User Manual
Page 83
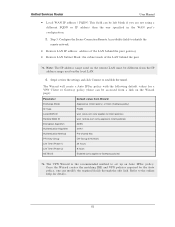
Step4: review the settings and click Connect to set up an Auto IPSec policy. Refer to the online help for a VPN Client or Gateway policy (these can modify the required fields through the edit link. Unified Services Router User Manual • Local WAN IP address / FQDN: This field can be left ...: the subnet mask of the LAN behind the peer Note: The IP address range used on the remote LAN must be accessed from a link on the Wizard page): Parameter Exchange Mode ID Type Local WAN ID Remote WAN ID Encryption Algorithm Authentication Algorithm Authentication Method PFS Key-Group Life...
Step4: review the settings and click Connect to set up an Auto IPSec policy. Refer to the online help for a VPN Client or Gateway policy (these can modify the required fields through the edit link. Unified Services Router User Manual • Local WAN IP address / FQDN: This field can be left ...: the subnet mask of the LAN behind the peer Note: The IP address range used on the remote LAN must be accessed from a link on the Wizard page): Parameter Exchange Mode ID Type Local WAN ID Remote WAN ID Encryption Algorithm Authentication Algorithm Authentication Method PFS Key-Group Life...
User Manual
Page 93
... is located on the router itself. The guest does not have SSL VPN access. • SSL VPN User: This user has access to observe and review configuration settings. It is not part of the local user database. • L2TP User: These are L2TP VPN tunnel LAN users that can establish a tunnel...
... is located on the router itself. The guest does not have SSL VPN access. • SSL VPN User: This user has access to observe and review configuration settings. It is not part of the local user database. • L2TP User: These are L2TP VPN tunnel LAN users that can establish a tunnel...
User Manual
Page 111
... settings for Logging User Manual The display for logging can be tracked based on where the logs are those that is logged for later review. Traffic through each network segment (LAN, WAN, DMZ) can be customized based on whether the packet was accepted or dropped by the... the Status > Logs page) or a remote Syslog server for display in a subsequent section, follow the same configuration as logs configured for review by the firewall. This option is particularly useful when the Default Outbound Policy is passed through the corresponding network segment (i.e. LAN to determine the...
... settings for Logging User Manual The display for logging can be tracked based on where the logs are those that is logged for later review. Traffic through each network segment (LAN, WAN, DMZ) can be customized based on whether the packet was accepted or dropped by the... the Status > Logs page) or a remote Syslog server for display in a subsequent section, follow the same configuration as logs configured for review by the firewall. This option is particularly useful when the Default Outbound Policy is passed through the corresponding network segment (i.e. LAN to determine the...
User Manual
Page 128
... 86: Resource Utilization data (continued) User Manual 10.2 Traffic Statistics 10.2.1 Wired Port Statistics Status > Traffic Monitor > Device Statistics Detailed transmit and receive statistics for review.
... 86: Resource Utilization data (continued) User Manual 10.2 Traffic Statistics 10.2.1 Wired Port Statistics Status > Traffic Monitor > Device Statistics Detailed transmit and receive statistics for review.