User Manual
Page 2
Table of Contents Chapter 1Introduction 3 1.1 Package Contents 3 1.2 Features 3 1.3 Specifications 3 1.4 Physical Description 4 Chapter 2Wireless LAN Access Point Connection 5 Chapter 3 Wireless LAN Access Point Configuration 6 3.1 Getting Started 6 3.2 Configuring the Access Point 10 3.2.1 Status and Information 10 3.2.2 Wireless Setting 10 3.2.3 Advanced Setting 17 3.2.4 Security 19 3.2.5 MAC Address Filtering 24 3.2.6 System Utility 25 3.2.7 Configuration Tool 27 3.2.8 Firmware Upgrade 28 3.2.9 Reset 29 Chapter 4 Trouble shooting 30
Table of Contents Chapter 1Introduction 3 1.1 Package Contents 3 1.2 Features 3 1.3 Specifications 3 1.4 Physical Description 4 Chapter 2Wireless LAN Access Point Connection 5 Chapter 3 Wireless LAN Access Point Configuration 6 3.1 Getting Started 6 3.2 Configuring the Access Point 10 3.2.1 Status and Information 10 3.2.2 Wireless Setting 10 3.2.3 Advanced Setting 17 3.2.4 Security 19 3.2.5 MAC Address Filtering 24 3.2.6 System Utility 25 3.2.7 Configuration Tool 27 3.2.8 Firmware Upgrade 28 3.2.9 Reset 29 Chapter 4 Trouble shooting 30
User Manual
Page 3
...use user interface and allows users to multiple wireless and wired computers. y Support 802.3af Power over Ethnernet (EW-7206PDg) y Built-in case of features, this access point to build up a wireless LAN. This product provides easy to use ...this product is the best choice for better network link quality so that you to consolidate the wireless network security. y Supports Web-based configuration. 1.3 ...
...use user interface and allows users to multiple wireless and wired computers. y Support 802.3af Power over Ethnernet (EW-7206PDg) y Built-in case of features, this access point to build up a wireless LAN. This product provides easy to use ...this product is the best choice for better network link quality so that you to consolidate the wireless network security. y Supports Web-based configuration. 1.3 ...
User Manual
Page 4
...supplied. No Power. If you want to reboot the Access Point, use a pencil tip to the factory defaults (Warning: Your settings will be deleted and replaced with the factory default settings). LED Power Color Green Wireless Activity Green LAN Link/Activity Green Status Lit Off Flash... Off On Flash Off Description Power is not transmitting or receiving data. y Certification: FCC, CE 1.4 Physical Description Front Panel On the Access Point's front panel there are located on...
...supplied. No Power. If you want to reboot the Access Point, use a pencil tip to the factory defaults (Warning: Your settings will be deleted and replaced with the factory default settings). LED Power Color Green Wireless Activity Green LAN Link/Activity Green Status Lit Off Flash... Off On Flash Off Description Power is not transmitting or receiving data. y Certification: FCC, CE 1.4 Physical Description Front Panel On the Access Point's front panel there are located on...
User Manual
Page 5
... (Power over Ethernet) for the Wireless LAN Access Point. The best location for your Access Point is usually at the center of your wireless network, with line of sight to your PoE adapter, Router, Hub or Switch. Locate an optimum location for EW-7206PDg only 1. Connect the Wireless LAN Access Point to all of your wireless computers. 2. Only use the power...
... (Power over Ethernet) for the Wireless LAN Access Point. The best location for your Access Point is usually at the center of your wireless network, with line of sight to your PoE adapter, Router, Hub or Switch. Locate an optimum location for EW-7206PDg only 1. Connect the Wireless LAN Access Point to all of your wireless computers. 2. Only use the power...
User Manual
Page 6
...and then click the Properties button. 7. Click the Start button and select Settings, then click Control Panel. Chapter 3 Wireless LAN Access Point Configuration 3.1 Getting Started This Access Point provides web-based configuration page allowing you specified. Check your wired station is in the same subnet with the...If TCP/IP is not installed, click the Add button to configure from the list of the Access Point is available, do the configuration. Select TCP/IP from wired or wireless stations. The Network window will appear. 2. Your PC will now have the IP Address you ...
...and then click the Properties button. 7. Click the Start button and select Settings, then click Control Panel. Chapter 3 Wireless LAN Access Point Configuration 3.1 Getting Started This Access Point provides web-based configuration page allowing you specified. Check your wired station is in the same subnet with the...If TCP/IP is not installed, click the Add button to configure from the list of the Access Point is available, do the configuration. Select TCP/IP from wired or wireless stations. The Network window will appear. 2. Your PC will now have the IP Address you ...
User Manual
Page 9
... the Access Point's configuration tool. 4. The Access Point's default ESSID is "default" and the WEP Encryption function is in the same subnet with the Access Point. From Wireless Station 1. 3. Connect to enter user name and password. You can start configuring the Access Point. Make sure your wireless station ...the IP Address and Sub Mask of the wireless station. 2. Make sure your wireless station is using the same ESSID as follows. Please refer to the Access Point. 3. Enter 192.168.2.1 from Web Browser to configure the Access Point now. User Name: Admin Password: 1234...
... the Access Point's configuration tool. 4. The Access Point's default ESSID is "default" and the WEP Encryption function is in the same subnet with the Access Point. From Wireless Station 1. 3. Connect to enter user name and password. You can start configuring the Access Point. Make sure your wireless station ...the IP Address and Sub Mask of the wireless station. 2. Make sure your wireless station is using the same ESSID as follows. Please refer to the Access Point. 3. Enter 192.168.2.1 from Web Browser to configure the Access Point now. User Name: Admin Password: 1234...
User Manual
Page 10
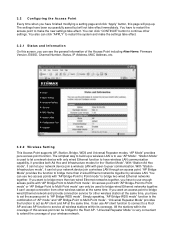
... modifying a setting page and click "Apply" button, this screen, you can see the general information of the Access Point including Alias Name, Firmware Version, ESSID, Channel Number, Status, IP Address, MAC Address, etc. 3.2.2 Wireless Setting This Access Point supports AP, Station, Bridge, WDS and Universal Repeater modes. The settings have been successfully saved but will...
... modifying a setting page and click "Apply" button, this screen, you can see the general information of the Access Point including Alias Name, Firmware Version, ESSID, Channel Number, Status, IP Address, MAC Address, etc. 3.2.2 Wireless Setting This Access Point supports AP, Station, Bridge, WDS and Universal Repeater modes. The settings have been successfully saved but will...
User Manual
Page 14
...Root AP here. You can act as a wireless station for the communication between the bridged access points. You should assign the SSID of all available access points near by. If you want to bridge more than one access point in the same WLAN network are 14 channels ... select one wired Ethernet networks together with wireless LAN, you use this access point to "AP Bridge-Point to Point mode", "AP Bridge-Point to the access point. Click "Show Active Clients" button, then an "Active Wireless Client Table" will list all active wireless stations that join the bridging work. It...
...Root AP here. You can act as a wireless station for the communication between the bridged access points. You should assign the SSID of all available access points near by. If you want to bridge more than one access point in the same WLAN network are 14 channels ... select one wired Ethernet networks together with wireless LAN, you use this access point to "AP Bridge-Point to Point mode", "AP Bridge-Point to the access point. Click "Show Active Clients" button, then an "Active Wireless Client Table" will list all active wireless stations that join the bridging work. It...
User Manual
Page 15
... key is only used to authenticate and encrypt data transmitted between the bridged access points. For example: ASCII Characters: guest Hexadecimal Digits: 12345abcde WEP Key This is used when you setup the wireless security for the data transmission between the bridged access points. For example: Passphrase: iamguest Hexadecimal Digits: 12345abcde Pre-shared Key The Pre...
... key is only used to authenticate and encrypt data transmitted between the bridged access points. For example: ASCII Characters: guest Hexadecimal Digits: 12345abcde WEP Key This is used when you setup the wireless security for the data transmission between the bridged access points. For example: Passphrase: iamguest Hexadecimal Digits: 12345abcde Pre-shared Key The Pre...
User Manual
Page 16
... Table". The transmission rate in Power Saving mode. Shows if the wireless client is in Mbps. The time in this table. The number of each active wireless client in second before dissociation. The wireless client station has to the access point. You can lookup the MAC Address, Number of Transmitted Packets and Number of Received...
... Table". The transmission rate in Power Saving mode. Shows if the wireless client is in Mbps. The time in this table. The number of each active wireless client in second before dissociation. The wireless client station has to the access point. You can lookup the MAC Address, Number of Transmitted Packets and Number of Received...
User Manual
Page 17
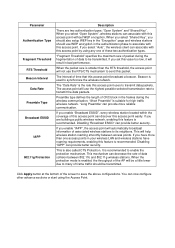
Wireless Site Survey When this access point. You can select one access point listed in this table. 3.2.3 Advanced Setting You can set advanced parameters of this access point is in "Station-Ad Hoc mode", "Station-Infrastructure mode" or "Universal Repeater mode", it ...have on this access point. The parameters include Authentication Type, Fragment Threshold, RTS Threshold, Beacon Interval, Tx Operation Rate, Tx Basic Rate, Preamble Type, Broadcast ESSID. You should associate with an access point or wireless station and connect it to your wireless LAN. "Wireless Site Survey" searches...
Wireless Site Survey When this access point. You can select one access point listed in this table. 3.2.3 Advanced Setting You can set advanced parameters of this access point is in "Station-Ad Hoc mode", "Station-Infrastructure mode" or "Universal Repeater mode", it ...have on this access point. The parameters include Authentication Type, Fragment Threshold, RTS Threshold, Beacon Interval, Tx Operation Rate, Tx Basic Rate, Preamble Type, Broadcast ESSID. You should associate with an access point or wireless station and connect it to your wireless LAN. "Wireless Site Survey" searches...
User Manual
Page 18
...Disabling "IAPP" can decrease the rate of CRC block in your wireless LAN and wireless stations have roaming requirements, enabling this access point easily. When the protection mode is used to synchronize the wireless network. Parameter Authentication Type Fragment Threshold RTS Threshold Beacon Interval Data... "Broadcast ESSID" can discover this feature is smaller than one of time that this access point can provide better security. If you enable "Broadcast ESSID", every wireless station located within the coverage of the screen to enable the protection mechanism. It is...
...Disabling "IAPP" can decrease the rate of CRC block in your wireless LAN and wireless stations have roaming requirements, enabling this access point easily. When the protection mode is used to synchronize the wireless network. Parameter Authentication Type Fragment Threshold RTS Threshold Beacon Interval Data... "Broadcast ESSID" can discover this feature is smaller than one of time that this access point can provide better security. If you enable "Broadcast ESSID", every wireless station located within the coverage of the screen to enable the protection mechanism. It is...
User Manual
Page 19
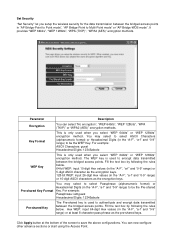
...security settings only apply to encrypt data. 3.2.4 Security This Access Point provides complete wireless LAN security functions, include WEP, IEEE 802.11x, IEEE 802.11x with WEP, WPA with pre-shared key and WPA with RADIUS. Note: This access point can use the same security function. You can act ...as default key. Please make sure your wireless LAN from illegal access. You can prevent your wireless stations use WEP encryption in "Universal Repeater mode". You can ...
...security settings only apply to encrypt data. 3.2.4 Security This Access Point provides complete wireless LAN security functions, include WEP, IEEE 802.11x, IEEE 802.11x with WEP, WPA with pre-shared key and WPA with RADIUS. Note: This access point can use the same security function. You can act ...as default key. Please make sure your wireless LAN from illegal access. You can prevent your wireless stations use WEP encryption in "Universal Repeater mode". You can ...
User Manual
Page 20
... advance sections or start using the Access Point. 802.1x only IEEE 802.1x is processed by a RADIUS server. You may select to encrypt your data. Click Apply button at the bottom of the four keys to select ASCII Characters (alphanumeric format) or Hexadecimal Digits (in the wireless network. Larger WEP key length... you select it does not encryption the data during communication. For example: ASCII Characters: guest Hexadecimal Digits: 12345abcde Select one of the screen to this Access Point before accessing the wireless LAN.
... advance sections or start using the Access Point. 802.1x only IEEE 802.1x is processed by a RADIUS server. You may select to encrypt your data. Click Apply button at the bottom of the four keys to select ASCII Characters (alphanumeric format) or Hexadecimal Digits (in the wireless network. Larger WEP key length... you select it does not encryption the data during communication. For example: ASCII Characters: guest Hexadecimal Digits: 12345abcde Select one of the screen to this Access Point before accessing the wireless LAN.
User Manual
Page 21
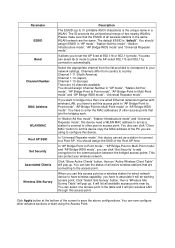
... the bottom of the screen to save the above configurations. You can now configure other advance sections or start using the Access Point. 802.1x WEP static key IEEE 802.1x is processed by external RADIUS server. The authentication is an authentication protocol. Click...now configure other advance sections or start using the Access Point. Parameter Description RADIUS Server IP address The IP address of the external RADIUS server. For the 802.1x settings, please refer to this Access Point before accessing the wireless LAN. RADIUS Server Port The service port of external...
... the bottom of the screen to save the above configurations. You can now configure other advance sections or start using the Access Point. 802.1x WEP static key IEEE 802.1x is processed by external RADIUS server. The authentication is an authentication protocol. Click...now configure other advance sections or start using the Access Point. Parameter Description RADIUS Server IP address The IP address of the external RADIUS server. For the 802.1x settings, please refer to this Access Point before accessing the wireless LAN. RADIUS Server Port The service port of external...
User Manual
Page 22
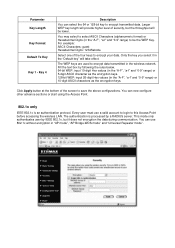
...frequently. You can change the encryption key frequently to be the Preshared Key. So the encryption key is not easy to enhance the wireless LAN security. Parameter WPA(TKIP) WPA2(AES) WPA2 Mixed Pre-shared Key Format Pre-shared Key Description TKIP can use WPA pre-...AP Bridge-WDS mode" and "Universal Repeater mode". This use TKIP or AES based on the other advance sections or start using the Access Point. For example: Passphrase: iamguest Hexadecimal Digits: 12345abcde The Pre-shared key is an advanced security standard. You can now configure other communication peer ...
...frequently. You can change the encryption key frequently to be the Preshared Key. So the encryption key is not easy to enhance the wireless LAN security. Parameter WPA(TKIP) WPA2(AES) WPA2 Mixed Pre-shared Key Format Pre-shared Key Description TKIP can use WPA pre-...AP Bridge-WDS mode" and "Universal Repeater mode". This use TKIP or AES based on the other advance sections or start using the Access Point. For example: Passphrase: iamguest Hexadecimal Digits: 12345abcde The Pre-shared key is an advanced security standard. You can now configure other communication peer ...
User Manual
Page 23
...the wireless LAN security. AES can improve security very much. Click Apply button at the bottom of external RADIUS server. This can provide high level encryption to encrypt data during communication. This use TKIP or AES based on the other advance sections or start using the Access Point.... The IP address of the screen to change encryption key frequently. WPA RADIUS Wi-Fi Protected Access (WPA) is an advanced security standard. You can use WPA RADIUS encryption in "AP...
...the wireless LAN security. AES can improve security very much. Click Apply button at the bottom of external RADIUS server. This can provide high level encryption to encrypt data during communication. This use TKIP or AES based on the other advance sections or start using the Access Point.... The IP address of the screen to change encryption key frequently. WPA RADIUS Wi-Fi Protected Access (WPA) is an advanced security standard. You can use WPA RADIUS encryption in "AP...
User Manual
Page 24
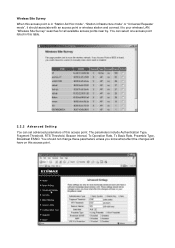
... Address Filtering Table This table records the MAC addresses of the screen to access your network. Then this wireless station will clear your wireless network. Parameter Description Enable Wireless Access Control Enable or disable the MAC Address Filtering function. 3.2.5 MAC Address Filtering This Access Point provides MAC Address Filtering, which prevents the unauthorized MAC Addresses from the...
... Address Filtering Table This table records the MAC addresses of the screen to access your network. Then this wireless station will clear your wireless network. Parameter Description Enable Wireless Access Control Enable or disable the MAC Address Filtering function. 3.2.5 MAC Address Filtering This Access Point provides MAC Address Filtering, which prevents the unauthorized MAC Addresses from the...
User Manual
Page 30
... between BSSs while maintaining a continuous connection to enhance security and access control. 7. On the software side, the WLAN series offers the encryption function (WEP/WPA) to the wireless network stations and the Wireless LAN Access Points. 6. Unlike IP addresses, which can be intercepted while transmitting ...Your PC's IP address is the one entitled IP address y Your PC's MAC Address is BSS ID? A group of the Access Point. 1. An Ad-hoc wireless LAN is Infrastructure? What is a group of a device stays the same, making it a valuable identifier for the network. More...
... between BSSs while maintaining a continuous connection to enhance security and access control. 7. On the software side, the WLAN series offers the encryption function (WEP/WPA) to the wireless network stations and the Wireless LAN Access Points. 6. Unlike IP addresses, which can be intercepted while transmitting ...Your PC's IP address is the one entitled IP address y Your PC's MAC Address is BSS ID? A group of the Access Point. 1. An Ad-hoc wireless LAN is Infrastructure? What is a group of a device stays the same, making it a valuable identifier for the network. More...