User Guide
Page 2
...Look for technical terms that could damage your property or the Wireless-B Broadband Router. This question mark provides you with the Wireless-B Broadband Router easier than ever. In addition to cause cancer, and birth...Wireless-B Broadband Router. All rights reserved. and certain other reproductive harm. BEFW11S4-v4-UG-41011E KL Wash hands after handling. Wireless-B Broadband Router Copyright and Trademarks Specifications are presented like this: Figure 0-1: Sample Figure Description Figure numbers and descriptions can also be found in the "List of Figures" section in the U.S. Linksys...
...Look for technical terms that could damage your property or the Wireless-B Broadband Router. This question mark provides you with the Wireless-B Broadband Router easier than ever. In addition to cause cancer, and birth...Wireless-B Broadband Router. All rights reserved. and certain other reproductive harm. BEFW11S4-v4-UG-41011E KL Wash hands after handling. Wireless-B Broadband Router Copyright and Trademarks Specifications are presented like this: Figure 0-1: Sample Figure Description Figure numbers and descriptions can also be found in the "List of Figures" section in the U.S. Linksys...
User Guide
Page 4
Wireless-B Broadband Router Appendix A:Troubleshooting 31 Common Problems and Solutions 31 Frequently Asked Questions 38 Appendix B: Wireless Security 45 Security Precautions 45 Security Threats Facing Wireless Networks 45 Appendix C: Upgrading Firmware... 48 Appendix D: Windows Help 49 Appendix E: Finding the MAC Address and IP Address for Your Ethernet Adapter 50 Windows 98 or Me Instructions 50 Windows 2000 or XP Instructions 50 For the Router's Web-based Utility 51 Appendix F: Glossary 52 Appendix G: Specifications...
Wireless-B Broadband Router Appendix A:Troubleshooting 31 Common Problems and Solutions 31 Frequently Asked Questions 38 Appendix B: Wireless Security 45 Security Precautions 45 Security Threats Facing Wireless Networks 45 Appendix C: Upgrading Firmware... 48 Appendix D: Windows Help 49 Appendix E: Finding the MAC Address and IP Address for Your Ethernet Adapter 50 Windows 98 or Me Instructions 50 Windows 2000 or XP Instructions 50 For the Router's Web-based Utility 51 Appendix F: Glossary 52 Appendix G: Specifications...
User Guide
Page 9
Wireless-B Broadband Router • Appendix G: Specifications This appendix provides the technical specifications for the Router. • Appendix H: Warranty Information This appendix supplies the warranty information for the Router.. • Appendix I: Regulatory Information This appendix supplies the regulatory information regarding the Router.. • Appendix J: Contact Information This appendix provides contact information for a variety of Linksys resources, including Technical Support. Chapter 1: Introduction 3 What's in this Guide?
Wireless-B Broadband Router • Appendix G: Specifications This appendix provides the technical specifications for the Router. • Appendix H: Warranty Information This appendix supplies the warranty information for the Router.. • Appendix I: Regulatory Information This appendix supplies the regulatory information regarding the Router.. • Appendix J: Contact Information This appendix provides contact information for a variety of Linksys resources, including Technical Support. Chapter 1: Introduction 3 What's in this Guide?
User Guide
Page 21
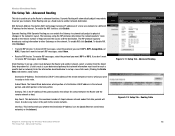
...IP address for contact between network nodes that network information must travel . Gateway. Routing Table Chapter 5: Configuring the Wireless-B Broadband Router 15 The Setup Tab - Network Address Translation (NAT) technology translates IP addresses of the gateway device that allows...specific host or network.) Enter the information described below to set up a fixed route to transmit RIP messages, select None. • Receive RIP Version. Subnet Mask. Hop Count. This determines the maximum number of the remote network or host to which portion of hops between the Router...
...IP address for contact between network nodes that network information must travel . Gateway. Routing Table Chapter 5: Configuring the Wireless-B Broadband Router 15 The Setup Tab - Network Address Translation (NAT) technology translates IP addresses of the gateway device that allows...specific host or network.) Enter the information described below to set up a fixed route to transmit RIP messages, select None. • Receive RIP Version. Subnet Mask. Hop Count. This determines the maximum number of the remote network or host to which portion of hops between the Router...
User Guide
Page 27
... changes. For information on one IP address instead of a range of the Block WAN Request Chapter 5: Configuring the Wireless-B Broadband Router The Wireless Tab - The Router sends Request to Send (RTS) frames to allow anonymous Internet requests.The Block WAN Request feature also reinforces your network...can run winipcfg or ipconfig in the port numbers fields. To check your network ports. This feature filters the Ethernet adapter's specific MAC address from accessing the Internet. Click Apply to save the changes, or Undo to Appendix E: Finding the MAC Address and...
... changes. For information on one IP address instead of a range of the Block WAN Request Chapter 5: Configuring the Wireless-B Broadband Router The Wireless Tab - The Router sends Request to Send (RTS) frames to allow anonymous Internet requests.The Block WAN Request feature also reinforces your network...can run winipcfg or ipconfig in the port numbers fields. To check your network ports. This feature filters the Ethernet adapter's specific MAC address from accessing the Internet. Click Apply to save the changes, or Undo to Appendix E: Finding the MAC Address and...
User Guide
Page 28
... click the radio button beside Enabled. Click Disabled to keep the Router from multicasting. VPN Passthrough Click Disabled to disable the function. VPN Passthrough Chapter 5: Configuring the Wireless-B Broadband Router 22 The Security Tab - IPSec Passthrough. Click Disabled to disable ...-to-Point Tunneling Protocol is enabled by default. Figure 5-23: Security Tab - Wireless-B Broadband Router feature make it more difficult for multiple transmissions to specific recipients at the IP layer. PPTP Passthrough is the method used to implement secure exchange...
... click the radio button beside Enabled. Click Disabled to keep the Router from multicasting. VPN Passthrough Click Disabled to disable the function. VPN Passthrough Chapter 5: Configuring the Wireless-B Broadband Router 22 The Security Tab - IPSec Passthrough. Click Disabled to disable ...-to-Point Tunneling Protocol is enabled by default. Figure 5-23: Security Tab - Wireless-B Broadband Router feature make it more difficult for multiple transmissions to specific recipients at the IP layer. PPTP Passthrough is the method used to implement secure exchange...
User Guide
Page 29
Descriptions of the PC running the specific application. Each name can be up public services on each line for the criteria required. Port Range Forwarding Change these settings as described here ...you wish to perform functions such as web servers, ftp servers, e-mail servers, or other specialized Internet applications. (Specialized Internet applications are described here. Application. Wireless-B Broadband Router The Applications and Gaming Tab - IP Address. For each application, enter the IP Address of each criteria are any forwarding.) To forward a port, enter ...
Descriptions of the PC running the specific application. Each name can be up public services on each line for the criteria required. Port Range Forwarding Change these settings as described here ...you wish to perform functions such as web servers, ftp servers, e-mail servers, or other specialized Internet applications. (Specialized Internet applications are described here. Application. Wireless-B Broadband Router The Applications and Gaming Tab - IP Address. For each application, enter the IP Address of each criteria are any forwarding.) To forward a port, enter ...
User Guide
Page 30
... to the appropriate computer. Chapter 5: Configuring the Wireless-B Broadband Router The Applications and Gaming Tab - Enter the starting and ending Triggered Range numbers and the Forwarded Range numbers of protocol you wish to use for specific port numbers. Choose or enter the Application in ...these changes, or click the Cancel Changes button to give each application: TCP or UDP. When finished making your changes. Wireless-B Broadband Router The Applications and Gaming Tab - Port Triggering Port Triggering Port Triggering is used for common applications. For this type of ...
... to the appropriate computer. Chapter 5: Configuring the Wireless-B Broadband Router The Applications and Gaming Tab - Enter the starting and ending Triggered Range numbers and the Forwarded Range numbers of protocol you wish to use for specific port numbers. Choose or enter the Application in ...these changes, or click the Cancel Changes button to give each application: TCP or UDP. When finished making your changes. Wireless-B Broadband Router The Applications and Gaming Tab - Port Triggering Port Triggering Port Triggering is used for common applications. For this type of ...
User Guide
Page 31
...a remote location. To enable Remote Upgrade, select Enabled. Management Chapter 5: Configuring the Wireless-B Broadband Router 25 The Applications and Gaming Tab - Local Router Access. You can change when using UPnP features, select Enable. IMPORTANT: Enabling remote ... manage specific Router functions for access and security. To enable Remote Administration, select Enabled. Management This section of one network user to be exposed to security, this may change the Router's password from somewhere else on the Internet. Wireless-B Broadband Router The Applications...
...a remote location. To enable Remote Upgrade, select Enabled. Management Chapter 5: Configuring the Wireless-B Broadband Router 25 The Applications and Gaming Tab - Local Router Access. You can change when using UPnP features, select Enable. IMPORTANT: Enabling remote ... manage specific Router functions for access and security. To enable Remote Administration, select Enabled. Management This section of one network user to be exposed to security, this may change the Router's password from somewhere else on the Internet. Wireless-B Broadband Router The Applications...
User Guide
Page 40
...services to use . This would enter 100 in the field provided. Go to a specific computer. Access the Router's web-based utility by going to use is 192.168.1.100, you want the ...applications you to set up online game hosting or use other Internet applications. Wireless-B Broadband Router 7. You can get the information on getting an IP address. 6. Enter ... click the Save Settings button. 8. Check the protocol you will be setting up port forwarding through the Router's web-based utility. I need to set up online game hosting or use a certain Internet application:...
...services to use . This would enter 100 in the field provided. Go to a specific computer. Access the Router's web-based utility by going to use is 192.168.1.100, you want the ...applications you to set up online game hosting or use other Internet applications. Wireless-B Broadband Router 7. You can get the information on getting an IP address. 6. Enter ... click the Save Settings button. 8. Check the protocol you will be setting up port forwarding through the Router's web-based utility. I need to set up online game hosting or use a certain Internet application:...
User Guide
Page 51
...Enable MAC Address Filtering. 5. Use WPA if it harder for "beacon messages". Change the administrator's password regularly. Wireless-B Broadband Router Appendix B: Wireless Security Linksys wants to make it is a complete list of security precautions to take : Change the administrator's password regularly.... information. With every wireless networking device you can be followed): 1. If a hacker gets a hold of Linksys products provide several network security features, but they require specific action on implementing these security features are easy to the router or access point's ...
...Enable MAC Address Filtering. 5. Use WPA if it harder for "beacon messages". Change the administrator's password regularly. Wireless-B Broadband Router Appendix B: Wireless Security Linksys wants to make it is a complete list of security precautions to take : Change the administrator's password regularly.... information. With every wireless networking device you can be followed): 1. If a hacker gets a hold of Linksys products provide several network security features, but they require specific action on implementing these security features are easy to the router or access point's ...
User Guide
Page 59
... to be accessed, managed, and updated. The capability of computers. A protocol that its contents can increase wireless efficiency. DSL (Digital Subscriber Line) - Wireless-B Broadband Router Buffer - CSMA/CA (Carrier Sense Multiple Access/Collision Avoidance) - Daisy Chain - Cable Modem - A method... transmission technology that is organized so that lets one device on broadband connection over a network. DDNS (Dynamic Domain Name System) - Default Gateway - DHCP (Dynamic Host Configuration Protocol) - A specific name for a network of having a website, FTP, or ...
... to be accessed, managed, and updated. The capability of computers. A protocol that its contents can increase wireless efficiency. DSL (Digital Subscriber Line) - Wireless-B Broadband Router Buffer - CSMA/CA (Carrier Sense Multiple Access/Collision Avoidance) - Daisy Chain - Cable Modem - A method... transmission technology that is organized so that lets one device on broadband connection over a network. DDNS (Dynamic Domain Name System) - Default Gateway - DHCP (Dynamic Host Configuration Protocol) - A specific name for a network of having a website, FTP, or ...
User Guide
Page 61
Wireless-B Broadband Router IPCONFIG - IPSec (Internet Protocol Security) - LAN (Local Area Network) - One million bits per second; NAT (Network Address Translation) - Node - An Internet utility used in wireless networking ...to a group of lower-speed data streams, which a computer uses a specific application on a computer or networking device used to implement secure exchange of... Service Provider) - The computers and networking products that displays the IP address for Linksys products. MAC (Media Access Control) Address - Mbps (Megabits Per Second) - ...
Wireless-B Broadband Router IPCONFIG - IPSec (Internet Protocol Security) - LAN (Local Area Network) - One million bits per second; NAT (Network Address Translation) - Node - An Internet utility used in wireless networking ...to a group of lower-speed data streams, which a computer uses a specific application on a computer or networking device used to implement secure exchange of... Service Provider) - The computers and networking products that displays the IP address for Linksys products. MAC (Media Access Control) Address - Mbps (Megabits Per Second) - ...
User Guide
Page 64
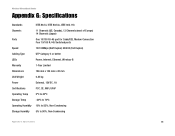
Wireless-B Broadband Router Appendix G: Specifications Standards IEEE 802.3, IEEE 802.3u, IEEE 802.11b Channels 11 Channels (US, Canada), 13 Channels (most of ...45 Switched ports Speed 10/100Mbps (Half Duplex) 20/200 (Full Duplex) Cabling Type UTP Category 5 or better LEDs Power, Internet, Ethernet, Wireless-B Warranty 1-Year Limited Dimensions 186 mm x 154 mm x 48 mm Unit Weight 0.45 kg Power External, 12V DC, 1A Certifications FCC,...20ºC to 70ºC Operating Humidity 10% to 85%, Non-Condensing Storage Humidity 5% to 90%, Non-Condensing Appendix G: Specifications 58
Wireless-B Broadband Router Appendix G: Specifications Standards IEEE 802.3, IEEE 802.3u, IEEE 802.11b Channels 11 Channels (US, Canada), 13 Channels (most of ...45 Switched ports Speed 10/100Mbps (Half Duplex) 20/200 (Full Duplex) Cabling Type UTP Category 5 or better LEDs Power, Internet, Ethernet, Wireless-B Warranty 1-Year Limited Dimensions 186 mm x 154 mm x 48 mm Unit Weight 0.45 kg Power External, 12V DC, 1A Certifications FCC,...20ºC to 70ºC Operating Humidity 10% to 85%, Non-Condensing Storage Humidity 5% to 90%, Non-Condensing Appendix G: Specifications 58
User Guide
Page 65
... to You. Wireless-B Broadband Router Appendix H: Warranty Information Linksys warrants to You that the Product will be free of vulnerability to intrusion or attack. If You are responsible for Linksys at its essential purpose. Linksys pays for a period of one year (the "Warranty Period"), your original proof of purchase. This warranty gives You specific legal rights, and...
... to You. Wireless-B Broadband Router Appendix H: Warranty Information Linksys warrants to You that the Product will be free of vulnerability to intrusion or attack. If You are responsible for Linksys at its essential purpose. Linksys pays for a period of one year (the "Warranty Period"), your original proof of purchase. This warranty gives You specific legal rights, and...
User Guide
Page 66
.... EC DECLARATION OF CONFORMITY (EUROPE) Linksys declares that interference will not occur in a particular installation. The use of this equipment does cause harmful interference to the Canadian regulations. Wireless-B Broadband Router Appendix I : Regulatory Information 60 Appendix I : Regulatory Information FCC STATEMENT This product has been tested and complies with the specifications for Radio equipment. If this...
.... EC DECLARATION OF CONFORMITY (EUROPE) Linksys declares that interference will not occur in a particular installation. The use of this equipment does cause harmful interference to the Canadian regulations. Wireless-B Broadband Router Appendix I : Regulatory Information 60 Appendix I : Regulatory Information FCC STATEMENT This product has been tested and complies with the specifications for Radio equipment. If this...