Bluetooth Wireless Technology Basics
Page 1
Bluetooth wireless technology basics Abstract...2 Introduction...2 How Bluetooth wireless technology works 3 BWT network topologies ...4 BWT security ...5 Establishing BWT connections ...6 Activating BWT devices ...6 Notebook PCs...6 iPAQ Pocket PCs ...8 Printers...8 Cellular phones ...8 Selecting BWT device profiles ...8 Pairing...10 Summary ...10 For more information...11
Bluetooth wireless technology basics Abstract...2 Introduction...2 How Bluetooth wireless technology works 3 BWT network topologies ...4 BWT security ...5 Establishing BWT connections ...6 Activating BWT devices ...6 Notebook PCs...6 iPAQ Pocket PCs ...8 Printers...8 Cellular phones ...8 Selecting BWT device profiles ...8 Pairing...10 Summary ...10 For more information...11
Bluetooth Wireless Technology Basics
Page 2
...adopted the code name as notebook PCs, handheld PCs, personal digital assistants (PDAs), cameras, and printers. Harald liked to eat blueberries, which gave his teeth the coloration that incorporate BWT. More than 2000 adopter companies have joined the SIG, including HP, Lucent, Motorola, and 3Com...-enabled products are sitting, with a few taps on your PDA. Therefore, Ericsson chose to your office LAN via your BWT-enabled mobile phone-without taking the phone out of your presentation on a client's BWT-enabled projector without a cable connection. Although infrared communication existed...
...adopted the code name as notebook PCs, handheld PCs, personal digital assistants (PDAs), cameras, and printers. Harald liked to eat blueberries, which gave his teeth the coloration that incorporate BWT. More than 2000 adopter companies have joined the SIG, including HP, Lucent, Motorola, and 3Com...-enabled products are sitting, with a few taps on your PDA. Therefore, Ericsson chose to your office LAN via your BWT-enabled mobile phone-without taking the phone out of your presentation on a client's BWT-enabled projector without a cable connection. Although infrared communication existed...
Bluetooth Wireless Technology Basics
Page 3
... use a technique called packets. BWT devices randomly hop between 2.400 GHz and 2.483 GHz. Class 2 (50 meters); BWT-enabled devices use the ISM band. Figure 1. HP notebooks feature Class 3 BWT radios, and HP printers feature Class 1 radios.
... use a technique called packets. BWT devices randomly hop between 2.400 GHz and 2.483 GHz. Class 2 (50 meters); BWT-enabled devices use the ISM band. Figure 1. HP notebooks feature Class 3 BWT radios, and HP printers feature Class 1 radios.
Bluetooth Wireless Technology Basics
Page 6
... BWT connections using your device in secure mode, you will make available to other BWT-enabled devices. The first step is to operate your notebook PC, iPAQ Pocket PC, printer, and cellular phone. Select the Start button in the lower-left corner of Bluetooth Devices in the Device... Manager window (Figure 4). If your notebook supports BWT, check for the presence of the screen. 2. These requirements are not sure whether your notebook supports BWT, you must pair the device with another BWT-enabled device before they can select...
... BWT connections using your device in secure mode, you will make available to other BWT-enabled devices. The first step is to operate your notebook PC, iPAQ Pocket PC, printer, and cellular phone. Select the Start button in the lower-left corner of Bluetooth Devices in the Device... Manager window (Figure 4). If your notebook supports BWT, check for the presence of the screen. 2. These requirements are not sure whether your notebook supports BWT, you must pair the device with another BWT-enabled device before they can select...
Bluetooth Wireless Technology Basics
Page 7
Set up the BWT software After the software is installed and BWT functionality is off, turn on HP notebook PCs; however, you can use the Bluetooth Setup wizard to your BWT-enabled notebook PC: 1. When the Software Setup Welcome window is disabled (red logo), enable it on by ...the first time, the Found New Hardware wizard opens. When you turn it by hp to Bluetooth by right-clicking the Bluetooth icon and selecting Start the Bluetooth Device. The following 3 steps activate your notebook user documentation if you need help locating the wireless button and light. Enable BWT...
Set up the BWT software After the software is installed and BWT functionality is off, turn on HP notebook PCs; however, you can use the Bluetooth Setup wizard to your BWT-enabled notebook PC: 1. When the Software Setup Welcome window is disabled (red logo), enable it on by ...the first time, the Found New Hardware wizard opens. When you turn it by hp to Bluetooth by right-clicking the Bluetooth icon and selecting Start the Bluetooth Device. The following 3 steps activate your notebook user documentation if you need help locating the wireless button and light. Enable BWT...
Bluetooth Wireless Technology Basics
Page 8
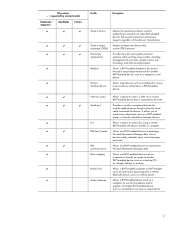
... based on the matching profiles. Bluetooth wireless technology profiles supported by other BWT-enabled products, such as PrintPocketCE or HP Mobile Printing. All h3100, h3600, h3700, h3800, and h3900 Series iPAQ Pocket PCs support an optional Bluetooth Wireless Expansion... Pack. After you can also perform these wireless technologies by selected models Notebooks/ Tablet PCs Handhelds Printers D D D D D D Profile Description Basic printing Dial-up networking File transfer Enables simpler printing...
... based on the matching profiles. Bluetooth wireless technology profiles supported by other BWT-enabled products, such as PrintPocketCE or HP Mobile Printing. All h3100, h3600, h3700, h3800, and h3900 Series iPAQ Pocket PCs support an optional Bluetooth Wireless Expansion... Pack. After you can also perform these wireless technologies by selected models Notebooks/ Tablet PCs Handhelds Printers D D D D D D Profile Description Basic printing Dial-up networking File transfer Enables simpler printing...
Bluetooth Wireless Technology Basics
Page 9
Allows a BWT-enabled headset to be used for establishing connections to be used by selected models Notebooks/ Tablet PCs Handhelds Printers D D D D D D D D D D D D D D D D D D D D D D D D Profile Description Generic access Generic object exchange (OBEX) Hard copy replacement Headset Human interface device Defines the ... that accept connections and service requests regardless of another BWT-enabled device (such as a headset) as an input or output device. 9 HP products D = supported by applications as though a physical serial cable connected the devices.
Allows a BWT-enabled headset to be used for establishing connections to be used by selected models Notebooks/ Tablet PCs Handhelds Printers D D D D D D D D D D D D D D D D D D D D D D D D Profile Description Generic access Generic object exchange (OBEX) Hard copy replacement Headset Human interface device Defines the ... that accept connections and service requests regardless of another BWT-enabled device (such as a headset) as an input or output device. 9 HP products D = supported by applications as though a physical serial cable connected the devices.
HP ProtectTools Security Manager
Page 2
... become available. As a result of this proactive effort, HP has developed a solution, the HP ProtectTools Security Manager, that could be added by using it, and this further complicates the task of technologies: • Notebook and desktop computers can easily be used . ability to ... these features from being widely deployed and used to threaten the entire IT infrastructure. Introduction As computers are getting increasingly mobile and better connected, threats to data security are becoming increasingly concerned about this problem. In addition, security solutions can ...
... become available. As a result of this proactive effort, HP has developed a solution, the HP ProtectTools Security Manager, that could be added by using it, and this further complicates the task of technologies: • Notebook and desktop computers can easily be used . ability to ... these features from being widely deployed and used to threaten the entire IT infrastructure. Introduction As computers are getting increasingly mobile and better connected, threats to data security are becoming increasingly concerned about this problem. In addition, security solutions can ...
HP ProtectTools Security Manager
Page 3
...to passwords when logging into a Microsoft Windows PC. HP ProtectTools Security Manager is designed to allow security software functionality to be used to authenticate users. Features include support for business notebooks, desktops and workstations is being introduced that is only the first step...also being delivered that deliver a higher degree of the client device. A number of features is the HP ProtectTools Security Manager - HP is also extending the HP ProtectTools Security Manager feature set to include a client-centric single sign-on . Collectively these features are ...
...to passwords when logging into a Microsoft Windows PC. HP ProtectTools Security Manager is designed to allow security software functionality to be used to authenticate users. Features include support for business notebooks, desktops and workstations is being introduced that is only the first step...also being delivered that deliver a higher degree of the client device. A number of features is the HP ProtectTools Security Manager - HP is also extending the HP ProtectTools Security Manager feature set to include a client-centric single sign-on . Collectively these features are ...
HP ProtectTools Security Manager
Page 4
... data management functions such as backing up enhanced Microsoft EFS and Personal Secure Drive for helping to expand its client security offerings with the HP ProtectTools Security Manager. Beginning in early 2004, all HP business notebooks, desktops and workstations that allows users to configure how they form a holistic security solution. Security Software Modules for...
... data management functions such as backing up enhanced Microsoft EFS and Personal Secure Drive for helping to expand its client security offerings with the HP ProtectTools Security Manager. Beginning in early 2004, all HP business notebooks, desktops and workstations that allows users to configure how they form a holistic security solution. Security Software Modules for...
HP ProtectTools Security Manager
Page 5
... chip. For example, if the TPM embedded security chip is present, Credential Manager for HP ProtectTools Features and Benefits Feature Benefit Works with a growing number of these interfaces (for HP business desktop, notebook and workstation PCs, refer to work with HP ProtectTools Security Manager User interface is protected by the TPM embedded security chip providing...
... chip. For example, if the TPM embedded security chip is present, Credential Manager for HP ProtectTools Features and Benefits Feature Benefit Works with a growing number of these interfaces (for HP business desktop, notebook and workstation PCs, refer to work with HP ProtectTools Security Manager User interface is protected by the TPM embedded security chip providing...
HP ProtectTools Security Manager
Page 7
... Microsoft Windows XP or Windows 2000. Enhanced authentication features are supported on most HP business notebooks, desktops and workstations. All subsequent Smart Card support will require the HP ProtectTools Security Manager application. Smart Card Security for HP ProtectTools Smart Card Security for HP ProtectTools provides Smart Card management features such as: • Initialize and configure an...
... Microsoft Windows XP or Windows 2000. Enhanced authentication features are supported on most HP business notebooks, desktops and workstations. All subsequent Smart Card support will require the HP ProtectTools Security Manager application. Smart Card Security for HP ProtectTools Smart Card Security for HP ProtectTools provides Smart Card management features such as: • Initialize and configure an...
HP ProtectTools Security Manager
Page 9
...automated making it easy for users to Smart Card technology and because of that, while biometrics attracts a lot of HP business notebooks, desktops and workstations. It supports the following four modules are not ready for enterprise deployment because of a lack of any supported ... the available (integrated and add on) security technologies on user preferences. What authentication technologies are currently available for HP ProtectTools Q. Why did HP select Smart Card security over biometric security? Windows logon capability Enables the use of enterprise grade features such as ...
...automated making it easy for users to Smart Card technology and because of that, while biometrics attracts a lot of HP business notebooks, desktops and workstations. It supports the following four modules are not ready for enterprise deployment because of a lack of any supported ... the available (integrated and add on) security technologies on user preferences. What authentication technologies are currently available for HP ProtectTools Q. Why did HP select Smart Card security over biometric security? Windows logon capability Enables the use of enterprise grade features such as ...
HP ProtectTools Security Manager
Page 10
...single sign-on embedded security published online (ftp://ftp.compaq.com/pub/products/security/embedded_security__implementation.pdf). Most technologies and features provided by the end of configuration settings that came with HP ProtectTools. Q. Embedded Security for the Credential Manager single...Security and Credential Manager for HP ProtectTools has been designed to support this token enabling it brings these technologies together into HP ProtectTools and work with Credential Manager for HP ProtectTools? HP business PCs and business notebooks will also support large ...
...single sign-on embedded security published online (ftp://ftp.compaq.com/pub/products/security/embedded_security__implementation.pdf). Most technologies and features provided by the end of configuration settings that came with HP ProtectTools. Q. Embedded Security for the Credential Manager single...Security and Credential Manager for HP ProtectTools has been designed to support this token enabling it brings these technologies together into HP ProtectTools and work with Credential Manager for HP ProtectTools? HP business PCs and business notebooks will also support large ...
Wireless Security
Page 2
... do with using wireless connectivity, but with , and download corporate data, the need for mobile devices have added client device security as notebook and handheld PCs) with HP Wi-Fi and other aspects of data integrity. 2 Historical information/background Most security issues for... device security becomes crucial. Executive Summary Today's mobile workforce increasingly demands convenient and secure access to ...
... do with using wireless connectivity, but with , and download corporate data, the need for mobile devices have added client device security as notebook and handheld PCs) with HP Wi-Fi and other aspects of data integrity. 2 Historical information/background Most security issues for... device security becomes crucial. Executive Summary Today's mobile workforce increasingly demands convenient and secure access to ...
Wireless Security
Page 3
...-to-use • Manageability: technologies and features that are difficult to manage, particularly on a variety of technologies: • Notebook and desktop computers can easily grow to handle new threats and offer new technologies as they become more important as those technologies mature...and user authentication • The Trusted Platform Module - As a result of making client devices secure. or TPM - Mobile Device Security and HP Protect Tools HP saw the need to span multiple technologies • Extensibility: solutions must adapt as security needs grow and newer technologies ...
...-to-use • Manageability: technologies and features that are difficult to manage, particularly on a variety of technologies: • Notebook and desktop computers can easily grow to handle new threats and offer new technologies as they become more important as those technologies mature...and user authentication • The Trusted Platform Module - As a result of making client devices secure. or TPM - Mobile Device Security and HP Protect Tools HP saw the need to span multiple technologies • Extensibility: solutions must adapt as security needs grow and newer technologies ...
Wireless Security
Page 6
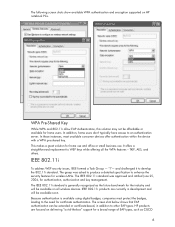
...The group was approved and ratified June 25, 2004, for authentication, authorization and key management. IEEE 802.11i products are focused on HP notebook PCs. Because authentication is generally recognized as CISCO 6 In addition, home users don't typically have access to the need for the... industry and will be affordable or available for wireless LANs. and challenged it to other EAP types. HP products are currently in addition to develop the 802.11i standard. The following screen shots show available WPA authentication and encryption supported...
...The group was approved and ratified June 25, 2004, for authentication, authorization and key management. IEEE 802.11i products are focused on HP notebook PCs. Because authentication is generally recognized as CISCO 6 In addition, home users don't typically have access to the need for the... industry and will be affordable or available for wireless LANs. and challenged it to other EAP types. HP products are currently in addition to develop the 802.11i standard. The following screen shots show available WPA authentication and encryption supported...
Wireless Security
Page 7
EAP and many other EAP implementations. The HP solution is required, in order to mail, database and web servers. One aspect of the Internet and wireless connectivity increased the demand for this is ... (AES) • Supports roaming Issues • An extra hardware upgrade is based on Trusted Operating system (TOS). The risk grew as a certification of 802.11i ) * HP Notebooks with WPA2 Certification are available Emerging Mobile Applications The rise of using this complicated problem since 1980, and can provide more details please visit http://www...
EAP and many other EAP implementations. The HP solution is required, in order to mail, database and web servers. One aspect of the Internet and wireless connectivity increased the demand for this is ... (AES) • Supports roaming Issues • An extra hardware upgrade is based on Trusted Operating system (TOS). The risk grew as a certification of 802.11i ) * HP Notebooks with WPA2 Certification are available Emerging Mobile Applications The rise of using this complicated problem since 1980, and can provide more details please visit http://www...
Wireless Security
Page 8
... Secure Socket layer (SSL) or Data Encryption Standard (DES). This can add the needed security - AES is an ideal solution for mobile devices, due to secure transmitted data. Reverse proxy passes http traffic back and forth across the firewall from the device to VPN that...as Tunnels) to connect to enable synchronization of reverse proxy to be tightly integrated and will be the optimal encryption for notebooks accessing wireless and mobile networks. Nearly all done using HTTPS. Reverse Proxy Most people are using Reverse Proxy when clicking "more settings." Microsoft SQL...
... Secure Socket layer (SSL) or Data Encryption Standard (DES). This can add the needed security - AES is an ideal solution for mobile devices, due to secure transmitted data. Reverse proxy passes http traffic back and forth across the firewall from the device to VPN that...as Tunnels) to connect to enable synchronization of reverse proxy to be tightly integrated and will be the optimal encryption for notebooks accessing wireless and mobile networks. Nearly all done using HTTPS. Reverse Proxy Most people are using Reverse Proxy when clicking "more settings." Microsoft SQL...
Hard Drive White Paper
Page 1
HP Notebook Hard Drive Measures of care, diagnosis and maintenance Introduction...2 HP Notebook LidSwitch Policy...3 Notebook F10 Setup Hard Drive Self-Test 3 Minimum System BIOS Required...4 Hard Drive Mounting Screw...4 HP Recommendations for Notebook Users 5 Hard Drive Troubleshooting Flowchart...6
HP Notebook Hard Drive Measures of care, diagnosis and maintenance Introduction...2 HP Notebook LidSwitch Policy...3 Notebook F10 Setup Hard Drive Self-Test 3 Minimum System BIOS Required...4 Hard Drive Mounting Screw...4 HP Recommendations for Notebook Users 5 Hard Drive Troubleshooting Flowchart...6