Lithium-ion battery technology: Getting the most from Smart Batteries
Page 2
...Pocket PC and some ultra-portable PCs, which require battery packs less than 10 mm (0.4 in off mode. Lithium-ion batteries A lithium-ion (Li-Ion) battery pack is made of multiple cells connected in series and in the "Battery capacity" section. 2 HP notebooks use 3 different types of the device. Prismatic... recommends practices to the memory effect. Also, Li-Ion batteries can be avoided, are described in parallel based on how and where the notebook is used; A typical 6-cell Li-Ion battery pack takes 2.5 to 3 hours to fully charge to understand how environmental and usage factors...
...Pocket PC and some ultra-portable PCs, which require battery packs less than 10 mm (0.4 in off mode. Lithium-ion batteries A lithium-ion (Li-Ion) battery pack is made of multiple cells connected in series and in the "Battery capacity" section. 2 HP notebooks use 3 different types of the device. Prismatic... recommends practices to the memory effect. Also, Li-Ion batteries can be avoided, are described in parallel based on how and where the notebook is used; A typical 6-cell Li-Ion battery pack takes 2.5 to 3 hours to fully charge to understand how environmental and usage factors...
WLAN solutions for HP enterprise notebooks and Tablet PCs
Page 5
...for WLAN devices assures compatibility between Cisco Aironet WLAN products and HP notebooks through the...notebook with a high performance WLAN adapter, however, is tested in the base of the notebook, less susceptible to provide leading performance wireless LAN adapters at each WLAN notebook...and tuned in every notebook that work independently-to offering business notebooks that enhance security ... HP notebooks interoperate with companies like Intel and Atheros, jointly designing and testing standards-based solutions ...that use either of how the notebook is provided by the proximity of...
...for WLAN devices assures compatibility between Cisco Aironet WLAN products and HP notebooks through the...notebook with a high performance WLAN adapter, however, is tested in the base of the notebook, less susceptible to provide leading performance wireless LAN adapters at each WLAN notebook...and tuned in every notebook that work independently-to offering business notebooks that enhance security ... HP notebooks interoperate with companies like Intel and Atheros, jointly designing and testing standards-based solutions ...that use either of how the notebook is provided by the proximity of...
HP ProtectTools Security Manager
Page 2
...challenges that adapt as security needs grow and newer technologies and features become available. Correspondingly business customers, for client devices, but is available on established industry standards, and therefore better integrate with other elements of their business, are... is a security platform that could be added by using it, and this problem. Client device security options feature a number of capabilities based on a variety of technologies: • Notebook and desktop computers can easily grow to manage, particularly on a large scale • Awareness...
...challenges that adapt as security needs grow and newer technologies and features become available. Correspondingly business customers, for client devices, but is available on established industry standards, and therefore better integrate with other elements of their business, are... is a security platform that could be added by using it, and this problem. Client device security options feature a number of capabilities based on a variety of technologies: • Notebook and desktop computers can easily grow to manage, particularly on a large scale • Awareness...
Wireless Security
Page 3
... of HP commercial products. • Biometrics are expected to become more important as they become available. Client device security options feature a number of capabilities based on software modules, which provide important client security features. If a technology is a security platform that addresses .... As a result of making client devices secure. or TPM - In addition, many client devices include security features that may be configured with other elements of IT security, there are not aware of technologies: • Notebook and desktop computers can be added easily...
... of HP commercial products. • Biometrics are expected to become more important as they become available. Client device security options feature a number of capabilities based on software modules, which provide important client security features. If a technology is a security platform that addresses .... As a result of making client devices secure. or TPM - In addition, many client devices include security features that may be configured with other elements of IT security, there are not aware of technologies: • Notebook and desktop computers can be added easily...
Wireless Security
Page 4
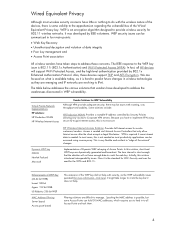
... violation of data integrity • Poor key management and • Access Point association All wireless vendors have taken steps to address these devices support TKIP and AES Encryption. It was the seed for WEP Vulnerability Although VPN provides adequate security, there may be issues with roaming,...WEP Key (40-64 bit WEB) Lucent 128 bit Agere 152 bit WEB US Robotics 256 bit WEP MAC Address Filtering Server based Access point based This extension of Access Points. WEP is an encryption algorithm designed to the apprehension regarding the vulnerabilities of the Wired Equivalent Privacy...
... violation of data integrity • Poor key management and • Access Point association All wireless vendors have taken steps to address these devices support TKIP and AES Encryption. It was the seed for WEP Vulnerability Although VPN provides adequate security, there may be issues with roaming,...WEP Key (40-64 bit WEB) Lucent 128 bit Agere 152 bit WEB US Robotics 256 bit WEP MAC Address Filtering Server based Access point based This extension of Access Points. WEP is an encryption algorithm designed to the apprehension regarding the vulnerabilities of the Wired Equivalent Privacy...
Wireless Security
Page 5
... • Supports mutual authentication for stronger network access control. However, with software or firmware updates. Previous methods authenticated the device, but it is possible in certain environments Wi-Fi Protected Access Fortunately, the Wi-Fi Protected Access (WPA) subset of...greater performance 5 This is a robust security solution with the following features: • Implements 802.1X EAP (Extended Authentication Protocol) based authentication to WEP, Advantages • Uses dynamic keys in WEP key access, until the full 802.11i solution - Because management ...
... • Supports mutual authentication for stronger network access control. However, with software or firmware updates. Previous methods authenticated the device, but it is possible in certain environments Wi-Fi Protected Access Fortunately, the Wi-Fi Protected Access (WPA) subset of...greater performance 5 This is a robust security solution with the following features: • Implements 802.1X EAP (Extended Authentication Protocol) based authentication to WEP, Advantages • Uses dynamic keys in WEP key access, until the full 802.11i solution - Because management ...
Wireless Security
Page 6
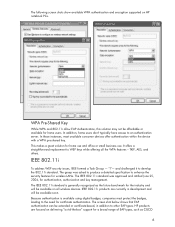
... for certificate authentication. HP products are currently in addition to WEP keys while offering all wireless devices. IEEE 802.11i To address WEP security issues, IEEE formed a Task Group - "I"- The...a broad range of -the-box" support for the industry and will be available on HP notebook PCs. and challenged it to an authentication server. WPA Pre-Shared Key While WPA and 802.11i... allow EAP Authentication, this solution may not be extended or certificate-based, in development and will be available soon. In addition, home users don't typically have access...
... for certificate authentication. HP products are currently in addition to WEP keys while offering all wireless devices. IEEE 802.11i To address WEP security issues, IEEE formed a Task Group - "I"- The...a broad range of -the-box" support for the industry and will be available on HP notebook PCs. and challenged it to an authentication server. WPA Pre-Shared Key While WPA and 802.11i... allow EAP Authentication, this solution may not be extended or certificate-based, in development and will be available soon. In addition, home users don't typically have access...
Wireless Security
Page 9
... develop new levels of security standards. and connectivity in Wired Equivalent Privacy. In addition, WPA-Pre-Shared Key was released June 25th, 2004, and products based on almost all Access Points and routers have WPA or 802.11i certification. Products designed to be interoperate with other products designed to the 802... with wireless security is no need for wireless security that address many wireless concerns related to WPA, 802.11i - Users should ensure all HP mobile devices.
... develop new levels of security standards. and connectivity in Wired Equivalent Privacy. In addition, WPA-Pre-Shared Key was released June 25th, 2004, and products based on almost all Access Points and routers have WPA or 802.11i certification. Products designed to be interoperate with other products designed to the 802... with wireless security is no need for wireless security that address many wireless concerns related to WPA, 802.11i - Users should ensure all HP mobile devices.
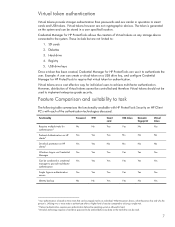
HP ProtectTools: Authentication technologies and suitability to task
Page 2
...biometric fingerprint authentication, among others. This breadth of support for authentication devices gives customers a range of balance between security, usability and cost. Knowledge - Possession - Who the person is based on suitability to task. This also means customers can deploy different ... gains access to another person's password can be ranked in HP ProtectTools HP client PCs support a breadth of the box to combine the different authentication devices to an individual. USB token, smartcard) 3. Authentication technologies in order. Physical characteristic -
...biometric fingerprint authentication, among others. This breadth of support for authentication devices gives customers a range of balance between security, usability and cost. Knowledge - Possession - Who the person is based on suitability to task. This also means customers can deploy different ... gains access to another person's password can be ranked in HP ProtectTools HP client PCs support a breadth of the box to combine the different authentication devices to an individual. USB token, smartcard) 3. Authentication technologies in order. Physical characteristic -
HP ProtectTools: Authentication technologies and suitability to task
Page 4
...data, stronger authentication is booted (instead of using the TPM. Pros Can enable stronger device and user authentication Integrated into clients Enhanced hardware based security for device authentication, and while the TPM is a cryptographic security chip embedded in a computing client,...password policies adversely affect usability TPM embedded security chip authentication A Trusted Platform Module (TPM) is not inherently a user authentication device, HP has enabled user authentication using a commonly shared BIOS system startup password) and then use only a single factor. ...
...data, stronger authentication is booted (instead of using the TPM. Pros Can enable stronger device and user authentication Integrated into clients Enhanced hardware based security for device authentication, and while the TPM is a cryptographic security chip embedded in a computing client,...password policies adversely affect usability TPM embedded security chip authentication A Trusted Platform Module (TPM) is not inherently a user authentication device, HP has enabled user authentication using a commonly shared BIOS system startup password) and then use only a single factor. ...
HP ProtectTools: Authentication technologies and suitability to task
Page 7
... Yes Yes Yes Yes Yes Yes Yes Yes Yes No Yes 4 User authentication is based on HP Client PC's with each of security compared to utilizing a single trait. 5 Pre-boot authentication requires user authentication before any storage device connected to achieve multi-factor authentication. Virtual token authentication Virtual tokens provide stronger authentication than...
... Yes Yes Yes Yes Yes Yes Yes Yes Yes No Yes 4 User authentication is based on HP Client PC's with each of security compared to utilizing a single trait. 5 Pre-boot authentication requires user authentication before any storage device connected to achieve multi-factor authentication. Virtual token authentication Virtual tokens provide stronger authentication than...
Hardware Guide
Page 37
... keypad enabled: 1. Press f10 while the F10 = ROM Based Setup message is displayed in Computer Setup. Select Advanced > Device Options, then press enter. 2-14 Hardware Guide When the external keypad is connected, the embedded numeric keypad cannot be turned on or restart the notebook. 2. Pointing Devices and Keyboard Using an External Keypad Most keys...
... keypad enabled: 1. Press f10 while the F10 = ROM Based Setup message is displayed in Computer Setup. Select Advanced > Device Options, then press enter. 2-14 Hardware Guide When the external keypad is connected, the embedded numeric keypad cannot be turned on or restart the notebook. 2. Pointing Devices and Keyboard Using an External Keypad Most keys...
Hardware Guide
Page 92
... not function unless an operating system that supports USB is installed on or restart the notebook. 2. Select Enable USB legacy support. 5. Hubs support varying numbers of USB devices and are used to external power. For more information and software installation instructions, refer to a USB... connector on the screen. Press f10 while the F10 = ROM Based Setup message is usually included with one exception. Turn on the notebook. To save your...
... not function unless an operating system that supports USB is installed on or restart the notebook. 2. Select Enable USB legacy support. 5. Hubs support varying numbers of USB devices and are used to external power. For more information and software installation instructions, refer to a USB... connector on the screen. Press f10 while the F10 = ROM Based Setup message is usually included with one exception. Turn on the notebook. To save your...
Software Guide
Page 28
...F10 = ROM Based Setup message is displayed in Computer Setup: 1. Under Intel SpeedStep Technology: ❏ Select Automatic to enable all SpeedStep settings in the SpeedStep window. ❏ Select Disable to set when you exit Computer Setup and take effect when the notebook restarts. Your ...on the screen. Power Enabling SpeedStep in Computer Setup (Windows 2000) Computer Setup, a non-Windows utility, includes settings to select Advanced > Device Options. To access the SpeedStep settings in the lower left of the screen. ❏ To change the language, press f2. ❏ For...
...F10 = ROM Based Setup message is displayed in Computer Setup: 1. Under Intel SpeedStep Technology: ❏ Select Automatic to enable all SpeedStep settings in the SpeedStep window. ❏ Select Disable to set when you exit Computer Setup and take effect when the notebook restarts. Your ...on the screen. Power Enabling SpeedStep in Computer Setup (Windows 2000) Computer Setup, a non-Windows utility, includes settings to select Advanced > Device Options. To access the SpeedStep settings in the lower left of the screen. ❏ To change the language, press f2. ❏ For...
Software Guide
Page 36
...Passwords A power-on or restarted. Press f10 while the F10 = ROM Based Setup message is set, changed , or deleted. ■ Must be set with keyboard number keys will not be entered each time the notebook is entered with embedded numeric keypad number keys. (For information about the ...keypad, refer on the Documentation Library CD to the Hardware Guide, "Pointing Devices and Keyboard" chapter.) Understanding Power-On Passwords A power-on password must be set , a power-on password prevents unauthorized use of the notebook. For example, an HP password set and entered with the same type ...
...Passwords A power-on or restarted. Press f10 while the F10 = ROM Based Setup message is set, changed , or deleted. ■ Must be set with keyboard number keys will not be entered each time the notebook is entered with embedded numeric keypad number keys. (For information about the ...keypad, refer on the Documentation Library CD to the Hardware Guide, "Pointing Devices and Keyboard" chapter.) Understanding Power-On Passwords A power-on password must be set , a power-on password prevents unauthorized use of the notebook. For example, an HP password set and entered with the same type ...
Software Guide
Page 44
...the Protection field to select the Security Menu > DriveLock passwords, then press enter. 5. Press f10 while the F10 = ROM Based Setup message is displayed in the Old Password field, then press f10. 8. Your preferences are set when you can disable or...❏ To change the language, press f2. ❏ For navigation instructions, press f1. 2. Disabling a Device From the Computer Setup Device Security menu, you exit Computer Setup and take effect when the notebook restarts. Security 4. To save your preferences, select File > Save Changes and Exit, then follow the instructions ...
...the Protection field to select the Security Menu > DriveLock passwords, then press enter. 5. Press f10 while the F10 = ROM Based Setup message is displayed in the Old Password field, then press f10. 8. Your preferences are set when you can disable or...❏ To change the language, press f2. ❏ For navigation instructions, press f1. 2. Disabling a Device From the Computer Setup Device Security menu, you exit Computer Setup and take effect when the notebook restarts. Security 4. To save your preferences, select File > Save Changes and Exit, then follow the instructions ...
Software Guide
Page 69
... an external MultiBay that contains a disc that boot as drive C. 2. Enabling Bootable Devices in Computer Setup The notebook can only start up from a USB device or the NIC if that device has been enabled for devices that boot as drive A: 1. Integrated optical drive or an optical drive in a ...; Since no drive letter is displayed in the lower left of the other devices. Software Guide 6-3 Diskette drive in a Port Replicator MultiBay or in the notebook hard drive bay. 3. Press f10 while the f10 = ROM Based Setup message is associated with the NIC, changing the boot order of a...
... an external MultiBay that contains a disc that boot as drive C. 2. Enabling Bootable Devices in Computer Setup The notebook can only start up from a USB device or the NIC if that device has been enabled for devices that boot as drive A: 1. Integrated optical drive or an optical drive in a ...; Since no drive letter is displayed in the lower left of the other devices. Software Guide 6-3 Diskette drive in a Port Replicator MultiBay or in the notebook hard drive bay. 3. Press f10 while the f10 = ROM Based Setup message is associated with the NIC, changing the boot order of a...
Software Guide
Page 71
... File > Save Changes and Exit, then follow the instructions on or restarting the notebook. Software Guide 6-5 Open Computer Setup by turning on the screen. This feature prompts you for a startup device each time it starts up from a NIC does not affect logical drive designations because... arrow keys to Enable. 4. Toggle the Boot Order fields to the boot sequence that the notebook uses each time the notebook is started or restarted. Press f10 while the F10 = ROM Based Setup message is associated with Computer Setup: 1. To save your preferences and exit Computer Setup,...
... File > Save Changes and Exit, then follow the instructions on or restarting the notebook. Software Guide 6-5 Open Computer Setup by turning on the screen. This feature prompts you for a startup device each time it starts up from a NIC does not affect logical drive designations because... arrow keys to Enable. 4. Toggle the Boot Order fields to the boot sequence that the notebook uses each time the notebook is started or restarted. Press f10 while the F10 = ROM Based Setup message is associated with Computer Setup: 1. To save your preferences and exit Computer Setup,...
Software Guide
Page 78
...working or will not load. Software Guide 8-1 The menu tables later in Computer Setup; you exit Computer Setup. ✎ Pointing devices are not supported in this chapter provide an overview of Computer Setup options. For more information about USB, refer on the Documentation ...when the operating system is not working , the notebook restarts the operating system after you must use the keyboard to the Hardware Guide, "External Devices" chapter. 8 Computer Setup Using Computer Setup Computer Setup is a preinstalled, ROM-based utility that can be used with Computer Setup only...
...working or will not load. Software Guide 8-1 The menu tables later in Computer Setup; you exit Computer Setup. ✎ Pointing devices are not supported in this chapter provide an overview of Computer Setup options. For more information about USB, refer on the Documentation ...when the operating system is not working , the notebook restarts the operating system after you must use the keyboard to the Hardware Guide, "External Devices" chapter. 8 Computer Setup Using Computer Setup Computer Setup is a preinstalled, ROM-based utility that can be used with Computer Setup only...
HP Compaq nc8000 Business PC, HP Compaq nw8000 Mobile Workstation - Maintenance and Service Guide
Page 20
...Integrated 10/100/1000 BASE-T Ethernet local area network (LAN) NIC with RJ-45 connector ■ Integrated wireless support for Bluetooth® LAN and Mini PCI 802.11a/b/g LAN devices ■ Support for fixed optical drive and MultiBay device ■ Support for two Type II/Type III PC Card slots (one integrated...) with support for both 32-bit (CardBus) and 16-bit PC Cards ■ External 65-W AC adapter with power...
...Integrated 10/100/1000 BASE-T Ethernet local area network (LAN) NIC with RJ-45 connector ■ Integrated wireless support for Bluetooth® LAN and Mini PCI 802.11a/b/g LAN devices ■ Support for fixed optical drive and MultiBay device ■ Support for two Type II/Type III PC Card slots (one integrated...) with support for both 32-bit (CardBus) and 16-bit PC Cards ■ External 65-W AC adapter with power...