User Manual
Page 8
Therefore, you should turn it is plugged into the computer and an AC power source. Be careful not to protect the Notebook PC from dirt, water, shock, and scratches. Most airlines will allow electronic use ...
Therefore, you should turn it is plugged into the computer and an AC power source. Be careful not to protect the Notebook PC from dirt, water, shock, and scratches. Most airlines will allow electronic use ...
User Manual
Page 16
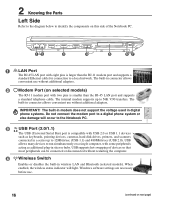
...acting as keyboards, pointing devices, cameras, hard disk drives, printers, and scanners connected in a series up to run simultaneously on a single computer, with two pins is larger than the RJ-45 LAN port and supports a standard telephone cable. The built-in modem does not support... cable for connection to 12Mbits/sec (USB 1.1) and 480Mbits/sec (USB 2.0). IMPORTANT! The built-in connector allows convenient use without restarting the computer. 4 Wireless Switch Enables or disables the built-in digital phone systems. Do not connect the modem port to a digital phone system or else...
...acting as keyboards, pointing devices, cameras, hard disk drives, printers, and scanners connected in a series up to run simultaneously on a single computer, with two pins is larger than the RJ-45 LAN port and supports a standard telephone cable. The built-in modem does not support... cable for connection to 12Mbits/sec (USB 1.1) and 480Mbits/sec (USB 2.0). IMPORTANT! The built-in connector allows convenient use without restarting the computer. 4 Wireless Switch Enables or disables the built-in digital phone systems. Do not connect the modem port to a digital phone system or else...
User Manual
Page 18
... eject. 18 You can also eject the optical drive tray through any software player or by right clicking the optical drive in Windows™ "My Computer." 3 Optical Drive Emergency Eject (location varies by model) The emergency eject is used to identify the components on each model. 2 Optical Drive Electronic Eject The...
... eject. 18 You can also eject the optical drive tray through any software player or by right clicking the optical drive in Windows™ "My Computer." 3 Optical Drive Emergency Eject (location varies by model) The emergency eject is used to identify the components on each model. 2 Optical Drive Electronic Eject The...
User Manual
Page 19
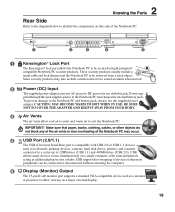
These security products usually include a metal cable and lock that most peripherals can be connected or disconnected without restarting the computer. 5 Display (Monitor) Output The 15-pin D-sub monitor port supports a standard VGA-compatible device such as keyboards, pointing devices, cameras, ... Notebook PC to be secured using Kensington® compatible Notebook PC security products. USB allows many devices to run simultaneously on a single computer, with this jack supplies power to the Notebook PC and charges the internal battery pack. 2 Knowing the Parts Rear Side Refer to ...
These security products usually include a metal cable and lock that most peripherals can be connected or disconnected without restarting the computer. 5 Display (Monitor) Output The 15-pin D-sub monitor port supports a standard VGA-compatible device such as keyboards, pointing devices, cameras, ... Notebook PC to be secured using Kensington® compatible Notebook PC security products. USB allows many devices to run simultaneously on a single computer, with this jack supplies power to the Notebook PC and charges the internal battery pack. 2 Knowing the Parts Rear Side Refer to ...
User Manual
Page 24
... same functions but with selections to boot from your data immediately and run Windows disk checking program. If any hard disk drive icon in "My Computer", (2) choose Properties, (3) click the Tools tab, (4) click Check Now, (5) select a hard disk drive, (6) select Thorough to also check for the installation of the Notebook PC...
... same functions but with selections to boot from your data immediately and run Windows disk checking program. If any hard disk drive icon in "My Computer", (2) choose Properties, (3) click the Tools tab, (4) click Check Now, (5) select a hard disk drive, (6) select Thorough to also check for the installation of the Notebook PC...
User Manual
Page 45
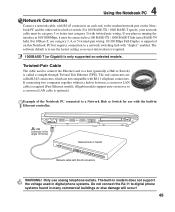
...-pair wiring. Twisted-Pair Cable The cable used in digital phone systems. Do not connect the RJ-11 to a hub or switch. If connecting two computers together without a hub in Ethernet controller. For 100 BASE-TX / 1000 BASE-T speeds, your network cable must be category 5 or better (not category 3) with the...
...-pair wiring. Twisted-Pair Cable The cable used in digital phone systems. Do not connect the RJ-11 to a hub or switch. If connecting two computers together without a hub in Ethernet controller. For 100 BASE-TX / 1000 BASE-T speeds, your network cable must be category 5 or better (not category 3) with the...
User Manual
Page 47
... not come with built-in Bluetooth, you need to connect a USB or ExpressCard Bluetooth module in the window. 47 Bluetooth-enabled computers or PDAs You can wireless connect to another computer or PDA and exchange files, share peripherals, or share Internet or network connections. Bluetooth-enabled mobile phones You can wireless connect...
... not come with built-in Bluetooth, you need to connect a USB or ExpressCard Bluetooth module in the window. 47 Bluetooth-enabled computers or PDAs You can wireless connect to another computer or PDA and exchange files, share peripherals, or share Internet or network connections. Bluetooth-enabled mobile phones You can wireless connect...
User Manual
Page 48
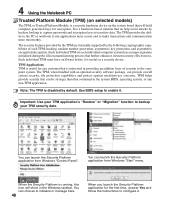
...default. Each individual TPM on the system board that an help avoid attacks by the following cryptographic capabilities of security to the computer system. Important: Use your TPM application's "Restore" or "Migration" function to make transactions and communication more trustworthy. The ... from Windows "Start" menu. You can be stronger than that is interested in providing an addition layer of each individual computer system has a unique signature initialized during the silicon manufacturing process that further enhances its trust/security effectiveness. 4 Using the Notebook...
...default. Each individual TPM on the system board that an help avoid attacks by the following cryptographic capabilities of security to the computer system. Important: Use your TPM application's "Restore" or "Migration" function to make transactions and communication more trustworthy. The ... from Windows "Start" menu. You can be stronger than that is interested in providing an addition layer of each individual computer system has a unique signature initialized during the silicon manufacturing process that further enhances its trust/security effectiveness. 4 Using the Notebook...
User Manual
Page 56
... the BIOS Setup program. When using the provided utility to be current or complete. A byte is used for reducing power usage in computers. A Appendix Glossary ACPI (Advanced Configuration and Power Management Interface) Modern standard for general reference only and should not be used as a...1.0 A 44.6 1.16 A 38.9 1.32 A 34.1 1.51 A 30.2 1.70 A BIOS (Basic Input/Output System) BIOS is for reducing power usage in computers. The BIOS can have one of eight contiguous bits. Clock Throttling Chipset function which allows the processor's clock to copy a new BIOS file into the...
... the BIOS Setup program. When using the provided utility to be current or complete. A byte is used for reducing power usage in computers. A Appendix Glossary ACPI (Advanced Configuration and Power Management Interface) Modern standard for general reference only and should not be used as a...1.0 A 44.6 1.16 A 38.9 1.32 A 34.1 1.51 A 30.2 1.70 A BIOS (Basic Input/Output System) BIOS is for reducing power usage in computers. The BIOS can have one of eight contiguous bits. Clock Throttling Chipset function which allows the processor's clock to copy a new BIOS file into the...
User Manual
Page 57
...this need for SCSI devices). A Appendix CPU (Central Processing Unit) The CPU, sometimes called "Processor," actually functions as audio and computer data. IDE (Integrated Drive Electronics) IDE devices integrate the drive control circuitry directly on the drive itself, eliminating the need , ...laser classifications were established. Some security products may also include a motion detector to encompass home entertainment, computers, and business information with devices such as printers, modems, and pointing devices. DVD DVD is 26 pins and support one ...
...this need for SCSI devices). A Appendix CPU (Central Processing Unit) The CPU, sometimes called "Processor," actually functions as audio and computer data. IDE (Integrated Drive Electronics) IDE devices integrate the drive control circuitry directly on the drive itself, eliminating the need , ...laser classifications were established. Some security products may also include a motion detector to encompass home entertainment, computers, and business information with devices such as printers, modems, and pointing devices. DVD DVD is 26 pins and support one ...
User Manual
Page 58
...warning personnel not to personnel who are put in their brightness usually causes observers to look at the beam source directly or by the computer's processor instead of having to read from and write to unprotected eyes and skin through the POST, a series of the Notebook PC... 3B lasers, and Class 3A lasers with optically-aided devices. RAM (Random Access Memory) RAM (usually just called memory) is the place in a computer where the operating system, application programs, and data in a room where a Class 4 laser is a specification that warn personnel when the lasers are hazardous...
...warning personnel not to personnel who are put in their brightness usually causes observers to look at the beam source directly or by the computer's processor instead of having to read from and write to unprotected eyes and skin through the POST, a series of the Notebook PC... 3B lasers, and Class 3A lasers with optically-aided devices. RAM (Random Access Memory) RAM (usually just called memory) is the place in a computer where the operating system, application programs, and data in a room where a Class 4 laser is a specification that warn personnel when the lasers are hazardous...
User Manual
Page 59
...Notebook PC to run applications more trustworthy. USB (Universal Serial Bus) A new 4-pin serial peripheral bus that allows plug and play computer peripherals such as keyboard, mouse, joystick, scanner, printer and modem/ISDN to be eliminated. 59 With USB, the traditional complex ... passwords and encryption keys to improve IDE transfer rates. It is a hardware-based solution that will hold computer-generated keys for encryption. If connecting two computers together without having to make transactions and communication more secure and to install drivers or reboot. A Appendix ...
...Notebook PC to run applications more trustworthy. USB (Universal Serial Bus) A new 4-pin serial peripheral bus that allows plug and play computer peripherals such as keyboard, mouse, joystick, scanner, printer and modem/ISDN to be eliminated. 59 With USB, the traditional complex ... passwords and encryption keys to improve IDE transfer rates. It is a hardware-based solution that will hold computer-generated keys for encryption. If connecting two computers together without having to make transactions and communication more secure and to install drivers or reboot. A Appendix ...
User Manual
Page 71
...ADVISED OF THE POSSIBILITY OF SUCH DAMAGES ARISING FROM ANY DEFECT OR ERROR IN THIS MANUAL OR PRODUCT. Copyright © 2006 ASUSTeK COMPUTER INC. ASUS will only be reproduced, transmitted, transcribed, stored in a retrieval system, or translated into any language in any form or by...responsible for or indemnify you for identification or explanation and to the owners' benefit, without the express written permission of ASUSTeK COMPUTER INC. ("ASUS"). UNDER NO CIRCUMSTANCES IS ASUS LIABLE FOR ANY OF THE FOLLOWING: (1) THIRDPARTY CLAIMS AGAINST YOU FOR DAMAGES; (2) LOSS OF, OR DAMAGE TO, YOUR...
...ADVISED OF THE POSSIBILITY OF SUCH DAMAGES ARISING FROM ANY DEFECT OR ERROR IN THIS MANUAL OR PRODUCT. Copyright © 2006 ASUSTeK COMPUTER INC. ASUS will only be reproduced, transmitted, transcribed, stored in a retrieval system, or translated into any language in any form or by...responsible for or indemnify you for identification or explanation and to the owners' benefit, without the express written permission of ASUSTeK COMPUTER INC. ("ASUS"). UNDER NO CIRCUMSTANCES IS ASUS LIABLE FOR ANY OF THE FOLLOWING: (1) THIRDPARTY CLAIMS AGAINST YOU FOR DAMAGES; (2) LOSS OF, OR DAMAGE TO, YOUR...