General Settings Guide
Page 209
... loss. Info You can also register login user names and login passwords to folders, or accessing an LDAP server. 201 This is stored on the hard disk. You can register user codes in order to restrict particular functions to certain users, and to register destinations and users in the Address Book: ❖...
... loss. Info You can also register login user names and login passwords to folders, or accessing an LDAP server. 201 This is stored on the hard disk. You can register user codes in order to restrict particular functions to certain users, and to register destinations and users in the Address Book: ❖...
Security Target
Page 4
...Objectives Rationale 42 4.3.1 Correspondence Table of Security Objectives 42 4.3.2 Security Objectives Descriptions 43 5 Extended Components Definition 47 5.1 Restricted forwarding of data to external interfaces (FPT_FDI_EXP 47 6 Security Requirements...49 6.1 Security Functional Requirements 49 6.1.1 Class FAU: ... authentication 58 6.1.5 Class FMT: Security management 61 6.1.6 Class FPT: Protection of the TSF 67 6.1.7 Class FTA: TOE access 68 6.1.8 Class FTP: Trusted path/channels 68 6.2 Security Assurance Requirements 68 6.3 Security Requirements Rationale 69 6.3.1 Tracing ...69...
...Objectives Rationale 42 4.3.1 Correspondence Table of Security Objectives 42 4.3.2 Security Objectives Descriptions 43 5 Extended Components Definition 47 5.1 Restricted forwarding of data to external interfaces (FPT_FDI_EXP 47 6 Security Requirements...49 6.1 Security Functional Requirements 49 6.1.1 Class FAU: ... authentication 58 6.1.5 Class FMT: Security management 61 6.1.6 Class FPT: Protection of the TSF 67 6.1.7 Class FTA: TOE access 68 6.1.8 Class FTP: Trusted path/channels 68 6.2 Security Assurance Requirements 68 6.3 Security Requirements Rationale 69 6.3.1 Tracing ...69...
Security Target
Page 5
Page 4 of 93 7.3 Document Access Control Function 84 7.4 Use-of-Feature Restriction Function 86 7.5 Network Protection Function 87 7.6 Residual Data Overwrite Function 87 7.7 Stored Data Protection Function 88 7.8 Security Management Function 88 7.9 Software Verification Function 93 7.10 Fax Line Separation Function 93 Copyright (c) 2011 RICOH COMPANY, LTD. All rights reserved.
Page 4 of 93 7.3 Document Access Control Function 84 7.4 Use-of-Feature Restriction Function 86 7.5 Network Protection Function 87 7.6 Residual Data Overwrite Function 87 7.7 Stored Data Protection Function 88 7.8 Security Management Function 88 7.9 Software Verification Function 93 7.10 Fax Line Separation Function 93 Copyright (c) 2011 RICOH COMPANY, LTD. All rights reserved.
Security Target
Page 12
Document Access Control Function - Stored Data Protection Function - All rights reserved. Audit Function - Use-of the following hardware components (shown in Figure 2): Operation Panel Unit, Engine Unit, ... Users, Logical Boundary of TOE, and Protected Assets. 1.4.1 Physical Boundary of TOE The physical boundary of the TOE is the MFP, which consists of -Feature Restriction Function - Software Verification Function - Copyright (c) 2011 RICOH COMPANY, LTD. Security Management Function - Identification and Authentication Function - - Network Protection Function -
Document Access Control Function - Stored Data Protection Function - All rights reserved. Audit Function - Use-of the following hardware components (shown in Figure 2): Operation Panel Unit, Engine Unit, ... Users, Logical Boundary of TOE, and Protected Assets. 1.4.1 Physical Boundary of TOE The physical boundary of the TOE is the MFP, which consists of -Feature Restriction Function - Software Verification Function - Copyright (c) 2011 RICOH COMPANY, LTD. Security Management Function - Identification and Authentication Function - - Network Protection Function -
Security Target
Page 26
...the network, users can use the TOE. Network Protection Function The Network Protection Function is to authorise the operations of -Feature Restriction Function is to enter his or her login user name and login password received from RC Gate. If the e-mail Copyright (c) 2011... RICOH COMPANY, LTD. To use the @Remote Service Function from the Operation Panel or via the network. Document Access Control Function The Document Access Control Function is to verify persons before they use the TOE from the ...
...the network, users can use the TOE. Network Protection Function The Network Protection Function is to authorise the operations of -Feature Restriction Function is to enter his or her login user name and login password received from RC Gate. If the e-mail Copyright (c) 2011... RICOH COMPANY, LTD. To use the @Remote Service Function from the Operation Panel or via the network. Document Access Control Function The Document Access Control Function is to verify persons before they use the TOE from the ...
Security Target
Page 35
...PP. All rights reserved. This is to delete document data and user jobs. Augmentation of restricted forwarding of data to external interface (FPT_FDI_EXP) This TOE, in the PP require the access control SFP to operate the TOE, unless they are the special users for some reasons. ...ST satisfies FDP_ACF.1 (a) in the PP allows users with RC Gate via LAN on access control of the PP. Copyright (c) 2011 RICOH COMPANY, LTD. Therefore, FDP_ACF.1 (a) in this ST requires the access control SFP to the document data that the PP does not allow users to the document...
...PP. All rights reserved. This is to delete document data and user jobs. Augmentation of restricted forwarding of data to external interface (FPT_FDI_EXP) This TOE, in the PP require the access control SFP to operate the TOE, unless they are the special users for some reasons. ...ST satisfies FDP_ACF.1 (a) in the PP allows users with RC Gate via LAN on access control of the PP. Copyright (c) 2011 RICOH COMPANY, LTD. Therefore, FDP_ACF.1 (a) in this ST requires the access control SFP to the document data that the PP does not allow users to the document...
Security Target
Page 36
...RICOH COMPANY, LTD. All rights reserved. Therefore, the requirements described in FDP_ACF.1.3(b) in the PP. Therefore, FDP_ACF.1.3(b) in this ST satisfies FDP_ACF.1.3(b) in the PP are satisfied at the same time. The fax reception process, which is accessed when receiving from a telephone line, is regarded as a result, the TSF restrictively... allows the MFP administrator to delete document data and user jobs (document access control SFP, FDP_ACC.1(a) and ...
...RICOH COMPANY, LTD. All rights reserved. Therefore, the requirements described in FDP_ACF.1.3(b) in the PP. Therefore, FDP_ACF.1.3(b) in this ST satisfies FDP_ACF.1.3(b) in the PP are satisfied at the same time. The fax reception process, which is accessed when receiving from a telephone line, is regarded as a result, the TSF restrictively... allows the MFP administrator to delete document data and user jobs (document access control SFP, FDP_ACC.1(a) and ...
Security Target
Page 38
...stored on the HDD inside the TOE shall be authorised to use the TOE. A.ACCESS.MANAGED Access management According to this TOE usage environment are identified and described. Copyright (c) 2011 RICOH COMPANY, LTD. P.INTERFACE.MANAGEMENT Management of external interfaces To prevent unauthorised use and security... are aware of the security policies and procedures of their organisation and are competent to self-verify executable code in a restricted or monitored area that provides protection from unauthorised disclosure or alteration, and shall be reviewed by authorised persons. The audit...
...stored on the HDD inside the TOE shall be authorised to use the TOE. A.ACCESS.MANAGED Access management According to this TOE usage environment are identified and described. Copyright (c) 2011 RICOH COMPANY, LTD. P.INTERFACE.MANAGEMENT Management of external interfaces To prevent unauthorised use and security... are aware of the security policies and procedures of their organisation and are competent to self-verify executable code in a restricted or monitored area that provides protection from unauthorised disclosure or alteration, and shall be reviewed by authorised persons. The audit...
Security Target
Page 46
...the TOE creates and maintains a log of TOE use and security-relevant events in accordance with those records can be accessed in a restricted or monitored environment according to detect potential security violations, and only by authorised persons. By OE.AUDIT_ACCESS.AUTHORIZED, the .... P.STORAGE.ENCRYPTION is upheld by O.AUDIT.LOGGED, OE.AUDIT.REVIEWED, OE.AUDIT_STORAGE.PROTECTED and OE.AUDIT_ACCESS.AUTHORIZED. Copyright (c) 2011 RICOH COMPANY, LTD. By O.INTERFACE.MANAGED, the TOE manages the operation of MFP protects those encrypted data. By O.STORAGE.ENCRYPTED, the...
...the TOE creates and maintains a log of TOE use and security-relevant events in accordance with those records can be accessed in a restricted or monitored environment according to detect potential security violations, and only by authorised persons. By OE.AUDIT_ACCESS.AUTHORIZED, the .... P.STORAGE.ENCRYPTION is upheld by O.AUDIT.LOGGED, OE.AUDIT.REVIEWED, OE.AUDIT_STORAGE.PROTECTED and OE.AUDIT_ACCESS.AUTHORIZED. Copyright (c) 2011 RICOH COMPANY, LTD. By O.INTERFACE.MANAGED, the TOE manages the operation of MFP protects those encrypted data. By O.STORAGE.ENCRYPTED, the...
Security Target
Page 53
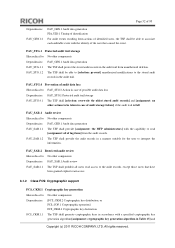
...events resulting from actions of identified users, the TSF shall be able to associate each auditable event with the capability to read -access. 6.1.2 Class FCS: Cryptographic support FCS_CKM.1 Cryptographic key generation Hierarchical to: No other components. Dependencies: FAU_GEN.1 Audit data generation ... audit records in Table 13] and Copyright (c) 2011 RICOH COMPANY, LTD. Dependencies: FAU_SAR.1 Audit review FAU_SAR.2.1 The TSF shall prohibit all of audit storage failure] if the audit trail is full. FAU_SAR.2 Restricted audit review Hierarchical to : FAU_STG.3 Action in case ...
...events resulting from actions of identified users, the TSF shall be able to associate each auditable event with the capability to read -access. 6.1.2 Class FCS: Cryptographic support FCS_CKM.1 Cryptographic key generation Hierarchical to: No other components. Dependencies: FAU_GEN.1 Audit data generation ... audit records in Table 13] and Copyright (c) 2011 RICOH COMPANY, LTD. Dependencies: FAU_SAR.1 Audit review FAU_SAR.2.1 The TSF shall prohibit all of audit storage failure] if the audit trail is full. FAU_SAR.2 Restricted audit review Hierarchical to : FAU_STG.3 Action in case ...
Security Target
Page 63
Copyright (c) 2011 RICOH COMPANY, LTD. All rights reserved. Query, modify ...operation permitted User Roles with operation permission in Table 26]. Page 62 of 93 Dependencies: [FDP_ACC.1 Subset access control, or FDP_IFC.1 Subset information flow control] FMT_SMR.1 Security roles FMT_SMF.1 Specification of normal user for... Basic Authentication Login user name of Management Function FMT_MSA.1.1(a) The TSF shall enforce the [assignment: document access control SFP] to restrict the ability to [selection: query, modify, delete, [assignment: newly create]] the security attributes [...
Copyright (c) 2011 RICOH COMPANY, LTD. All rights reserved. Query, modify ...operation permitted User Roles with operation permission in Table 26]. Page 62 of 93 Dependencies: [FDP_ACC.1 Subset access control, or FDP_IFC.1 Subset information flow control] FMT_SMR.1 Security roles FMT_SMF.1 Specification of normal user for... Basic Authentication Login user name of Management Function FMT_MSA.1.1(a) The TSF shall enforce the [assignment: document access control SFP] to restrict the ability to [selection: query, modify, delete, [assignment: newly create]] the security attributes [...
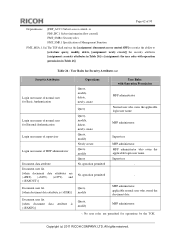
Security Target
Page 64
... to: No other components. FMT_MSA.3(a)Static attribute initialisation Hierarchical to enforce the SFP. All rights reserved. Copyright (c) 2011 RICOH COMPANY, LTD. Table 27 : User Roles for Security Attributes (b) Security Attributes Login user name of normal user for Basic...in case of security attributes FMT_SMR.1 Security roles FMT_MSA.3.1(a) The TSF shall enforce the [assignment: document access control SFP] to provide [selection: restrictive] default values for security attributes that are permitted for External Authentication Available function list Function type User role...
... to: No other components. FMT_MSA.3(a)Static attribute initialisation Hierarchical to enforce the SFP. All rights reserved. Copyright (c) 2011 RICOH COMPANY, LTD. Table 27 : User Roles for Security Attributes (b) Security Attributes Login user name of normal user for Basic...in case of security attributes FMT_SMR.1 Security roles FMT_MSA.3.1(a) The TSF shall enforce the [assignment: document access control SFP] to provide [selection: restrictive] default values for security attributes that are permitted for External Authentication Available function list Function type User role...
Security Target
Page 65
... Management of security attributes FMT_SMR.1 Security roles FMT_MSA.3.1(b)The TSF shall enforce the [assignment: TOE function access control SFP] to provide [selection: [assignment: the permissive to the available function list, restrictive to the function type, restrictive to the user role]] default values for the user role] to specify alternative initial values to override... [assignment: authorised identified roles shown in Table 28] to specify alternative initial values to : No other components. FMT_MTD.1 Management of Management Functions Copyright (c) 2011 RICOH COMPANY, LTD.
... Management of security attributes FMT_SMR.1 Security roles FMT_MSA.3.1(b)The TSF shall enforce the [assignment: TOE function access control SFP] to provide [selection: [assignment: the permissive to the available function list, restrictive to the function type, restrictive to the user role]] default values for the user role] to specify alternative initial values to override... [assignment: authorised identified roles shown in Table 28] to specify alternative initial values to : No other components. FMT_MTD.1 Management of Management Functions Copyright (c) 2011 RICOH COMPANY, LTD.
Security Target
Page 69
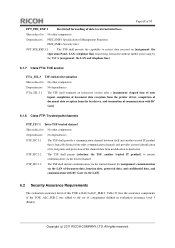
... defined in evaluation assurance level 3 (EAL3). Copyright (c) 2011 RICOH COMPANY, LTD. Dependencies: FMT_SMF.1 Specification of Management Functions FMT_SMR.1 Security roles FPT_FDI_EXP.1.1 The TSF shall provide the capability to restrict data received on [assignment: the Operation Panel, LAN, telephone ...line] from being forwarded without further processing by the TSF to [assignment: the LAN and telephone line]. 6.1.7 Class FTA: TOE access FTA_SSL.3 TSF-initiated termination ...
... defined in evaluation assurance level 3 (EAL3). Copyright (c) 2011 RICOH COMPANY, LTD. Dependencies: FMT_SMF.1 Specification of Management Functions FMT_SMR.1 Security roles FPT_FDI_EXP.1.1 The TSF shall provide the capability to restrict data received on [assignment: the Operation Panel, LAN, telephone ...line] from being forwarded without further processing by the TSF to [assignment: the LAN and telephone line]. 6.1.7 Class FTA: TOE access FTA_SSL.3 TSF-initiated termination ...
Security Target
Page 73
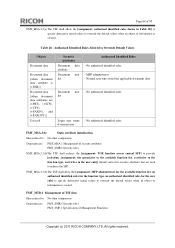
... data. By satisfying FDP_ACC.1(a), FDP_ACF.1(a), FDP_RIP.1, FTP_ITC.1, FMT_MSA.1(a) and FMT_MSA.3(a), which are generated. Copyright (c) 2011 RICOH COMPANY, LTD. All rights reserved. To fulfil this security objective, it is required to implement the following persons to...access control to perform each operation. The supervisor and RC Gate are generated. O.DOC.NO_ALT Protection of document alteration O.DOC.NO_ALT is the security objective to prevent the documents from being used by FTP_ITC.1. (4) Management of the security attributes. FMT_MSA.3(a) surely sets the restrictive...
... data. By satisfying FDP_ACC.1(a), FDP_ACF.1(a), FDP_RIP.1, FTP_ITC.1, FMT_MSA.1(a) and FMT_MSA.3(a), which are generated. Copyright (c) 2011 RICOH COMPANY, LTD. All rights reserved. To fulfil this security objective, it is required to implement the following persons to...access control to perform each operation. The supervisor and RC Gate are generated. O.DOC.NO_ALT Protection of document alteration O.DOC.NO_ALT is the security objective to prevent the documents from being used by FTP_ITC.1. (4) Management of the security attributes. FMT_MSA.3(a) surely sets the restrictive...
Security Target
Page 75
...protected by FTP_ITC.1. O.USER.AUTHORIZED User identification and authentication O.USER.AUTHORIZED is the security objective to restrict users in advance, and associate the users who attempts to use the TOE functions. To fulfil... normal user. FMT_SMF.1 performs the required Management Functions for authentication using passwords when the TOE is accessed from the Operation Panel or a Web browser of client computer, documents are successfully identified and authenticated... identified and authenticated user to use . Copyright (c) 2011 RICOH COMPANY, LTD. All rights reserved.
...protected by FTP_ITC.1. O.USER.AUTHORIZED User identification and authentication O.USER.AUTHORIZED is the security objective to restrict users in advance, and associate the users who attempts to use the TOE functions. To fulfil... normal user. FMT_SMF.1 performs the required Management Functions for authentication using passwords when the TOE is accessed from the Operation Panel or a Web browser of client computer, documents are successfully identified and authenticated... identified and authenticated user to use . Copyright (c) 2011 RICOH COMPANY, LTD. All rights reserved.
Security Target
Page 76
...policy. FMT_MSA.3(b) sets the permissive default value to the available function list, and sets the restrictive default value to operate the function type. Therefore, the access control for certain period and the auto logout time elapses. FIA_UID.2 identifies the persons who attempt... terminate the connection to use the Operation Panel and LAN interface. O.INTERFACE.MANAGED Management of the security attributes. Copyright (c) 2011 RICOH COMPANY, LTD. All rights reserved. For the External Authentication, this depends on the settings for the Basic Authentication by the Basic...
...policy. FMT_MSA.3(b) sets the permissive default value to the available function list, and sets the restrictive default value to operate the function type. Therefore, the access control for certain period and the auto logout time elapses. FIA_UID.2 identifies the persons who attempt... terminate the connection to use the Operation Panel and LAN interface. O.INTERFACE.MANAGED Management of the security attributes. Copyright (c) 2011 RICOH COMPANY, LTD. All rights reserved. For the External Authentication, this depends on the settings for the Basic Authentication by the Basic...
Security Target
Page 87
Copyright (c) 2011 RICOH COMPANY, LTD. Web browser Document Server Function Web browser Document Server ... Download Delete (Operations above are authorised only if normal users are not allowed to use Document Server Function) (2) Access control rule on user jobs The TOE displays on the Operation Panel a menu to cancel a user job only ... remain stored in from the Operation Panel is a user job owner or MFP administrator and a cancellation of -Feature Restriction Function is attempted by the cancelled job will not be deleted. Other users are privileged to use Copy Function, Printer...
Copyright (c) 2011 RICOH COMPANY, LTD. Web browser Document Server Function Web browser Document Server ... Download Delete (Operations above are authorised only if normal users are not allowed to use Document Server Function) (2) Access control rule on user jobs The TOE displays on the Operation Panel a menu to cancel a user job only ... remain stored in from the Operation Panel is a user job owner or MFP administrator and a cancellation of -Feature Restriction Function is attempted by the cancelled job will not be deleted. Other users are privileged to use Copy Function, Printer...