User Guide
Page 7
Contents Overview Contents Overview User's Guide ...19 Getting to Know Your NSA ...21 zMedia App ...25 NAS Starter Utility ...35 Web Configurator Basics ...43 Tutorials ...63 Technical Reference ...147 Status Screen ...149 System Setting ...153 Storage ...157 Network ...171 Applications ...181 Package Management ...225 Auto Upload ...275 Dropbox ...289 Users ...293 Groups ...299 Shares ...303 Maintenance Screens ...311 Protecting Your Data ...331 Using Time Machine with the NSA 337 Troubleshooting ...347 Product Specifications ...365 Open Source Licences ...447 Media Server User's Guide 7
Contents Overview Contents Overview User's Guide ...19 Getting to Know Your NSA ...21 zMedia App ...25 NAS Starter Utility ...35 Web Configurator Basics ...43 Tutorials ...63 Technical Reference ...147 Status Screen ...149 System Setting ...153 Storage ...157 Network ...171 Applications ...181 Package Management ...225 Auto Upload ...275 Dropbox ...289 Users ...293 Groups ...299 Shares ...303 Maintenance Screens ...311 Protecting Your Data ...331 Using Time Machine with the NSA 337 Troubleshooting ...347 Product Specifications ...365 Open Source Licences ...447 Media Server User's Guide 7
User Guide
Page 16
... Restoration 331 18.4 Memeo Autobackup ...332 18.4.1 Memeo Autobackup Installation and Setup 332 18.4.2 Using Memeo Autobackup After the Initial Setup 334 Chapter 19 Using Time Machine with the NSA 337 19.1 Overview ...337 19.2 Create an Account and a Share on the NSA 337 16 Media Server User's Guide
... Restoration 331 18.4 Memeo Autobackup ...332 18.4.1 Memeo Autobackup Installation and Setup 332 18.4.2 Using Memeo Autobackup After the Initial Setup 334 Chapter 19 Using Time Machine with the NSA 337 19.1 Overview ...337 19.2 Create an Account and a Share on the NSA 337 16 Media Server User's Guide
User Guide
Page 17
....5.1 Finding out Computer Name and MAC Address 341 19.5.2 Creating a Sparse Bundle File 342 19.5.3 Mounting the Sparse Bundle to the NSA 344 19.6 Using Time Machine ...345 Chapter 20 Troubleshooting...347 20.1 Troubleshooting Overview 347 20.2 Power, Hardware, Connections, and LEDs 347 20.3 NAS Starter Utility ...349 20.4 NSA Login and...
....5.1 Finding out Computer Name and MAC Address 341 19.5.2 Creating a Sparse Bundle File 342 19.5.3 Mounting the Sparse Bundle to the NSA 344 19.6 Using Time Machine ...345 Chapter 20 Troubleshooting...347 20.1 Troubleshooting Overview 347 20.2 Power, Hardware, Connections, and LEDs 347 20.3 NAS Starter Utility ...349 20.4 NSA Login and...
User Guide
Page 337
... including pictures, music, videos, documents, applications, and settings. It automatically backs up Time Machine on your Mac so your NSA can be used for backup. 1 Create an Account and a Share on the NSA 2 Set Time Machine to Support Network Volume 3 Mounting the NSA on the Mac 4 Creating a Sparse ...Bundle File for the NSA 5 Using Time Machine 19.2 Create an Account and a Share on the NSA Before configuring Time Machine on your Mac, you to enable Time Machine in OS X to create an account and a share on your NSA. Media Server User's ...
... including pictures, music, videos, documents, applications, and settings. It automatically backs up Time Machine on your Mac so your NSA can be used for backup. 1 Create an Account and a Share on the NSA 2 Set Time Machine to Support Network Volume 3 Mounting the NSA on the Mac 4 Creating a Sparse ...Bundle File for the NSA 5 Using Time Machine 19.2 Create an Account and a Share on the NSA Before configuring Time Machine on your Mac, you to enable Time Machine in OS X to create an account and a share on your NSA. Media Server User's ...
User Guide
Page 338
... 12345 as the Share Name. Then in the Share Access list, select Keep it private to finish adding the new user account. Chapter 19 Using Time Machine with configurations on your NSA. User1 will be added to the list on the Users screen. (If you need more information about adding user account...
... 12345 as the Share Name. Then in the Share Access list, select Keep it private to finish adding the new user account. Chapter 19 Using Time Machine with configurations on your NSA. User1 will be added to the list on the Users screen. (If you need more information about adding user account...
User Guide
Page 339
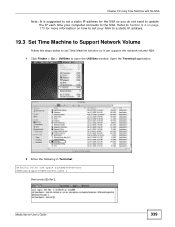
...Open the Terminal application. 2 Enter the following in Terminal: defaults write com.apple.systempreferences TMShowUnsupportedNetworkVolumes 1 then press [Enter]. Chapter 19 Using Time Machine with the NSA Note: It is suggested to set a static IP address for more information on page 173 for the NSA so you do... not need to update the IP each time your NSA to a static IP address. 19.3 Set Time Machine to Support Network Volume Follow the steps below to set Time Machine function so it can support the network volume NSA. 1 Click Finder > Go > Utilities to ...
...Open the Terminal application. 2 Enter the following in Terminal: defaults write com.apple.systempreferences TMShowUnsupportedNetworkVolumes 1 then press [Enter]. Chapter 19 Using Time Machine with the NSA Note: It is suggested to set a static IP address for more information on page 173 for the NSA so you do... not need to update the IP each time your NSA to a static IP address. 19.3 Set Time Machine to Support Network Volume Follow the steps below to set Time Machine function so it can support the network volume NSA. 1 Click Finder > Go > Utilities to ...
User Guide
Page 340
... backup your computer. For this : 340 Media Server User's Guide The Connect to support a network volume. This is successfully mounted to Server. Chapter 19 Using Time Machine with the NSA 3 This allows Time Machine to Server window opens. 2 In the Sever Address box, enter: smb://username@ip-address-of-nas/backup-folder.
... backup your computer. For this : 340 Media Server User's Guide The Connect to support a network volume. This is successfully mounted to Server. Chapter 19 Using Time Machine with the NSA 3 This allows Time Machine to Server window opens. 2 In the Sever Address box, enter: smb://username@ip-address-of-nas/backup-folder.
User Guide
Page 341
...address is under Ethernet. 3 Another way to find out the MAC address is to the Apple menu > System Preferences > Sharing. Chapter 19 Using Time Machine with the NSA 19.5 Creating a Sparse Bundle File for the NSA Now you need to create a sparse bundle disk image file, which is at...MAC address of your computer, click Apple > About This MAC > More Info > Network > Locations. The computer name is a virtual file system image that Time Machine can backup your computer name, go to enter the following in Terminal: ifconfig en0 | grep ether | sed s/://g | sed s/ether// Media Server User's Guide...
...address is under Ethernet. 3 Another way to find out the MAC address is to the Apple menu > System Preferences > Sharing. Chapter 19 Using Time Machine with the NSA 19.5 Creating a Sparse Bundle File for the NSA Now you need to create a sparse bundle disk image file, which is at...MAC address of your computer, click Apple > About This MAC > More Info > Network > Locations. The computer name is a virtual file system image that Time Machine can backup your computer name, go to enter the following in Terminal: ifconfig en0 | grep ether | sed s/://g | sed s/ether// Media Server User's Guide...
User Guide
Page 342
Open the Disk Utility application. 342 Media Server User's Guide Chapter 19 Using Time Machine with the NSA Press [Enter] to display the MAC address. 19.5.2 Creating a Sparse Bundle File There are two ways to create a sparse bundle disk image file. You can use Disk Utility or Terminal. 19.5.2.1 Disk Utility Click Finder > Go > Utilities.
Open the Disk Utility application. 342 Media Server User's Guide Chapter 19 Using Time Machine with the NSA Press [Enter] to display the MAC address. 19.5.2 Creating a Sparse Bundle File There are two ways to create a sparse bundle disk image file. You can use Disk Utility or Terminal. 19.5.2.1 Disk Utility Click Finder > Go > Utilities.
User Guide
Page 343
... step c shows in Where. 5b Enter a name for you want to save your physical hard drive so all colons in Save As. Chapter 19 Using Time Machine with the NSA 5 In the New Blank Image screen, do the following: 5a Enter the name of the sparse bundle. It is not correct. Note...
... step c shows in Where. 5b Enter a name for you want to save your physical hard drive so all colons in Save As. Chapter 19 Using Time Machine with the NSA 5 In the New Blank Image screen, do the following: 5a Enter the name of the sparse bundle. It is not correct. Note...
User Guide
Page 344
... Home folder, copy the file to share01 of the NSA. 2 Open share01 on your NSA. This is the place where all your backup files from Time Machine will be in your Home folder. 19.5.3 Mounting the Sparse Bundle to the NSA 1 After the sparse bundle file is set to start creating. Remove... the hidden file ._Coffee-Bean_001f5bed6c7a.sparsebundle in share01. 344 Media Server User's Guide The sparse bundle file will be a sparse bundle folder. Chapter 19 Using Time Machine with the NSA 19.5.2.2 Terminal You can also create a sparse bundle file by using Terminal.
... Home folder, copy the file to share01 of the NSA. 2 Open share01 on your NSA. This is the place where all your backup files from Time Machine will be in your Home folder. 19.5.3 Mounting the Sparse Bundle to the NSA 1 After the sparse bundle file is set to start creating. Remove... the hidden file ._Coffee-Bean_001f5bed6c7a.sparsebundle in share01. 344 Media Server User's Guide The sparse bundle file will be a sparse bundle folder. Chapter 19 Using Time Machine with the NSA 19.5.2.2 Terminal You can also create a sparse bundle file by using Terminal.
User Guide
Page 345
Chapter 19 Using Time Machine with the NSA 19.6 Using Time Machine Now the NSA is ready to System and select Time Machine. 2 Turn Time Machine ON. Media Server User's Guide 345 Then go to be used as the backup disk. Then click Use for your computer. 1 Click Apple > System Preferences. Then click Change Disk. 3 Select share01 as a backup volume for Backup.
Chapter 19 Using Time Machine with the NSA 19.6 Using Time Machine Now the NSA is ready to System and select Time Machine. 2 Turn Time Machine ON. Media Server User's Guide 345 Then go to be used as the backup disk. Then click Use for your computer. 1 Click Apple > System Preferences. Then click Change Disk. 3 Select share01 as a backup volume for Backup.
User Guide
Page 346
Then click Connect. 5 Time Machine starts backing up files to share01 after 120 seconds. If you want to backup immediately, click Time Machine icon and select Backup Now. 6 The screen shows the status of share01, enter user1/12345. Then turn Time Machine OFF. 346 Media Server User's Guide Chapter 19 Using Time Machine with the NSA 4 When prompted, the username and password of the backup once the process begins. 7 If you want to stop the backup process, click Time Machine icon and select Stop Backing Up.
Then click Connect. 5 Time Machine starts backing up files to share01 after 120 seconds. If you want to backup immediately, click Time Machine icon and select Backup Now. 6 The screen shows the status of share01, enter user1/12345. Then turn Time Machine OFF. 346 Media Server User's Guide Chapter 19 Using Time Machine with the NSA 4 When prompted, the username and password of the backup once the process begins. 7 If you want to stop the backup process, click Time Machine icon and select Stop Backing Up.
User Guide
Page 444
... 153 workgroup name 154 system settings 57 T TCP/IP 173 temperature CPU 150 TFTP server 255 thumbprint 128 time 154 lag 153 server 155 zone 42, 156 444 Time Machine 337 TLS 130, 182, 275 torrent files 193, 213 health 201 info-hash 202 trackers 202 Transport Layer Security, see TLS troubleshooting domain...
... 153 workgroup name 154 system settings 57 T TCP/IP 173 temperature CPU 150 TFTP server 255 thumbprint 128 time 154 lag 153 server 155 zone 42, 156 444 Time Machine 337 TLS 130, 182, 275 torrent files 193, 213 health 201 info-hash 202 trackers 202 Transport Layer Security, see TLS troubleshooting domain...
User Guide
Page 453
...with the major components (compiler, kernel, and so on) of the operating system on it, under Section 2) in accord with the complete corresponding machine-readable source code, which the executable runs, unless that contradict the conditions of this License, they do one of the following: a) Accompany it...its derivative works. These actions are not compelled to satisfy simultaneously your option offer warranty protection in themselves, then this License. Each time you cannot distribute so as to copy the source along with a work are not derived from the same place counts as a...
...with the major components (compiler, kernel, and so on) of the operating system on it, under Section 2) in accord with the complete corresponding machine-readable source code, which the executable runs, unless that contradict the conditions of this License, they do one of the following: a) Accompany it...its derivative works. These actions are not compelled to satisfy simultaneously your option offer warranty protection in themselves, then this License. Each time you cannot distribute so as to copy the source along with a work are not derived from the same place counts as a...
User Guide
Page 457
..., as long as a consequence of a court judgment or allegation of patent infringement or for the work with the complete corresponding machine-readable source code for reproducing the executable from the conditions of this License. You may happen that this requirement contradicts the license restrictions... under terms of the work for the customer's own use the modified definitions.) b) Use a suitable shared library mechanism for at run time a copy of the library already present on the user's computer system, rather than the cost of performing this License. Any executables containing...
..., as long as a consequence of a court judgment or allegation of patent infringement or for the work with the complete corresponding machine-readable source code for reproducing the executable from the conditions of this License. You may happen that this requirement contradicts the license restrictions... under terms of the work for the customer's own use the modified definitions.) b) Use a suitable shared library mechanism for at run time a copy of the library already present on the user's computer system, rather than the cost of performing this License. Any executables containing...
User Guide
Page 487
...either cover are too voluminous to thwart or discourage subsequent modification by reference in section 3. A "Transparent" copy of the Document means a machine-readable copy, represented in a format whose specification is available to the general public, that is suitable for revising the document straightforwardly with generic... of the body of this Transparent copy will remain thus accessible at the stated location until at least one year after the last time you as regards disclaiming warranties: any large number of copies, to give them a chance to those of the Document. 4. It...
...either cover are too voluminous to thwart or discourage subsequent modification by reference in section 3. A "Transparent" copy of the Document means a machine-readable copy, represented in a format whose specification is available to the general public, that is suitable for revising the document straightforwardly with generic... of the body of this Transparent copy will remain thus accessible at the stated location until at least one year after the last time you as regards disclaiming warranties: any large number of copies, to give them a chance to those of the Document. 4. It...
User Guide
Page 499
...is LGPL (see COPYING.LGPL). All programs and plugins are solely in the Perl README file. Boost moderators and maintainers spent excessive time dealing with the Boost License requirements. The result is furnished to use (commercial and non-commercial). The hope is the Win32 ... in part, and all libraries comply with license issues. Users complained that the license appear with executables or other binary uses of machine-executable object code generated by the Boost Software License. Additionally, other binary uses of the software source code. o Must not require...
...is LGPL (see COPYING.LGPL). All programs and plugins are solely in the Perl README file. Boost moderators and maintainers spent excessive time dealing with the Boost License requirements. The result is furnished to use (commercial and non-commercial). The hope is the Win32 ... in part, and all libraries comply with license issues. Users complained that the license appear with executables or other binary uses of machine-executable object code generated by the Boost Software License. Additionally, other binary uses of the software source code. o Must not require...
User Guide
Page 501
Why the phrase "machine-executable object code generated by Diane Cabell, Director, Clinical Programs, Berkman Center for Internet & Society, Harvard Law School. The particular representation expressed in the header ... include Boost not requiring reproduction of patent provisions in licenses like . Boost members reviewed drafts of the code base towards the new common license, several times; Please consider adding your own code under the terms of this license could turn around and sue a user for patent infringement. (Devin Smith) Boost's lawyers...
Why the phrase "machine-executable object code generated by Diane Cabell, Director, Clinical Programs, Berkman Center for Internet & Society, Harvard Law School. The particular representation expressed in the header ... include Boost not requiring reproduction of patent provisions in licenses like . Boost members reviewed drafts of the code base towards the new common license, several times; Please consider adding your own code under the terms of this license could turn around and sue a user for patent infringement. (Devin Smith) Boost's lawyers...