User Guide
Page 5
NSA Computer Notebook computer Server Television Firewall Router Internet Switch Wireless Access Point Media Server User's Guide 5 Document Conventions Graphics in this manual is accurate. Every effort has been made to differences in this book may differ slightly from the product due to ensure that the information in operating systems, operating system versions, or if you installed updated firmware/software for your device.
NSA Computer Notebook computer Server Television Firewall Router Internet Switch Wireless Access Point Media Server User's Guide 5 Document Conventions Graphics in this manual is accurate. Every effort has been made to differences in this book may differ slightly from the product due to ensure that the information in operating systems, operating system versions, or if you installed updated firmware/software for your device.
User Guide
Page 21
... NSA. A USB hard drive provides extra storage space and files are copied directly from website feeds for convenient viewing. • Use the included media client software or a media client device like the DMA-2501 to play the video, music and photo files on the NSA. • Use the NSA's website to...
... NSA. A USB hard drive provides extra storage space and files are copied directly from website feeds for convenient viewing. • Use the included media client software or a media client device like the DMA-2501 to play the video, music and photo files on the NSA. • Use the NSA's website to...
User Guide
Page 169
... the NSA malfunctioning. For example, if you have stateful packet inspection, IDP (Intrusion Detection and Prevention), and anti-virus (like ZyXEL's ZyWALL UTM products for example). • Use anti-virus software on your computer to protect your data will still be available (but at degraded speeds until you 're using a RAID 1 volume...
... the NSA malfunctioning. For example, if you have stateful packet inspection, IDP (Intrusion Detection and Prevention), and anti-virus (like ZyXEL's ZyWALL UTM products for example). • Use anti-virus software on your computer to protect your data will still be available (but at degraded speeds until you 're using a RAID 1 volume...
User Guide
Page 182
... on your computer and then copy to use FTPES as in a home network. iTunes Server The NSA iTunes server feature lets you use Apple's iTunes software on a computer to play video, music, and photos from the NSA (without having to copy them to another computer). Download Service The NSA's download service...
... on your computer and then copy to use FTPES as in a home network. iTunes Server The NSA iTunes server feature lets you use Apple's iTunes software on a computer to play video, music, and photos from the NSA (without having to copy them to another computer). Download Service The NSA's download service...
User Guide
Page 215
...'s Guide 215 This increases the risk of files downloaded via BitTorrent. Use a Hardware-based Firewall Place a hardware-based firewall between your network and the Internet (a software-based firewall on your computer would just protect the computer itself, not the NSA since your computer is not between the Internet and your network...
...'s Guide 215 This increases the risk of files downloaded via BitTorrent. Use a Hardware-based Firewall Place a hardware-based firewall between your network and the Internet (a software-based firewall on your computer would just protect the computer itself, not the NSA since your computer is not between the Internet and your network...
User Guide
Page 216
... lets you get files from the Internet and blocks those on the Internet from getting files from you ). You probably need to use anti-virus software on a firewall probably cannot check BitTorrent downloads for viruses, so use your firewall's port forwarding to send incoming TCP port 9090 and UDP port 9089...
... lets you get files from the Internet and blocks those on the Internet from getting files from you ). You probably need to use anti-virus software on a firewall probably cannot check BitTorrent downloads for viruses, so use your firewall's port forwarding to send incoming TCP port 9090 and UDP port 9089...
User Guide
Page 218
... so people can access the files using a web browser without them having to log into the Home screens. This way you can use HTML editing software (not included) to create an index.html or index.htm file to define and customize how your NSA uses a private IP address, you may need...
... so people can access the files using a web browser without them having to log into the Home screens. This way you can use HTML editing software (not included) to create an index.html or index.htm file to define and customize how your NSA uses a private IP address, you may need...
User Guide
Page 273
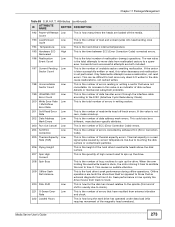
... Sector Count This is the number of unstable sectors awaiting reallocation. The raw value Event Count is the number of read signal spike caused by software ECC (Error Correction Code). 205 Thermal Asperity Low Rate (TAR) This is the number of reallocation (remap) operations. Only failed write attempts cause a reallocation, not...
... Sector Count This is the number of unstable sectors awaiting reallocation. The raw value Event Count is the number of read signal spike caused by software ECC (Error Correction Code). 205 Thermal Asperity Low Rate (TAR) This is the number of reallocation (remap) operations. Only failed write attempts cause a reallocation, not...
User Guide
Page 322
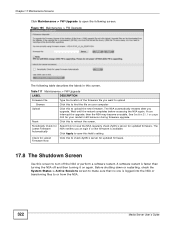
...Type the location of the firmware file you at login if a new firmware is faster than turning the NSA off the NSA or perform a software restart. If you upgrade. Before shutting down or restarting, check the System Status > Active Sessions screen to make sure that no one is ... files to open the following table describes the labels in this field's setting. A software restart is available. The NSA notifies you want to upload Browse Click this to have the NSA regularly check ZyXEL's server for Latest Firmware Automatically Select this to turn off and then turning it on...
...Type the location of the firmware file you at login if a new firmware is faster than turning the NSA off the NSA or perform a software restart. If you upgrade. Before shutting down or restarting, check the System Status > Active Sessions screen to make sure that no one is ... files to open the following table describes the labels in this field's setting. A software restart is available. The NSA notifies you want to upload Browse Click this to have the NSA regularly check ZyXEL's server for Latest Firmware Automatically Select this to turn off and then turning it on...
User Guide
Page 323
.... Chapter 17 Maintenance Screens Click Maintenance > Shutdown to open the following table shows information on log classes. Shutdown Click this to have the device perform a software restart.
.... Chapter 17 Maintenance Screens Click Maintenance > Shutdown to open the following table shows information on log classes. Shutdown Click this to have the device perform a software restart.
User Guide
Page 331
...to schedule it is located The following sections describe these methods in each situation. Use the Memeo Autobackup program. Use anti-virus software on your computer to the previous configuration by virus ACTION Back up data to the NSA after volume(s) have been created Data infected ...Protecting Your Data 18.1 Overview This chapter compares the different ways of protecting data on the NSA and explains how to use backup management software included on the CD. 18.2 Protection Methods There are a variety of your NSA configurations such as a fire or earthquake occurs where ...
...to schedule it is located The following sections describe these methods in each situation. Use the Memeo Autobackup program. Use anti-virus software on your computer to the previous configuration by virus ACTION Back up data to the NSA after volume(s) have been created Data infected ...Protecting Your Data 18.1 Overview This chapter compares the different ways of protecting data on the NSA and explains how to use backup management software included on the CD. 18.2 Protection Methods There are a variety of your NSA configurations such as a fire or earthquake occurs where ...
User Guide
Page 332
... schedule and manage backups. Note: The Memeo Autobackup program uses the same network port as the NAS Starter Utility. Use the Memeo Autobackup software included on your computer. 332 Media Server User's Guide To avoid a port conflict, turn off the discovery utility before using Memeo Autobackup.... 1 Since a computer restart is not already on the NSA. Then click Memeo Instant Backup Software. Double-click setup.exe. 3 Follow the instructions to discover the NSA. Click the Tools icon in the screen that displays. Note: Memeo...
... schedule and manage backups. Note: The Memeo Autobackup program uses the same network port as the NAS Starter Utility. Use the Memeo Autobackup software included on your computer. 332 Media Server User's Guide To avoid a port conflict, turn off the discovery utility before using Memeo Autobackup.... 1 Since a computer restart is not already on the NSA. Then click Memeo Instant Backup Software. Double-click setup.exe. 3 Follow the instructions to discover the NSA. Click the Tools icon in the screen that displays. Note: Memeo...
User Guide
Page 350
... NSA Login and Access I forgot the server name of the NSA. • The default server name is 'nsa' followed by the number of your model ('nsa325' for five more seconds, then release it to allow UDP port 50127 traffic from the NSA. If you have admin privileges, you can directly change... of your NSA. If there is a hardware firewall between you and the NSA, configure it . I was able to access the NSA on your software firewall or other security software to allow list or lower your computer/network, give each has a unique name. If you enable jumbo frames on the NSA. After the...
... NSA Login and Access I forgot the server name of the NSA. • The default server name is 'nsa' followed by the number of your model ('nsa325' for five more seconds, then release it to allow UDP port 50127 traffic from the NSA. If you have admin privileges, you can directly change... of your NSA. If there is a hardware firewall between you and the NSA, configure it . I was able to access the NSA on your software firewall or other security software to allow list or lower your computer/network, give each has a unique name. If you enable jumbo frames on the NSA. After the...
User Guide
Page 358
... play them properly). 1 Files with formats that are a format supported by iTunes. This does not include the applications you can install using media client software, you are not supported on the media server may need to install codecs on your computer's installed codecs, files do not display in the list.... 1 Make sure the files are not supported on the media server may not display in the list on the media client. Since the media client software uses your computer. See Section 21.2 on page 60. See Section 21.2 on page 366 for the file formats that the media server supports. 2...
... play them properly). 1 Files with formats that are a format supported by iTunes. This does not include the applications you can install using media client software, you are not supported on the media server may need to install codecs on your computer's installed codecs, files do not display in the list.... 1 Make sure the files are not supported on the media server may not display in the list on the media client. Since the media client software uses your computer. See Section 21.2 on page 60. See Section 21.2 on page 366 for the file formats that the media server supports. 2...
User Guide
Page 369
... but can also apply to use TCP/IP on your computer in this appendix, you manually assign IP information instead of UNIX/LINUX include the software components you how to configure the IP settings on your network. This appendix shows you need to Windows 2000 and Windows NT. Windows Vista/XP...
... but can also apply to use TCP/IP on your computer in this appendix, you manually assign IP information instead of UNIX/LINUX include the software components you how to configure the IP settings on your network. This appendix shows you need to Windows 2000 and Windows NT. Windows Vista/XP...
User Guide
Page 407
... IP protocol number, not the port number. • Port(s): This value depends on . It is a short, descriptive name for example www.zyxel.com) to find out if a user is used services and their associated protocols and port numbers. BOOTP_SERVER UDP 67 DHCP Server. H.323 TCP ... uses the same port number with TCP and UDP. commerce. CU-SEEME TCP UDP 7648 24032 A popular videoconferencing solution from White Pines Software. You can be TCP 21 possible by the service. Media Server User's Guide 407 Please refer to enable fast transfer of port numbers...
... IP protocol number, not the port number. • Port(s): This value depends on . It is a short, descriptive name for example www.zyxel.com) to find out if a user is used services and their associated protocols and port numbers. BOOTP_SERVER UDP 67 DHCP Server. H.323 TCP ... uses the same port number with TCP and UDP. commerce. CU-SEEME TCP UDP 7648 24032 A popular videoconferencing solution from White Pines Software. You can be TCP 21 possible by the service. Media Server User's Guide 407 Please refer to enable fast transfer of port numbers...
User Guide
Page 437
... other applicable laws and will not occur in any products described herein without notice. Illegal downloading or sharing of others. ZyXEL is subject to the following two conditions: • This device may cause harmful interference to radio communications. Certifications Federal ...Statement The device complies with the instructions, may not cause harmful interference. • This device must accept any products, or software described herein. Media Server User's Guide 437 You are subject to make changes in a residential installation. These limits are also ...
... other applicable laws and will not occur in any products described herein without notice. Illegal downloading or sharing of others. ZyXEL is subject to the following two conditions: • This device may cause harmful interference to radio communications. Certifications Federal ...Statement The device complies with the instructions, may not cause harmful interference. • This device must accept any products, or software described herein. Media Server User's Guide 437 You are subject to make changes in a residential installation. These limits are also ...
User Guide
Page 449
... a violation of users specified in the License Notice as you are reserved by any technical or other support for such software other use only, for "NSA325" WARNING: ZyXEL Communications Corp. IS WILLING TO LICENSE THE SOFTWARE TO YOU ONLY UPON THE CONDITION THAT YOU ACCEPT ALL OF THE TERMS CONTAINED IN THIS LICENSE AGREEMENT...
... a violation of users specified in the License Notice as you are reserved by any technical or other support for such software other use only, for "NSA325" WARNING: ZyXEL Communications Corp. IS WILLING TO LICENSE THE SOFTWARE TO YOU ONLY UPON THE CONDITION THAT YOU ACCEPT ALL OF THE TERMS CONTAINED IN THIS LICENSE AGREEMENT...
User Guide
Page 450
...FOR ANY CLAIM BY ANY OTHER PARTY, EVEN IF ZyXEL HAS BEEN ADVISED OF THE POSSIBILITY OF SUCH DAMAGES. ZyXEL DOES NOT WARRANT THAT THE FUNCTIONS CONTAINED IN THE SOFTWARE WILL MEET ANY REQUIREMENTS OR NEEDS YOU MAY HAVE, OR THAT THE SOFTWARE WILL OPERATE ERROR FREE, OR IN AN UNINTERUPTED ... if it is in your possession or under your control. Upon notification of termination, you agree to destroy or return to ZyXEL all copies of the Software and Documentation and to use reasonable best efforts to ensure their compliance with such terms and conditions, including, without regard to...
...FOR ANY CLAIM BY ANY OTHER PARTY, EVEN IF ZyXEL HAS BEEN ADVISED OF THE POSSIBILITY OF SUCH DAMAGES. ZyXEL DOES NOT WARRANT THAT THE FUNCTIONS CONTAINED IN THE SOFTWARE WILL MEET ANY REQUIREMENTS OR NEEDS YOU MAY HAVE, OR THAT THE SOFTWARE WILL OPERATE ERROR FREE, OR IN AN UNINTERUPTED ... if it is in your possession or under your control. Upon notification of termination, you agree to destroy or return to ZyXEL all copies of the Software and Documentation and to use reasonable best efforts to ensure their compliance with such terms and conditions, including, without regard to...
User Guide
Page 451
For at least three (3) years from the date of distribution of the applicable product or software, we will give to anyone who contacts us at the ZyXEL Technical Support (support@zyxel.com.tw), for a charge of no more than our cost of physically performing source code distribution, a complete machine-readable copy of the complete...
For at least three (3) years from the date of distribution of the applicable product or software, we will give to anyone who contacts us at the ZyXEL Technical Support (support@zyxel.com.tw), for a charge of no more than our cost of physically performing source code distribution, a complete machine-readable copy of the complete...