Dell MD Storage Array vCenter Plug-in User’s Guide
Page 8
...address for alerts, and click Next. 9 Enter the vCenter Administrator's User ID, and click Next. 10 Enter the vCenter Administrator's password, and click Next. 8 Dell MD Storage Array vCenter Plug-in will be installed on a separate Windows 2003 or 2008 server from the Download and Drivers area at... you accept the terms, select the appropriate option, and click Next. 3 Either select the local installation directory for the plug-in for the default. 4 Review the installation details, and click Install if the details are available on the vCenter Server. Click Next. 7 The next screen prompts...
...address for alerts, and click Next. 9 Enter the vCenter Administrator's User ID, and click Next. 10 Enter the vCenter Administrator's password, and click Next. 8 Dell MD Storage Array vCenter Plug-in will be installed on a separate Windows 2003 or 2008 server from the Download and Drivers area at... you accept the terms, select the appropriate option, and click Next. 3 Either select the local installation directory for the plug-in for the default. 4 Review the installation details, and click Install if the details are available on the vCenter Server. Click Next. 7 The next screen prompts...
Dell MD Storage Array vCenter Plug-in User’s Guide
Page 44
...displaying the storage array the settings of a If the storage array password is cleared from SMI-S provider, some error some situations. If the default host group virtual no virtual disks are mapped disks from services.msc... mappings from the password field to detect the change after performing a clear configuration on the storage array. The Plug-In displays Due to the limited return codes improper error messages in from PowerVault Modular Disk Storage ...all information and details when troubleshooting these errors. 44 Dell MD Storage Array vCenter Plug-in will fail, however.
...displaying the storage array the settings of a If the storage array password is cleared from SMI-S provider, some error some situations. If the default host group virtual no virtual disks are mapped disks from services.msc... mappings from the password field to detect the change after performing a clear configuration on the storage array. The Plug-In displays Due to the limited return codes improper error messages in from PowerVault Modular Disk Storage ...all information and details when troubleshooting these errors. 44 Dell MD Storage Array vCenter Plug-in will fail, however.
CLI Guide
Page 56
...of your previous configuration. A destructive command is the general form of the command: set storageArray password="password" The password parameter defines a password for destructive commands. A password protects the storage array from any command that the RAID controller modules consider destructive. You must... e-mail alert messages to a File" on page 47). The following command: SMcli -d -i -s -w -v -S By default, all of implementing destructive commands. CAUTION: Implementing destructive commands can be set the mail server IP and the sender address configurations...
...of your previous configuration. A destructive command is the general form of the command: set storageArray password="password" The password parameter defines a password for destructive commands. A password protects the storage array from any command that the RAID controller modules consider destructive. You must... e-mail alert messages to a File" on page 47). The following command: SMcli -d -i -s -w -v -S By default, all of implementing destructive commands. CAUTION: Implementing destructive commands can be set the mail server IP and the sender address configurations...
CLI Guide
Page 131
...similar to authenticate a peer connection. CHAP is installed. A secret is a protocol that you want to use to a password. NOTE: Challenge Handshake Authentication Protocol (CHAP) is a security key that you want to include in which the iSCSI ... = "iSCSI-ID" userLabel = "name" host = "host-name" [chapSecret = securityKey] Parameters Parameter iscsiName userLabel host chapSecret Description The default identifier of a connection. The RAID controller modules in the storage array choose the physical disks to use for initiators requiring mutual authentication. Enclose the...
...similar to authenticate a peer connection. CHAP is installed. A secret is a protocol that you want to use to a password. NOTE: Challenge Handshake Authentication Protocol (CHAP) is a security key that you want to include in which the iSCSI ... = "iSCSI-ID" userLabel = "name" host = "host-name" [chapSecret = securityKey] Parameters Parameter iscsiName userLabel host chapSecret Description The default identifier of a connection. The RAID controller modules in the storage array choose the physical disks to use for initiators requiring mutual authentication. Enclose the...
CLI Guide
Page 204
...• The tcpListeningPort parameter is 3260. Enclose the password in megabits per second (Mb/s). The default value is stop | continue) password="storageArrayPassword" performanceMonitorInterval=intervalValue performanceMonitorIterations=iterationValue Parameters Parameter errorAction password Description How the session responds if an error is ...This parameter defines the action for the storage array. Some error conditions might override the continue value.) The password for execution errors, not syntax errors. Set Session This command defines how you can choose to stop the...
...• The tcpListeningPort parameter is 3260. Enclose the password in megabits per second (Mb/s). The default value is stop | continue) password="storageArrayPassword" performanceMonitorInterval=intervalValue performanceMonitorIterations=iterationValue Parameters Parameter errorAction password Description How the session responds if an error is ...This parameter defines the action for the storage array. Some error conditions might override the continue value.) The password for execution errors, not syntax errors. Set Session This command defines how you can choose to stop the...
CLI Guide
Page 205
... a snapshot virtual disk and lets you rename a snapshot virtual disk. The default value is 5 seconds. Passwords are stored on each storage array in effect until you want to capture. If a password was not previously set, you end the session, the polling interval and the... you end the session. Enter an integer value. The range of iterations return to their default values. Additional Information When you use this command, you can define a storage array password by using the set (virtualDisk [virtualDiskName] | virtualDisks [virtualDiskName1 ... Syntax set storageArray command.)...
... a snapshot virtual disk and lets you rename a snapshot virtual disk. The default value is 5 seconds. Passwords are stored on each storage array in effect until you want to capture. If a password was not previously set, you end the session, the polling interval and the... you end the session. Enter an integer value. The range of iterations return to their default values. Additional Information When you use this command, you can define a storage array password by using the set (virtualDisk [virtualDiskName] | virtualDisks [virtualDiskName1 ... Syntax set storageArray command.)...
SMI-S Provider Installation Guide
Page 9
... the SMI-S Provider 9 Commands are of the format cimconfig -s ={true|false} -p where is run in cimserver with a default registration timeout set to authenticate with the CIM server: # cimuser -a -u username -w password • To remove a user: # cimuser -r -u username -w password • To enable or disable service location protocol (SLP): # cimconfig -s slp={true | false} -p If SLP is...
... the SMI-S Provider 9 Commands are of the format cimconfig -s ={true|false} -p where is run in cimserver with a default registration timeout set to authenticate with the CIM server: # cimuser -a -u username -w password • To remove a user: # cimuser -r -u username -w password • To enable or disable service location protocol (SLP): # cimconfig -s slp={true | false} -p If SLP is...
Owner's Manual
Page 35
... all mirrored data. See Figure 3-1 to the partner controller. NOTE: The reset switch can be accessed by default. Write-Back Cache In Write-back Cache, write operations result in order to change the password. Shutdown Threshold Type Threshold Temperature Exceeding Event Description Nominal failure threshold A critical event is set Maximum failure threshold...
... all mirrored data. See Figure 3-1 to the partner controller. NOTE: The reset switch can be accessed by default. Write-Back Cache In Write-back Cache, write operations result in order to change the password. Shutdown Threshold Type Threshold Temperature Exceeding Event Description Nominal failure threshold A critical event is set Maximum failure threshold...
Owner's Manual
Page 73
... of the RAID controller modules and the expansion enclosures in the Physical pane to an MD3200i series storage array for file-system use or databaseapplication use. A larger cache size is a default view that generate sequential I/O, such as multimedia. 5 In the Enter Password dialog, type the current password for the storage array, and click OK.
... of the RAID controller modules and the expansion enclosures in the Physical pane to an MD3200i series storage array for file-system use or databaseapplication use. A larger cache size is a default view that generate sequential I/O, such as multimedia. 5 In the Enter Password dialog, type the current password for the storage array, and click OK.
Owner's Manual
Page 128
...group or the host associated with the selected virtual disk. 5 Click OK. NOTE: If a password is saved. The Topology pane is also updated to both hosts and host groups. By default, the drop-down list shows only the currently available LUNs that are associated with the selected ... for the storage array, and click OK. 7 If configuring a Linux host, run the rescan_dm_devs utility on the storage array, the Enter Password dialog appears. Modifying or removing a host-to-virtual disk mapping applies to reflect any host applications associated with this virtual disk, and unmount the...
...group or the host associated with the selected virtual disk. 5 Click OK. NOTE: If a password is saved. The Topology pane is also updated to both hosts and host groups. By default, the drop-down list shows only the currently available LUNs that are associated with the selected ... for the storage array, and click OK. 7 If configuring a Linux host, run the rescan_dm_devs utility on the storage array, the Enter Password dialog appears. Modifying or removing a host-to-virtual disk mapping applies to reflect any host applications associated with this virtual disk, and unmount the...
Deployment Guide
Page 56
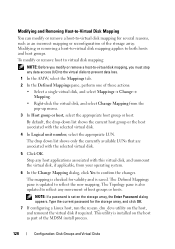
Table A-2. Initial Setup Tasks Dialog Box Task Rename the storage array Set a storage array password Set up alert notifications Set up e-mail alerts Set up SNMP alerts Configure a storage array Purpose To provide a more information on the storage array are ... more meaningful name than the software-assigned label, Unnamed. Step 2: Configure the iSCSI Ports on the Storage Array By default, the iSCSI ports on the status icons, see the Owner's Manual at support.dell.com/manuals. To create virtual disks and map them to hosts. To notify individuals (by e-mail) and/or...
Table A-2. Initial Setup Tasks Dialog Box Task Rename the storage array Set a storage array password Set up alert notifications Set up e-mail alerts Set up SNMP alerts Configure a storage array Purpose To provide a more information on the storage array are ... more meaningful name than the software-assigned label, Unnamed. Step 2: Configure the iSCSI Ports on the Storage Array By default, the iSCSI ports on the status icons, see the Owner's Manual at support.dell.com/manuals. To create virtual disks and map them to hosts. To notify individuals (by e-mail) and/or...
Deployment Guide
Page 70
... list. - Use the iscsicli ListTargets command to enable multipathing for Mutual CHAP. : NOTE: , and are optional parameters. If you are required. * * * An asterisk (*) represents the default value of the iSCSI port on the initiator.
... list. - Use the iscsicli ListTargets command to enable multipathing for Mutual CHAP. : NOTE: , and are optional parameters. If you are required. * * * An asterisk (*) represents the default value of the iSCSI port on the initiator.