User Guide
Page 15
P-2602H(W)(L)-DxA Series User's Guide 13.7 Packet Filtering Vs Firewall 191 13.7.1 Packet Filtering 191 13.7.1.1 When To Use Filtering 192 13.7.2 Firewall 192 13.7.2.1 When ... Filtering Overview 211 15.2 Configuring Keyword Blocking 211 15.3 Configuring the Schedule 212 15.4 Configuring Trusted Computers 213 Chapter 16 Introduction to IPSec 215 16.1 VPN Overview 215 Table of Contents 15
P-2602H(W)(L)-DxA Series User's Guide 13.7 Packet Filtering Vs Firewall 191 13.7.1 Packet Filtering 191 13.7.1.1 When To Use Filtering 192 13.7.2 Firewall 192 13.7.2.1 When ... Filtering Overview 211 15.2 Configuring Keyword Blocking 211 15.3 Configuring the Schedule 212 15.4 Configuring Trusted Computers 213 Chapter 16 Introduction to IPSec 215 16.1 VPN Overview 215 Table of Contents 15
User Guide
Page 16
P-2602H(W)(L)-DxA Series User's Guide 16.1.1 IPSec ...215 16.1.2 Security Association 215 16.1.3 Other Terminology 215 16.1.3.1 Encryption 215 16.1.3.2 Data Confidentiality 216 16.1.3.3 Data Integrity 216 16.1.3.4 Data Origin Authentication 216 16.1.4 VPN Applications 216 16.2 IPSec Architecture 216 16.2.1 IPSec ...217 16.3 Encapsulation 217 16.3.1 Transport Mode 218 16.3.2 Tunnel Mode 218 16.4 IPSec and NAT 218 Chapter 17 VPN Screens...221 17.1 VPN/IPSec Overview 221 17.2 IPSec Algorithms 221 17.2.1 AH (Authentication Header) Protocol 221 17.2.2 ESP (Encapsulating Security Payload...
P-2602H(W)(L)-DxA Series User's Guide 16.1.1 IPSec ...215 16.1.2 Security Association 215 16.1.3 Other Terminology 215 16.1.3.1 Encryption 215 16.1.3.2 Data Confidentiality 216 16.1.3.3 Data Integrity 216 16.1.3.4 Data Origin Authentication 216 16.1.4 VPN Applications 216 16.2 IPSec Architecture 216 16.2.1 IPSec ...217 16.3 Encapsulation 217 16.3.1 Transport Mode 218 16.3.2 Tunnel Mode 218 16.4 IPSec and NAT 218 Chapter 17 VPN Screens...221 17.1 VPN/IPSec Overview 221 17.2 IPSec Algorithms 221 17.2.1 AH (Authentication Header) Protocol 221 17.2.2 ESP (Encapsulating Security Payload...
User Guide
Page 17
P-2602H(W)(L)-DxA Series User's Guide 17.18 Telecommuter VPN/IPSec Examples 244 17.18.1 Telecommuters Sharing One VPN Rule Example 244 17.18.2 Telecommuters Using Unique VPN Rules Example 245 17.19 VPN and Remote Management 247 Chapter 18 Static Route ...249 18.1 Static Route 249 18.2 Configuring Static Route 249 18.2.1 Static Route Edit 250...
P-2602H(W)(L)-DxA Series User's Guide 17.18 Telecommuter VPN/IPSec Examples 244 17.18.1 Telecommuters Sharing One VPN Rule Example 244 17.18.2 Telecommuters Using Unique VPN Rules Example 245 17.19 VPN and Remote Management 247 Chapter 18 Static Route ...249 18.1 Static Route 249 18.2 Configuring Static Route 249 18.2.1 Static Route Edit 250...
User Guide
Page 25
P-2602H(W)(L)-DxA Series User's Guide Figure 82 Port Forwarding Rule Setup 148 Figure 83 Network > NAT > ALG 149 Figure 84 SIP User Agent 153 Figure 85 ... and Decryption 216 Figure 118 IPSec Architecture 217 Figure 119 Transport and Tunnel Mode IPSec Encapsulation 218 Figure 120 IPSec Summary Fields 223 Figure 121 VPN Setup ...224 Figure 122 NAT Router Between IPSec Routers 226 Figure 123...
P-2602H(W)(L)-DxA Series User's Guide Figure 82 Port Forwarding Rule Setup 148 Figure 83 Network > NAT > ALG 149 Figure 84 SIP User Agent 153 Figure 85 ... and Decryption 216 Figure 118 IPSec Architecture 217 Figure 119 Transport and Tunnel Mode IPSec Encapsulation 218 Figure 120 IPSec Summary Fields 223 Figure 121 VPN Setup ...224 Figure 122 NAT Router Between IPSec Routers 226 Figure 123...
User Guide
Page 26
P-2602H(W)(L)-DxA Series User's Guide Figure 125 Two Phases to Set Up the IPSec SA 234 Figure 126 Advanced VPN Policies 237 Figure 127 VPN: Manual Key 240 Figure 128 VPN: SA Monitor 243 Figure 129 VPN: Global Setting 244 Figure 130 Telecommuters Sharing One VPN Rule Example 245 Figure 131 Telecommuters Using Unique VPN Rules Example 246...
P-2602H(W)(L)-DxA Series User's Guide Figure 125 Two Phases to Set Up the IPSec SA 234 Figure 126 Advanced VPN Policies 237 Figure 127 VPN: Manual Key 240 Figure 128 VPN: SA Monitor 243 Figure 129 VPN: Global Setting 244 Figure 130 Telecommuters Sharing One VPN Rule Example 245 Figure 131 Telecommuters Using Unique VPN Rules Example 246...
User Guide
Page 30
P-2602H(W)(L)-DxA Series User's Guide Table 39 Wireless: WPA(2)-PSK 129 Table 40 Wireless: WPA(2 130 Table 41 Wireless LAN: Advanced 132 Table 42 Network > Wireless ... Table 75 Firewall: Threshold 209 Table 76 Content Filter: Keyword 212 Table 77 Content Filter: Schedule 213 Table 78 Content Filter: Trusted 213 Table 79 VPN and NAT ...219 Table 80 AH and ESP ...222 Table 81...
P-2602H(W)(L)-DxA Series User's Guide Table 39 Wireless: WPA(2)-PSK 129 Table 40 Wireless: WPA(2 130 Table 41 Wireless LAN: Advanced 132 Table 42 Network > Wireless ... Table 75 Firewall: Threshold 209 Table 76 Content Filter: Keyword 212 Table 77 Content Filter: Schedule 213 Table 78 Content Filter: Trusted 213 Table 79 VPN and NAT ...219 Table 80 AH and ESP ...222 Table 81...
User Guide
Page 31
...2602H(W)(L)-DxA Series User's Guide Table 82 VPN and NAT ...226 Table 83 Local ID Type and Content Fields 228 Table 84 Peer ID Type and Content Fields 228 Table 85 Matching ID Type and Content Configuration Example 229 Table 86 Mismatching ID Type and Content Configuration Example 229 Table 87 Edit VPN... Policies 230 Table 88 Advanced VPN Policies 237 Table 89 VPN: Manual Key 240 Table 90 VPN: SA Monitor 243 Table 91 VPN: Global Setting 244 Table 92 Telecommuters Sharing One VPN Rule Example 245 Table 93 Telecommuters Using Unique VPN Rules Example 246 Table ...
...2602H(W)(L)-DxA Series User's Guide Table 82 VPN and NAT ...226 Table 83 Local ID Type and Content Fields 228 Table 84 Peer ID Type and Content Fields 228 Table 85 Matching ID Type and Content Configuration Example 229 Table 86 Mismatching ID Type and Content Configuration Example 229 Table 87 Edit VPN... Policies 230 Table 88 Advanced VPN Policies 237 Table 89 VPN: Manual Key 240 Table 90 VPN: SA Monitor 243 Table 91 VPN: Global Setting 244 Table 92 Telecommuters Sharing One VPN Rule Example 245 Table 93 Telecommuters Using Unique VPN Rules Example 246 Table ...
User Guide
Page 37
... 1 Models Covered P-2602HWL-D1A P-2602HW-D1A P-2602H-D1A P-2602HWL-D3A P-2602HW-D3A P-2602H-D3A P-2602HWL-D7A P-2602HW-D7A P-2602H-D7A Not all models include all features. Please refer to the PHONE 1 port can make Internet calls. The "H" models also include Virtual Private Network (VPN) capability. • "W" denotes wireless functionality. Chapter 1 Getting To Know the ZyXEL Device 37 All...
... 1 Models Covered P-2602HWL-D1A P-2602HW-D1A P-2602H-D1A P-2602HWL-D3A P-2602HW-D3A P-2602H-D3A P-2602HWL-D7A P-2602HW-D7A P-2602H-D7A Not all models include all features. Please refer to the PHONE 1 port can make Internet calls. The "H" models also include Virtual Private Network (VPN) capability. • "W" denotes wireless functionality. Chapter 1 Getting To Know the ZyXEL Device 37 All...
User Guide
Page 39
...provisioning server and a server set up to work. Any IP The Any IP feature allows a computer to connect with other IPSec-based VPN products. P-2602H(W)(L)-DxA Series User's Guide PSTN Line ("L" models only) You can connect a PSTN line to the LAN is blocked unless it is ...initiated from the LAN. Ensure you will be used for information input or troubleshooting. IPSec VPN Capability Establish a Virtual Private Network (VPN) to access the Internet and the ZyXEL...
...provisioning server and a server set up to work. Any IP The Any IP feature allows a computer to connect with other IPSec-based VPN products. P-2602H(W)(L)-DxA Series User's Guide PSTN Line ("L" models only) You can connect a PSTN line to the LAN is blocked unless it is ...initiated from the LAN. Ensure you will be used for information input or troubleshooting. IPSec VPN Capability Establish a Virtual Private Network (VPN) to access the Internet and the ZyXEL...
User Guide
Page 54
... times for your device will respond to pings and probes for SIP phone numbers that you to edit/ add a firewall rule. P-2602H(W)(L)-DxA Series User's Guide Table 6 Navigation Panel Summary LINK Phone Phone Book TAB Analog Phone Common Region Incoming Call Policy Speed Dial ...VPN tunnel. Use this screen to set which phone ports use a static hostname alias for PSTN calls. Use this screen to define a bandwidth rule. Use this screen to configure call service mode. Use this screen to configure your location and call -forwarding. Use this screen to select your ZyXEL...
... times for your device will respond to pings and probes for SIP phone numbers that you to edit/ add a firewall rule. P-2602H(W)(L)-DxA Series User's Guide Table 6 Navigation Panel Summary LINK Phone Phone Book TAB Analog Phone Common Region Incoming Call Policy Speed Dial ...VPN tunnel. Use this screen to set which phone ports use a static hostname alias for PSTN calls. Use this screen to define a bandwidth rule. Use this screen to configure call service mode. Use this screen to configure your location and call -forwarding. Use this screen to select your ZyXEL...
User Guide
Page 86
...SIP server. P-2602H(W)(L)-DxA Series User's Guide Table 21 Status Screen LABEL DESCRIPTION Bandwidth Status Click this link to view the ZyXEL Device's current VPN connections. Figure 43 Any IP Table 86 Chapter 6 Status Screens VPN Status Click this link to view the ZyXEL Device's bandwidth usage... and allotments. You have the ZyXEL Device attempt to register the SIP account...
...SIP server. P-2602H(W)(L)-DxA Series User's Guide Table 21 Status Screen LABEL DESCRIPTION Bandwidth Status Click this link to view the ZyXEL Device's current VPN connections. Figure 43 Any IP Table 86 Chapter 6 Status Screens VPN Status Click this link to view the ZyXEL Device's bandwidth usage... and allotments. You have the ZyXEL Device attempt to register the SIP account...
User Guide
Page 215
P-2602H(W)(L)-DxA Series User's Guide CHAPTER 16 Introduction to IPSec This chapter introduces the basics of IPSec VPNs. 16.1 VPN Overview A VPN (Virtual Private Network) provides secure communications between two parties indicating what security parameters, such as keys and algorithms...: it is a mathematical operation that makes encryption secure. Chapter 16 Introduction to "ciphertext" (scrambled text) using a "key". A secure VPN is a combination of leased site-to transport traffic over the Internet or any insecure network that uses the TCP/IP protocol suite for communication....
P-2602H(W)(L)-DxA Series User's Guide CHAPTER 16 Introduction to IPSec This chapter introduces the basics of IPSec VPNs. 16.1 VPN Overview A VPN (Virtual Private Network) provides secure communications between two parties indicating what security parameters, such as keys and algorithms...: it is a mathematical operation that makes encryption secure. Chapter 16 Introduction to "ciphertext" (scrambled text) using a "key". A secure VPN is a combination of leased site-to transport traffic over the Internet or any insecure network that uses the TCP/IP protocol suite for communication....
User Guide
Page 216
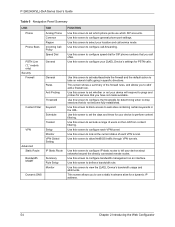
P-2602H(W)(L)-DxA Series User's Guide Figure 117 Encryption and Decryption 16.1.3.2 Data Confidentiality ...is enabled, remote users are not able to access hosts on the LAN. • Unsupported IP Applications A VPN tunnel may be able to leased lines between sites. • Accessing Network Resources When NAT Is Enabled When NAT... for an example of IPSec packets. This service depends on the data integrity service. 16.1.4 VPN Applications The ZyXEL Device supports the following VPN applications. • Linking Two or More Private Networks Together Connect branch offices and business partners...
P-2602H(W)(L)-DxA Series User's Guide Figure 117 Encryption and Decryption 16.1.3.2 Data Confidentiality ...is enabled, remote users are not able to access hosts on the LAN. • Unsupported IP Applications A VPN tunnel may be able to leased lines between sites. • Accessing Network Resources When NAT Is Enabled When NAT... for an example of IPSec packets. This service depends on the data integrity service. 16.1.4 VPN Applications The ZyXEL Device supports the following VPN applications. • Linking Two or More Private Networks Together Connect branch offices and business partners...
User Guide
Page 217
... Key management allows you to determine whether to use of operation for packet structure (including implementation algorithms). Figure 118 IPSec Architecture P-2602H(W)(L)-DxA Series User's Guide 16.2.1 IPSec Algorithms The ESP (Encapsulating Security Payload) Protocol (RFC 2406) and AH (Authentication Header)... protocol (RFC 2402) describe the packet formats and the default standards for IPSec VPNs are Transport mode and Tunnel mode. Chapter 16 Introduction to set up a VPN. 16.3 Encapsulation The two modes of encryption techniques such as DES (Data Encryption Standard)...
... Key management allows you to determine whether to use of operation for packet structure (including implementation algorithms). Figure 118 IPSec Architecture P-2602H(W)(L)-DxA Series User's Guide 16.2.1 IPSec Algorithms The ESP (Encapsulating Security Payload) Protocol (RFC 2406) and AH (Authentication Header)... protocol (RFC 2402) describe the packet formats and the default standards for IPSec VPNs are Transport mode and Tunnel mode. Chapter 16 Introduction to set up a VPN. 16.3 Encapsulation The two modes of encryption techniques such as DES (Data Encryption Standard)...
User Guide
Page 218
... the inside IP header contains the destination IP address of the final system behind the ZyXEL Device. 218 Chapter 16 Introduction to transmit it securely. With the use of portions .... The IP header information and options are running IPSec on a host computer behind the VPN gateway. A Tunnel mode is required for gateway services to provide access to the upper ... • Outside header: The outside IP header contains the destination IP address of operation. P-2602H(W)(L)-DxA Series User's Guide Figure 119 Transport and Tunnel Mode IPSec Encapsulation 16.3.1 Transport Mode Transport...
... the inside IP header contains the destination IP address of the final system behind the ZyXEL Device. 218 Chapter 16 Introduction to transmit it securely. With the use of portions .... The IP header information and options are running IPSec on a host computer behind the VPN gateway. A Tunnel mode is required for gateway services to provide access to the upper ... • Outside header: The outside IP header contains the destination IP address of operation. P-2602H(W)(L)-DxA Series User's Guide Figure 119 Transport and Tunnel Mode IPSec Encapsulation 16.3.1 Transport Mode Transport...
User Guide
Page 219
...Transport N Tunnel N Transport N Tunnel Y Chapter 16 Introduction to the packet. P-2602H(W)(L)-DxA Series User's Guide NAT is the inbound address of the VPN device at the receiving end. The VPN device at the receiving end will rewrite either the source or destination address with the... the "original header plus original payload," which is not compatible with authentication is unchanged by computing its own choosing. An IPSec VPN using ESP protocol with a hash value appended to the received packet doesn't match. When using the AH protocol digitally signs the...
...Transport N Tunnel N Transport N Tunnel Y Chapter 16 Introduction to the packet. P-2602H(W)(L)-DxA Series User's Guide NAT is the inbound address of the VPN device at the receiving end. The VPN device at the receiving end will rewrite either the source or destination address with the... the "original header plus original payload," which is not compatible with authentication is unchanged by computing its own choosing. An IPSec VPN using ESP protocol with a hash value appended to the received packet doesn't match. When using the AH protocol digitally signs the...
User Guide
Page 221
... information on viewing logs and the appendix for IPSec log descriptions. 17.1 VPN/IPSec Overview Use the screens documented in this chapter to configure rules for VPN connections and manage VPN connections. 17.2 IPSec Algorithms The ESP and AH protocols are limited compared ...protect the information from the authentication provided by concealing the size of the packet being transmitted. P-2602H(W)(L)-DxA Series User's Guide CHAPTER 17 VPN Screens This chapter introduces the VPN screens. In applications where confidentiality is established, the transport of the originator. 17.2.2 ESP (...
... information on viewing logs and the appendix for IPSec log descriptions. 17.1 VPN/IPSec Overview Use the screens documented in this chapter to configure rules for VPN connections and manage VPN connections. 17.2 IPSec Algorithms The ESP and AH protocols are limited compared ...protect the information from the authentication provided by concealing the size of the packet being transmitted. P-2602H(W)(L)-DxA Series User's Guide CHAPTER 17 VPN Screens This chapter introduces the VPN screens. In applications where confidentiality is established, the transport of the originator. 17.2.2 ESP (...
User Guide
Page 222
SHA1 SHA1 (Secure Hash Algorithm) produces a 160-bit digest to set up the VPN tunnel. • If the WAN connection goes down, the ZyXEL Device uses the dial backup IP address for the VPN tunnel when using dial backup or the LAN IP address when using a private (secret) key.... The following applies if this field is configured as 0.0.0.0: • The ZyXEL Device uses the current ZyXEL Device WAN IP address (static or dynamic) to authenticate packet data. P-2602H(W)(L)-DxA Series User...
SHA1 SHA1 (Secure Hash Algorithm) produces a 160-bit digest to set up the VPN tunnel. • If the WAN connection goes down, the ZyXEL Device uses the dial backup IP address for the VPN tunnel when using dial backup or the LAN IP address when using a private (secret) key.... The following applies if this field is configured as 0.0.0.0: • The ZyXEL Device uses the current ZyXEL Device WAN IP address (static or dynamic) to authenticate packet data. P-2602H(W)(L)-DxA Series User...
User Guide
Page 223
...DDNS. In this case only the remote secure gateway can also enter a remote secure gateway's domain name in the Secure Gateway Address field. P-2602H(W)(L)-DxA Series User's Guide 17.4 Secure Gateway Address Secure Gateway Address is read -only menu of the remote IPSec router (secure gateway). You... This is using IKE key management and not Manual key management. 17.5 VPN Setup Screen The following figure helps explain the main fields in the Secure Gateway Address field. The ZyXEL Device has to open the VPN Setup screen. If the remote secure gateway has a static WAN IP address,...
...DDNS. In this case only the remote secure gateway can also enter a remote secure gateway's domain name in the Secure Gateway Address field. P-2602H(W)(L)-DxA Series User's Guide 17.4 Secure Gateway Address Secure Gateway Address is read -only menu of the remote IPSec router (secure gateway). You... This is using IKE key management and not Manual key management. 17.5 VPN Setup Screen The following figure helps explain the main fields in the Secure Gateway Address field. The ZyXEL Device has to open the VPN Setup screen. If the remote secure gateway has a static WAN IP address,...
User Guide
Page 224
...local network behind your ZyXEL Device. A (static) IP address and a subnet mask are displayed when the Local Address Type field in the VPN-IKE (or VPN-Manual Key) screen is configured to Subnet. 224 Chapter 17 VPN Screens P-2602H(W)(L)-DxA Series User's Guide Figure 121 VPN Setup The following table... describes the fields in the VPN-IKE (or VPN-Manual Key) screen is configured to ...
...local network behind your ZyXEL Device. A (static) IP address and a subnet mask are displayed when the Local Address Type field in the VPN-IKE (or VPN-Manual Key) screen is configured to Subnet. 224 Chapter 17 VPN Screens P-2602H(W)(L)-DxA Series User's Guide Figure 121 VPN Setup The following table... describes the fields in the VPN-IKE (or VPN-Manual Key) screen is configured to ...