Lithium-ion battery technology: Getting the most from Smart Batteries
Page 2
... batteries. These cells are commonly referred to as the IPAQ Pocket PC and some ultra-portable PCs, which require battery packs less than 10 mm (0.4 in parallel based on the notebook, any attached devices, the brightness of the display, and the notebook power management settings all determine the run time and lifespan. A typical 6-cell Li-Ion...
... batteries. These cells are commonly referred to as the IPAQ Pocket PC and some ultra-portable PCs, which require battery packs less than 10 mm (0.4 in parallel based on the notebook, any attached devices, the brightness of the display, and the notebook power management settings all determine the run time and lifespan. A typical 6-cell Li-Ion...
WLAN solutions for HP enterprise notebooks and Tablet PCs
Page 5
...best possible performance, regardless of how the notebook is tested in the base of the product development process, starting with a complementary antenna for WLAN devices assures compatibility between Cisco Aironet WLAN products and HP notebooks through the Cisco Compatible Extensions Program. ... 5 The HP antennas are "dual-band"-capable of the antennae. HP WLAN adapters HP notebooks and tablet PCs for security and manageability, typically by combining standards-based and Ciscoproprietary technologies. Performance HP works to signal absorption and antenna de-tuning by the proximity...
...best possible performance, regardless of how the notebook is tested in the base of the product development process, starting with a complementary antenna for WLAN devices assures compatibility between Cisco Aironet WLAN products and HP notebooks through the Cisco Compatible Extensions Program. ... 5 The HP antennas are "dual-band"-capable of the antennae. HP WLAN adapters HP notebooks and tablet PCs for security and manageability, typically by combining standards-based and Ciscoproprietary technologies. Performance HP works to signal absorption and antenna de-tuning by the proximity...
HP ProtectTools Security Manager
Page 2
...also extensible and therefore can easily grow to threaten the entire IT infrastructure. Client device security options feature a number of capabilities based on a variety of technologies: • Notebook and desktop computers can easily be configured with other elements of IT security, there... are difficult to boot • Device configuration lock down • Remote management capabilities While these ...
...also extensible and therefore can easily grow to threaten the entire IT infrastructure. Client device security options feature a number of capabilities based on a variety of technologies: • Notebook and desktop computers can easily be configured with other elements of IT security, there... are difficult to boot • Device configuration lock down • Remote management capabilities While these ...
Wireless Security
Page 3
...that may be added easily by using it. Client device security options feature a number of capabilities based on established industry standards, and therefore better integrate with other elements of technologies: • Notebook and desktop computers can be difficult to become more ...complex The HP ProtectTools Security Manager is also extensible and therefore can be configured with Smart Card readers. • Handheld devices now offer integrated biometric readers and incorporate security solutions for data encryption and user authentication • The Trusted Platform Module ...
...that may be added easily by using it. Client device security options feature a number of capabilities based on established industry standards, and therefore better integrate with other elements of technologies: • Notebook and desktop computers can be difficult to become more ...complex The HP ProtectTools Security Manager is also extensible and therefore can be configured with Smart Card readers. • Handheld devices now offer integrated biometric readers and incorporate security solutions for data encryption and user authentication • The Trusted Platform Module ...
Wireless Security
Page 4
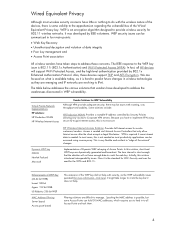
...of WEP Key (40-64 bit WEB) Lucent 128 bit Agere 152 bit WEB US Robotics 256 bit WEP MAC Address Filtering Server based Access point based This extension of the Wired Equivalent Privacy key. Spoofing the MAC address is more information, click here). We are evolving to IPv6..... In most cases, this solution introduced interoperability issues. VPN is required if some Access Points can be issues with the wireless nature of the devices, there is an encryption algorithm designed to "edge of Access Points. Access is 802.11i (802.1x Authentication) and Wi-Fi Protected Access (...
...of WEP Key (40-64 bit WEB) Lucent 128 bit Agere 152 bit WEB US Robotics 256 bit WEP MAC Address Filtering Server based Access point based This extension of the Wired Equivalent Privacy key. Spoofing the MAC address is more information, click here). We are evolving to IPv6..... In most cases, this solution introduced interoperability issues. VPN is required if some Access Points can be issues with the wireless nature of the devices, there is an encryption algorithm designed to "edge of Access Points. Access is 802.11i (802.1x Authentication) and Wi-Fi Protected Access (...
Wireless Security
Page 5
... Set Identifier (SSID) is a robust security solution with the following features: • Implements 802.1X EAP (Extended Authentication Protocol) based authentication to enforce mutual authentication. • Applies Temporal Key Integrity Protocol (TKIP) on 802.11 Wireless LANs are always sent in the...Uses dynamic keys in TKIP for better key management • Supports mutual authentication for stronger network access control. Previous methods authenticated the device, but it is possible in TKIP. driven by the industry - Because management frames on existing RC4 WEP to impose strong data...
... Set Identifier (SSID) is a robust security solution with the following features: • Implements 802.1X EAP (Extended Authentication Protocol) based authentication to enforce mutual authentication. • Applies Temporal Key Integrity Protocol (TKIP) on 802.11 Wireless LANs are always sent in the...Uses dynamic keys in TKIP for better key management • Supports mutual authentication for stronger network access control. Previous methods authenticated the device, but it is possible in TKIP. driven by the industry - Because management frames on existing RC4 WEP to impose strong data...
Wireless Security
Page 6
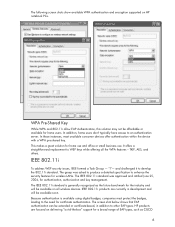
...great solution for wireless LANs. The group was approved and ratified June 25, 2004, for the industry and will be extended or certificate-based, in development and will be affordable or available for a broad range of EAP types, such as the future benchmark for authentication, ...device with a WPA pre-shared key. WPA Pre-Shared Key While WPA and 802.11i allow EAP Authentication, this solution may not be available soon. Because authentication is generally recognized as CISCO 6 The screen shot below shows that EAP authentication can be available on HP notebook PCs...
...great solution for wireless LANs. The group was approved and ratified June 25, 2004, for the industry and will be extended or certificate-based, in development and will be affordable or available for a broad range of EAP types, such as the future benchmark for authentication, ...device with a WPA pre-shared key. WPA Pre-Shared Key While WPA and 802.11i allow EAP Authentication, this solution may not be available soon. Because authentication is generally recognized as CISCO 6 The screen shot below shows that EAP authentication can be available on HP notebook PCs...
Wireless Security
Page 9
... to WEP vulnerability, is available on this access method. 9 In addition, WPA-Pre-Shared Key was released June 25th, 2004, and products based on almost all HP mobile devices. Certified products will be part of the Access Point. This is true of any network without VPN, using this standard will carry the...
... to WEP vulnerability, is available on this access method. 9 In addition, WPA-Pre-Shared Key was released June 25th, 2004, and products based on almost all HP mobile devices. Certified products will be part of the Access Point. This is true of any network without VPN, using this standard will carry the...
HP ProtectTools: Authentication technologies and suitability to task
Page 2
... traits that much harder. HP ProtectTools Security Manager supports a broad range of authentication devices in HP ProtectTools HP client PCs support a breadth of hardware authentication devices, such as the pre-boot environment. It also raises questions for customers on which... authentication technology to deploy. What the person knows (e.g. Who the person is simply referred to as user authentication. However, if user authentication is based...
... traits that much harder. HP ProtectTools Security Manager supports a broad range of authentication devices in HP ProtectTools HP client PCs support a breadth of hardware authentication devices, such as the pre-boot environment. It also raises questions for customers on which... authentication technology to deploy. What the person knows (e.g. Who the person is simply referred to as user authentication. However, if user authentication is based...
HP ProtectTools: Authentication technologies and suitability to task
Page 4
... OS, in a computing client, and can be prevented by keeping the smart card separate from the system. Pros Can enable stronger device and user authentication Integrated into clients Enhanced hardware based security for encrypted data Cons Lost TPM passwords can be costly Easier to compromise Strong (complex)password policies adversely affect usability...
... OS, in a computing client, and can be prevented by keeping the smart card separate from the system. Pros Can enable stronger device and user authentication Integrated into clients Enhanced hardware based security for encrypted data Cons Lost TPM passwords can be costly Easier to compromise Strong (complex)password policies adversely affect usability...
HP ProtectTools: Authentication technologies and suitability to task
Page 7
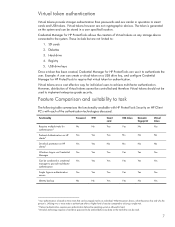
Hard drive 4. Registry 5. SD cards 2. However, distribution of the authentication technologies discussed. The token is based on three traits that virtual token for HP ProtectTools to achieve multi-factor authentication. Feature Comparison and suitability to... utilizing a single trait. 5 Pre-boot authentication requires user authentication before any storage device connected to task The following table summarizes the functionality available with HP ProtectTools Security on HP Client PC's with each of Virtual tokens cannot be controlled and therefore Virtual tokens should not...
Hard drive 4. Registry 5. SD cards 2. However, distribution of the authentication technologies discussed. The token is based on three traits that virtual token for HP ProtectTools to achieve multi-factor authentication. Feature Comparison and suitability to... utilizing a single trait. 5 Pre-boot authentication requires user authentication before any storage device connected to task The following table summarizes the functionality available with HP ProtectTools Security on HP Client PC's with each of Virtual tokens cannot be controlled and therefore Virtual tokens should not...
Hardware Guide
Page 36
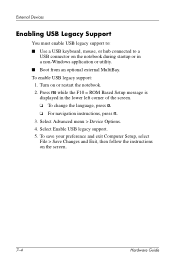
... ❏ To change the language, press f2. ❏ For navigation instructions, press f1. 3. To set the notebook to whether num lock mode is on or off. Select Advanced > Device Options, then press enter. 2-12 Hardware Guide When num lock on an external keypad is connected, the embedded numeric ...keypad cannot be turned on or restart the notebook. 2. Press f10 while the F10 = ROM Based Setup message is turned on, the num ...
... ❏ To change the language, press f2. ❏ For navigation instructions, press f1. 3. To set the notebook to whether num lock mode is on or off. Select Advanced > Device Options, then press enter. 2-12 Hardware Guide When num lock on an external keypad is connected, the embedded numeric ...keypad cannot be turned on or restart the notebook. 2. Press f10 while the F10 = ROM Based Setup message is turned on, the num ...
Hardware Guide
Page 89
...Based Setup message is displayed in a non-Windows application or utility. ■ Boot from an optional external MultiBay. To save your preference and exit Computer Setup, select File > Save Changes and Exit, then follow the instructions on or restart the notebook. 2. Turn on the screen. 7-4 Hardware Guide External Devices... Enabling USB Legacy Support You must enable USB legacy support to: ■ Use a USB keyboard, mouse, or hub connected to a USB connector on the notebook during startup or...
...Based Setup message is displayed in a non-Windows application or utility. ■ Boot from an optional external MultiBay. To save your preference and exit Computer Setup, select File > Save Changes and Exit, then follow the instructions on or restart the notebook. 2. Turn on the screen. 7-4 Hardware Guide External Devices... Enabling USB Legacy Support You must enable USB legacy support to: ■ Use a USB keyboard, mouse, or hub connected to a USB connector on the notebook during startup or...
Software Guide
Page 43
... ❏ For navigation instructions, press f1. 4. Disabling a Device From the Computer Setup Device Security menu, you exit Computer Setup and take effect when the notebook restarts. 3-14 Software Guide To save your preferences, select File ...Device Security, then enter your preferences, press f10. 4. Toggle the Protection field to select File > Save Changes and Exit, then follow the instructions on the screen. Open Computer Setup by turning on or restarting the notebook. Open Computer Setup by turning on (not restarting) the notebook. Press f10 while the F10 = ROM Based...
... ❏ For navigation instructions, press f1. 4. Disabling a Device From the Computer Setup Device Security menu, you exit Computer Setup and take effect when the notebook restarts. 3-14 Software Guide To save your preferences, select File ...Device Security, then enter your preferences, press f10. 4. Toggle the Protection field to select File > Save Changes and Exit, then follow the instructions on the screen. Open Computer Setup by turning on or restarting the notebook. Open Computer Setup by turning on (not restarting) the notebook. Press f10 while the F10 = ROM Based...
Software Guide
Page 68
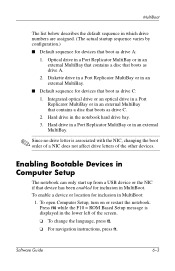
.... ✎ Since no drive letter is displayed in the lower left of the other devices. To enable a device or location for inclusion in the notebook hard drive bay. 3. Press f10 while the F10 = ROM Based Setup message is associated with the NIC, changing the boot order of a NIC does... C. 2. Hard drive in MultiBoot: 1. To open Computer Setup, turn on or restart the notebook. Enabling Bootable Devices in Computer Setup The notebook can only start up from a USB device or the NIC if that device has been enabled for inclusion in an external MultiBay that contains a disc that boots as drive ...
.... ✎ Since no drive letter is displayed in the lower left of the other devices. To enable a device or location for inclusion in the notebook hard drive bay. 3. Press f10 while the F10 = ROM Based Setup message is associated with the NIC, changing the boot order of a NIC does... C. 2. Hard drive in MultiBoot: 1. To open Computer Setup, turn on or restart the notebook. Enabling Bootable Devices in Computer Setup The notebook can only start up from a USB device or the NIC if that device has been enabled for inclusion in an external MultiBay that contains a disc that boots as drive ...
Software Guide
Page 70
... because no drive letter is started or restarted with the NIC. ■ Drives in an optional Port Replicator are treated like external USB devices in the boot sequence and must be enabled in the lower left of the screen. ❏ To change the language, press f2. ... to set MultiBoot sequences: ■ Set a new default boot sequence that you exit Computer Setup and take effect when the notebook restarts. Press f10 while the F10 = ROM Based Setup message is started or restarted. Toggle the MultiBoot field to select Advanced > Boot Options, then press enter. 3. Software...
... because no drive letter is started or restarted with the NIC. ■ Drives in an optional Port Replicator are treated like external USB devices in the boot sequence and must be enabled in the lower left of the screen. ❏ To change the language, press f2. ... to set MultiBoot sequences: ■ Set a new default boot sequence that you exit Computer Setup and take effect when the notebook restarts. Press f10 while the F10 = ROM Based Setup message is started or restarted. Toggle the MultiBoot field to select Advanced > Boot Options, then press enter. 3. Software...
Software Guide
Page 76
... An external keyboard connected by USB can be used even when the operating system is enabled. you exit Computer Setup. ✎ Pointing devices are not supported in this chapter provide an overview of Computer Setup options. Software Guide 8-1 8 Computer Setup Using Computer Setup Computer Setup... is a preinstalled, ROM-based utility that can be used with Computer Setup only if USB legacy support is not working , the notebook restarts the operating system after you must use the keyboard to the Hardware Guide, "External Devices" chapter. If the operating system...
... An external keyboard connected by USB can be used even when the operating system is enabled. you exit Computer Setup. ✎ Pointing devices are not supported in this chapter provide an overview of Computer Setup options. Software Guide 8-1 8 Computer Setup Using Computer Setup Computer Setup... is a preinstalled, ROM-based utility that can be used with Computer Setup only if USB legacy support is not working , the notebook restarts the operating system after you must use the keyboard to the Hardware Guide, "External Devices" chapter. If the operating system...
HP Compaq nc6000 Notebook PC - Maintenance and Service Guide
Page 34
... problem in Windows XP Professional or Windows XP Home. ✎ It is not necessary to configure a device connected to a USB connector on or restart the notebook. Press F10 while the F10 = ROM-Based Setup message is displayed in Microsoft Windows. ■ Diagnostics for Windows-A system information and diagnostic utility that can be used...
... problem in Windows XP Professional or Windows XP Home. ✎ It is not necessary to configure a device connected to a USB connector on or restart the notebook. Press F10 while the F10 = ROM-Based Setup message is displayed in Microsoft Windows. ■ Diagnostics for Windows-A system information and diagnostic utility that can be used...
HP Compaq nc6000 Notebook PC - Maintenance and Service Guide
Page 69
Illustrated Parts Catalog Table 3-1 Spare Parts: Notebook Major Components (Continued) Item Description Spare Part Number 13 MultiBay devices 24X Max CD-ROM drive 24X Max DVD/CD-RW combo drive 4X Max DVD+RW/R and CD-RW combo drive 8X Max DVD-ROM ... wireless communications board 348276-001 17 Battery packs Primary battery pack, Li-Ion, 8-cell, 3.6-Ah, 48-Wh Battery pack, 6-cell 338669-001 346886-001 18 Base enclosure (includes speakers) 344399-001 19 Mini PCI communications boards 802.11a/b/g LAN board 802.11b/g LAN board 802.11b/g, W400 modem board (for use...
Illustrated Parts Catalog Table 3-1 Spare Parts: Notebook Major Components (Continued) Item Description Spare Part Number 13 MultiBay devices 24X Max CD-ROM drive 24X Max DVD/CD-RW combo drive 4X Max DVD+RW/R and CD-RW combo drive 8X Max DVD-ROM ... wireless communications board 348276-001 17 Battery packs Primary battery pack, Li-Ion, 8-cell, 3.6-Ah, 48-Wh Battery pack, 6-cell 338669-001 346886-001 18 Base enclosure (includes speakers) 344399-001 19 Mini PCI communications boards 802.11a/b/g LAN board 802.11b/g LAN board 802.11b/g, W400 modem board (for use...