Manuals
Page 48
.... See "Saving Energy", Getting Started . Number keys Use to program defaults for the selected function. 46 In Sleep mode, the [Energy Saver] key flashes slowly. 9. [Login/Logout] key Press to log in progress, such as copying, scanning, faxing, or printing. 16. [Clear] key Press to make interrupt copies. See "Switching Screen...
.... See "Saving Energy", Getting Started . Number keys Use to program defaults for the selected function. 46 In Sleep mode, the [Energy Saver] key flashes slowly. 9. [Login/Logout] key Press to log in progress, such as copying, scanning, faxing, or printing. 16. [Clear] key Press to make interrupt copies. See "Switching Screen...
Manuals
Page 63
... for logging in the machine, be sure to enter a User Code appears. 1. The machine only becomes operable after entering your own Login User Name and Login Password. If User Code Authentication is set. 61 If User Code Authentication is active. Enter a User Code (up to the machine ... active, a screen prompting you are logged out. After logging in to prevent unauthorized usage. • Ask the user administrator for the Login User Name, Login Password, and User Code. If you can say that you enter the User Code. User Code Authentication Using the Control Panel This section...
... for logging in the machine, be sure to enter a User Code appears. 1. The machine only becomes operable after entering your own Login User Name and Login Password. If User Code Authentication is set. 61 If User Code Authentication is active. Enter a User Code (up to the machine ... active, a screen prompting you are logged out. After logging in to prevent unauthorized usage. • Ask the user administrator for the Login User Name, Login Password, and User Code. If you can say that you enter the User Code. User Code Authentication Using the Control Panel This section...
Manuals
Page 64
... use of the machine by unauthorized persons, always log out when you are using the machine. 1. Press the [Login/Logout] key. Press [Yes]. 62 2. Enter a Login User Name, and then press [OK]. 3. Enter a Login Password, and then press [OK]. Logging Out Using the Control Panel This section explains the procedure for the function...
... use of the machine by unauthorized persons, always log out when you are using the machine. 1. Press the [Login/Logout] key. Press [Yes]. 62 2. Enter a Login User Name, and then press [OK]. 3. Enter a Login Password, and then press [OK]. Logging Out Using the Control Panel This section explains the procedure for the function...
Manuals
Page 117
...], [IJK], [LMN], [OPQ], [RST], [UVW], [XYZ], [1] to [10]: Added to the list of items in "Default User Name / Password (Send)" of "Folder Authentication". Enter the login user name of the destination computer, and then press [OK]. 14. Enter the password of the destination computer, and then press [OK]. 12. Press [Folder... selected title. You can either enter the path manually or locate the folder by browsing the network. 18. Press [Specify Other Auth. Press [Change] under "Login Password". 13.
...], [IJK], [LMN], [OPQ], [RST], [UVW], [XYZ], [1] to [10]: Added to the list of items in "Default User Name / Password (Send)" of "Folder Authentication". Enter the login user name of the destination computer, and then press [OK]. 14. Enter the password of the destination computer, and then press [OK]. 12. Press [Folder... selected title. You can either enter the path manually or locate the folder by browsing the network. 18. Press [Specify Other Auth. Press [Change] under "Login Password". 13.
Manuals
Page 173
...to be displayed even though you open and close the cover as required. • Paper is still jammed in the tray. The entered login user name or login password is removed. • When a misfeed message appears, it remains until you have the privileges to set . The machine cannot ...then open and close the cover. Load paper into the Large capacity tray (LCT), or bypass tray with the print side up. Enter your login user name and user password. The logged in when User Code Authentication is enabled, see "When the Authentication Screen is Displayed", Getting Started . ...
...to be displayed even though you open and close the cover as required. • Paper is still jammed in the tray. The entered login user name or login password is removed. • When a misfeed message appears, it remains until you have the privileges to set . The machine cannot ...then open and close the cover. Load paper into the Large capacity tray (LCT), or bypass tray with the print side up. Enter your login user name and user password. The logged in when User Code Authentication is enabled, see "When the Authentication Screen is Displayed", Getting Started . ...
Manuals
Page 186
...; Check that User Name and Password for the following settings in [System Settings] are listed correctly. • SMTP Authentication • POP before SMTP authentication, or login authentication of the computer in [Fax E-mail Account] of [System Settings]. Troubleshooting Message "Check whether there are any network problems." [14-33] Causes E-mail transmission...
...; Check that User Name and Password for the following settings in [System Settings] are listed correctly. • SMTP Authentication • POP before SMTP authentication, or login authentication of the computer in [Fax E-mail Account] of [System Settings]. Troubleshooting Message "Check whether there are any network problems." [14-33] Causes E-mail transmission...
Manuals
Page 212
... logged in user is not supported. Delete some of the files stored in the Document of files." This job has been function. The entered login user name or login password is incorrect. cancelled." memory." 10. have a privilege to use the selected permissions, see Security Guide . Delete the files stored in user does...
... logged in user is not supported. Delete some of the files stored in the Document of files." This job has been function. The entered login user name or login password is incorrect. cancelled." memory." 10. have a privilege to use the selected permissions, see Security Guide . Delete the files stored in user does...
Manuals
Page 228
...driver encryption key was invalid. However, the access privileges for permissions, see Security Guide . An unrecoverable error has Contact your login user name, login password, or driver encryption key, and then enter them correctly. Message Causes Solutions "Any of registerable scan modes has been...access mask is 100. The logged in user name For details about login user name, login password, and driver encryption key, see Security Guide . The maximum number of Login User Name, Login Password or Driver Encryption Key is incorrect." occurred in User Tools." ...
...driver encryption key was invalid. However, the access privileges for permissions, see Security Guide . An unrecoverable error has Contact your login user name, login password, or driver encryption key, and then enter them correctly. Message Causes Solutions "Any of registerable scan modes has been...access mask is 100. The logged in user name For details about login user name, login password, and driver encryption key, see Security Guide . The maximum number of Login User Name, Login Password or Driver Encryption Key is incorrect." occurred in User Tools." ...
Manuals
Page 238
..., 37, 39, 41, 43, 144, 146 Locked Print 15, 104 Locked print file 104 Logging in to the machine 61 Logging out the machine 62 Login/Logout key 45 Lower paper tray......27, 30, 33, 35, 37, 39, 41, 43 Lower right cover 27, 30 M Magazine 14 Main power 59 Main...
..., 37, 39, 41, 43, 144, 146 Locked Print 15, 104 Locked print file 104 Logging in to the machine 61 Logging out the machine 62 Login/Logout key 45 Lower paper tray......27, 30, 33, 35, 37, 39, 41, 43 Lower right cover 27, 30 M Magazine 14 Main power 59 Main...
Security Target
Page 14
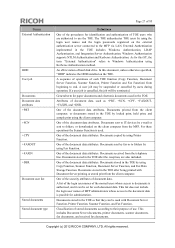
... Font, LANG0, LANG1, and Data Erase Onb. FCU Control Software is the identifier for the Operation Panel Control Software. Copyright (c) 2012 RICOH COMPANY, LTD. The Operation Control Board is shipped. - The Engine Control Software sends status information about the Controller Board and the FCU .... The Operation Panel Control Software is an output device to and from the MFP Control Software. It stores documents, login user names and login passwords of 93 and digital signature. The Operation Panel Control Software performs the following devices: key switches, LED indicators,...
... Font, LANG0, LANG1, and Data Erase Onb. FCU Control Software is the identifier for the Operation Panel Control Software. Copyright (c) 2012 RICOH COMPANY, LTD. The Operation Control Board is shipped. - The Engine Control Software sends status information about the Controller Board and the FCU .... The Operation Panel Control Software is an output device to and from the MFP Control Software. It stores documents, login user names and login passwords of 93 and digital signature. The Operation Panel Control Software performs the following devices: key switches, LED indicators,...
Security Target
Page 19
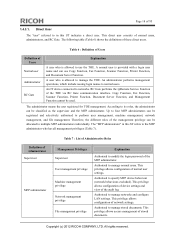
... and file management. This privilege allows access management of these direct users. An administrator performs management operations, which include issuing login names to specify MFP device behaviour (network behaviours excluded). Authorised to normal users. Table 6 : Definition of Users Definition... : List of the management privilege can use the TOE. This privilege allows configuration of normal user settings. Copyright (c) 2012 RICOH COMPANY, LTD. Direct User The "user" referred to manage stored documents. Copy Function, Fax Function, Scanner Function, Printer ...
... and file management. This privilege allows access management of these direct users. An administrator performs management operations, which include issuing login names to specify MFP device behaviour (network behaviours excluded). Authorised to normal users. Table 6 : Definition of Users Definition... : List of the management privilege can use the TOE. This privilege allows configuration of normal user settings. Copyright (c) 2012 RICOH COMPANY, LTD. Direct User The "user" referred to manage stored documents. Copy Function, Fax Function, Scanner Function, Printer ...
Security Target
Page 24
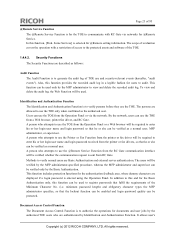
... functions for @Remote Service. It allows user's Copyright (c) 2012 RICOH COMPANY, LTD. Security Functions The Security Functions are allowed to use the @Remote Service Function from the RC Gate communication interface will be required to verify normal users are displayed if a login password is entered using the Operation Panel. To view and...
... functions for @Remote Service. It allows user's Copyright (c) 2012 RICOH COMPANY, LTD. Security Functions The Security Functions are allowed to use the @Remote Service Function from the RC Gate communication interface will be required to verify normal users are displayed if a login password is entered using the Operation Panel. To view and...
Security Target
Page 26
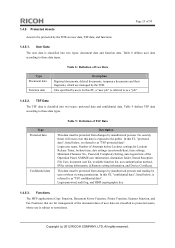
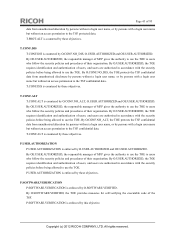
...whose use is referred to as "TSF protected data". Table 9 defines TSF data according to these data types. Login password, audit log, and HDD cryptographic key. 1.4.5.3. Table 8 defines user data according to these data types. TSF...restrictions. Type Protected data Confidential data Table 9 : Definition of user data are managed by unauthorised persons. Login user name, Number of Attempts before Lockout, settings for management of the document data of TSF Data Description... be protected from changes by the TOE. Copyright (c) 2012 RICOH COMPANY, LTD. All rights reserved.
...whose use is referred to as "TSF protected data". Table 9 defines TSF data according to these data types. Login password, audit log, and HDD cryptographic key. 1.4.5.3. Table 8 defines user data according to these data types. TSF...restrictions. Type Protected data Confidential data Table 9 : Definition of user data are managed by unauthorised persons. Login user name, Number of Attempts before Lockout, settings for management of the document data of TSF Data Description... be protected from changes by the TOE. Copyright (c) 2012 RICOH COMPANY, LTD. All rights reserved.
Security Target
Page 27
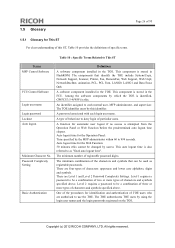
... All rights reserved. A function for the Web Function: 30 minutes (this cannot be used as "fixed auto logout time". Copyright (c) 2012 RICOH COMPANY, LTD. 1.5 Glossary Page 26 of 93 1.5.1 Glossary for This ST For clear understanding of this ST, Table 10 provides the definitions ... lower case alphabets, digits and symbols. There are four types of behaviour to This ST Terms MFP Control Software FCU Control Software Login user name Login password Lockout Auto logout Minimum Character No. Level 2 requires a password to be a combination of three or more types of registrable...
... All rights reserved. A function for the Web Function: 30 minutes (this cannot be used as "fixed auto logout time". Copyright (c) 2012 RICOH COMPANY, LTD. 1.5 Glossary Page 26 of 93 1.5.1 Glossary for This ST For clear understanding of this ST, Table 10 provides the definitions ... lower case alphabets, digits and symbols. There are four types of behaviour to This ST Terms MFP Control Software FCU Control Software Login user name Login password Lockout Auto logout Minimum Character No. Level 2 requires a password to be a combination of three or more types of registrable...
Security Target
Page 28
...of the procedures for identification and authentication of each document data. The TOE authenticates TOE users by using the login user names and the login passwords registered on the external authentication server connected to Windows Authentication using Kerberos Authentication method. A sequence of ...in the TOE so that they can be used . General term for administration. One of the document data attributes. Copyright (c) 2012 RICOH COMPANY, LTD. A user job may be terminated. One of the document data attributes. External Authentication implemented in the TOE includes ...
...of the procedures for identification and authentication of each document data. The TOE authenticates TOE users by using the login user names and the login passwords registered on the external authentication server connected to Windows Authentication using Kerberos Authentication method. A sequence of ...in the TOE so that they can be used . General term for administration. One of the document data attributes. Copyright (c) 2012 RICOH COMPANY, LTD. A user job may be terminated. One of the document data attributes. External Authentication implemented in the TOE includes ...
Security Target
Page 36
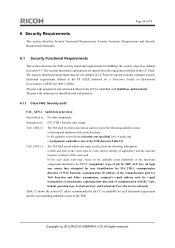
....ALT Alteration of TSF protected data TSF Protected Data under the TOE management may be altered by persons without a login user name, or by persons with a login user name but without an access permission to the document. T.CONF.ALT Alteration of TSF confidential data TSF Confidential ... User jobs under the TOE management may be disclosed to persons without a login user name, or to persons with a login user name but without an access permission to the TSF Confidential Data. Copyright (c) 2012 RICOH COMPANY, LTD. The threats defined in this section are unauthorised persons with...
....ALT Alteration of TSF protected data TSF Protected Data under the TOE management may be altered by persons without a login user name, or by persons with a login user name but without an access permission to the document. T.CONF.ALT Alteration of TSF confidential data TSF Confidential ... User jobs under the TOE management may be disclosed to persons without a login user name, or to persons with a login user name but without an access permission to the TSF Confidential Data. Copyright (c) 2012 RICOH COMPANY, LTD. The threats defined in this section are unauthorised persons with...
Security Target
Page 39
... shall protect documents from unauthorised disclosure by persons without a login user name, or by persons with a login user name but without an access permission to the document. All rights reserved. Copyright (c) 2012 RICOH COMPANY, LTD. O.DOC.NO_ALT Protection of user job alteration... The TOE shall protect user jobs from unauthorised alteration by persons without a login user name, or by persons with a login user name but without an access permission ...
... shall protect documents from unauthorised disclosure by persons without a login user name, or by persons with a login user name but without an access permission to the document. All rights reserved. Copyright (c) 2012 RICOH COMPANY, LTD. O.DOC.NO_ALT Protection of user job alteration... The TOE shall protect user jobs from unauthorised alteration by persons without a login user name, or by persons with a login user name but without an access permission ...
Security Target
Page 43
... name but without a login user name, or by persons with the security policies before being allowed to use the TOE. By O.PROT.NO_ALT, the TOE protects the TSF protected Copyright (c) 2012 RICOH COMPANY, LTD. By OE.USER.AUTHORIZED, the responsible manager of MFP gives the authority to use the...to use the TOE to users who follow the security policies and procedures of users, and users are authorised in accordance with a login user name but without a login user name, or by these objectives. All rights reserved. Page 42 of users, and users are authorised in accordance with the...
... name but without a login user name, or by persons with the security policies before being allowed to use the TOE. By O.PROT.NO_ALT, the TOE protects the TSF protected Copyright (c) 2012 RICOH COMPANY, LTD. By OE.USER.AUTHORIZED, the responsible manager of MFP gives the authority to use the...to use the TOE to users who follow the security policies and procedures of users, and users are authorised in accordance with a login user name but without a login user name, or by these objectives. All rights reserved. Page 42 of users, and users are authorised in accordance with the...
Security Target
Page 44
...TOE to users who follow the security policies and procedures of users, and users are authorised in accordance with a login user name but without a login user name, or by these objectives. P.USER.AUTHORIZATION is enforced by these objectives. By O.USER.AUTHORIZED, the ... O.USER.AUTHORIZED, the TOE requires identification and authentication of the TSF. P.SOFTWARE.VERIFICATION is enforced by this objective. Copyright (c) 2012 RICOH COMPANY, LTD. T.PROT.ALT is countered by these objectives. T.CONF.DIS T.CONF.DIS is countered by O.CONF.NO_DIS, O.USER.AUTHORIZED ...
...TOE to users who follow the security policies and procedures of users, and users are authorised in accordance with a login user name but without a login user name, or by these objectives. P.USER.AUTHORIZATION is enforced by these objectives. By O.USER.AUTHORIZED, the ... O.USER.AUTHORIZED, the TOE requires identification and authentication of the TSF. P.SOFTWARE.VERIFICATION is enforced by this objective. Copyright (c) 2012 RICOH COMPANY, LTD. T.PROT.ALT is countered by these objectives. T.CONF.DIS T.CONF.DIS is countered by O.CONF.NO_DIS, O.USER.AUTHORIZED ...
Security Target
Page 49
Copyright (c) 2012 RICOH COMPANY, LTD. Page 48 of the TOE shown in Table 12]. The security functional requirements that attempted the user identification for FIA_UID.1, communication direction of ... audit event type, based on the auditable event definitions of the functional components included in the PP/ST, [assignment: types of job for FDP_ACF.1(a), all login user names that are not defined in CC Part2 are quoted from the extended security functional requirements defined in the PP (IEEE Standard for the...
Copyright (c) 2012 RICOH COMPANY, LTD. Page 48 of the TOE shown in Table 12]. The security functional requirements that attempted the user identification for FIA_UID.1, communication direction of ... audit event type, based on the auditable event definitions of the functional components included in the PP/ST, [assignment: types of job for FDP_ACF.1(a), all login user names that are not defined in CC Part2 are quoted from the extended security functional requirements defined in the PP (IEEE Standard for the...