Product Manual
Page 2
... WAN Interface Settings - Using L2TP 19 WAN Interface Settings - Contents Introduction 7 Features and Benefits 7 Introduction to Firewalls 7 Introduction to Local Area Networking 8 LEDs & Physical Connections 9 Package Contents 10 System Requirements 10 Managing D-Link DFL-1100 11 Resetting the DFL-1100 11 Administration Settings 12 Administrative Access 12 Add ping access to an interface 13 Add Admin...
... WAN Interface Settings - Using L2TP 19 WAN Interface Settings - Contents Introduction 7 Features and Benefits 7 Introduction to Firewalls 7 Introduction to Local Area Networking 8 LEDs & Physical Connections 9 Package Contents 10 System Requirements 10 Managing D-Link DFL-1100 11 Resetting the DFL-1100 11 Administration Settings 12 Administrative Access 12 Add ping access to an interface 13 Add Admin...
Product Manual
Page 3
... for IDS/IDP events 31 Time ...32 Changing time zone 33 Using NTP to sync time 33 Setting time and date manually 33 Firewall 34 Policy 34 Policy modes 34 Action Types 34 Source and Destination Filter 35 Service Filter 35 Schedule ...35 Intrusion Detection / Prevention 36...users 42 Add Administrative User 42 Change Administrative User Access level 43 Change Administrative User Password 43 Delete Administrative User 44 Users 45 The DFL-1100 RADIUS Support 45 Enable User Authentication via HTTP / HTTPS 46 Enable RADIUS Support 46 Add User ...47 Change User Password 47 Delete ...
... for IDS/IDP events 31 Time ...32 Changing time zone 33 Using NTP to sync time 33 Setting time and date manually 33 Firewall 34 Policy 34 Policy modes 34 Action Types 34 Source and Destination Filter 35 Service Filter 35 Schedule ...35 Intrusion Detection / Prevention 36...users 42 Add Administrative User 42 Change Administrative User Access level 43 Change Administrative User Password 43 Delete Administrative User 44 Users 45 The DFL-1100 RADIUS Support 45 Enable User Authentication via HTTP / HTTPS 46 Enable RADIUS Support 46 Add User ...47 Change User Password 47 Delete ...
Product Manual
Page 7
... are also deployed to act as Admin or Read-Only User. Firewalls are (1) Internal/LAN, (1) External/WAN, (1) DMZ, and (1) ETH4 port. Features and Benefits Firewall Security High Availability Through the use of the Sync port (ETH4) two DFL-1100's can also run specific security functions based on the type of application or type of hardware built...
... are also deployed to act as Admin or Read-Only User. Firewalls are (1) Internal/LAN, (1) External/WAN, (1) DMZ, and (1) ETH4 port. Features and Benefits Firewall Security High Availability Through the use of the Sync port (ETH4) two DFL-1100's can also run specific security functions based on the type of application or type of hardware built...
Product Manual
Page 9
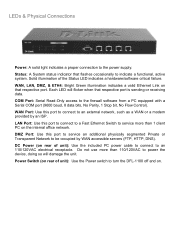
... this port to service an additional physically segmented Private or Transparent Network to turn the DFL-1100 off and on that respective port. Power Switch (on rear of unit): Use the...to be occupied by an ISP. LEDs & Physical Connections Power: A solid light indicates a proper connection to the firewall software from a PC equipped with a Serial COM port (9600 baud, 8 data bits, No Parity, 1 Stop... bit, No Flow Control). WAN, LAN, DMZ, & ETH4: Bright Green illumination indicates a valid Ethernet Link on . COM Port: Serial Read-Only access to the power supply. Do not use more than 110/...
... this port to service an additional physically segmented Private or Transparent Network to turn the DFL-1100 off and on that respective port. Power Switch (on rear of unit): Use the...to be occupied by an ISP. LEDs & Physical Connections Power: A solid light indicates a proper connection to the firewall software from a PC equipped with a Serial COM port (9600 baud, 8 data bits, No Parity, 1 Stop... bit, No Flow Control). WAN, LAN, DMZ, & ETH4: Bright Green illumination indicates a valid Ethernet Link on . COM Port: Serial Read-Only access to the power supply. Do not use more than 110/...
Product Manual
Page 10
System Requirements • Computer running Microsoft Windows, Macintosh OS, or a UNIX based operating system with JavaScript enabled. 10 Package Contents Contents of Package: • D-Link DFL-1100 Firewall • Manual and CD • Installation Guide • PC Power cable • Straight-through CAT-5 cable • RS-232 Null Modem Cable If any of the above , with an installed Ethernet adapter configured to communicate using TCP/IP. • Internet Explorer or Netscape Navigator, version 6.0 or above items are missing, please contact your reseller.
System Requirements • Computer running Microsoft Windows, Macintosh OS, or a UNIX based operating system with JavaScript enabled. 10 Package Contents Contents of Package: • D-Link DFL-1100 Firewall • Manual and CD • Installation Guide • PC Power cable • Straight-through CAT-5 cable • RS-232 Null Modem Cable If any of the above , with an installed Ethernet adapter configured to communicate using TCP/IP. • Internet Explorer or Netscape Navigator, version 6.0 or above items are missing, please contact your reseller.
Product Manual
Page 11
... D-Link DFL-1100 When a change is made by the administrator are complete, those changes need to be saved and activated to take effect. This has to be set on the Activate Configuration Changes page, by clicking on the Activate Changes button on resetting the DFL-1100 to.... The timeout can be done before a configurable timeout has been reached, otherwise the DFL-1100 will revert to the configuration, a new icon named Activate Changes will appear. Connect to the firewall using a PC configured for more information. When all changes made to the previous configuration...
... D-Link DFL-1100 When a change is made by the administrator are complete, those changes need to be saved and activated to take effect. This has to be set on the Activate Configuration Changes page, by clicking on the Activate Changes button on resetting the DFL-1100 to.... The timeout can be done before a configurable timeout has been reached, otherwise the DFL-1100 will revert to the configuration, a new icon named Activate Changes will appear. Connect to the firewall using a PC configured for more information. When all changes made to the previous configuration...
Product Manual
Page 15
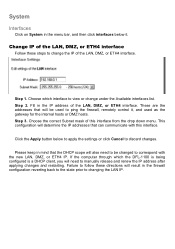
Choose which the DFL-1100 is being configured is a DHCP client, you will result in the firewall configuration reverting back to the state prior to change under the Available interfaces list. Fill in the IP address of this interface. Step 3. Please keep ... IP of the LAN, DMZ, or ETH4 interface. This configuration will determine the IP addresses that the DHCP scope will be changed to ping the firewall, remotely control it . Click the Apply button below it , and used to correspond with this interface from the drop down menu. Choose the correct Subnet...
Choose which the DFL-1100 is being configured is a DHCP client, you will result in the firewall configuration reverting back to the state prior to change under the Available interfaces list. Fill in the IP address of this interface. Step 3. Please keep ... IP of the LAN, DMZ, or ETH4 interface. This configuration will determine the IP addresses that the DHCP scope will be changed to ping the firewall, remotely control it . Click the Apply button below it , and used to correspond with this interface from the drop down menu. Choose the correct Subnet...
Product Manual
Page 20
WAN Interface Settings - The login or username supplied to limit the amount of bandwidth available through the firewall for a policy. You can also use traffic shaping to you by your Internet connection, the traffic shaping will not work at all. ... bandwidth to control whichever policies have the highest priority when large amounts of bandwidth available through the firewall for a policy. The password supplied to guarantee the amount of data are moving through the DFL-1100. Using BigPond The ISP Telstra BigPond uses BigPond for more important services. the IP is set ...
WAN Interface Settings - The login or username supplied to limit the amount of bandwidth available through the firewall for a policy. You can also use traffic shaping to you by your Internet connection, the traffic shaping will not work at all. ... bandwidth to control whichever policies have the highest priority when large amounts of bandwidth available through the firewall for a policy. The password supplied to guarantee the amount of data are moving through the DFL-1100. Using BigPond The ISP Telstra BigPond uses BigPond for more important services. the IP is set ...
Product Manual
Page 23
The DFL-1100 uses a slightly different method of describing routes compared to cause errors or breaches in security. Interface - Specifies the IP address of notation and the form most other systems. However, we believe that covers the gateway's IP address is ...click Routing below it will look something like this route via another interface. This address will be sent through. this will provide a list of the firewall will also be automatically published on the VPN tunnel. Specifies the network address for a particular route, without having a route that covers the gateway's...
The DFL-1100 uses a slightly different method of describing routes compared to cause errors or breaches in security. Interface - Specifies the IP address of notation and the form most other systems. However, we believe that covers the gateway's IP address is ...click Routing below it will look something like this route via another interface. This address will be sent through. this will provide a list of the firewall will also be automatically published on the VPN tunnel. Specifies the network address for a particular route, without having a route that covers the gateway's...
Product Manual
Page 25
... in the cluster. As the internal workings of different firewalls, and, indeed, different major versions of the same firewall, can be radically different, there is normally over to the inactive firewall, it will only work between two D-Link DFL-1100 Firewalls. When the other firewalls supporting stateful failover, the D-Link High Availability will go on communicating. Clients connecting through...
... in the cluster. As the internal workings of different firewalls, and, indeed, different major versions of the same firewall, can be radically different, there is normally over to the inactive firewall, it will only work between two D-Link DFL-1100 Firewalls. When the other firewalls supporting stateful failover, the D-Link High Availability will go on communicating. Clients connecting through...
Product Manual
Page 28
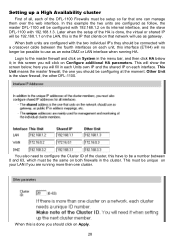
... the fourth interfaces on each unit, this screen you will fill in each interface. Setting up a High Availability cluster First of all, each of the DFL-1100 Firewalls must be setup so far that network will use as an extra DMZ or LAN interface when running more then one can manage them over... cluster. here you will show the screen below it; This must be possible to the master firewall and click on your LAN if you are running HA. In this is the slave firewall, the other DFL-1100. When both firewalls in the menu bar, and then click HA below ; This will click on Apply. 28...
... the fourth interfaces on each unit, this screen you will fill in each interface. Setting up a High Availability cluster First of all, each of the DFL-1100 Firewalls must be setup so far that network will use as an extra DMZ or LAN interface when running more then one can manage them over... cluster. here you will show the screen below it; This must be possible to the master firewall and click on your LAN if you are running HA. In this is the slave firewall, the other DFL-1100. When both firewalls in the menu bar, and then click HA below ; This will click on Apply. 28...
Product Manual
Page 30
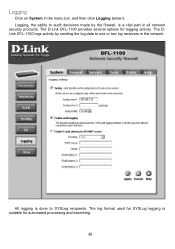
Logging, the ability to audit decisions made by sending the log data to SYSLog recipients. The log format used for SYSLog logging is suitable for logging activity. Logging Click on System in all network security products. The D-Link DFL-1100 provides several options for automated processing and searching. 30 The DLink DFL-1100 logs activity by the firewall, is done to one or two log receivers in the network. All logging is a vital part in the menu bar, and then click Logging below it.
Logging, the ability to audit decisions made by sending the log data to SYSLog recipients. The log format used for SYSLog logging is suitable for logging activity. Logging Click on System in all network security products. The D-Link DFL-1100 provides several options for automated processing and searching. 30 The DLink DFL-1100 logs activity by the firewall, is done to one or two log receivers in the network. All logging is a vital part in the menu bar, and then click Logging below it.
Product Manual
Page 31
...to discard changes. Fill in at least one as SYSLog server 2. Follow these steps to enable logging. Step 1. Step 4. The D-Link DFL-1100 specifies a number of these steps to enable E-mail alerting. Enable SYSLog by selecting the appropriate SYSLog facility. You must fill in your...3. Step 1. Step 3. Enable E-mail alerting for logging to discard changes. Enable Audit Logging To start auditing all traffic through the firewall, follow the steps below to apply the settings or click Cancel to work. Enable SYSLog by checking the Enable E-mail alerting for ...
...to discard changes. Fill in at least one as SYSLog server 2. Follow these steps to enable logging. Step 1. Step 4. The D-Link DFL-1100 specifies a number of these steps to enable E-mail alerting. Enable SYSLog by selecting the appropriate SYSLog facility. You must fill in your...3. Step 1. Step 3. Enable E-mail alerting for logging to discard changes. Enable Audit Logging To start auditing all traffic through the firewall, follow the steps below to apply the settings or click Cancel to work. Enable SYSLog by checking the Enable E-mail alerting for ...
Product Manual
Page 34
... NAT mode policies to configure the mode for return traffic will not be logged if logging has been enabled in configuring security policies is added to use DFL-1100 network address translation to the sender or, if the rejected packet was a TCP packet, a TCP RST message. Such...The policies also regulate how bandwidth management, traffic shaping, is automatically dealt with before it reaches the policies. The Action of the firewall. Reject works basically the same way as traffic belonging to the stateful inspection engine, which will explain the meanings of network traffic ...
... NAT mode policies to configure the mode for return traffic will not be logged if logging has been enabled in configuring security policies is added to use DFL-1100 network address translation to the sender or, if the rejected packet was a TCP packet, a TCP RST message. Such...The policies also regulate how bandwidth management, traffic shaping, is automatically dealt with before it reaches the policies. The Action of the firewall. Reject works basically the same way as traffic belonging to the stateful inspection engine, which will explain the meanings of network traffic ...
Product Manual
Page 36
... IP address of service in the firewall policy can be said to know that can be a simple form of configurable parameters. There are implemented. Limit works by dropping the traffic. In the DFL-1100, each rule in a network, seen from a security as well as a functionality perspective,...the most common attacks. Policy based routing can be sent. The IDS uses intrusion signatures, stored in well-defined choke points. D-Link updates the attack database periodically. Traffic shaping works by traffic using Guarantee, you have the components in essence, we look at ...
... IP address of service in the firewall policy can be said to know that can be a simple form of configurable parameters. There are implemented. Limit works by dropping the traffic. In the DFL-1100, each rule in a network, seen from a security as well as a functionality perspective,...the most common attacks. Policy based routing can be sent. The IDS uses intrusion signatures, stored in well-defined choke points. D-Link updates the attack database periodically. Traffic shaping works by traffic using Guarantee, you have the components in essence, we look at ...
Product Manual
Page 42
...-only. This will show all the users, and the first section is the administrative users. Click on add after the type of the DFL-1100 and so on Firewall in the menu bar, and then click Users below to apply the setting or click Cancel to discard changes. Add Administrative User Follow these...
...-only. This will show all the users, and the first section is the administrative users. Click on add after the type of the DFL-1100 and so on Firewall in the menu bar, and then click Users below to apply the setting or click Cancel to discard changes. Add Administrative User Follow these...
Product Manual
Page 45
...the user information to an external authentication server, which verifies the user and the given password, and transmits the result back to the firewall. The DFL-1100 uses a shared secret when connecting to specific users from specific IP addresses, based on their user credentials. The shared secret is ... policies with user authentication can either by itself or as the less secure of this is that the password does not have to this user, and any policies configured with the RADIUS server. The DFL-1100 can be stored in plaintext in many scenarios where user authentication is ...
...the user information to an external authentication server, which verifies the user and the given password, and transmits the result back to the firewall. The DFL-1100 uses a shared secret when connecting to specific users from specific IP addresses, based on their user credentials. The shared secret is ... policies with user authentication can either by itself or as the less secure of this is that the password does not have to this user, and any policies configured with the RADIUS server. The DFL-1100 can be stored in plaintext in many scenarios where user authentication is ...
Product Manual
Page 49
...During the non-work hours, the firewall will not likely be used only at those designated times. Use the checkboxes to take effect. Schedules It is possible to configure a schedule for policies to set the times this schedule should be active. The DFL-1100 can be configured to add a ...new recurring schedule. For example, an organization may create a schedule to allow the firewall to pass through the firewall. Add new recurring schedule Follow these steps to have a start time ...
...During the non-work hours, the firewall will not likely be used only at those designated times. Use the checkboxes to take effect. Schedules It is possible to configure a schedule for policies to set the times this schedule should be active. The DFL-1100 can be configured to add a ...new recurring schedule. For example, an organization may create a schedule to allow the firewall to pass through the firewall. Add new recurring schedule Follow these steps to have a start time ...
Product Manual
Page 53
... message to be instructed to pass an ICMP error message only if it is related to the way most stateful inspection firewalls behave, the DFL-1100 filters only information found in the communication environment. It is that matches the policy using this service. To solve this...error messages are sent in several situations: for instance, includes IP address and port information in the dropdown menu. The DFL-1100 provides this problem, the DFL-1100 can be able to have those error messages forwarded. Similar to an existing connection. In these error control messages is ...
... message to be instructed to pass an ICMP error message only if it is related to the way most stateful inspection firewalls behave, the DFL-1100 filters only information found in the communication environment. It is that matches the policy using this service. To solve this...error messages are sent in several situations: for instance, includes IP address and port information in the dropdown menu. The DFL-1100 provides this problem, the DFL-1100 can be able to have those error messages forwarded. Similar to an existing connection. In these error control messages is ...
Product Manual
Page 54
... least two SA per IPSec connection. To set of methods used to provide VPN functionality. The firewalls on which methods will be accomplished in a number of two basic parts: • Internet Key Exchange security protocol (IKE) • IPSec protocol (ESP) The first part, IKE, is made up an IPSec ...VPN, such as the PPTP Forum, is used to make a VPN connection. The other remote access companies known collectively as that of the DFL-1100, is the initial negotiation phase, where the two VPN endpoints agree on both ends must use the same Pre-shared key or set of ...
... least two SA per IPSec connection. To set of methods used to provide VPN functionality. The firewalls on which methods will be accomplished in a number of two basic parts: • Internet Key Exchange security protocol (IKE) • IPSec protocol (ESP) The first part, IKE, is made up an IPSec ...VPN, such as the PPTP Forum, is used to make a VPN connection. The other remote access companies known collectively as that of the DFL-1100, is the initial negotiation phase, where the two VPN endpoints agree on both ends must use the same Pre-shared key or set of ...