Command Line Interface Guide
Page 4
enable authentication 194 enable password 194 ip http authentication 195 ip https authentication 196 login authentication 197 password (Line Configuration 198 password (User EXEC 199 show authentication methods 200 show users accounts 201 show users login-history 202 username 203 5 ACL Commands 205 deny | permit 207 ip access-group 209 no ip access-group 209 mac access-group 210 mac access-list extended 211 mac access-list extended rename 212 show ip access-lists 213 show mac access-list 214 4 Contents
enable authentication 194 enable password 194 ip http authentication 195 ip https authentication 196 login authentication 197 password (Line Configuration 198 password (User EXEC 199 show authentication methods 200 show users accounts 201 show users login-history 202 username 203 5 ACL Commands 205 deny | permit 207 ip access-group 209 no ip access-group 209 mac access-group 210 mac access-list extended 211 mac access-list extended rename 212 show ip access-lists 213 show mac access-list 214 4 Contents
Command Line Interface Guide
Page 47
66 Serviceability Tracing Packet Commands 1199 debug auto-voip 1201 debug clear 1202 debug console 1202 debug dot1x 1203 debug igmpsnooping 1204 debug ip acl 1204 debug ip dvmrp 1205 debug ip igmp 1206 debug ip mcache 1207 debug ip pimdm 1207 debug ip pimsm 1208 debug ip vrrp 1209 debug ipv6 mcache 1210 debug ipv6 mld 1210 debug ipv6 pimdm 1211 debug ipv6 pimsm 1212 debug isdp 1213 debug lacp 1213 debug mldsnooping 1214 debug ospf 1215 Contents 47
66 Serviceability Tracing Packet Commands 1199 debug auto-voip 1201 debug clear 1202 debug console 1202 debug dot1x 1203 debug igmpsnooping 1204 debug ip acl 1204 debug ip dvmrp 1205 debug ip igmp 1206 debug ip mcache 1207 debug ip pimdm 1207 debug ip pimsm 1208 debug ip vrrp 1209 debug ipv6 mcache 1210 debug ipv6 mld 1210 debug ipv6 pimdm 1211 debug ipv6 pimsm 1212 debug isdp 1213 debug lacp 1213 debug mldsnooping 1214 debug ospf 1215 Contents 47
Command Line Interface Guide
Page 55
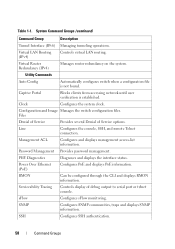
... sets of a Graphic User Interface (GUI) driven software application. System Command Groups Command Group Layer 2 Commands AAA ACL Description Configures connection security including authorization and passwords. This guide also provides information for configuring the PowerConnect switch, details the procedures, and provides configuration examples. Command Groups The system commands can be completed before...
... sets of a Graphic User Interface (GUI) driven software application. System Command Groups Command Group Layer 2 Commands AAA ACL Description Configures connection security including authorization and passwords. This guide also provides information for configuring the PowerConnect switch, details the procedures, and provides configuration examples. Command Groups The system commands can be completed before...
Command Line Interface Guide
Page 56
... Configures and displays GVRP configuration and information. Link Dependency Configures and displays link dependency information. Port Monitor Monitors activity on Spanning Tree protocol. IPv6 ACL Configures and displays ACL information for example ports, storm control, port speed and auto-negotiation. Spanning Tree Configures and reports on specific target ports. LACP Configures and...
... Configures and displays GVRP configuration and information. Link Dependency Configures and displays link dependency information. Port Monitor Monitors activity on Spanning Tree protocol. IPv6 ACL Configures and displays ACL information for example ports, storm control, port speed and auto-negotiation. Spanning Tree Configures and reports on specific target ports. LACP Configures and...
Command Line Interface Guide
Page 58
... on the system. Utility Commands Auto Config Automatically configures switch when a configuration file is established. Line Configures the console, SSH, and remote Telnet connection. Management ACL Configures and displays management access-list information. RMON Can be configured through the CLI and displays RMON information. Clock Configures the system clock. Serviceability Tracing...
... on the system. Utility Commands Auto Config Automatically configures switch when a configuration file is established. Line Configures the console, SSH, and remote Telnet connection. Management ACL Configures and displays management access-list information. RMON Can be configured through the CLI and displays RMON information. Clock Configures the system clock. Serviceability Tracing...
Command Line Interface Guide
Page 60
ARP ACL Configuration • CC - Key Chain • KE - MST Configuration • ML - Policy Class Map Configuration • R - Radius • RIP - Key • L - Logging • LC - ... CP - Captive Portal Configuration • CPI - Class-Map Configuration • GC - Global Configuration • IC - Line Configuration • MA - MAC-List Configuration • MT - MAC-acl • PE - Privileged EXEC • PM - Policy Map Global Configuration • PCMC - Router Configuration • ROSPF - Router Open Shortest Path First Version 3 • SG -
ARP ACL Configuration • CC - Key Chain • KE - MST Configuration • ML - Policy Class Map Configuration • R - Radius • RIP - Key • L - Logging • LC - ... CP - Captive Portal Configuration • CPI - Class-Map Configuration • GC - Global Configuration • IC - Line Configuration • MA - MAC-List Configuration • MT - MAC-acl • PE - Privileged EXEC • PM - Policy Map Global Configuration • PCMC - Router Configuration • ROSPF - Router Open Shortest Path First Version 3 • SG -
Command Line Interface Guide
Page 62
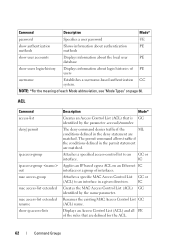
...histories of PE users username Establishes a username-based authentication GC system. IC Creates the MAC Access Control List (ACL) GC identified by the parameter accesslistnumber. Displays an Access Control List (ACL) and all PE of interfaces. Attaches a specified access-control list to an interface in a given direction. ... Displays information about the local user PE database show ip access-lists Description Mode* Creates an Access Control List (ACL) that are matched. The permit command allows traffic if the conditions defined in the deny statement are defined for the...
...histories of PE users username Establishes a username-based authentication GC system. IC Creates the MAC Access Control List (ACL) GC identified by the parameter accesslistnumber. Displays an Access Control List (ACL) and all PE of interfaces. Attaches a specified access-control list to an interface in a given direction. ... Displays information about the local user PE database show ip access-lists Description Mode* Creates an Access Control List (ACL) that are matched. The permit command allows traffic if the conditions defined in the deny statement are defined for the...
Command Line Interface Guide
Page 63
... be IC learned on a IC port. IC forward-unregistered multicast-addresses port. IC port security max Configures the maximum addresses that are defined for the ACL. bridge multicast forward- show bridge address-table Displays statically created entries in port security mode. Command Groups 63 show bridge address-table Displays dynamically created...
... be IC learned on a IC port. IC forward-unregistered multicast-addresses port. IC port security max Configures the maximum addresses that are defined for the ACL. bridge multicast forward- show bridge address-table Displays statically created entries in port security mode. Command Groups 63 show bridge address-table Displays dynamically created...
Command Line Interface Guide
Page 66
... ip arp inspection ip arp inspection filter ip arp inspection limit ip arp inspection trust ip arp inspection validate Description Mode* Creates an ARP ACL. Configures the ARP ACL to the database persistence. Enables additional validation checks like source GC MAC address validation, destination MAC address validation or IP address validation on...
... ip arp inspection ip arp inspection filter ip arp inspection limit ip arp inspection trust ip arp inspection validate Description Mode* Creates an ARP ACL. Configures the ARP ACL to the database persistence. Enables additional validation checks like source GC MAC address validation, destination MAC address validation or IP address validation on...
Command Line Interface Guide
Page 67
... multiple Ethernet type interfaces. GC Enters the interface configuration mode to GC configure an Ethernet type interface. show arp access-list Displays the configured ARP ACLs with the PE rules. Ethernet Configuration Command clear counters description duplex flowcontrol interface ethernet interface range ethernet mtu Description Mode* Clears statistics on all the...
... multiple Ethernet type interfaces. GC Enters the interface configuration mode to GC configure an Ethernet type interface. show arp access-list Displays the configured ARP ACLs with the PE rules. Ethernet Configuration Command clear counters description duplex flowcontrol interface ethernet interface range ethernet mtu Description Mode* Clears statistics on all the...
Command Line Interface Guide
Page 72
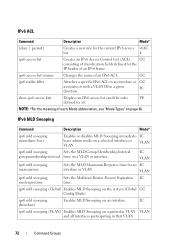
... or VLAN. ipv6 mld snooping (Interface) Enables MLD Snooping on a VLAN or interface. GC ipv6 traffic-filter Attaches a specific IPv6 ACL to an interface or GC associates it ). VLAN ipv6 mld snooping mcrtexpiretime Sets the Multicast Router Present Expiration IC time. L ipv6 access... or disables MLD Snooping immediate- VLAN ipv6 mld snooping Sets the MLD Group Membership Interval groupmembership-interval time on an interface. IPv6 ACL Command Description Mode* {deny | permit} Creates a new rule for an IC interface or VLAN. ipv6 mld snooping (Global) ...
... or VLAN. ipv6 mld snooping (Interface) Enables MLD Snooping on a VLAN or interface. GC ipv6 traffic-filter Attaches a specific IPv6 ACL to an interface or GC associates it ). VLAN ipv6 mld snooping mcrtexpiretime Sets the Multicast Router Present Expiration IC time. L ipv6 access... or disables MLD Snooping immediate- VLAN ipv6 mld snooping Sets the MLD Group Membership Interval groupmembership-interval time on an interface. IPv6 ACL Command Description Mode* {deny | permit} Creates a new rule for an IC interface or VLAN. ipv6 mld snooping (Global) ...
Command Line Interface Guide
Page 122
... abbreviation, see "Mode Types" on the passwords such that GC users are stored to ensure that are required to change passwords when they expire. Management ACL Command Description Mode* deny (management) Defines a deny rule. PE class show management access- Command Description Mode* line Identifies a specific line for configuration. MA show management...
... abbreviation, see "Mode Types" on the passwords such that GC users are stored to ensure that are required to change passwords when they expire. Management ACL Command Description Mode* deny (management) Defines a deny rule. PE class show management access- Command Description Mode* line Identifies a specific line for configuration. MA show management...
Command Line Interface Guide
Page 125
... reception and PE transmission. Serviceability Tracing Command debug arp debug auto-voip debug clear debug console debug dot1x debug igmpsnooping debug ip acl debug ip dvmrp debug ip igmp debug ip mcache debug ip pimdm debug ip pimsm debug ip vrrp debug ipv6 mcache debug ipv6...* Enables tracing of IGMP Snooping packets PE transmitted and/or received by the switch. Enables debug of IP Protocol packets matching PE the ACL criteria. Traces MLD packet reception and transmission. PE Enables Auto VOIP debug messages. Traces IGMP packet reception and PE transmission. PE Disables ...
... reception and PE transmission. Serviceability Tracing Command debug arp debug auto-voip debug clear debug console debug dot1x debug igmpsnooping debug ip acl debug ip dvmrp debug ip igmp debug ip mcache debug ip pimdm debug ip pimsm debug ip vrrp debug ipv6 mcache debug ipv6...* Enables tracing of IGMP Snooping packets PE transmitted and/or received by the switch. Enables debug of IP Protocol packets matching PE the ACL criteria. Traces MLD packet reception and transmission. PE Enables Auto VOIP debug messages. Traces IGMP packet reception and PE transmission. PE Disables ...
Command Line Interface Guide
Page 187
..., addressing, and checksum functions for transmitting data bits on a particular medium. This section of the document contains the following Layer 2 topics: • AAA Commands • ACL Commands • Address Table Commands • CDP Interoperability Commands • DHCP Layer 2 Relay Commands • DHCP Snooping Commands • Dynamic ARP Inspection Commands • Ethernet...
..., addressing, and checksum functions for transmitting data bits on a particular medium. This section of the document contains the following Layer 2 topics: • AAA Commands • ACL Commands • Address Table Commands • CDP Interoperability Commands • DHCP Layer 2 Relay Commands • DHCP Snooping Commands • Dynamic ARP Inspection Commands • Ethernet...
Command Line Interface Guide
Page 205
ACL Commands This chapter explains the following commands: • access-list • deny | permit • ip access-group • no ip access-group • mac access-group • mac access-list extended • mac access-list extended rename • show ip access-lists • show mac access-list 4 ACL Commands 205
ACL Commands This chapter explains the following commands: • access-list • deny | permit • ip access-group • no ip access-group • mac access-group • mac access-list extended • mac access-list extended rename • show ip access-lists • show mac access-list 4 ACL Commands 205
Command Line Interface Guide
Page 206
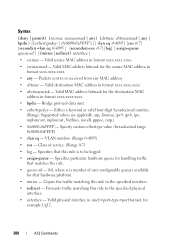
... address. • srcmask - Source IP mask. • dstip - Or you can specify the portkey, which can be logged. 206 ACL Commands Specifies whether the IP ACL rule permits or denies an action. • every - Destination IP mask. • portvalue - Specifies that this rule is to create an... first reference is source match criteria, the second is specified by the parameter list-name. The source layer 4 port match condition for the ACL rule is destination match criteria. • number - Refers to 31 characters in Global Configuration mode to be one of the following keywords: ...
... address. • srcmask - Source IP mask. • dstip - Or you can specify the portkey, which can be logged. 206 ACL Commands Specifies whether the IP ACL rule permits or denies an action. • every - Destination IP mask. • portvalue - Specifies that this rule is to create an... first reference is source match criteria, the second is specified by the parameter list-name. The source layer 4 port match condition for the ACL rule is destination match criteria. • number - Refers to 31 characters in Global Configuration mode to be one of the following keywords: ...
Command Line Interface Guide
Page 207
... Specifies the particular hardware queue for handling traffic that matches the rule. (Range: 0-6) • mirror interface - Examples The following examples create an ACL to discard any userspecified rules, the packet is dropped by the implicit "deny all other traffic from 192.168.77.171, but allow traffic if... copied to deny traffic if the conditions defined in Mac-Access-List Configuration mode to the specified interface. • redirect interface - ACL Commands 207 • assign-queue queue-id - Use the permit command in Mac-Access-List Configuration mode to allow all " rule.
... Specifies the particular hardware queue for handling traffic that matches the rule. (Range: 0-6) • mirror interface - Examples The following examples create an ACL to discard any userspecified rules, the packet is dropped by the implicit "deny all other traffic from 192.168.77.171, but allow traffic if... copied to deny traffic if the conditions defined in Mac-Access-List Configuration mode to the specified interface. • redirect interface - ACL Commands 207 • assign-queue queue-id - Use the permit command in Mac-Access-List Configuration mode to allow all " rule.
Command Line Interface Guide
Page 208
... of user configurable queues available for the source MAC address in format xxxx.xxxx.xxxx. • destmacmask - Specifies particular hardware queue for example 1/g12. 208 ACL Commands
... of user configurable queues available for the source MAC address in format xxxx.xxxx.xxxx. • destmacmask - Specifies particular hardware queue for example 1/g12. 208 ACL Commands
Command Line Interface Guide
Page 209
... ip access-group Use the ip access-group or no ip access-group command to apply/disable an IP based egress ACL on an Ethernet interface or a group of the ACL. (Range: In or out. Access list name. (Range: Valid IP access-list name up to deny traffic from MAC... is not supported, as the rules within an ACL cannot be deleted and respecified. Example The following example configures a MAC ACL to 31 characters in .) ACL Commands 209 An IP based ACL should have been created by the access-list ... Rather the entire ACL must be deleted individually. command with the same name...
... ip access-group Use the ip access-group or no ip access-group command to apply/disable an IP based egress ACL on an Ethernet interface or a group of the ACL. (Range: In or out. Access list name. (Range: Valid IP access-list name up to deny traffic from MAC... is not supported, as the rules within an ACL cannot be deleted and respecified. Example The following example configures a MAC ACL to 31 characters in .) ACL Commands 209 An IP based ACL should have been created by the access-list ... Rather the entire ACL must be deleted individually. command with the same name...
Command Line Interface Guide
Page 210
...no default configuration. A lower sequence number has higher precedence. Command Mode Global and Interface Configuration User Guidelines Global mode command configures the ACL on all the interfaces, whereas the interface mode command does so for this interface and direction. (Range: 1-4294967295) 210... ACL Commands Name of access list relative to other access lists already assigned to an interface in a given direction. Range: 1 - 4294967295. • seqnum ...
...no default configuration. A lower sequence number has higher precedence. Command Mode Global and Interface Configuration User Guidelines Global mode command configures the ACL on all the interfaces, whereas the interface mode command does so for this interface and direction. (Range: 1-4294967295) 210... ACL Commands Name of access list relative to other access lists already assigned to an interface in a given direction. Range: 1 - 4294967295. • seqnum ...