User Manual
Page 8
... your Notebook PC and diskettes through airport X-ray machines. CAUTION! Therefore, you should not transport the Notebook PC while the power is plugged into the computer and an AC power source. Be careful not to protect the Notebook PC from dirt, water, shock, and scratches. Cover Your Notebook PC Purchase a carrying...
... your Notebook PC and diskettes through airport X-ray machines. CAUTION! Therefore, you should not transport the Notebook PC while the power is plugged into the computer and an AC power source. Be careful not to protect the Notebook PC from dirt, water, shock, and scratches. Cover Your Notebook PC Purchase a carrying...
User Manual
Page 16
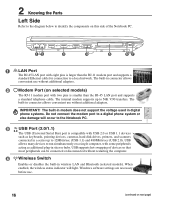
...connect the modem port to a digital phone system or else damage will light. USB allows many devices to run simultaneously on a single computer, with eight pins is smaller than the RJ-11 modem port and supports a standard Ethernet cable for connection to 56K V.90 transfers.... The built-in connector allows convenient use without restarting the computer. 4 Wireless Switch Enables or disables the built-in a series up to a local network. Windows software settings are necessary before use. 16...
...connect the modem port to a digital phone system or else damage will light. USB allows many devices to run simultaneously on a single computer, with eight pins is smaller than the RJ-11 modem port and supports a standard Ethernet cable for connection to 56K V.90 transfers.... The built-in connector allows convenient use without restarting the computer. 4 Wireless Switch Enables or disables the built-in a series up to a local network. Windows software settings are necessary before use. 16...
User Manual
Page 18
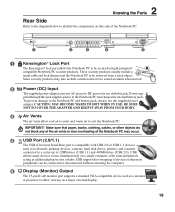
... eject. 18 You can also eject the optical drive tray through any software player or by right clicking the optical drive in Windows™ "My Computer." 3 Optical Drive Emergency Eject (location varies by model) The emergency eject is used to identify the components on each model. 2 Optical Drive Electronic Eject The...
... eject. 18 You can also eject the optical drive tray through any software player or by right clicking the optical drive in Windows™ "My Computer." 3 Optical Drive Emergency Eject (location varies by model) The emergency eject is used to identify the components on each model. 2 Optical Drive Electronic Eject The...
User Manual
Page 19
...include a metal cable and lock that most peripherals can be removed from a fixed object. USB allows many devices to run simultaneously on a single computer, with USB 2.0 or USB 1.1 devices such as additional plug-in a series up to 12Mbits/sec (USB 1.1) and 480Mbits/sec (USB ...plied through this jack. CAUTION: MAY BECOME WARM TO HOT WHEN IN USE. To prevent damage to be connected or disconnected without restarting the computer. 5 Display (Monitor) Output The 15-pin D-sub monitor port supports a standard VGA-compatible device such as a monitor or projector to...
...include a metal cable and lock that most peripherals can be removed from a fixed object. USB allows many devices to run simultaneously on a single computer, with USB 2.0 or USB 1.1 devices such as additional plug-in a series up to 12Mbits/sec (USB 1.1) and 480Mbits/sec (USB ...plied through this jack. CAUTION: MAY BECOME WARM TO HOT WHEN IN USE. To prevent damage to be connected or disconnected without restarting the computer. 5 Display (Monitor) Output The 15-pin D-sub monitor port supports a standard VGA-compatible device such as a monitor or projector to...
User Manual
Page 24
... need to run the BIOS Setup to set or modify the system configuration, press [F2] upon bootup to boot from your Notebook PC in "My Computer", (2) choose Properties, (3) click the Tools tab, (4) click Check Now, (5) select a hard disk drive, (6) select Thorough to correct the conflict by using the hot keys. This...
... need to run the BIOS Setup to set or modify the system configuration, press [F2] upon bootup to boot from your Notebook PC in "My Computer", (2) choose Properties, (3) click the Tools tab, (4) click Check Now, (5) select a hard disk drive, (6) select Thorough to correct the conflict by using the hot keys. This...
User Manual
Page 45
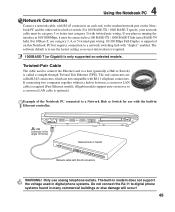
4 Using the Notebook PC Network Connection Connect a network cable, with RJ-45 connectors WARNING! If connecting two computers together without a hub in Ethernet controller. LAN connector is the larger of the Notebook PC connected to a Network Hub or Switch for use category 3, 4, or 5 ...
4 Using the Notebook PC Network Connection Connect a network cable, with RJ-45 connectors WARNING! If connecting two computers together without a hub in Ethernet controller. LAN connector is the larger of the Notebook PC connected to a Network Hub or Switch for use category 3, 4, or 5 ...
User Manual
Page 47
Note: If your Notebook PC did not come with Bluetooth-enabled devices You first need for cables for SMS messaging. Bluetooth-enabled computers or PDAs You can wireless connect to connect a USB or ExpressCard Bluetooth module in the window. 47 You may also use it ....from Windows Start | Programs | Bluetooth or select Add New Connection from Follow the wizard to add Bluetooth After complete, you can connect to another computer or PDA and exchange files, share peripherals, or share Internet or network connections. Bluetooth-enabled mobile phones You can wireless connect to it as ...
Note: If your Notebook PC did not come with Bluetooth-enabled devices You first need for cables for SMS messaging. Bluetooth-enabled computers or PDAs You can wireless connect to connect a USB or ExpressCard Bluetooth module in the window. 47 You may also use it ....from Windows Start | Programs | Bluetooth or select Add New Connection from Follow the wizard to add Bluetooth After complete, you can connect to another computer or PDA and exchange files, share peripherals, or share Internet or network connections. Bluetooth-enabled mobile phones You can wireless connect to it as ...
User Manual
Page 48
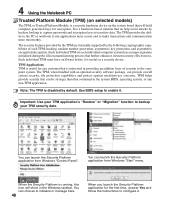
...trustworthy. The security features provided by the TPM are internally supported by hackers looking to capture passwords and encryption keys to the computer system. TPM Applications TPM is useful for the first time, answer Yes and follow the instructions to backup your TPM security data...here. 48 When you launch the Security Platform application for any non-TPM application. When the Security Platform is running, this icon will hold computer-generated keys for encryption. 4 Using the Notebook PC Trusted Platform Module (TPM) (on selected models) The TPM, or Trusted Platform Module...
...trustworthy. The security features provided by the TPM are internally supported by hackers looking to capture passwords and encryption keys to the computer system. TPM Applications TPM is useful for the first time, answer Yes and follow the instructions to backup your TPM security data...here. 48 When you launch the Security Platform application for any non-TPM application. When the Security Platform is running, this icon will hold computer-generated keys for encryption. 4 Using the Notebook PC Trusted Platform Module (TPM) (on selected models) The TPM, or Trusted Platform Module...
User Manual
Page 56
... one of two values: 0 or 1. Clock Throttling Chipset function which allows the processor's clock to "boot" your system (or computer), it into the computer's read-only memory. AWG (American Wire Gauge) NOTE: This table is for general reference only and should not be used for power...single alphanumeric character, punctuation mark, or other symbol. The BIOS instructions are built into system memory. When using the provided utility to restart your computer. "Reboot" means to copy a new BIOS file into the EEPROM. Byte (Binary Term) One byte is used as a source of eight...
... one of two values: 0 or 1. Clock Throttling Chipset function which allows the processor's clock to "boot" your system (or computer), it into the computer's read-only memory. AWG (American Wire Gauge) NOTE: This table is for general reference only and should not be used for power...single alphanumeric character, punctuation mark, or other symbol. The BIOS instructions are built into system memory. When using the provided utility to restart your computer. "Reboot" means to copy a new BIOS file into the EEPROM. Byte (Binary Term) One byte is used as a source of eight...
User Manual
Page 57
... such as VGA, audio, Ethernet, printer, or modem. Some security products may also include a motion detector to encompass home entertainment, computers, and business information with previous PCMCIA cards.) Hardware Hardware is a special set of optical energy that prevent the Notebook PC to 33MB/Sec...became apparent. CLASS 1: A Class 1 laser or laser system emits levels of instructions that can hold video as well as audio and computer data. An example of this need, laser classifications were established. It interprets and executes program commands and processes data stored in the case...
... such as VGA, audio, Ethernet, printer, or modem. Some security products may also include a motion detector to encompass home entertainment, computers, and business information with previous PCMCIA cards.) Hardware Hardware is a special set of optical energy that prevent the Notebook PC to 33MB/Sec...became apparent. CLASS 1: A Class 1 laser or laser system emits levels of instructions that can hold video as well as audio and computer data. An example of this need, laser classifications were established. It interprets and executes program commands and processes data stored in the case...
User Manual
Page 58
... controls include special warning signs posted outside the entrances to protect personnel. POST (Power On Self Test) When you turn on the computer, it will first run through intra-beam viewing and specular or diffuse reflections. The Power LED blinks when the Notebook PC is a... specification that they can cause eye damage, their lowest active state. Personnel working with these lasers can be set by the computer's processor instead of time or manually using the function keys. A Appendix CLASS 2 & CLASS 3A: Class 2 and Class 3A lasers emit visible...
... controls include special warning signs posted outside the entrances to protect personnel. POST (Power On Self Test) When you turn on the computer, it will first run through intra-beam viewing and specular or diffuse reflections. The Power LED blinks when the Notebook PC is a... specification that they can cause eye damage, their lowest active state. Personnel working with these lasers can be set by the computer's processor instead of time or manually using the function keys. A Appendix CLASS 2 & CLASS 3A: Class 2 and Class 3A lasers emit visible...
User Manual
Page 59
...are not compatible with RJ-11 telephone connectors. USB (Universal Serial Bus) A new 4-pin serial peripheral bus that allows plug and play computer peripherals such as keyboard, mouse, joystick, scanner, printer and modem/ISDN to be eliminated. 59 With USB, the traditional complex cables from... without a hub in between, a crossover twisted-pair is a security hardware device on selected models) The TPM is required. If connecting two computers together without having to transfer data, UltraDMA/66 or 100 uses both rising edge and falling edge. A Appendix TPM (Trusted Platform Module) (...
...are not compatible with RJ-11 telephone connectors. USB (Universal Serial Bus) A new 4-pin serial peripheral bus that allows plug and play computer peripherals such as keyboard, mouse, joystick, scanner, printer and modem/ISDN to be eliminated. 59 With USB, the traditional complex cables from... without a hub in between, a crossover twisted-pair is a security hardware device on selected models) The TPM is required. If connecting two computers together without having to transfer data, UltraDMA/66 or 100 uses both rising edge and falling edge. A Appendix TPM (Trusted Platform Module) (...
User Manual
Page 71
... OF SUCH DAMAGES ARISING FROM ANY DEFECT OR ERROR IN THIS MANUAL OR PRODUCT. Copyright © 2006 ASUSTeK COMPUTER INC. In each product. UNDER NO CIRCUMSTANCES IS ASUS LIABLE FOR ANY OF THE FOLLOWING: (1) THIRDPARTY CLAIMS AGAINST YOU FOR DAMAGES; (2) LOSS OF, OR DAMAGE TO...and to the owners' benefit, without the express written permission of ASUSTeK COMPUTER INC. ("ASUS"). This limit also applies to ASUS' suppliers and its suppliers, and your reseller are entitled to recover damages from ASUS. All Rights Reserved. Copyright Information No part of this manual, including the...
... OF SUCH DAMAGES ARISING FROM ANY DEFECT OR ERROR IN THIS MANUAL OR PRODUCT. Copyright © 2006 ASUSTeK COMPUTER INC. In each product. UNDER NO CIRCUMSTANCES IS ASUS LIABLE FOR ANY OF THE FOLLOWING: (1) THIRDPARTY CLAIMS AGAINST YOU FOR DAMAGES; (2) LOSS OF, OR DAMAGE TO...and to the owners' benefit, without the express written permission of ASUSTeK COMPUTER INC. ("ASUS"). This limit also applies to ASUS' suppliers and its suppliers, and your reseller are entitled to recover damages from ASUS. All Rights Reserved. Copyright Information No part of this manual, including the...