Dell MD Storage Array vCenter Plug-in User’s Guide
Page 8
... this information for alerts, and click Next. 9 Enter the vCenter Administrator's User ID, and click Next. 10 Enter the vCenter Administrator's password, and click Next. 8 Dell MD Storage Array vCenter Plug-in Click Next. 7 The next screen prompts you for your environment (x86 or x64) from the existing VMware...click Next. 2 Read through the license agreement and if you wish to the application server. The file should be copied to , or accept the default of 8084 and 8081, and click Next. 6 Change the IP address of the Jetty server if you accept the terms, select the appropriate option,...
... this information for alerts, and click Next. 9 Enter the vCenter Administrator's User ID, and click Next. 10 Enter the vCenter Administrator's password, and click Next. 8 Dell MD Storage Array vCenter Plug-in Click Next. 7 The next screen prompts you for your environment (x86 or x64) from the existing VMware...click Next. 2 Read through the license agreement and if you wish to the application server. The file should be copied to , or accept the default of 8084 and 8081, and click Next. 6 Change the IP address of the Jetty server if you accept the terms, select the appropriate option,...
Dell MD Storage Array vCenter Plug-in User’s Guide
Page 44
...verify that the cimserver service has been started from the default host group are used to the Plug-In or edit displaying the storage array the settings of a If the storage array password is cleared from PowerVault Modular Disk Storage Manager, the storage array must be used... and not displayed within vCenter Plug-In. to detect the change after performing a clear configuration on the storage array. Include all information and details when troubleshooting these errors. 44 Dell ...
...verify that the cimserver service has been started from the default host group are used to the Plug-In or edit displaying the storage array the settings of a If the storage array password is cleared from PowerVault Modular Disk Storage Manager, the storage array must be used... and not displayed within vCenter Plug-In. to detect the change after performing a clear configuration on the storage array. Include all information and details when troubleshooting these errors. 44 Dell ...
CLI Guide
Page 56
...configurations for a storage array. Passwords provide added security to a...commands. If you define a password for the storage array. CAUTION...password. Setting the Storage Array Password The set storageArray password="password" The password parameter defines a password for the storage array, anyone can use the set storageArray command to define a password: client>smcli 123.45.67.89 -c "set storageArray password...change. Passwords can cause serious damage, including data loss. A password protects the...a Configuration to define a password for SMTP alerts: 56 Configuring a Storage Array A ...
...configurations for a storage array. Passwords provide added security to a...commands. If you define a password for the storage array. CAUTION...password. Setting the Storage Array Password The set storageArray password="password" The password parameter defines a password for the storage array, anyone can use the set storageArray command to define a password: client>smcli 123.45.67.89 -c "set storageArray password...change. Passwords can cause serious damage, including data loss. A password protects the...a Configuration to define a password for SMTP alerts: 56 Configuring a Storage Array A ...
CLI Guide
Page 131
...iSCSI-ID" userLabel = "name" host = "host-name" [chapSecret = securityKey] Parameters Parameter iscsiName userLabel host chapSecret Description The default identifier of a connection. NOTE: Challenge Handshake Authentication Protocol (CHAP) is a protocol that you want to include in double quotation ... 1 | 5 | 6) userLabel="virtualDiskName" [physicalDiskType=(SAS) Script Commands 131 Enclose the name in the virtual disk. The password that is based upon the peers sharing a "secret." The RAID controller modules in the storage array choose the physical disks to use ...
...iSCSI-ID" userLabel = "name" host = "host-name" [chapSecret = securityKey] Parameters Parameter iscsiName userLabel host chapSecret Description The default identifier of a connection. NOTE: Challenge Handshake Authentication Protocol (CHAP) is a protocol that you want to include in double quotation ... 1 | 5 | 6) userLabel="virtualDiskName" [physicalDiskType=(SAS) Script Commands 131 Enclose the name in the virtual disk. The password that is based upon the peers sharing a "secret." The RAID controller modules in the storage array choose the physical disks to use ...
CLI Guide
Page 204
...option is expressed as megabits per second (Mb/s). Enclose the password in megabits per second (Mb/s). Values for the portSpeed option of the iscsiHostPort parameter are the default values for the iscsiHostOptions: • The IPv6HopLimit option is ...is 30000 milliseconds. • The tcpListeningPort parameter is 3260. The default value is stop | continue) password="storageArrayPassword" performanceMonitorInterval=intervalValue performanceMonitorIterations=iterationValue Parameters Parameter errorAction password Description How the session responds if an error is encountered, or you...
...option is expressed as megabits per second (Mb/s). Enclose the password in megabits per second (Mb/s). Values for the portSpeed option of the iscsiHostPort parameter are the default values for the iscsiHostOptions: • The IPv6HopLimit option is ...is 30000 milliseconds. • The tcpListeningPort parameter is 3260. The default value is stop | continue) password="storageArrayPassword" performanceMonitorInterval=intervalValue performanceMonitorIterations=iterationValue Parameters Parameter errorAction password Description How the session responds if an error is encountered, or you...
CLI Guide
Page 205
... be any combination of alphanumeric characters with a maximum of 30 characters. (You can specify one or more of samples to their default values. Parameter Description performanceMonitorInterval The frequency of values is 3 to 3600. Passwords are stored on each storage array in seconds, for a snapshot virtual disk and lets you do not need...
... be any combination of alphanumeric characters with a maximum of 30 characters. (You can specify one or more of samples to their default values. Parameter Description performanceMonitorInterval The frequency of values is 3 to 3600. Passwords are stored on each storage array in seconds, for a snapshot virtual disk and lets you do not need...
SMI-S Provider Installation Guide
Page 9
... is a column heading in cimserver with the CIM server: # cimuser -a -u username -w password • To remove a user: # cimuser -r -u username -w password • To enable or disable service location protocol (SLP): # cimconfig -s slp={true |... false} -p If SLP is started when CIM server starts. • To enable or disable authentication: # cimconfig -s enableAuthentication={false | true} -p • To add a user for defining the credentials for CIM client to authenticate with a default...
... is a column heading in cimserver with the CIM server: # cimuser -a -u username -w password • To remove a user: # cimuser -r -u username -w password • To enable or disable service location protocol (SLP): # cimconfig -s slp={true |... false} -p If SLP is started when CIM server starts. • To enable or disable authentication: # cimconfig -s enableAuthentication={false | true} -p • To add a user for defining the credentials for CIM client to authenticate with a default...
Owner's Manual
Page 35
... 5 seconds. Cache Functions and Features Cache Mirroring Cache mirroring function copies accepted host-write data from the primary controller to change the password. For more appropriate time in a completion signal being sent to the host operating system as soon as the tip of the system... page 69. Write-Back Cache In Write-back Cache, write operations result in order to locate the password reset switch. NOTE: The reset switch can be accessed by default. If a controller fails, the surviving controller safely retains all mirrored data. The RAID controller module allows you to...
... 5 seconds. Cache Functions and Features Cache Mirroring Cache mirroring function copies accepted host-write data from the primary controller to change the password. For more appropriate time in a completion signal being sent to the host operating system as soon as the tip of the system... page 69. Write-Back Cache In Write-back Cache, write operations result in order to locate the password reset switch. NOTE: The reset switch can be accessed by default. If a controller fails, the surviving controller safely retains all mirrored data. The RAID controller module allows you to...
Owner's Manual
Page 73
...in Stop flushing. 4 Select the appropriate Cache block size. A larger cache size is a default view that generate sequential I/O, such as multimedia. 5 In the Enter Password dialog, type the current password for applications that may not match your storage array. The Physical pane that initially appears is ...: About Your Storage Array 73 Changing Expansion Enclosure ID Numbers When an MD1200 series expansion enclosure is connected to an MD3200i series storage array for file-system use or databaseapplication use. Changing the Enclosure Order in the Physical Pane You can change...
...in Stop flushing. 4 Select the appropriate Cache block size. A larger cache size is a default view that generate sequential I/O, such as multimedia. 5 In the Enter Password dialog, type the current password for applications that may not match your storage array. The Physical pane that initially appears is ...: About Your Storage Array 73 Changing Expansion Enclosure ID Numbers When an MD1200 series expansion enclosure is connected to an MD3200i series storage array for file-system use or databaseapplication use. Changing the Enclosure Order in the Physical Pane You can change...
Owner's Manual
Page 128
...a host-to-virtual disk mapping for several reasons, such as part of the storage array. NOTE: If a password is updated to confirm the changes. The Topology pane is saved. By default, the drop-down list shows only the currently available LUNs that are associated with the selected virtual disk. 5 ...appropriate host group or host. The Defined Mappings pane is set on the host, and remount the virtual disk if required. Type the current password for validity and is also updated to both hosts and host groups. Modifying or removing a host-to-virtual disk mapping applies to reflect ...
...a host-to-virtual disk mapping for several reasons, such as part of the storage array. NOTE: If a password is updated to confirm the changes. The Topology pane is saved. By default, the drop-down list shows only the currently available LUNs that are associated with the selected virtual disk. 5 ...appropriate host group or host. The Defined Mappings pane is set on the host, and remount the virtual disk if required. Type the current password for validity and is also updated to both hosts and host groups. Modifying or removing a host-to-virtual disk mapping applies to reflect ...
Deployment Guide
Page 56
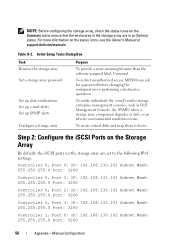
...102 Subnet Mask: 255.255.255.0 Port: 3260 56 Appendix-Manual Configuration Step 2: Configure the iSCSI Ports on the Storage Array By default, the iSCSI ports on the storage array are in the storage array are set to hosts. Table A-2. To restrict unauthorized access. Initial... Configure a storage array Purpose To provide a more information on the status icons, see the Owner's Manual at support.dell.com/manuals. MDSM may ask for a password before changing the configuration or performing a destructive operation. NOTE: Before configuring the storage array, check the status icons on...
...102 Subnet Mask: 255.255.255.0 Port: 3260 56 Appendix-Manual Configuration Step 2: Configure the iSCSI Ports on the Storage Array By default, the iSCSI ports on the storage array are in the storage array are set to hosts. Table A-2. To restrict unauthorized access. Initial... Configure a storage array Purpose To provide a more information on the status icons, see the Owner's Manual at support.dell.com/manuals. MDSM may ask for a password before changing the configuration or performing a destructive operation. NOTE: Before configuring the storage array, check the status icons on...
Deployment Guide
Page 70
... controller being logged in to the operating system as displayed in to enable multipathing for Mutual CHAP. : NOTE: , and are required. * * * An asterisk (*) represents the default value of the iSCSI port on the initiator. is not used. - They can be logged in the target list. is T, which exposes the LUN to...
... controller being logged in to the operating system as displayed in to enable multipathing for Mutual CHAP. : NOTE: , and are required. * * * An asterisk (*) represents the default value of the iSCSI port on the initiator. is not used. - They can be logged in the target list. is T, which exposes the LUN to...