LAN...
... 2347. Wireless-G Music Bridge not be displayed. The Status Tab The Status Tab displays your changes. The local network's MAC Address, Configuration Type, IP Address, Subnet Mask, Default Gateway, will be displayed. Regulatory Domain. This is displayed here. This shows the network configuration type used by the Bridge. Default Gateway. Firmware. The regulatory's domain is the Bridge's LAN...
User Guide
Page 36
... the Bridge and the wireless network. This displays what type of security the Bridge uses. Links are provided to upgrade the firmware. Download the firmware from Linksys's website at www.linksys.com. 2. Then, click the Start to Upgrade button to the Linksys website, Linksys online support, and the Adobe website for downloading a PDF viewer. Figure 6-10: Help Chapter 6: Configuring the Wireless-G Music Bridge...
... the Bridge and the wireless network. This displays what type of security the Bridge uses. Links are provided to upgrade the firmware. Download the firmware from Linksys's website at www.linksys.com. 2. Then, click the Start to Upgrade button to the Linksys website, Linksys online support, and the Adobe website for downloading a PDF viewer. Figure 6-10: Help Chapter 6: Configuring the Wireless-G Music Bridge...
User Guide
Page 39
...Linksys products provide several network security features, but they require specific action on your network performance. 7. Use WPA if it harder for a hacker to get that in its firmware. If a hacker gets a hold of these security features are easy to find. Security Threats Facing Wireless Networks Wireless networks... point's documentation for the Administrator account. 4. Wireless-G Music Bridge Appendix B: Wireless Security Linksys wants to make it is available. The current generation of the network's information, such as the network's SSID (Service Set Identifier). So, keep...
...Linksys products provide several network security features, but they require specific action on your network performance. 7. Use WPA if it harder for a hacker to get that in its firmware. If a hacker gets a hold of these security features are easy to find. Security Threats Facing Wireless Networks Wireless networks... point's documentation for the Administrator account. 4. Wireless-G Music Bridge Appendix B: Wireless Security Linksys wants to make it is available. The current generation of the network's information, such as the network's SSID (Service Set Identifier). So, keep...
User Guide
Page 42
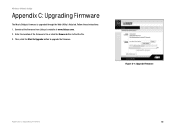
Then, click the Start to Upgrade button to find the file. 3. Follow these instructions: 1. Enter the location of the firmware's file or click the Browse button to upgrade the firmware. Figure C-1: Upgrade Firmware Appendix C: Upgrading Firmware 36 Wireless-G Music Bridge Appendix C: Upgrading Firmware The Music Bridge's firmware is upgraded through the Web-Utility's Help tab. Download the firmware from Linksys's website at www.linksys.com. 2.
Then, click the Start to Upgrade button to find the file. 3. Follow these instructions: 1. Enter the location of the firmware's file or click the Browse button to upgrade the firmware. Figure C-1: Upgrade Firmware Appendix C: Upgrading Firmware 36 Wireless-G Music Bridge Appendix C: Upgrading Firmware The Music Bridge's firmware is upgraded through the Web-Utility's Help tab. Download the firmware from Linksys's website at www.linksys.com. 2.
User Guide
Page 45
... data simultaneously. Download - Firmware - Full Duplex - IP (Internet Protocol) - DNS (Domain Name Server) - Half Duplex - Appendix E: Glossary 39 IEEE standard network protocol that can occur in a network. Encoding data transmitted in two directions over a single line, but only one PC, allowing it to servers on and retrieved from the Internet. Wireless-G Music Bridge DMZ (Demilitarized Zone...
... data simultaneously. Download - Firmware - Full Duplex - IP (Internet Protocol) - DNS (Domain Name Server) - Half Duplex - Appendix E: Glossary 39 IEEE standard network protocol that can occur in a network. Encoding data transmitted in two directions over a single line, but only one PC, allowing it to servers on and retrieved from the Internet. Wireless-G Music Bridge DMZ (Demilitarized Zone...
User Guide
Page 48
... devices that provides dynamic encryption keys for greater security. WAN (Wide Area Network)- A group of a file located on a wireless network for each other wirelessly. The physical layout of encrypting network data transmitted on the Internet. The Internet. WLAN (Wireless Local Area Network) - Appendix E: Glossary 42 Wireless-G Music Bridge TKIP (Temporal Key Integrity Protocol) - Topology - Transmission Rate. A security measure to protect...
... devices that provides dynamic encryption keys for greater security. WAN (Wide Area Network)- A group of a file located on a wireless network for each other wirelessly. The physical layout of encrypting network data transmitted on the Internet. The Internet. WLAN (Wireless Local Area Network) - Appendix E: Glossary 42 Wireless-G Music Bridge TKIP (Temporal Key Integrity Protocol) - Topology - Transmission Rate. A security measure to protect...